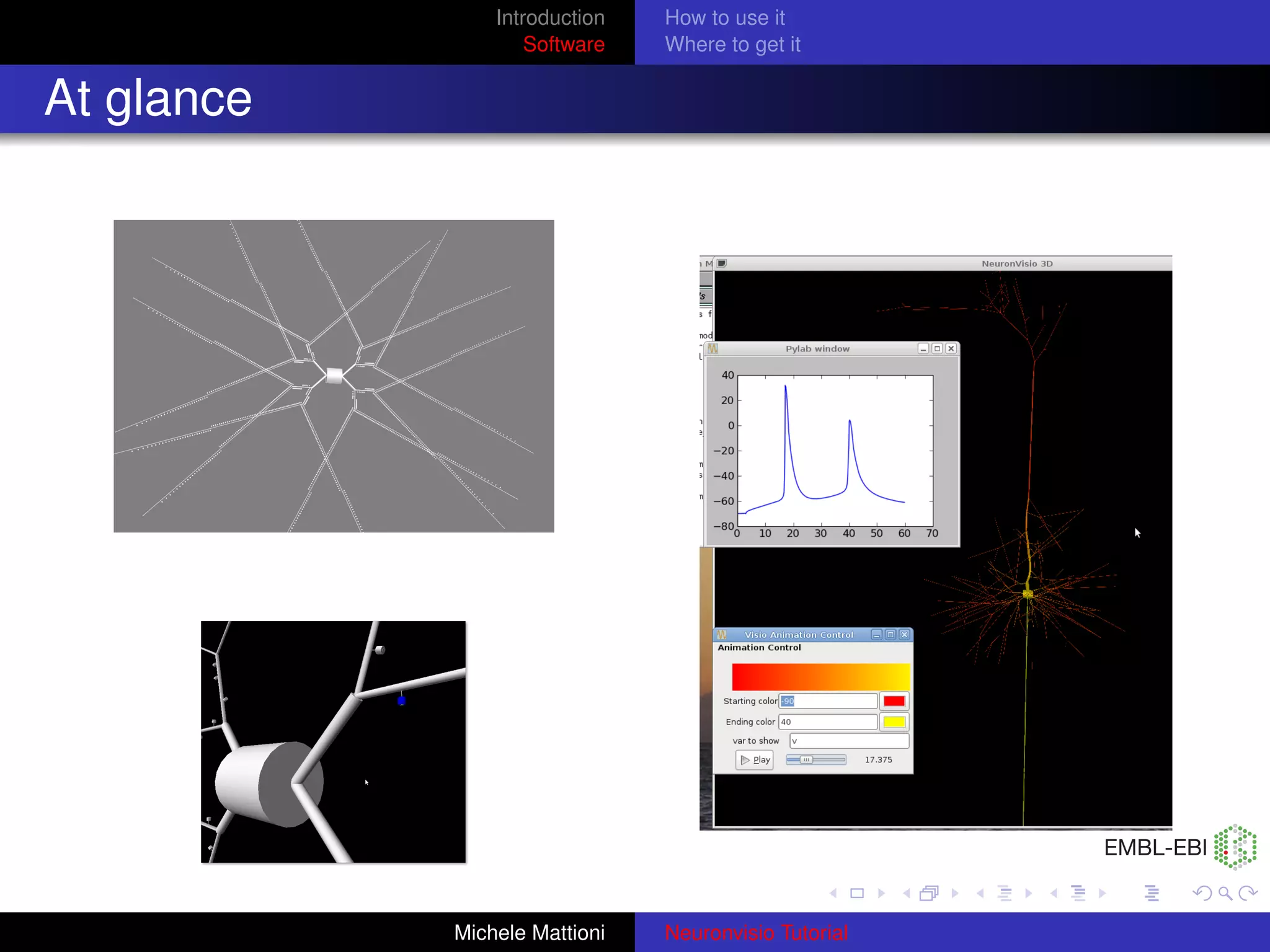
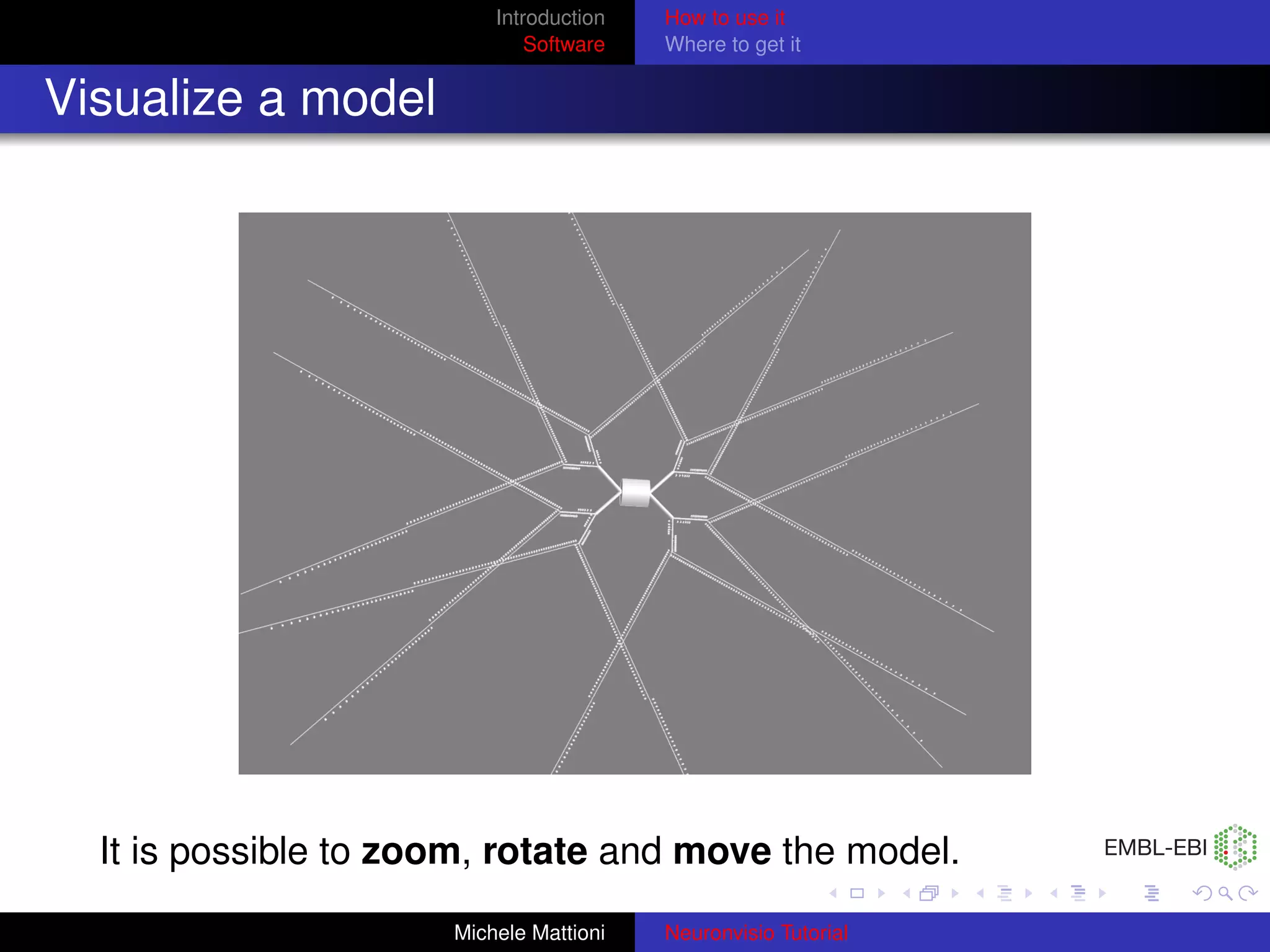
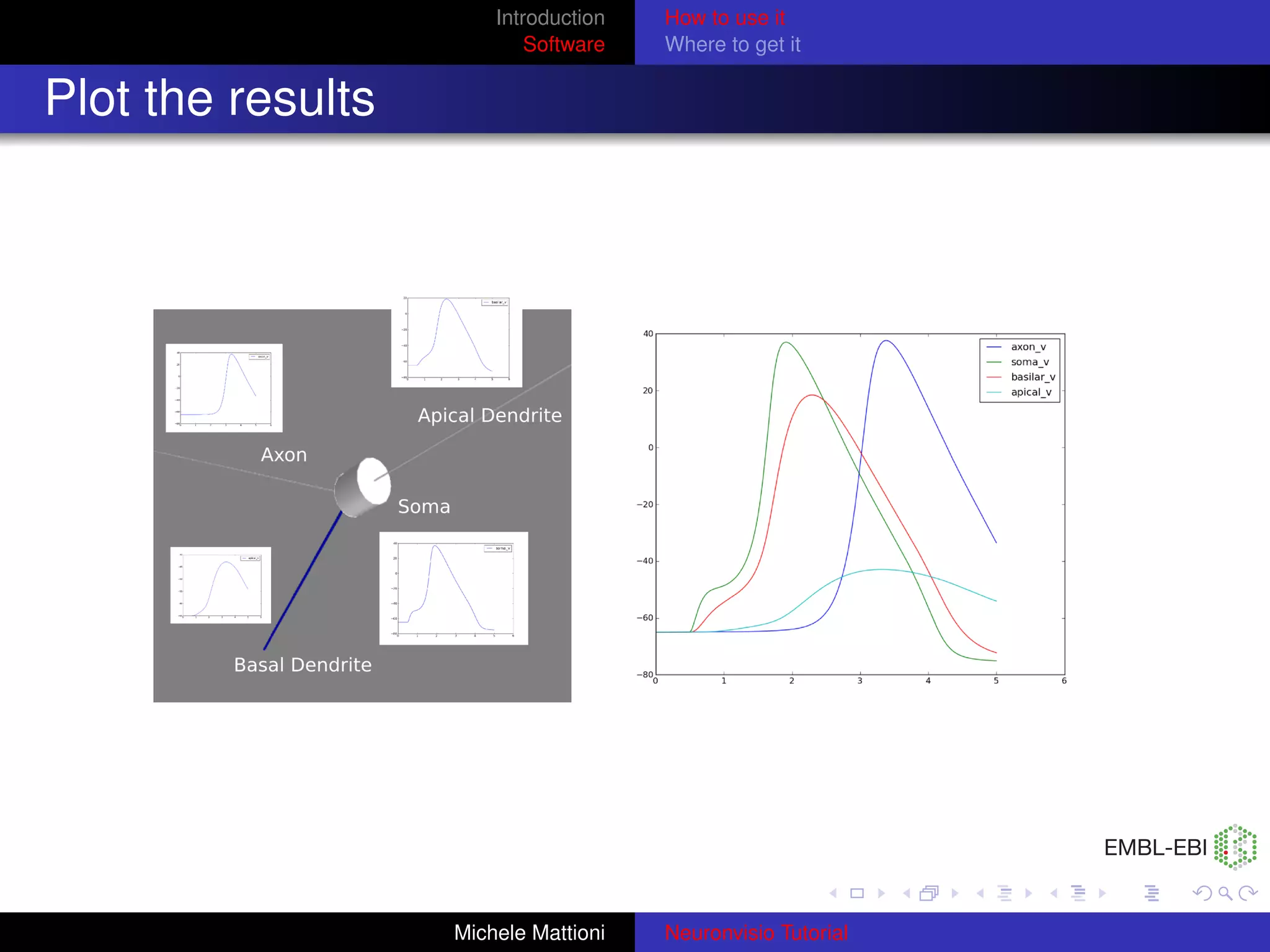
