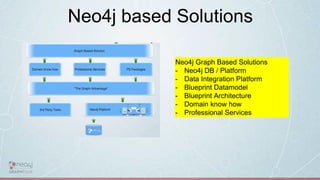
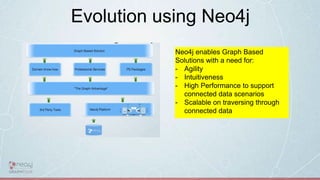
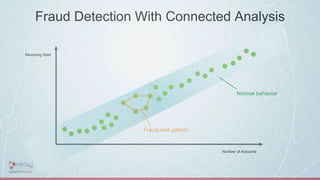
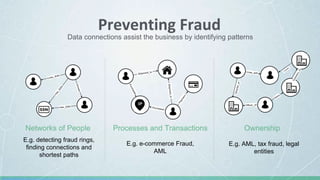
This document discusses how to build next generation fraud solutions using Neo4j graph database technology. It begins by outlining the challenges of fraud and how traditional relational databases are inadequate for detecting complex fraud patterns. It then describes how graph databases like Neo4j can provide a 360-degree view of connected customer and transaction data to enable real-time fraud detection. Examples of fraud use cases where Neo4j has been successfully applied are also provided, followed by an overview of how to architect a fraud solution leveraging Neo4j's graph capabilities.























![The Power of Cypher
Fraud Ring:
MATCH ring = (suspect:AccountHolder)-[*]->(contactInformation)<-[*..5]-(:AccountHolder)-[*]->(suspect)
RETURN ring](https://image.slidesharecdn.com/nextgenerationfraudsolutionsusingneo4j0-180515100117/85/Next-Generation-Fraud-Solutions-using-Neo4j-30-320.jpg)












![Conclusion
(graphs)-[:ARE]-> (everywhere)
and
(Solutions)-[:NEED]-> (graphs)](https://image.slidesharecdn.com/nextgenerationfraudsolutionsusingneo4j0-180515100117/85/Next-Generation-Fraud-Solutions-using-Neo4j-43-320.jpg)

