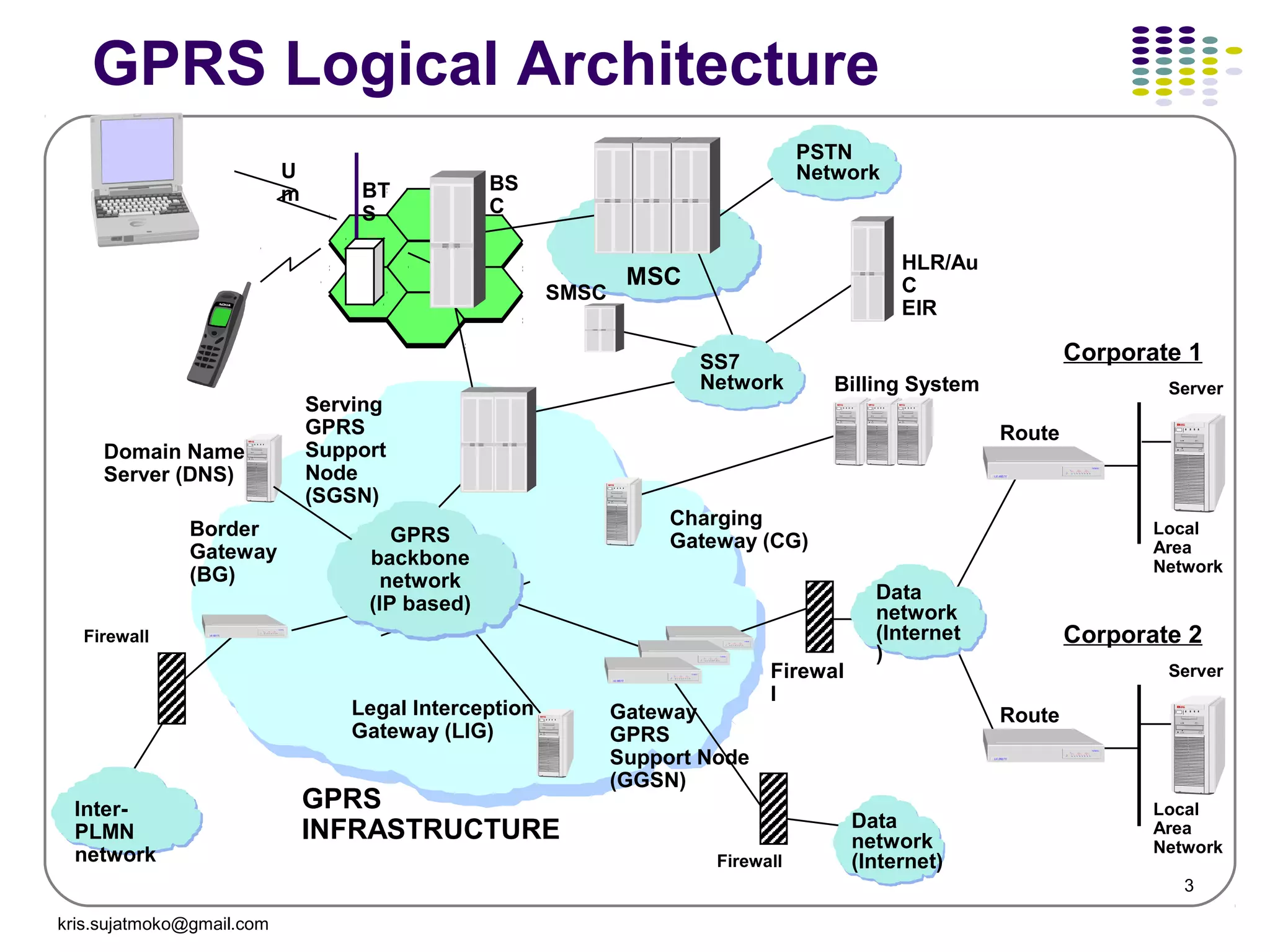
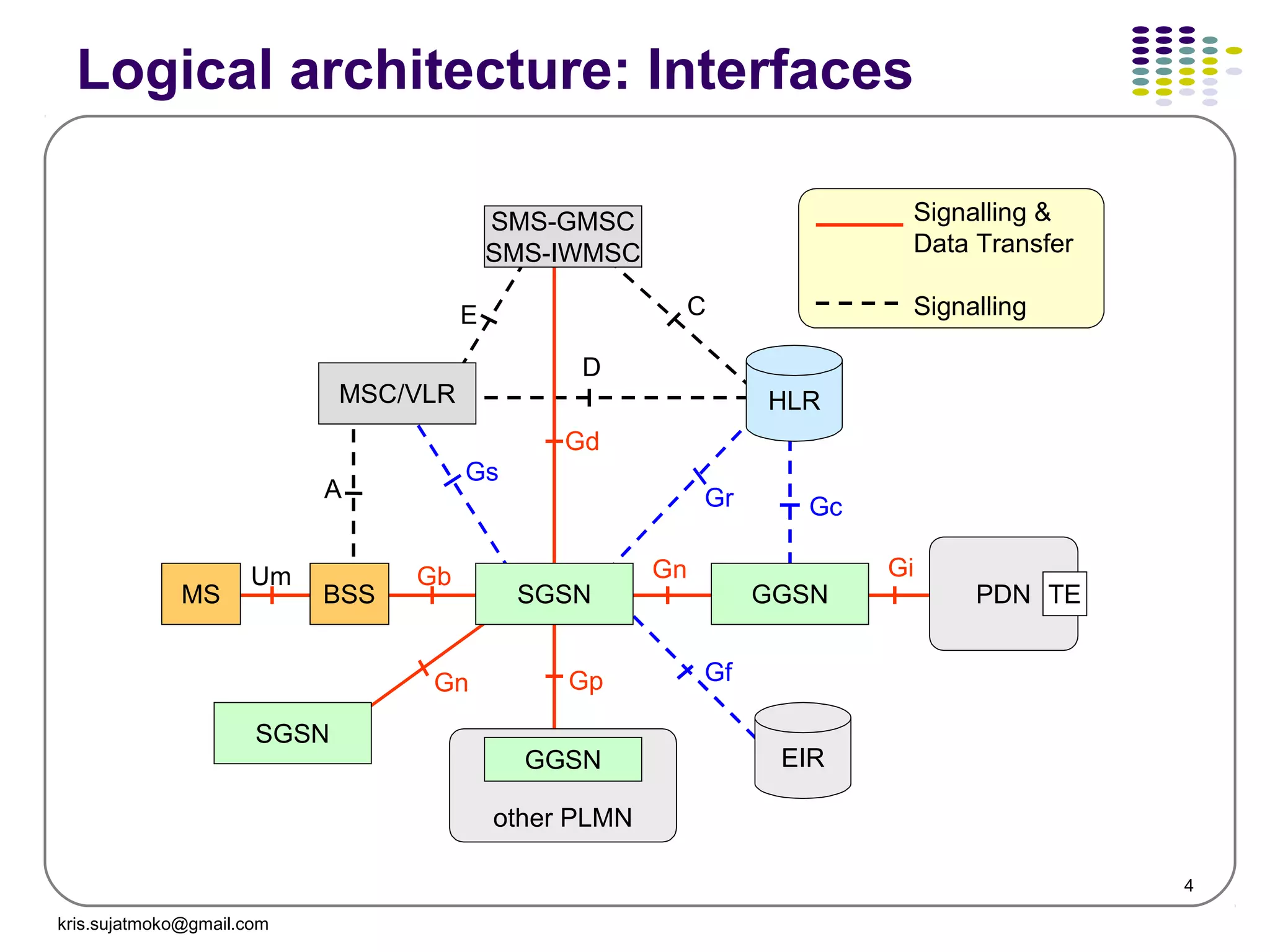