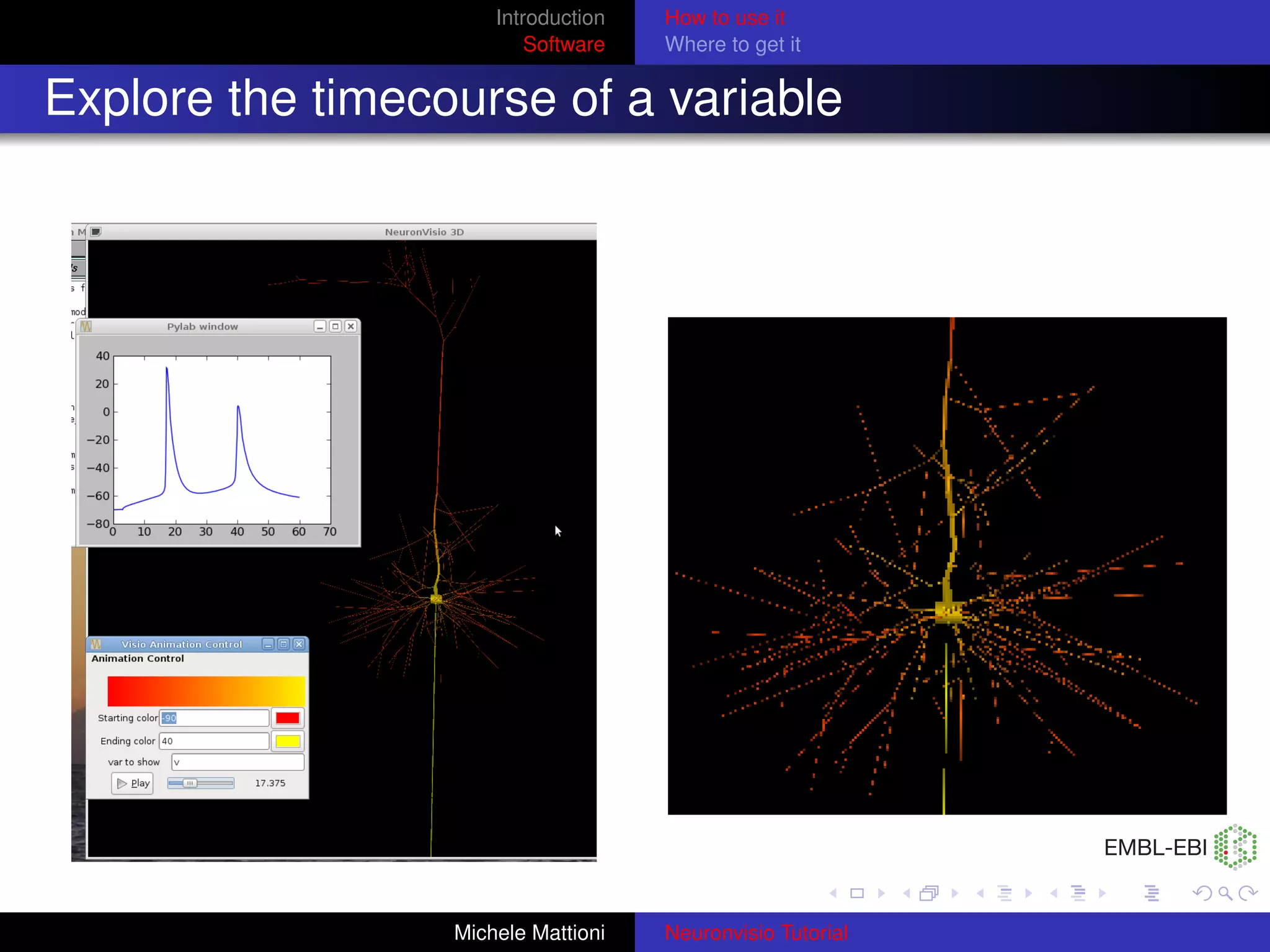
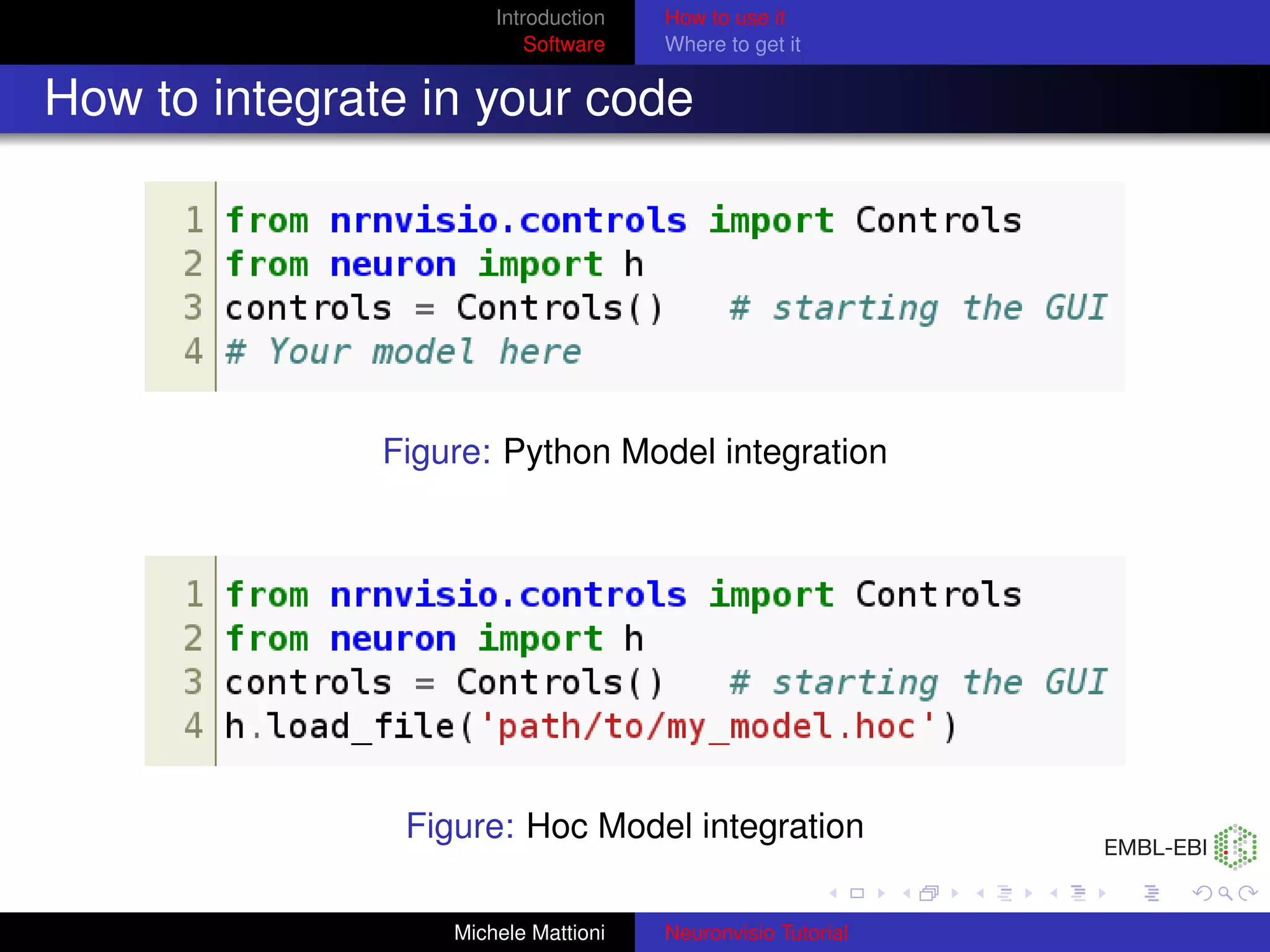
