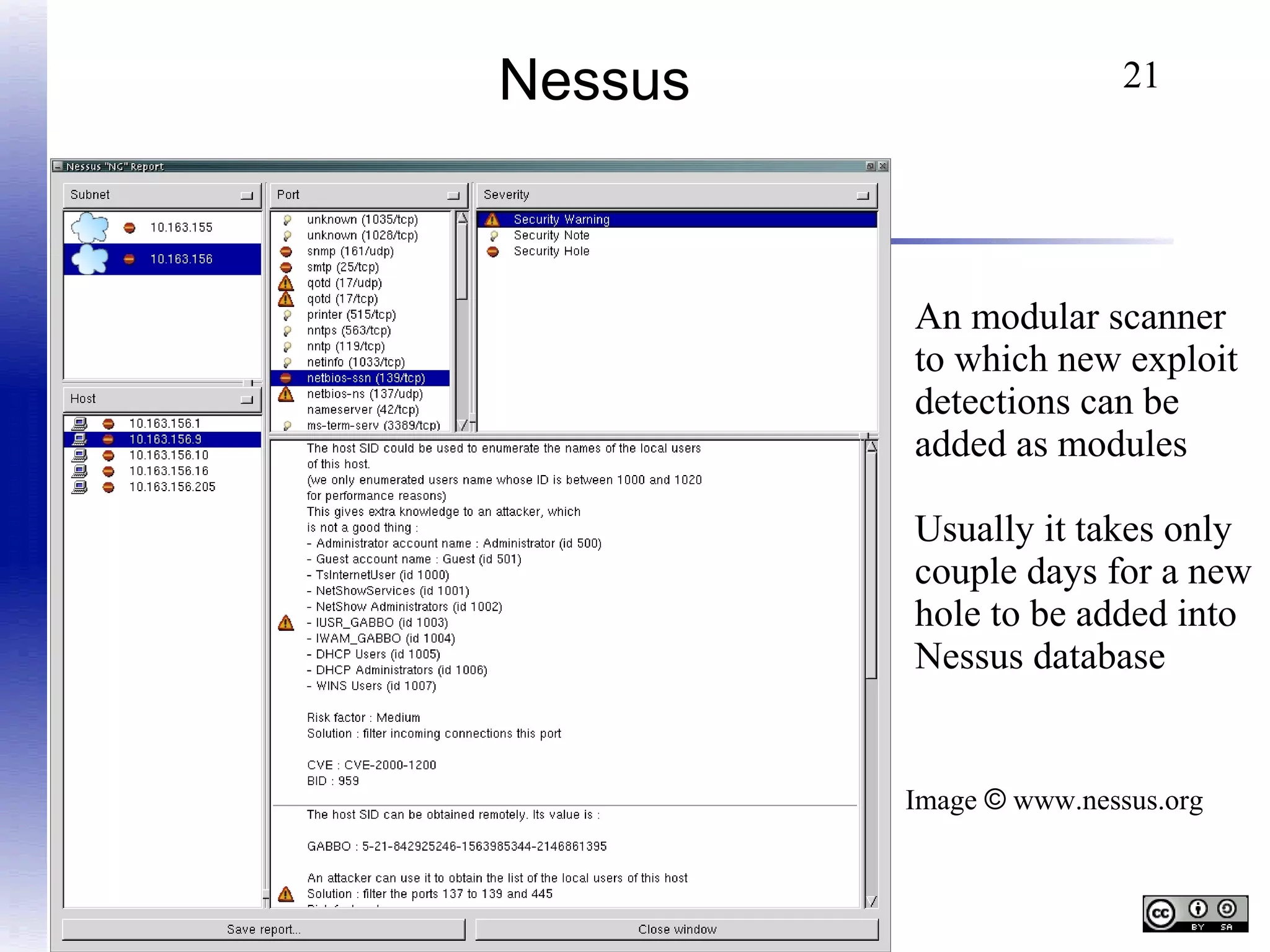
The document discusses the stages of a network attack from an attacker's perspective. It describes how attackers first perform reconnaissance to gather information about a target network such as open ports, services and vulnerabilities. It then discusses how attackers use this information to directly attack systems using exploits or malware. Finally, it mentions how attackers aim to maintain access and cover their tracks after gaining entry. The goal is to provide an overview of the attack process and challenges for network defense.