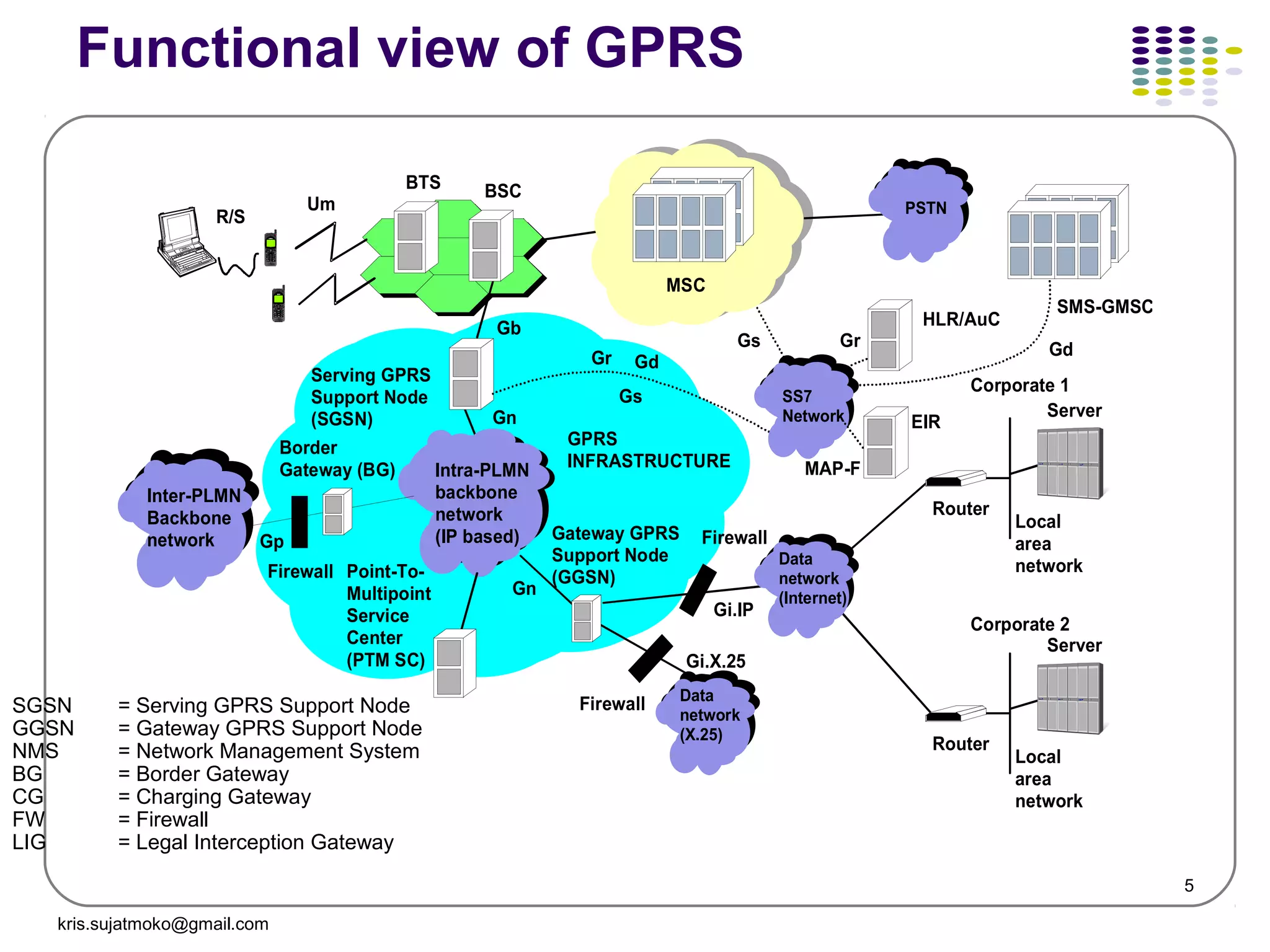
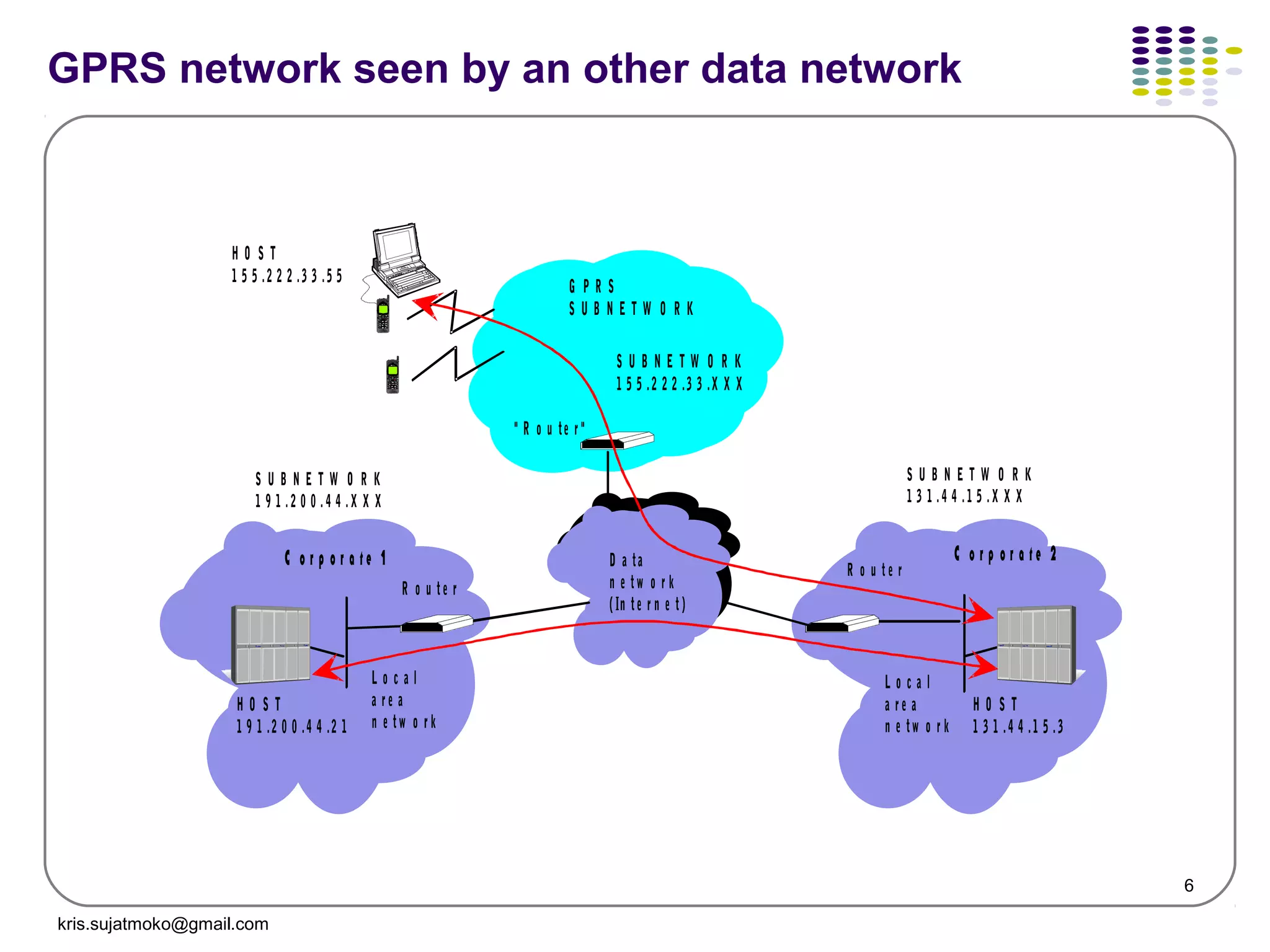
