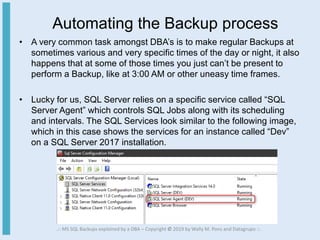
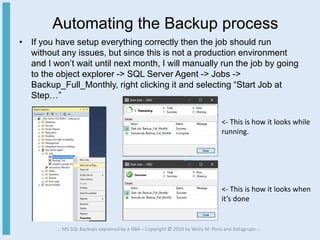
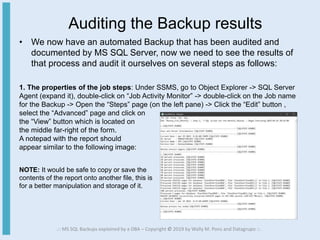
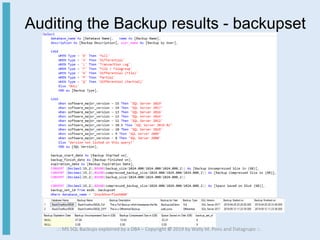
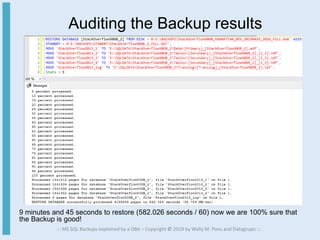
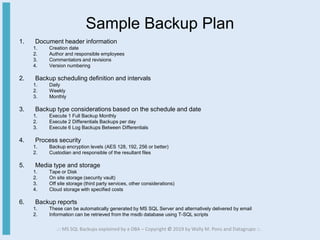
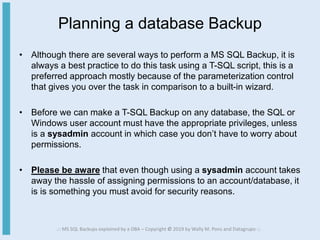
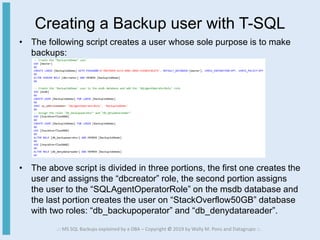
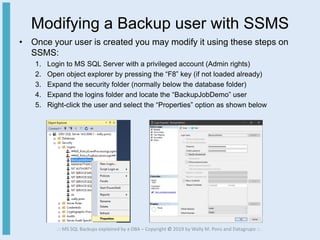
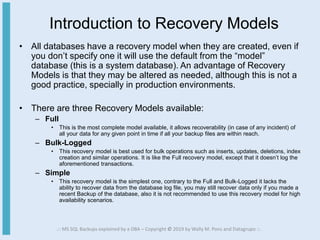
This document provides an overview of database backups for MS SQL, including defining backups, preparing a backup plan, creating different types of backups using T-SQL scripts, and recovery models. It discusses topics such as creating a dedicated backup user, modifying the user in SSMS, introducing full, differential, transaction log, and copy only backups. The document is intended to help readers understand and implement database backups.
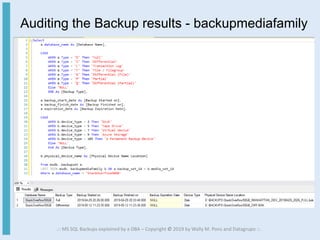
![Explaining the Backup script options (1 of 2)
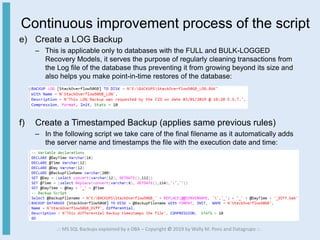
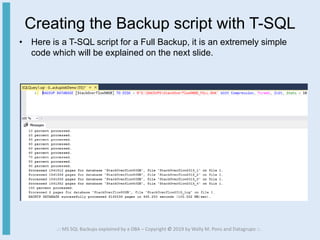
• The Backup script is composed by parameters and options which
define how the process will be performed, here is a detailed
explanation of our previous script:
– BACKUP: This is the first command you must issue.
– DATABASE: This parameter specifies that we’re making a backup to a
database, if we need to make a transaction log backup then we specify LOG
instead.
– [StackOverflow50GB]: This is the name of the database.
– TO DISK = N’’: This portion specifies the path and file name of the backup, you
can also specify a TAPE or URL. Please note that beyond this point all options
are preceded by the With keyword and are separated by commas.
– Compression: Starting with MS SQL Server 2008 R2 you may compress your
backups in size, this was achievable only with third party software solutions or
manually compressing the resultant file(s) with the compression software of your
choice.
.:: MS SQL Backups explained by a DBA – Copyright © 2019 by Wally M. Pons and Datagrupo ::.](https://image.slidesharecdn.com/sqlbackups-190513034341/85/MS-SQL-Backups-explained-by-a-DBA-13-320.jpg)