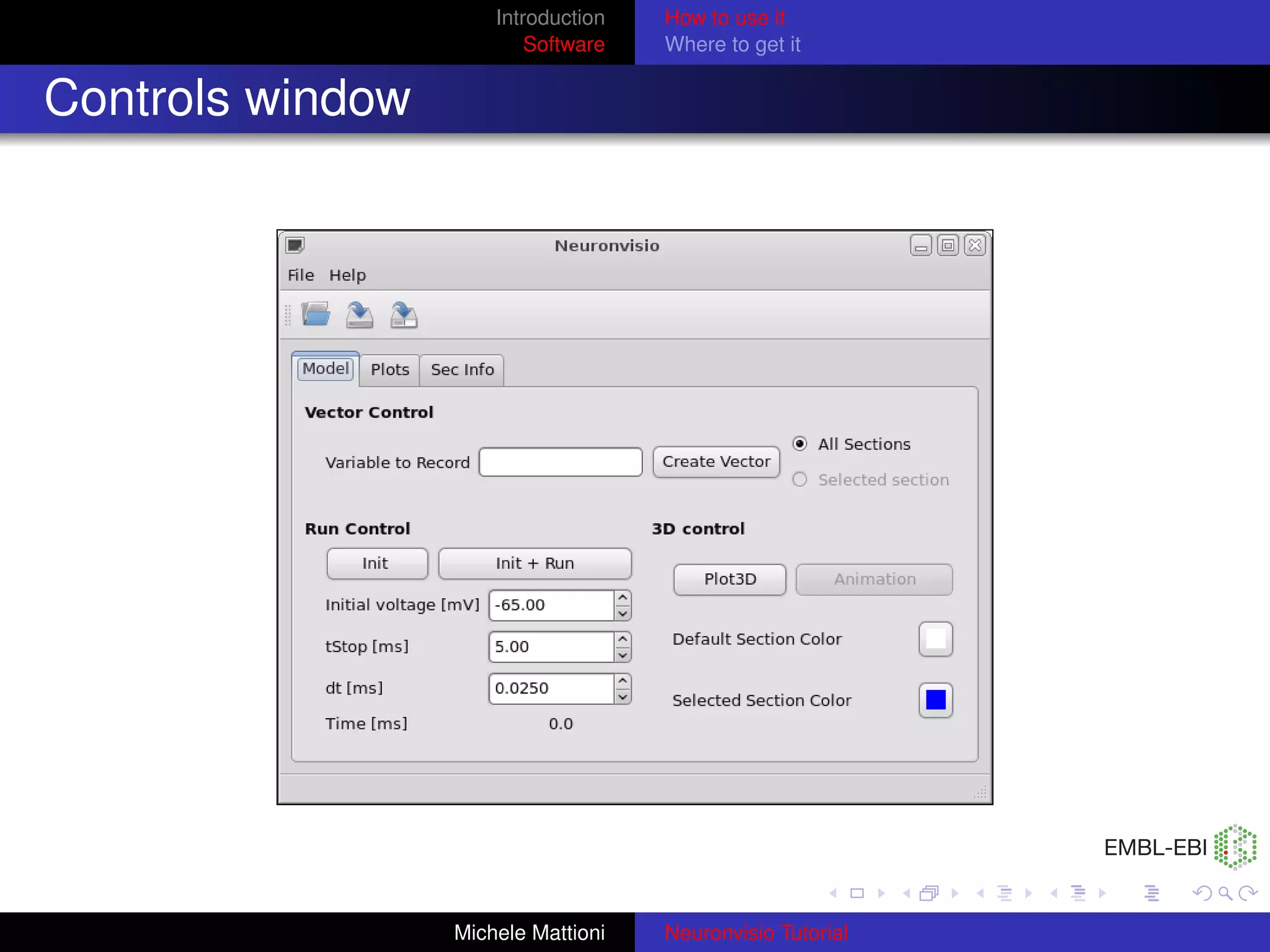
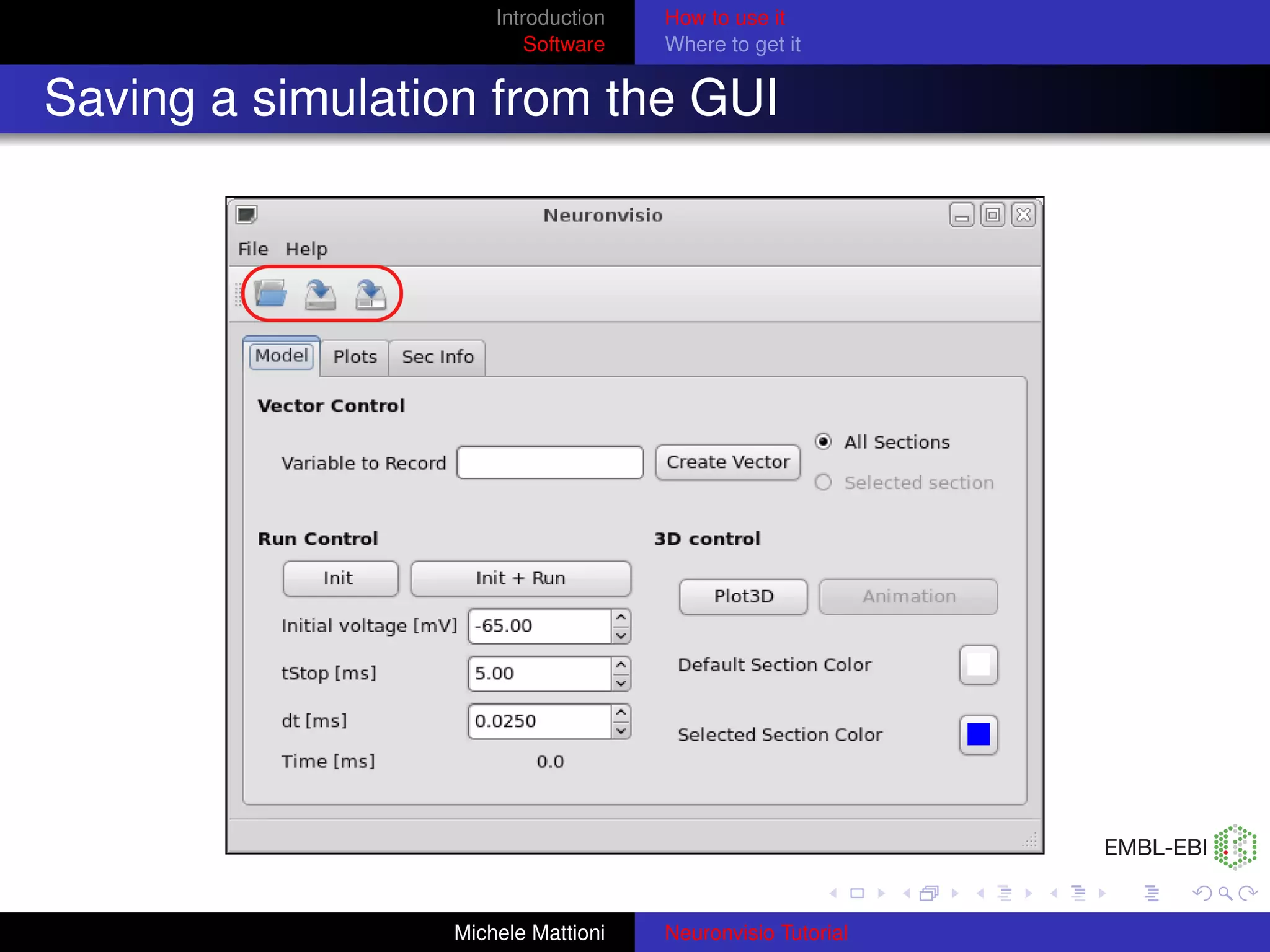
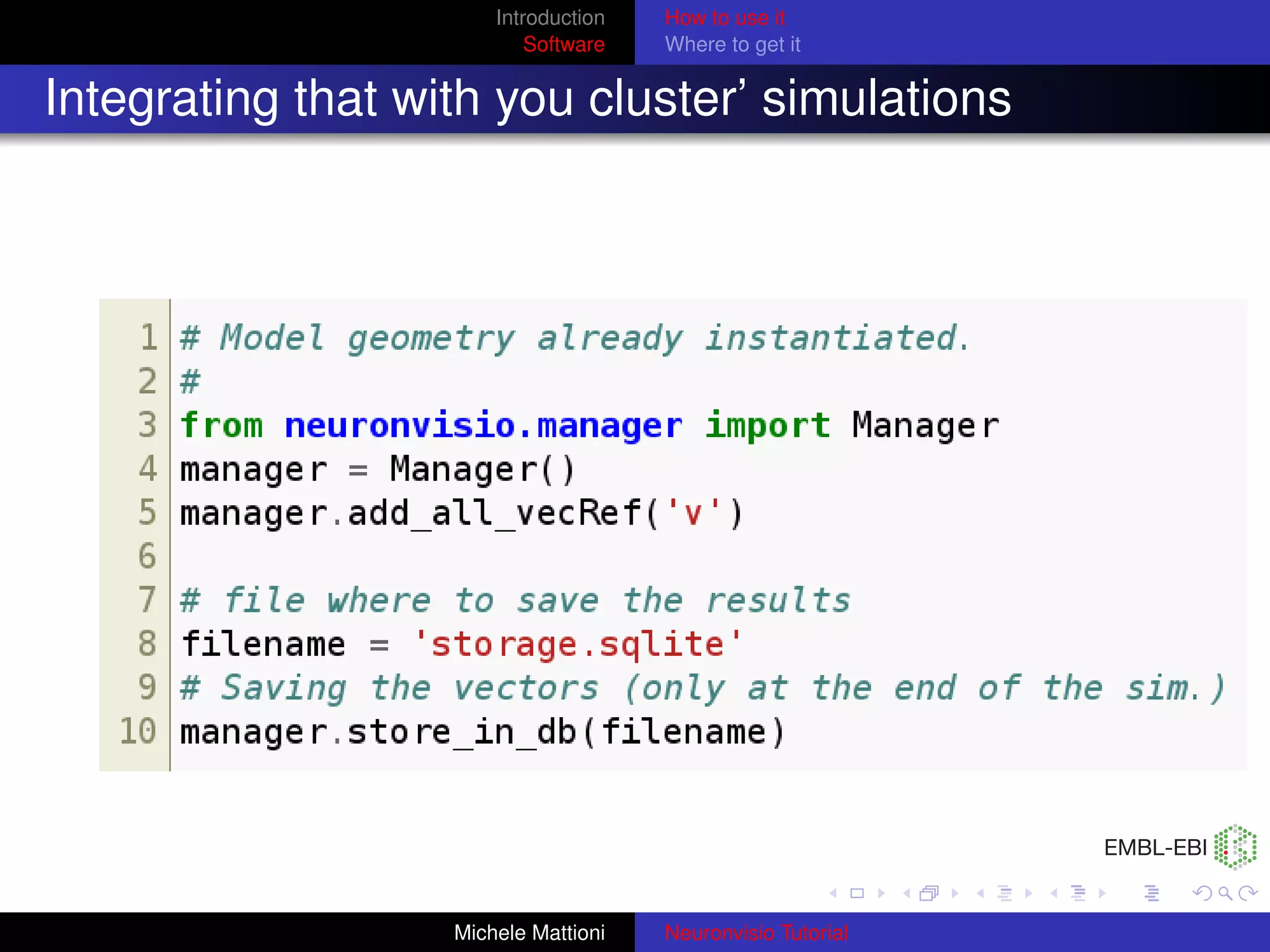