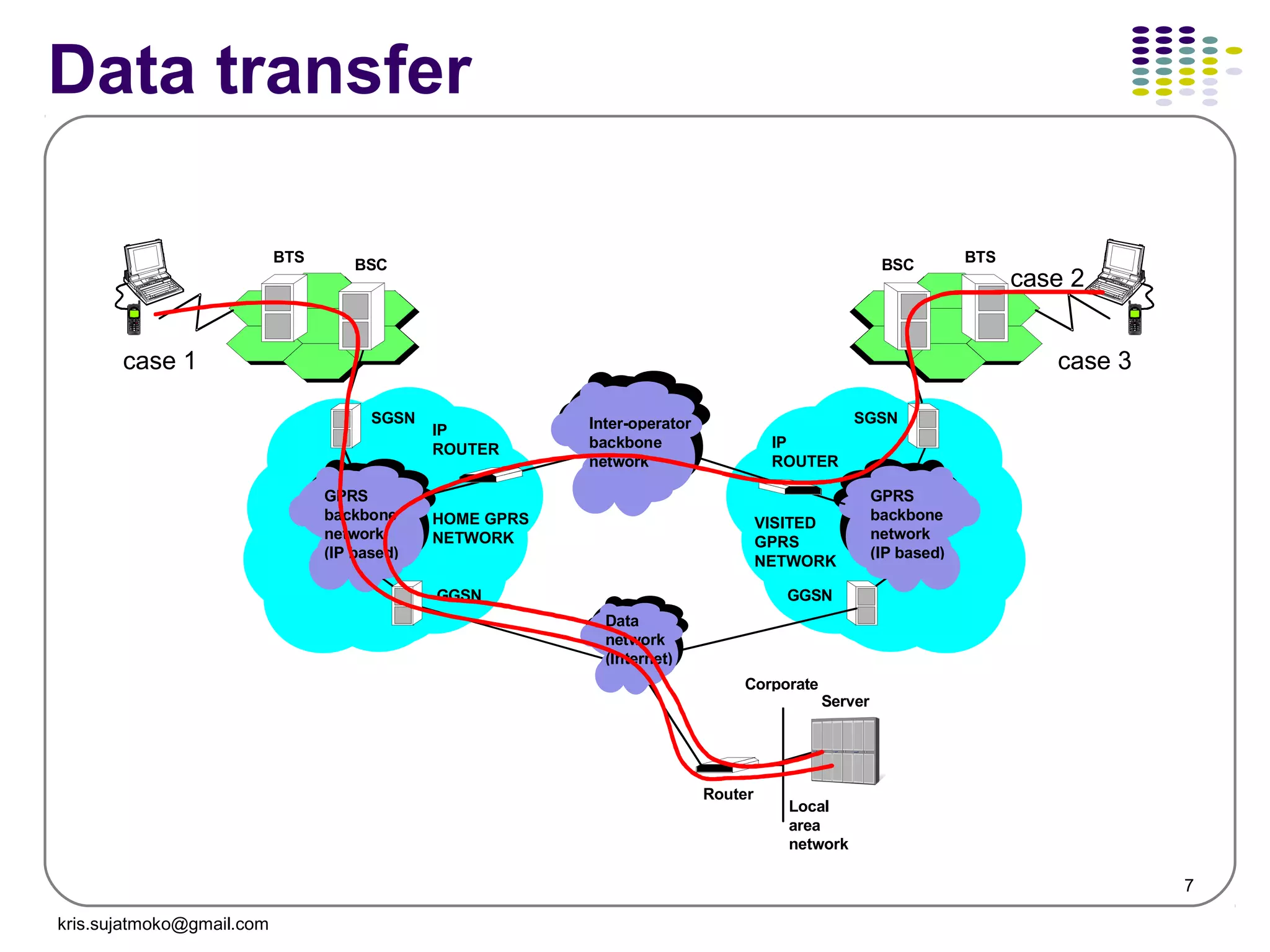
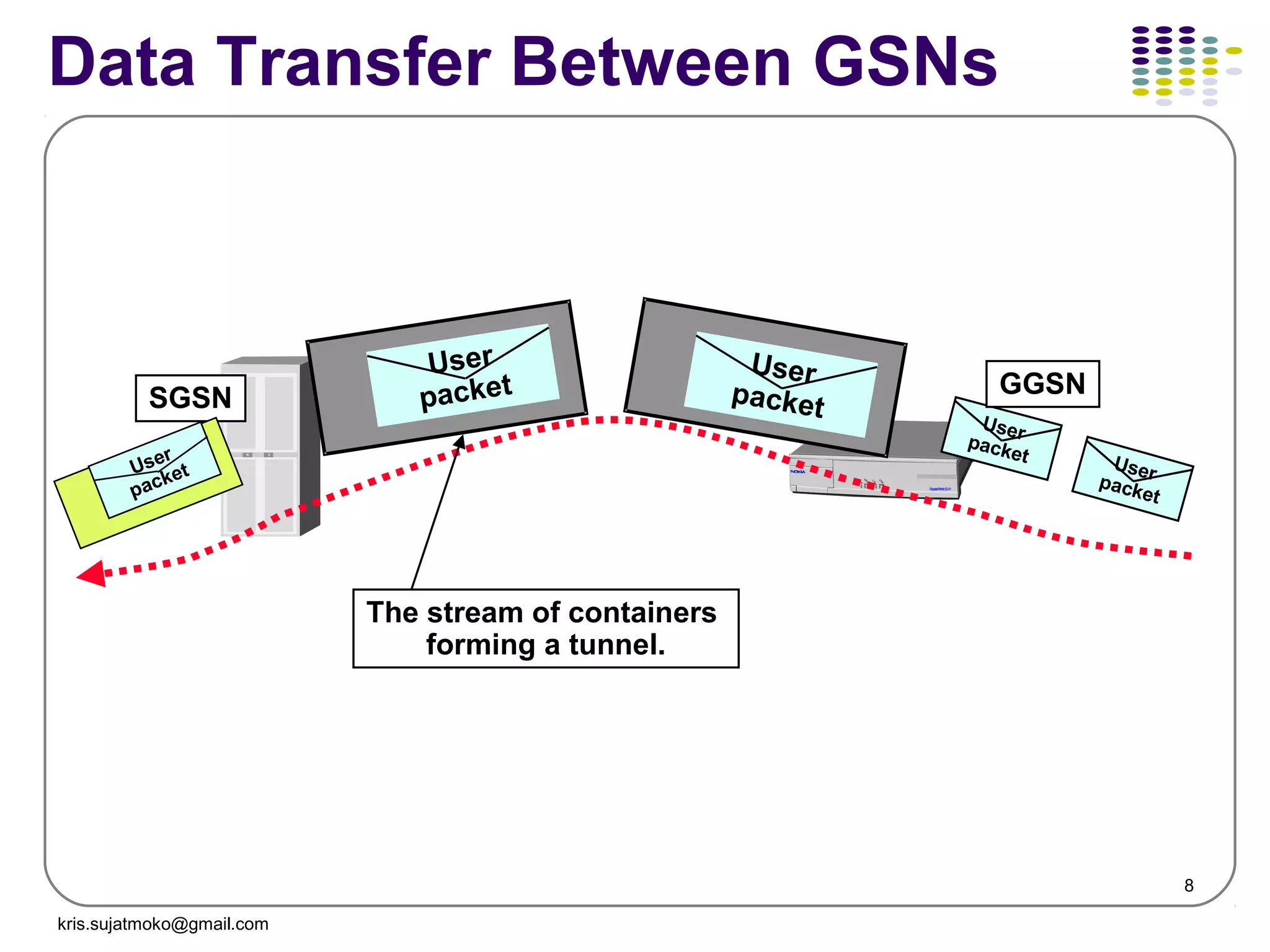
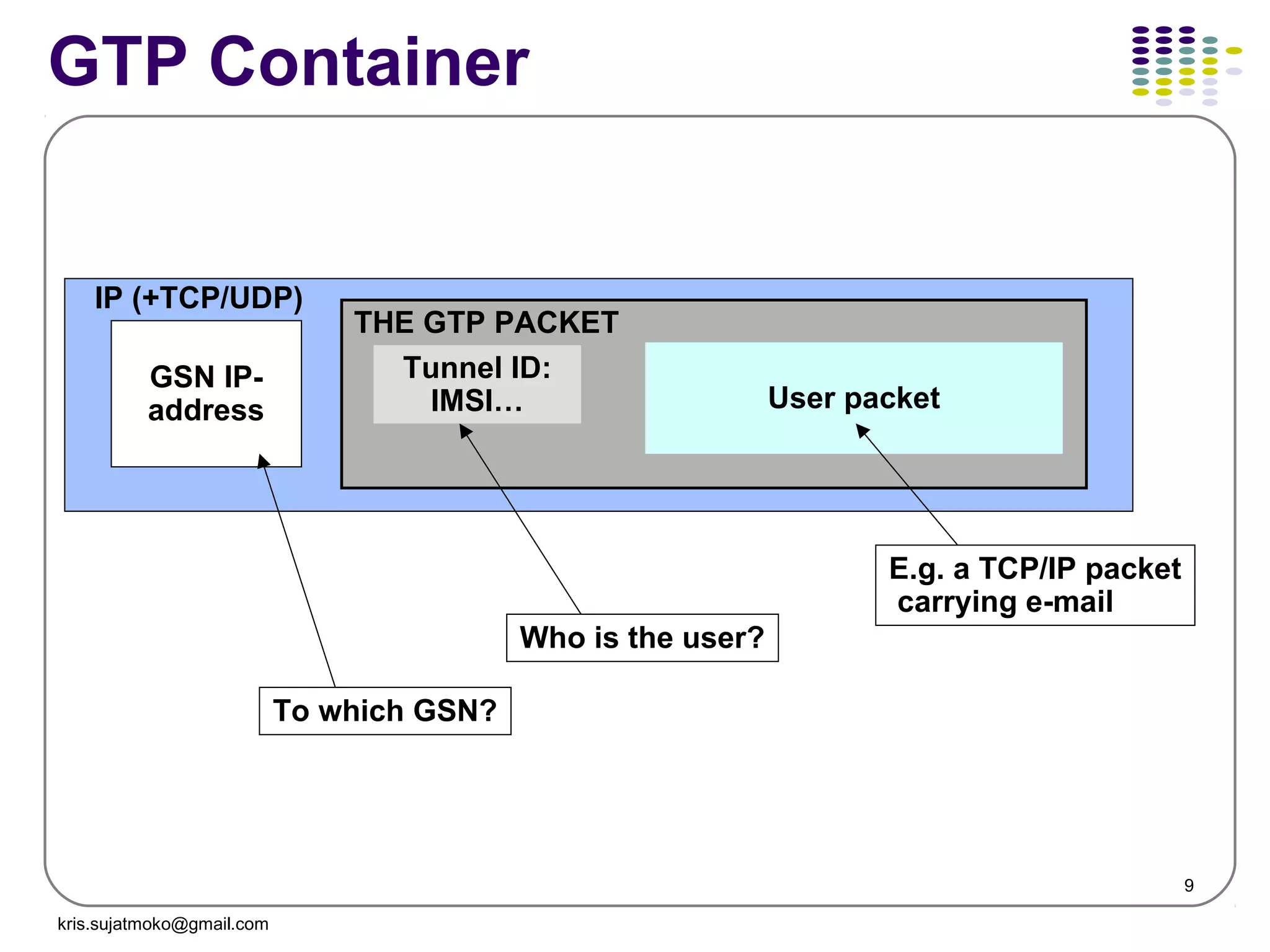
