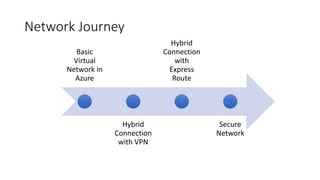
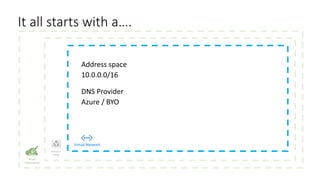
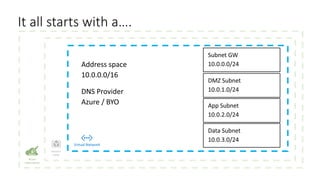
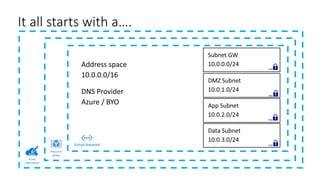
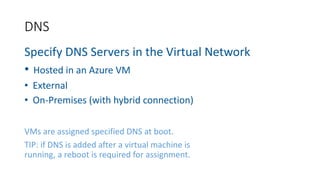
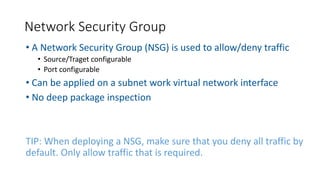
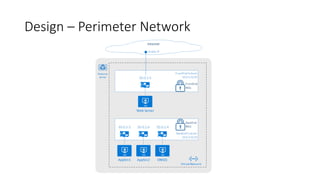
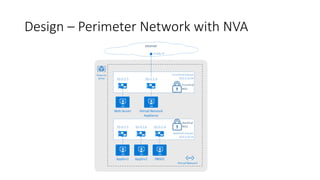
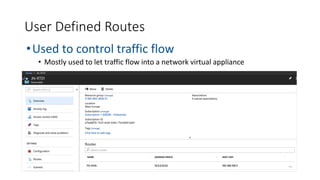
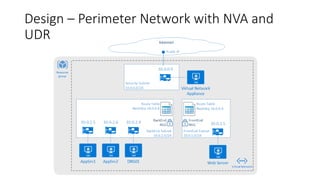
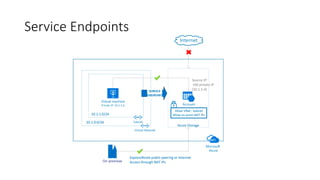
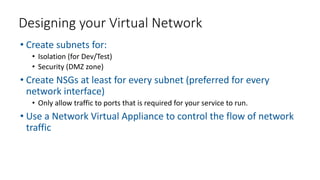
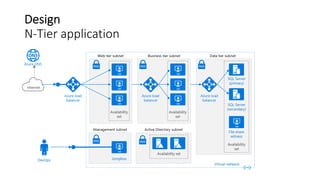
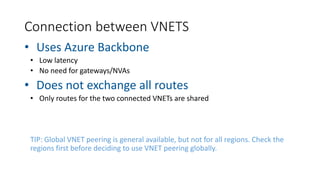
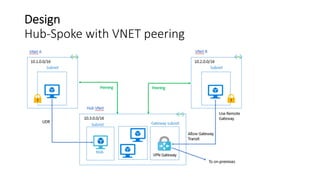
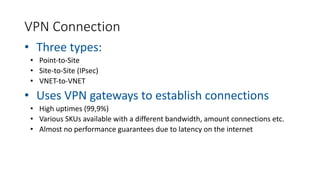
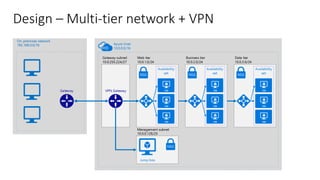
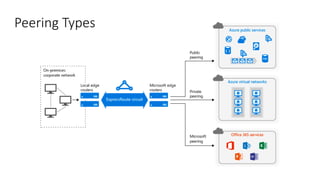
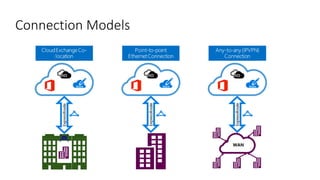
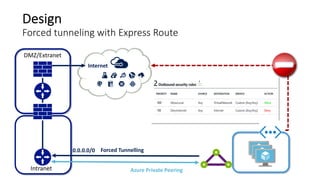
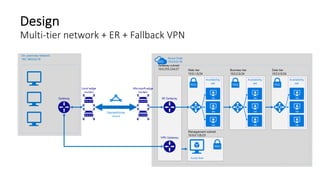
This document discusses designing secure Azure networks. It begins with an overview of basic virtual network (VNET) components like resource groups and network security groups. Various hybrid connection options are presented such as VNET peering, VPN, and ExpressRoute. Demos show how to apply network security groups and configure VNET peering. The importance of security in design is emphasized through recommendations to assume breach, use network components like NSGs and NVAs, and leverage Security Center.