![15
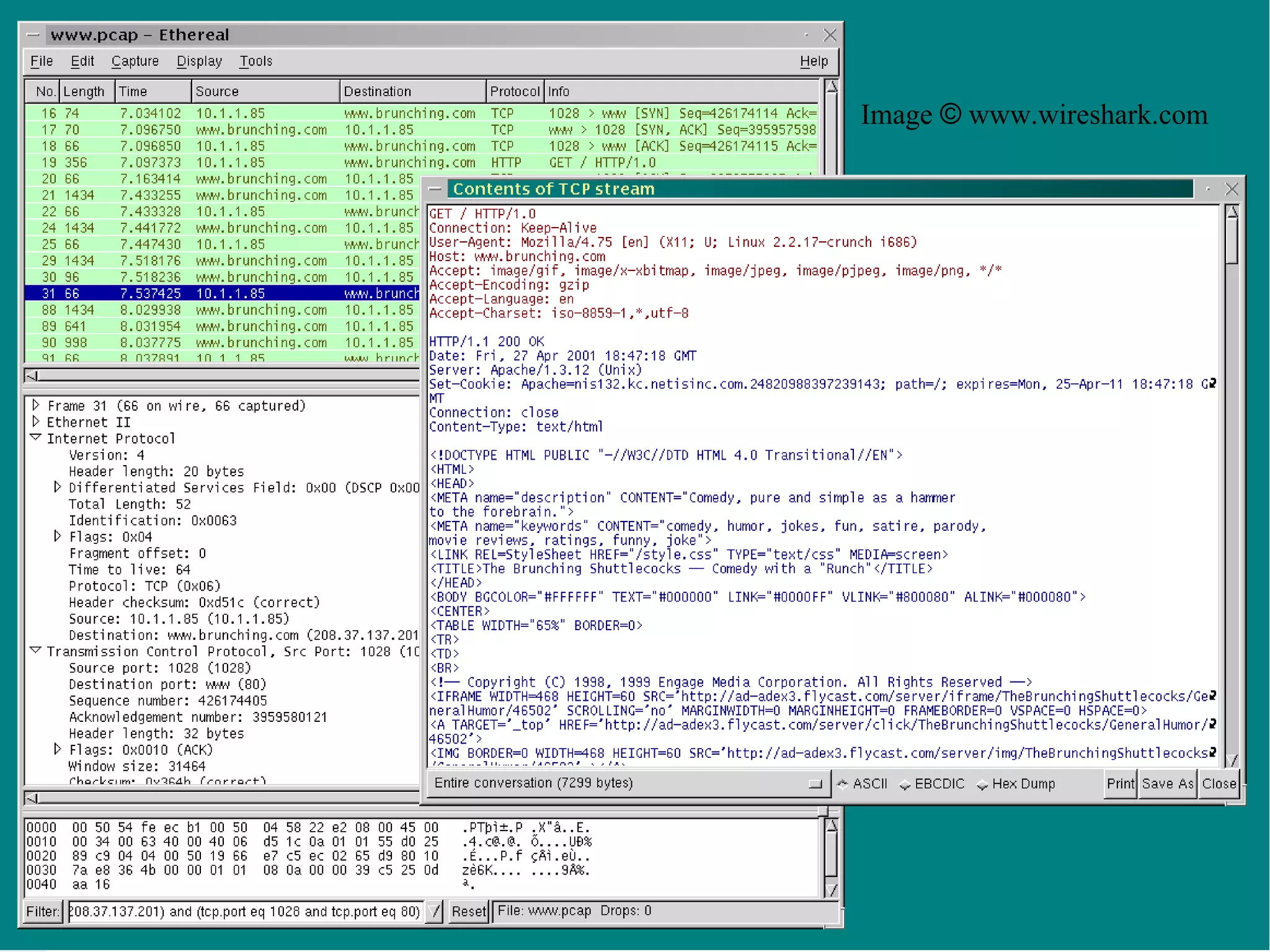
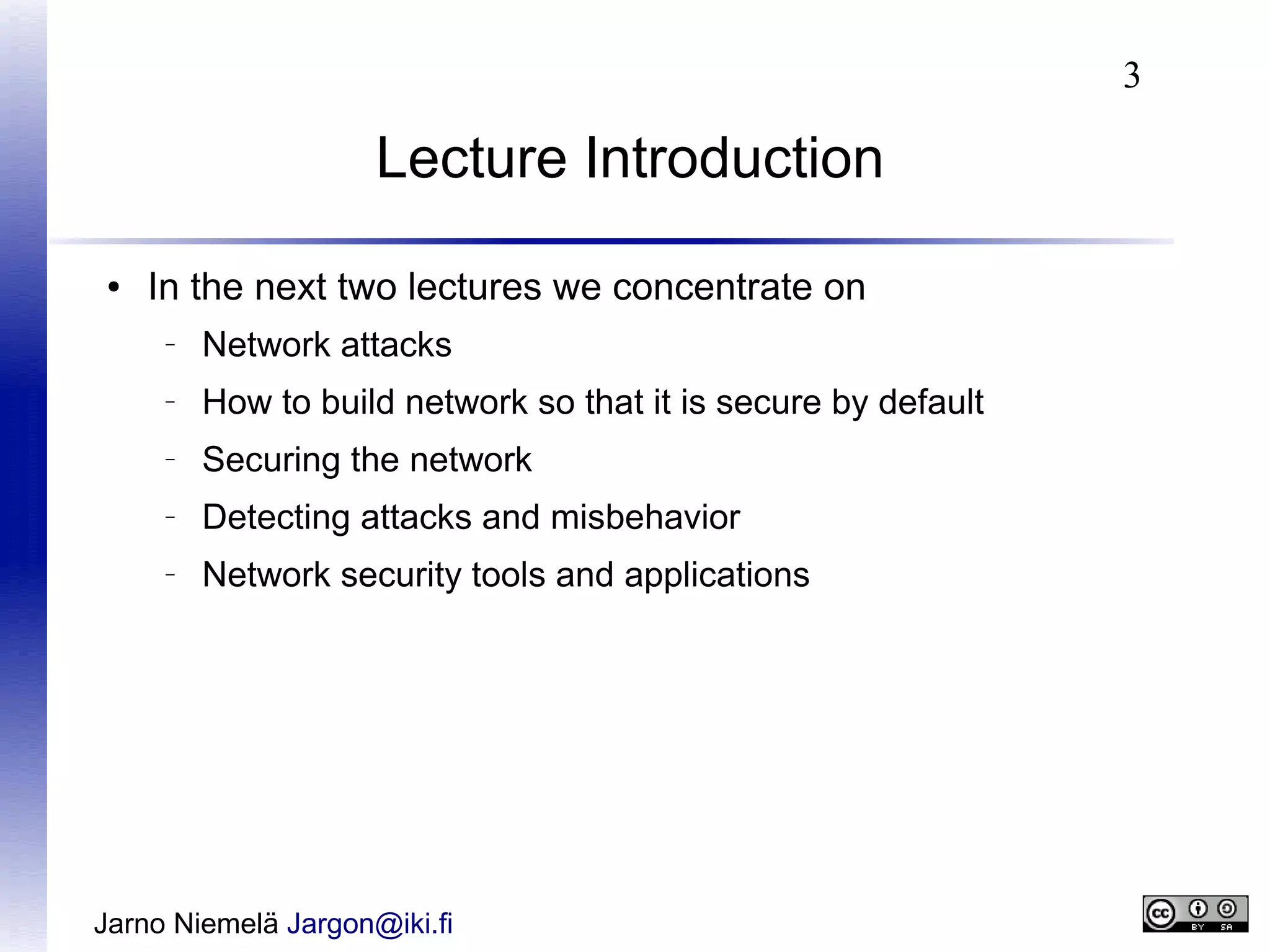
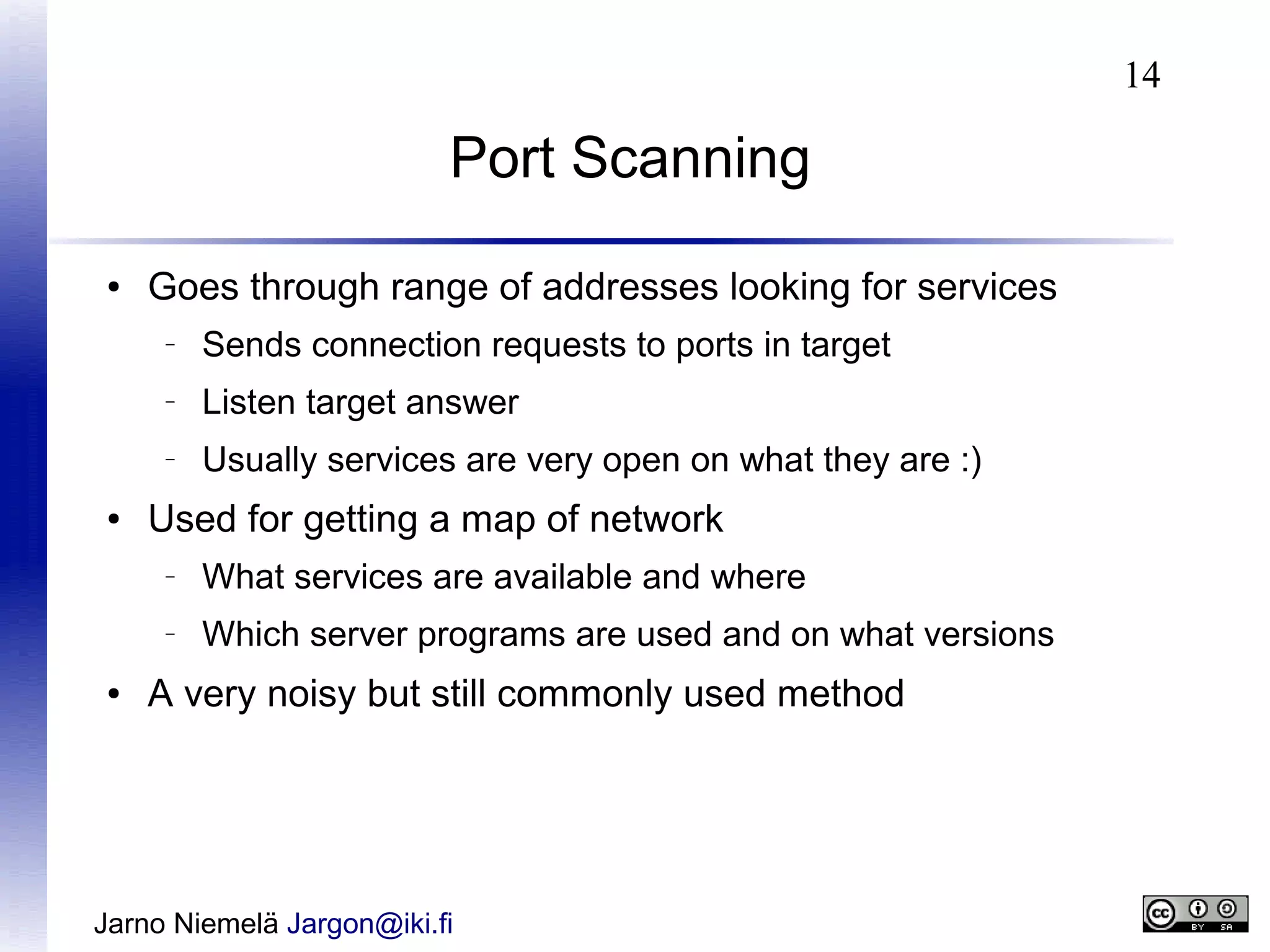
Port Scanning Example
●
●
Probing a port with telnet (so you see the result)
Telnet www.drivermuseum.com 80
Trying 212.226.165.105...
Connected to www.drivermuseum.com.
Escape character is '^]'.
<!DOCTYPE HTML PUBLIC "-//IETF//DTD HTML 2.0//EN">
<HTML><HEAD>
<TITLE>501 Method Not Implemented</TITLE>
</HEAD><BODY>
<H1>Method Not Implemented</H1>
helo to /index.html not supported.<P>
Invalid method in request helo<P>
<HR>
<ADDRESS>Apache/1.3.26 Server at drivermuseum.com Port 80
</ADDRESS></BODY></HTML>
Connection closed by foreign host.
Jarno Niemelä Jargon@iki.fi](https://image.slidesharecdn.com/networksecurity-140102100135-phpapp01/75/Network-security-15-2048.jpg)