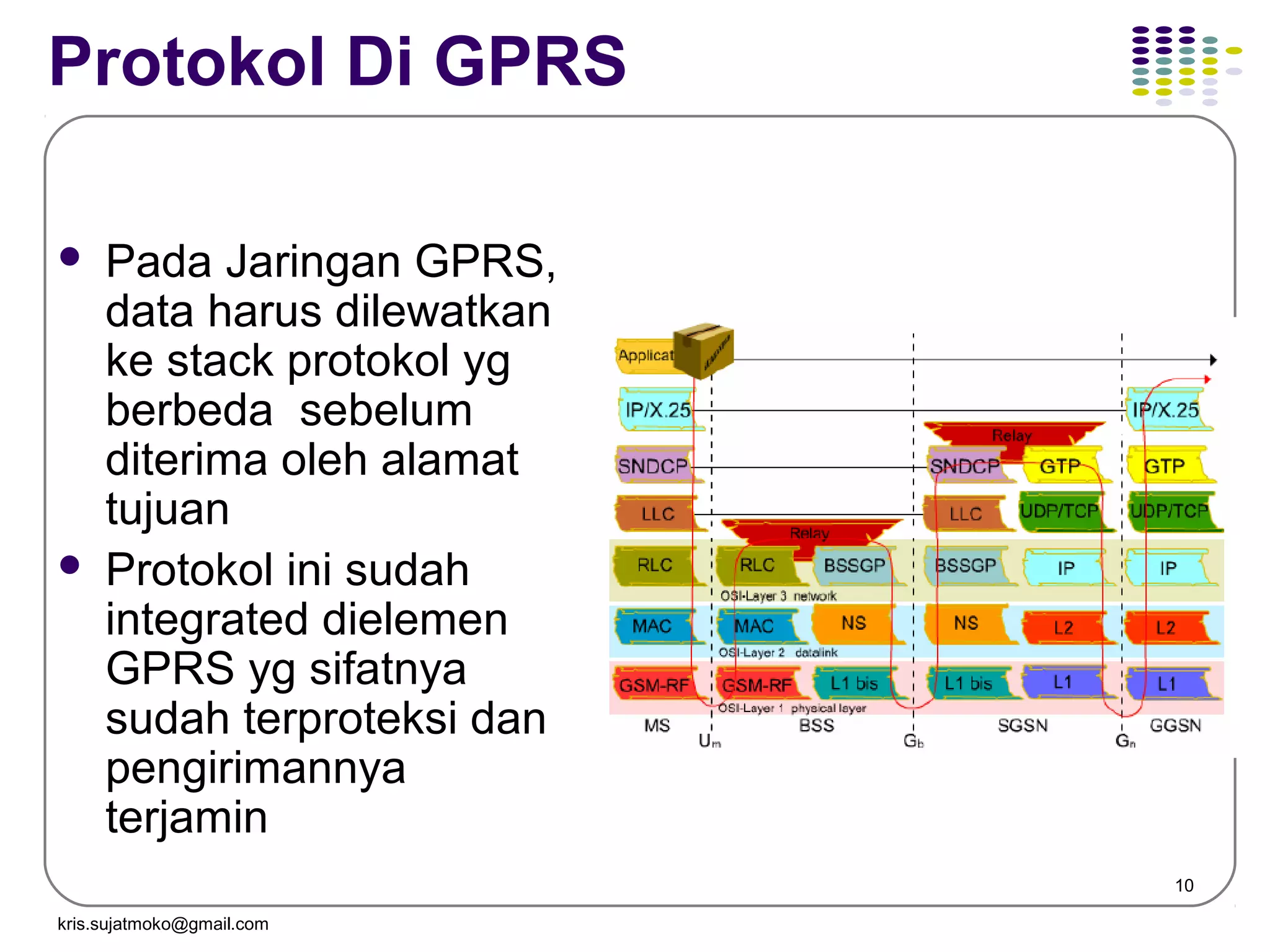
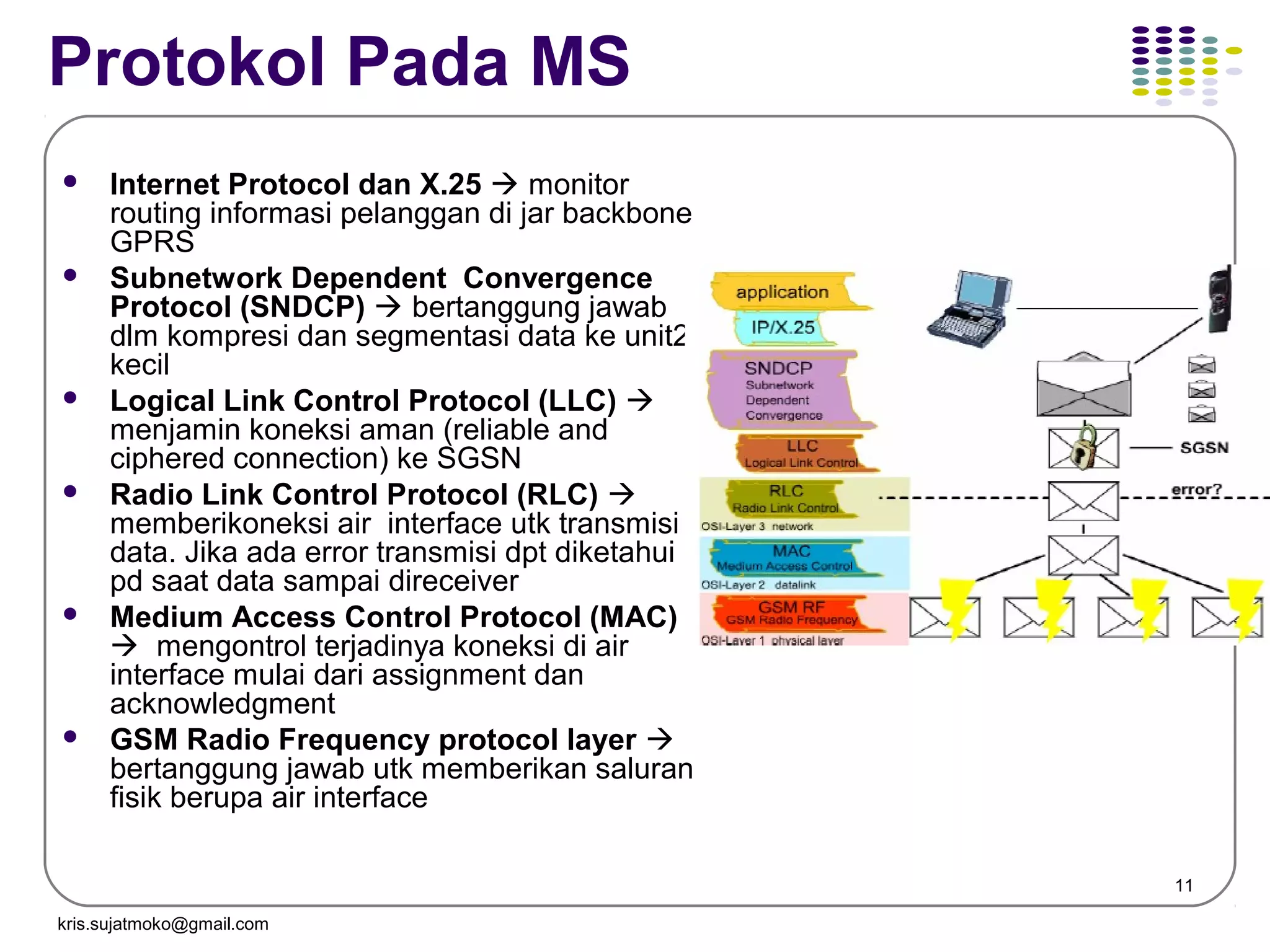