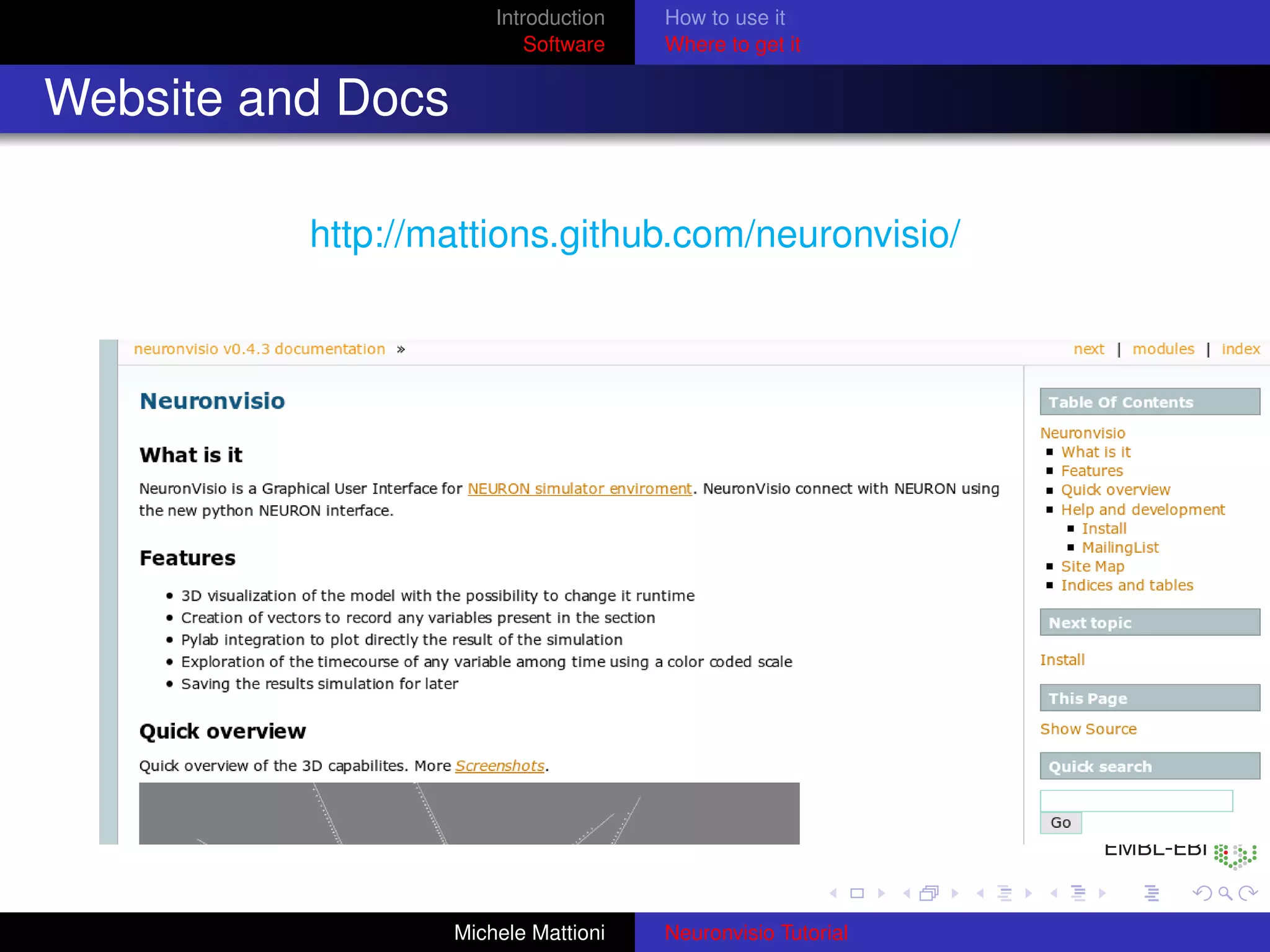
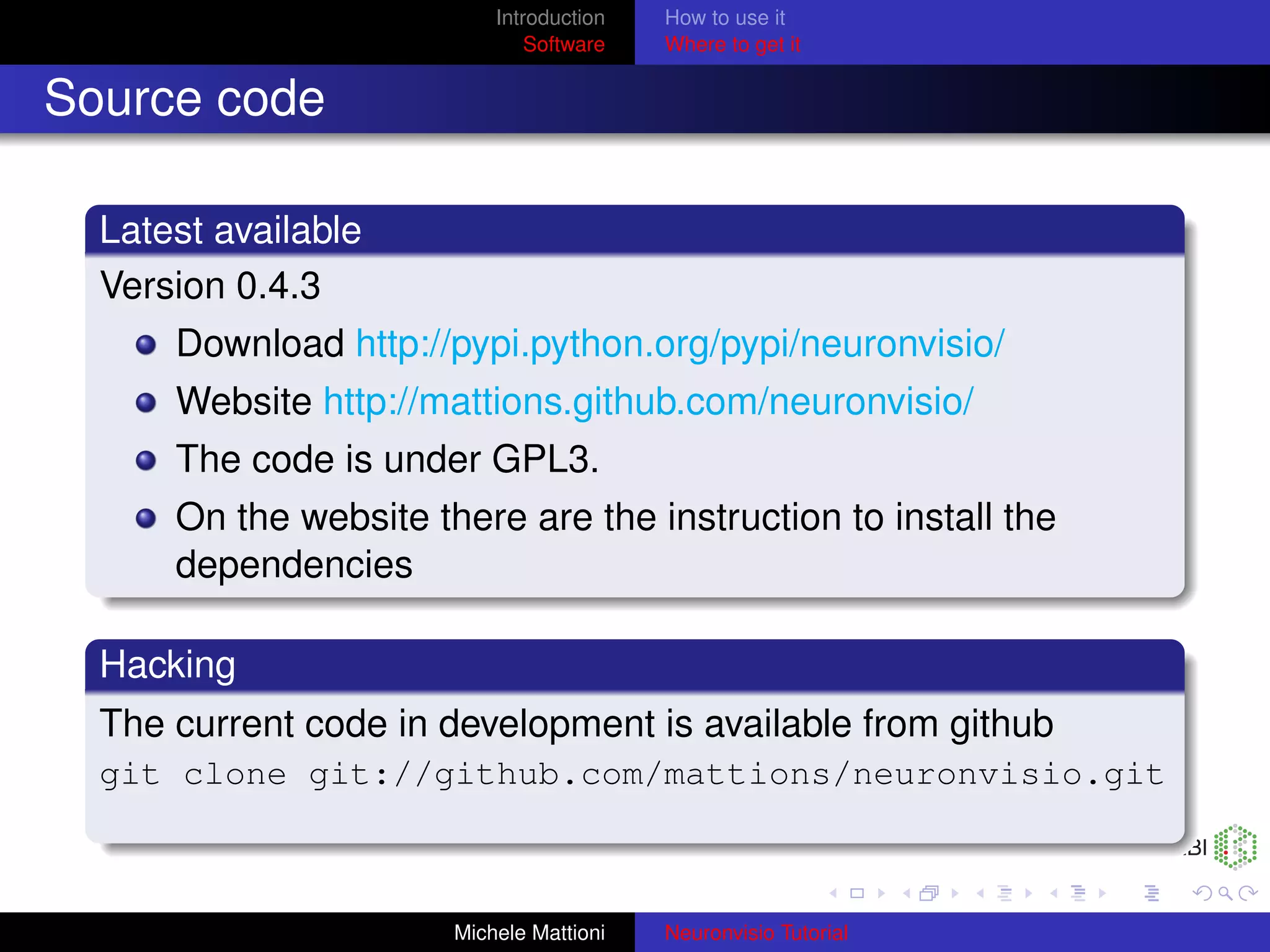
This document is a tutorial for the Neuronvisio software. It provides an overview of the software, including how to visualize and interact with neuron models, plot simulation results, and integrate the software into other code. The tutorial describes how to save simulation results for later analysis and explores the software's website, documentation, and open source code availability. It concludes by offering a live demo of the Neuronvisio software.