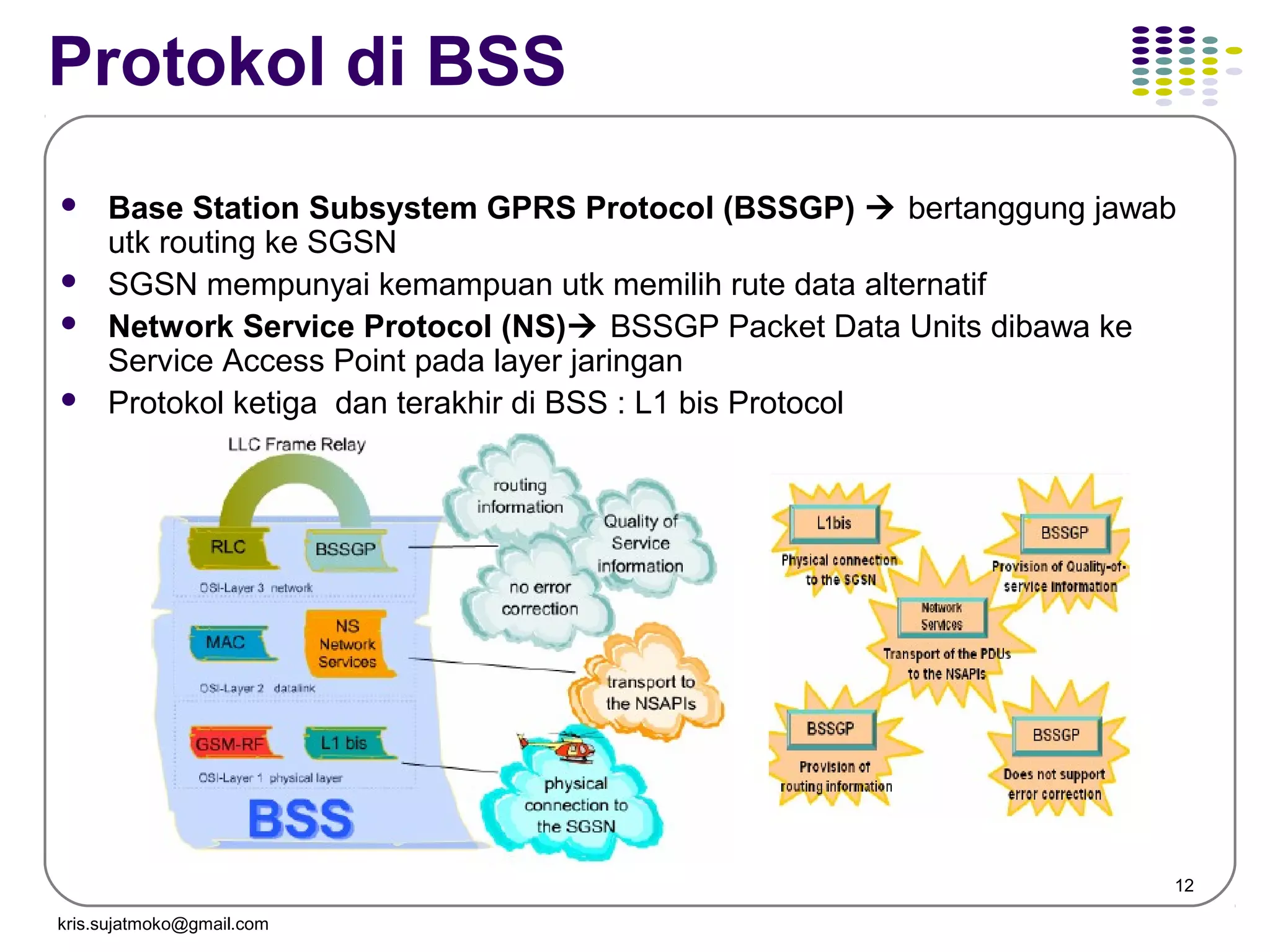
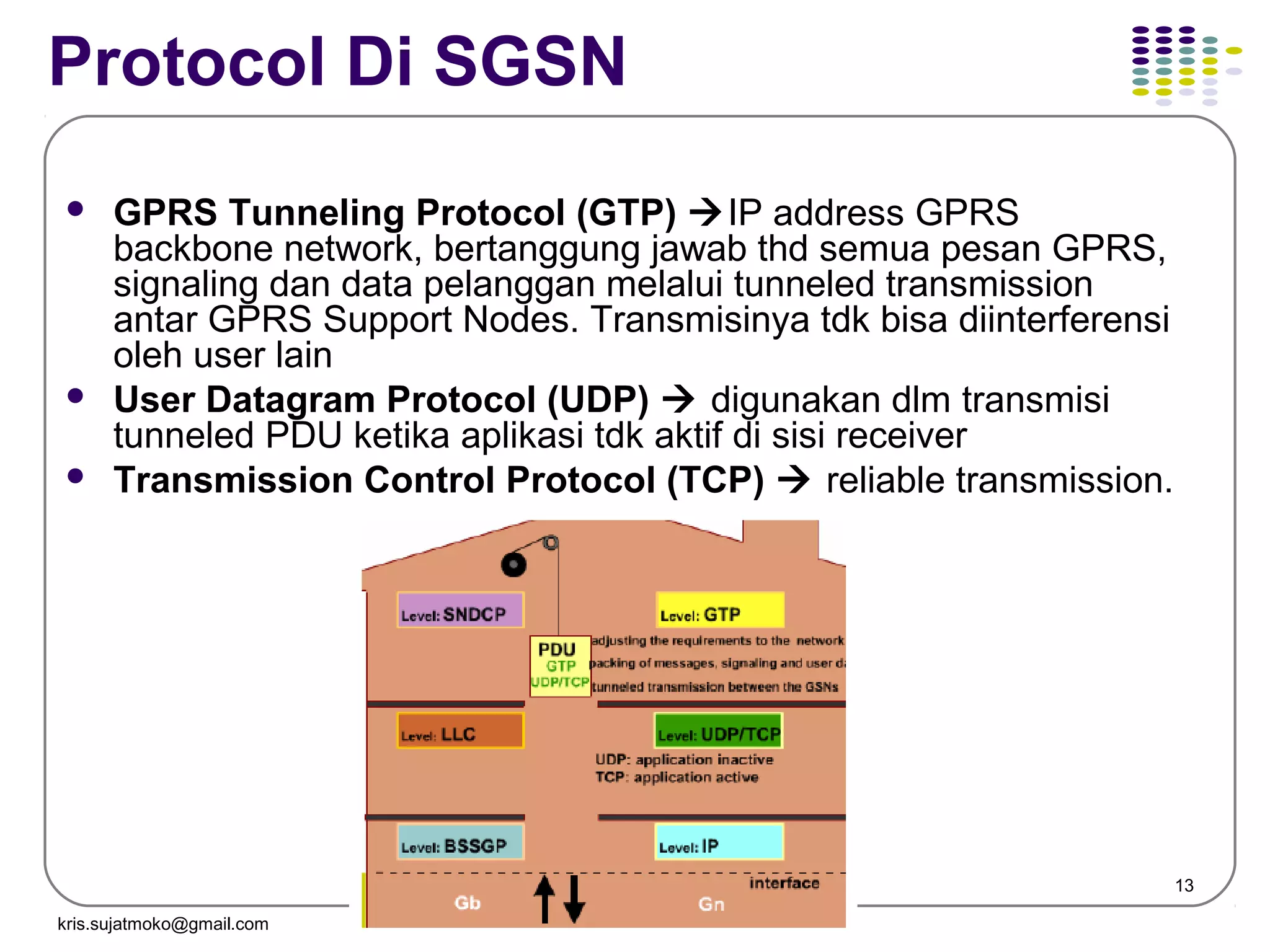
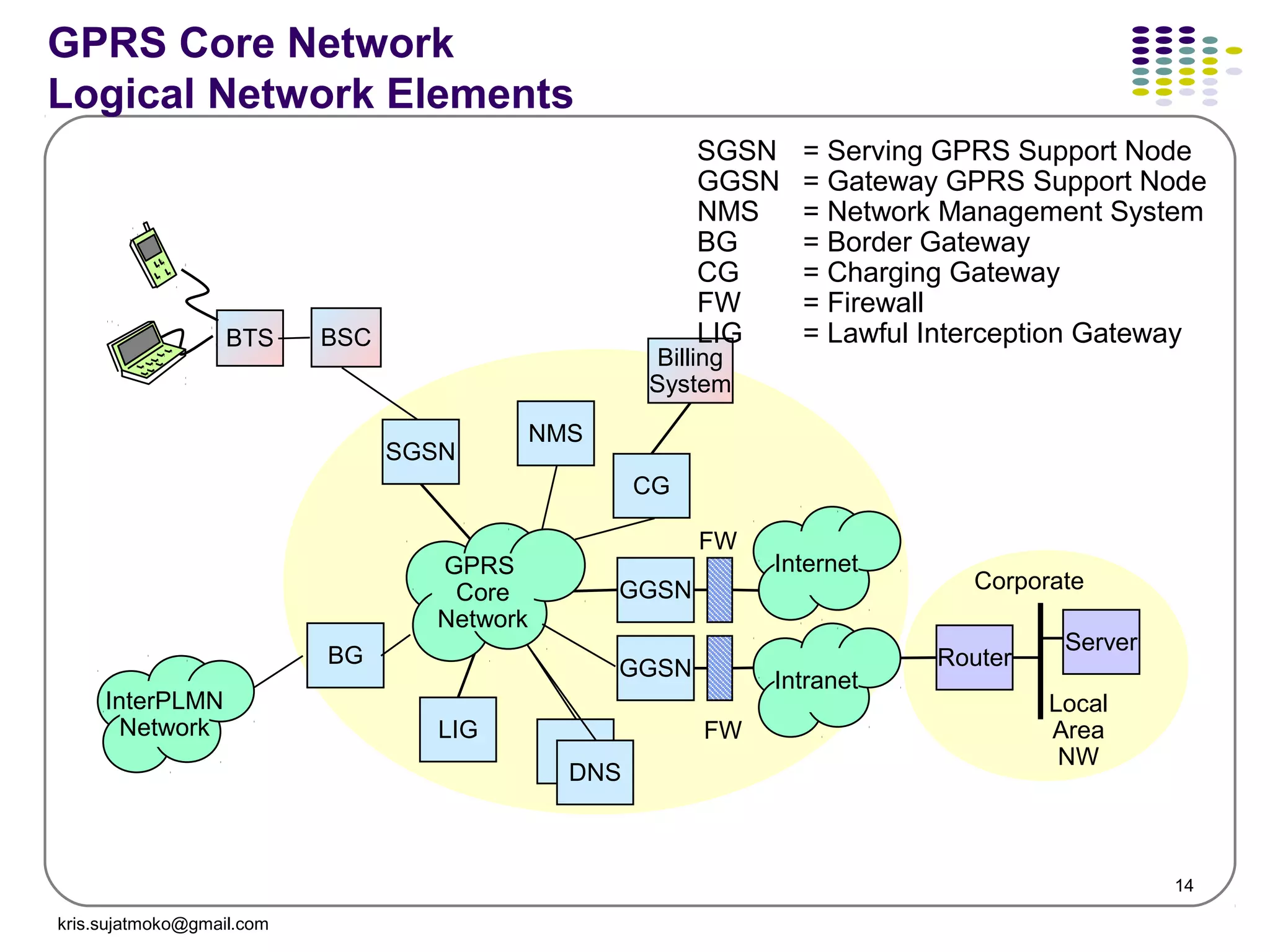
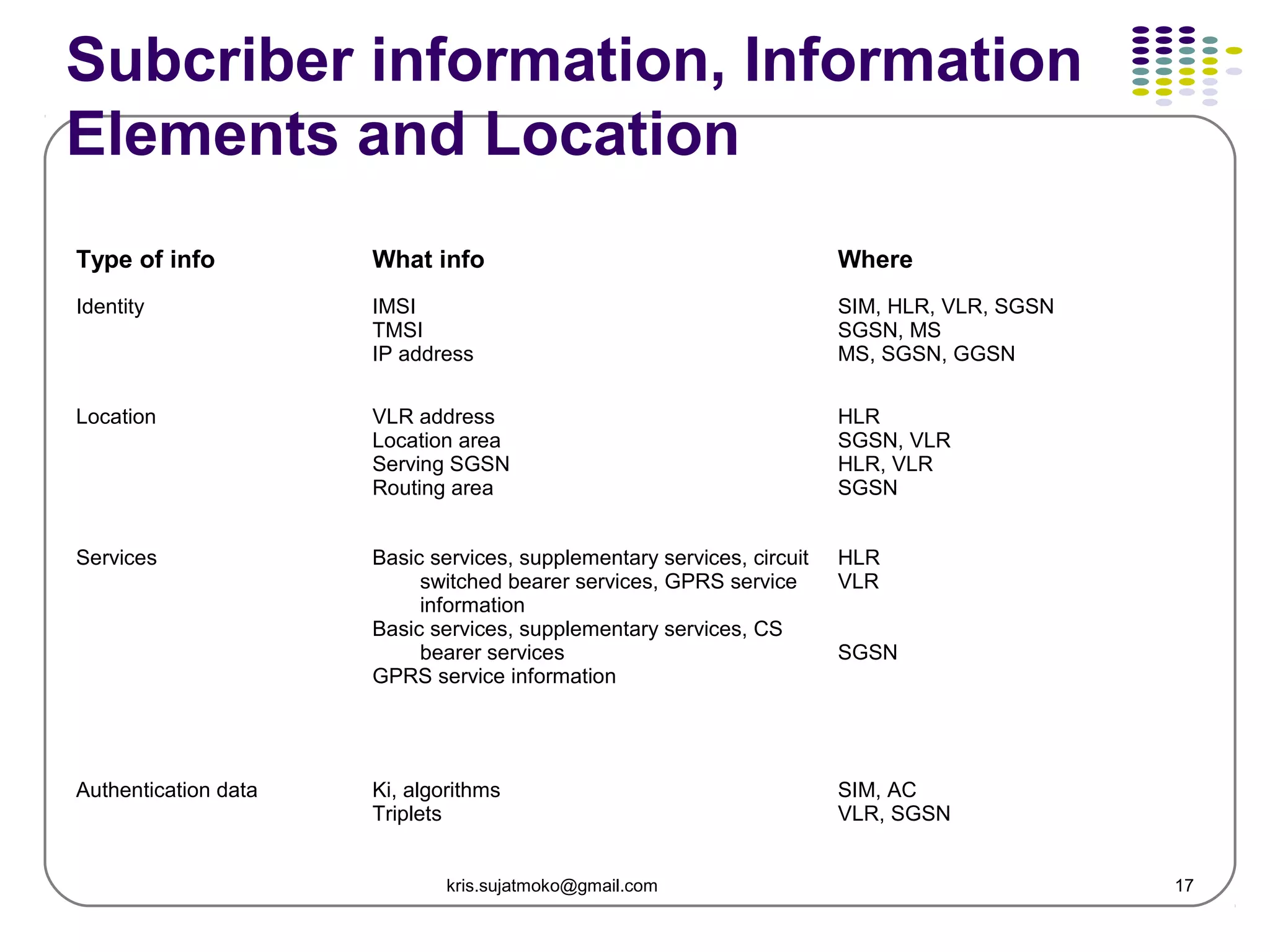
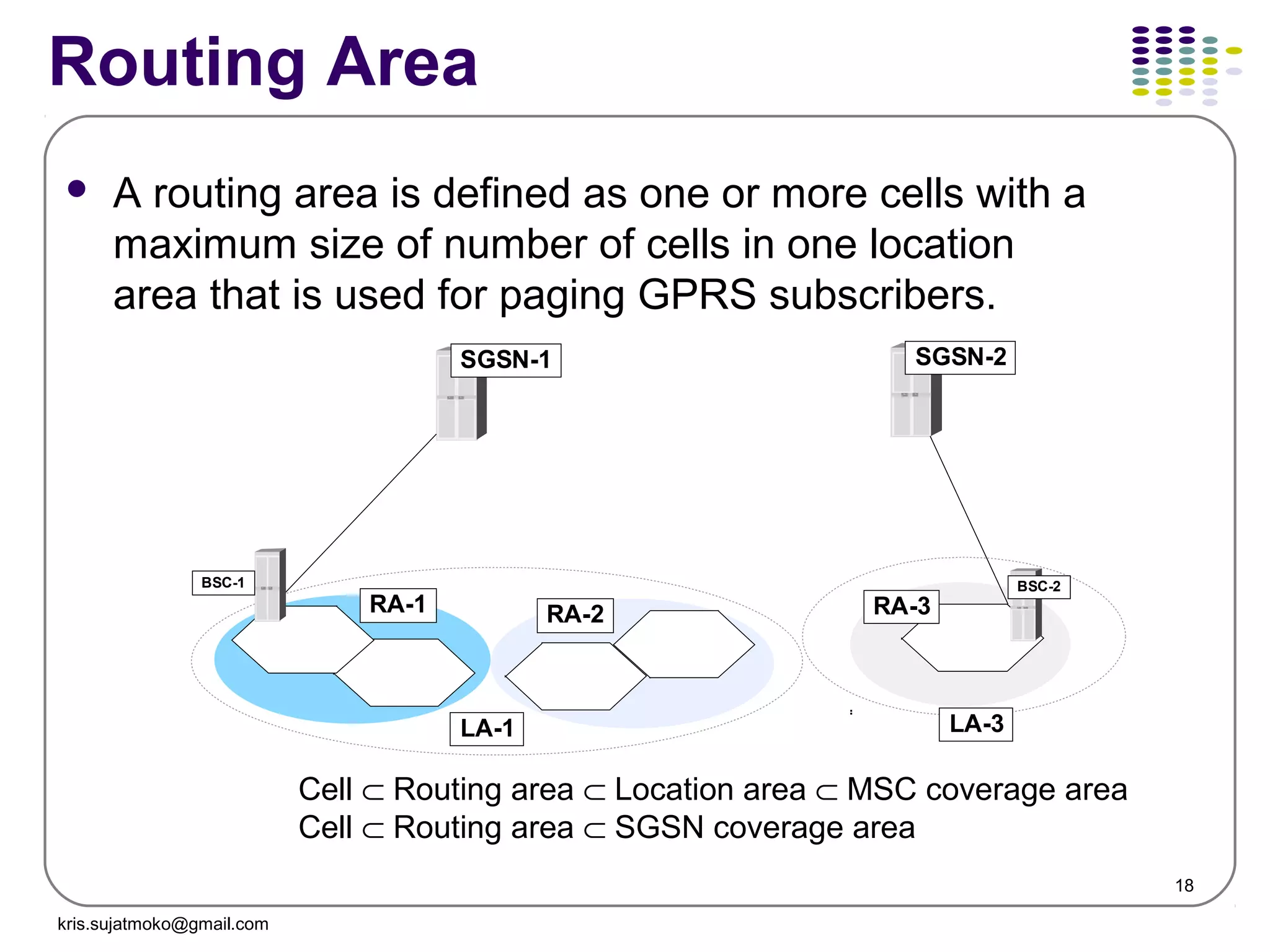
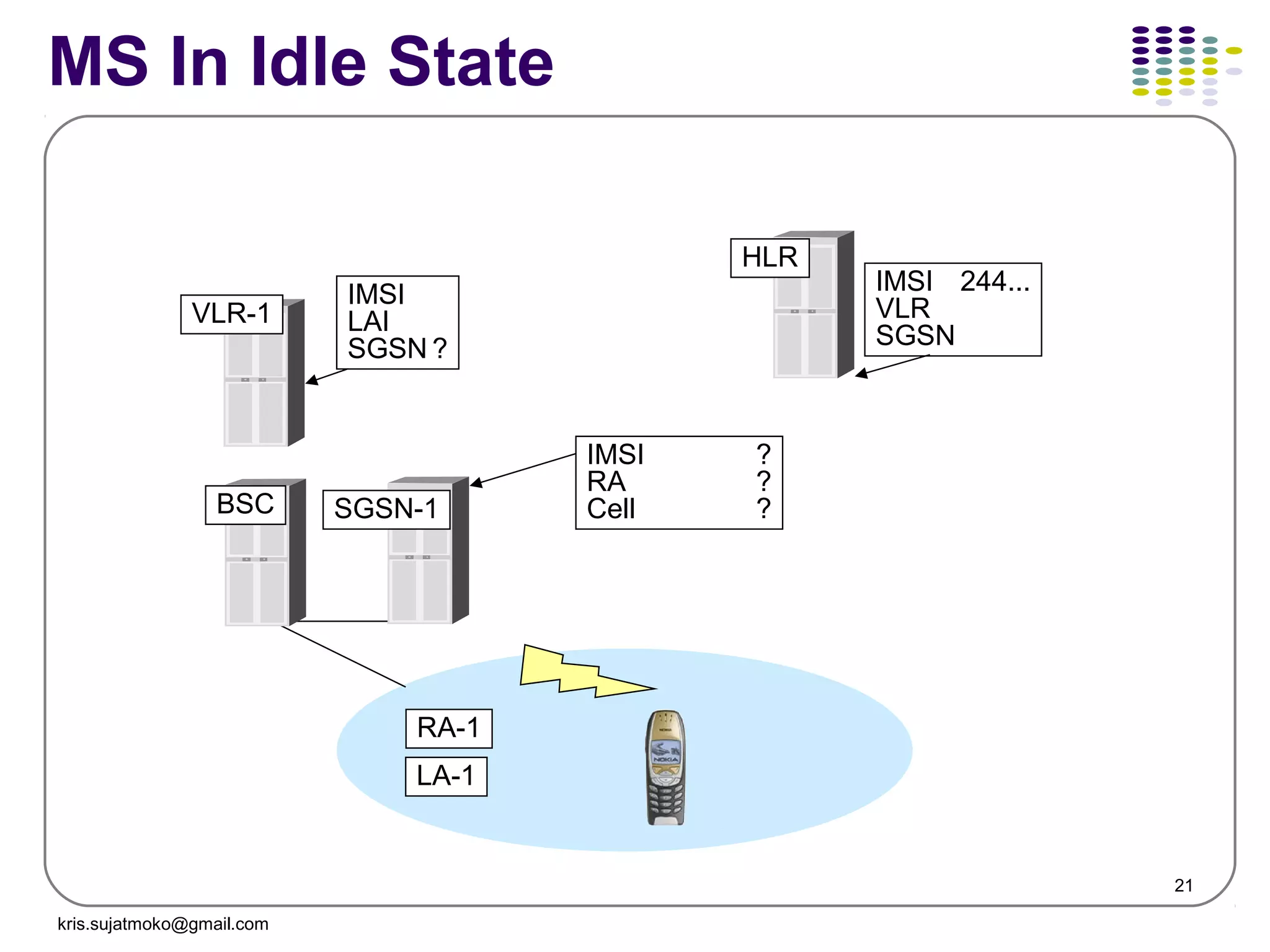
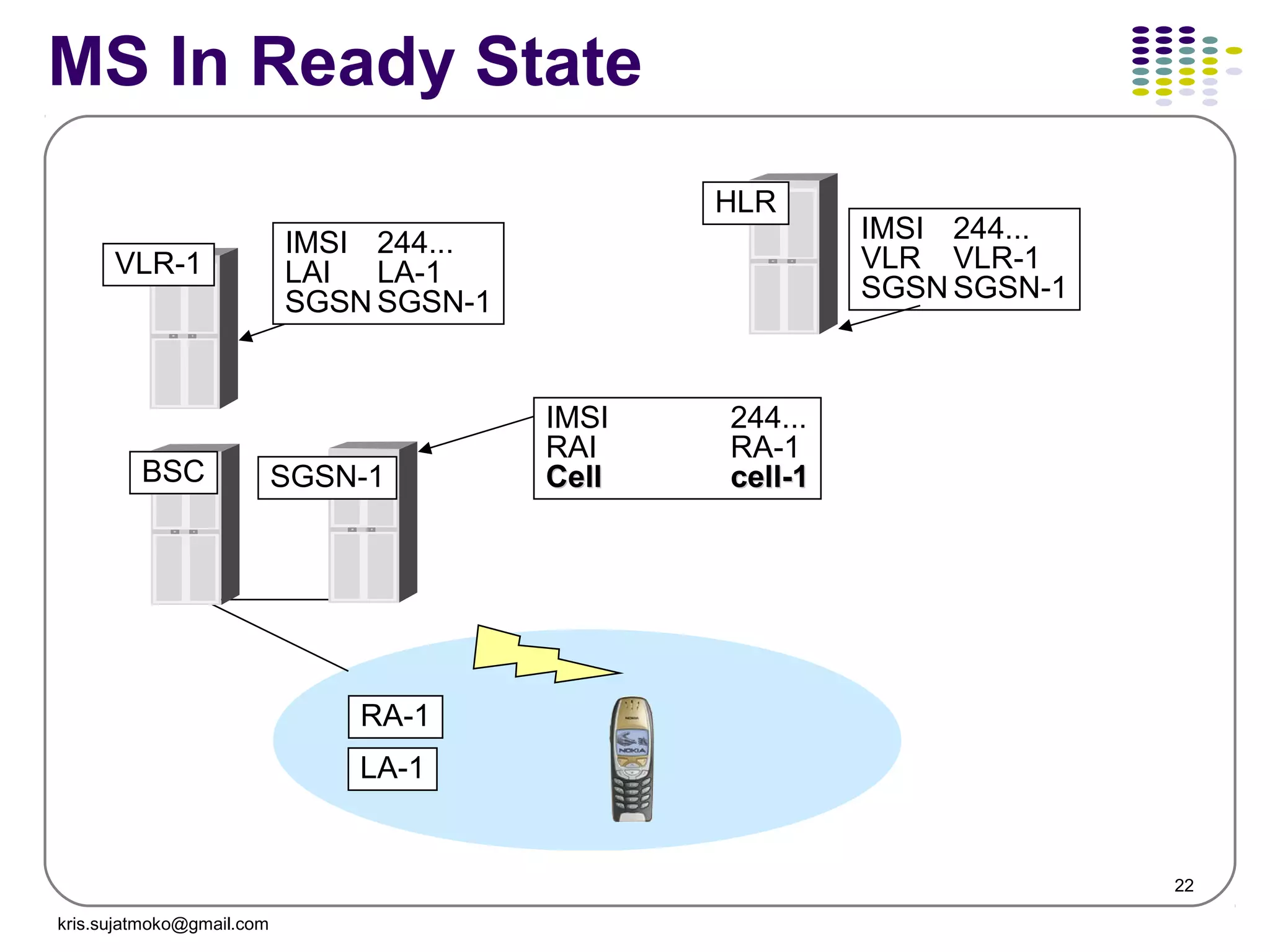
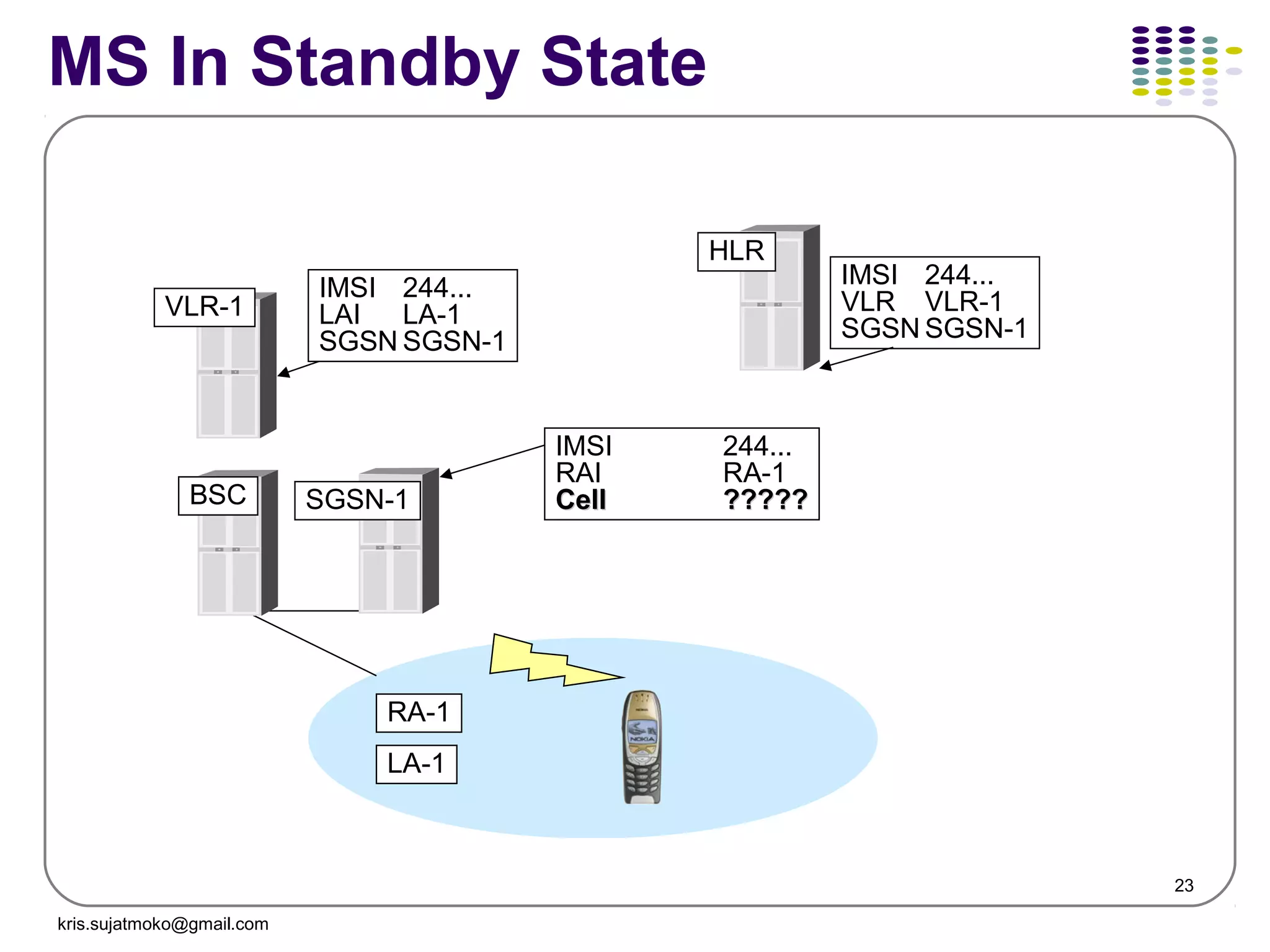
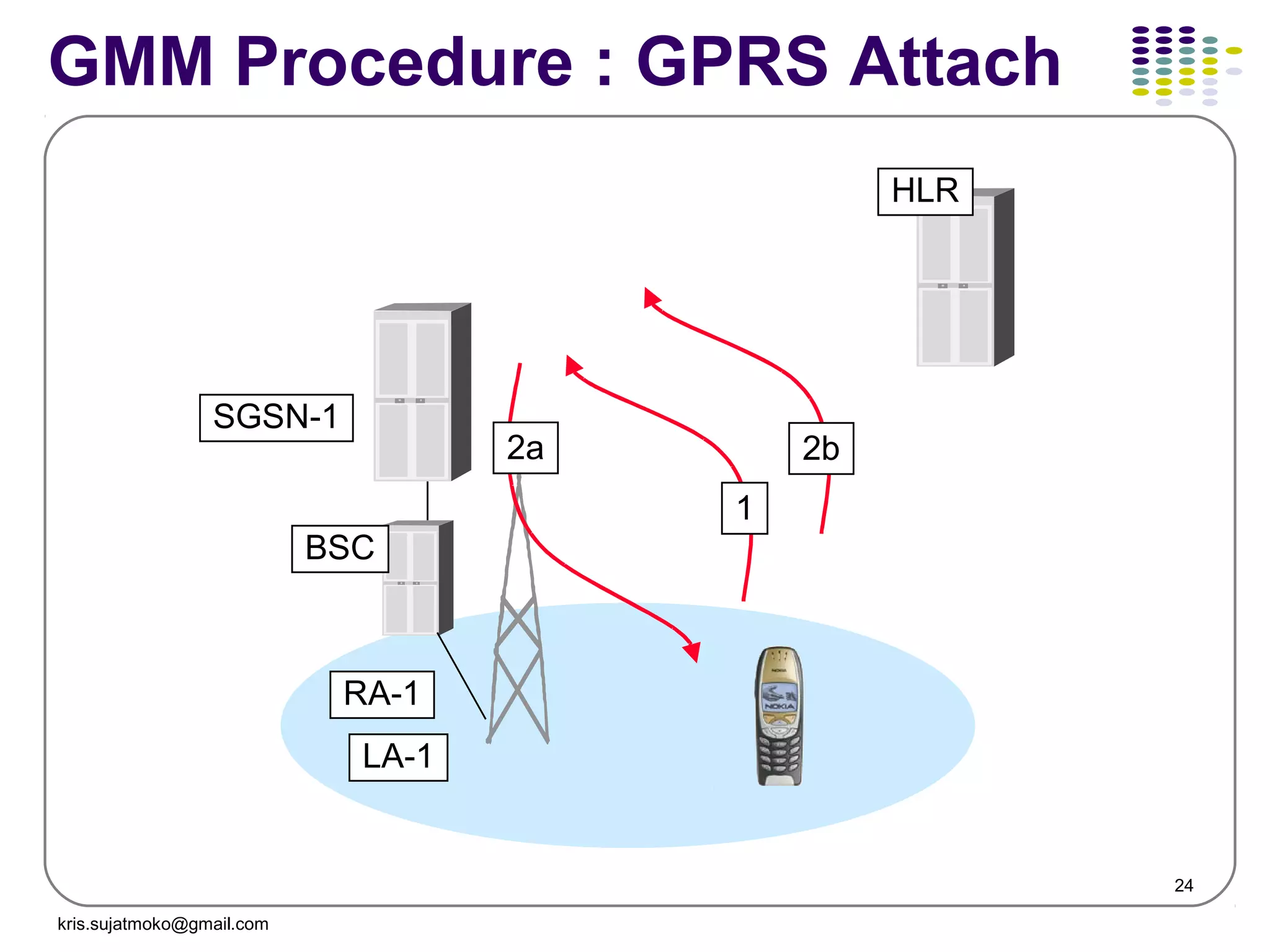
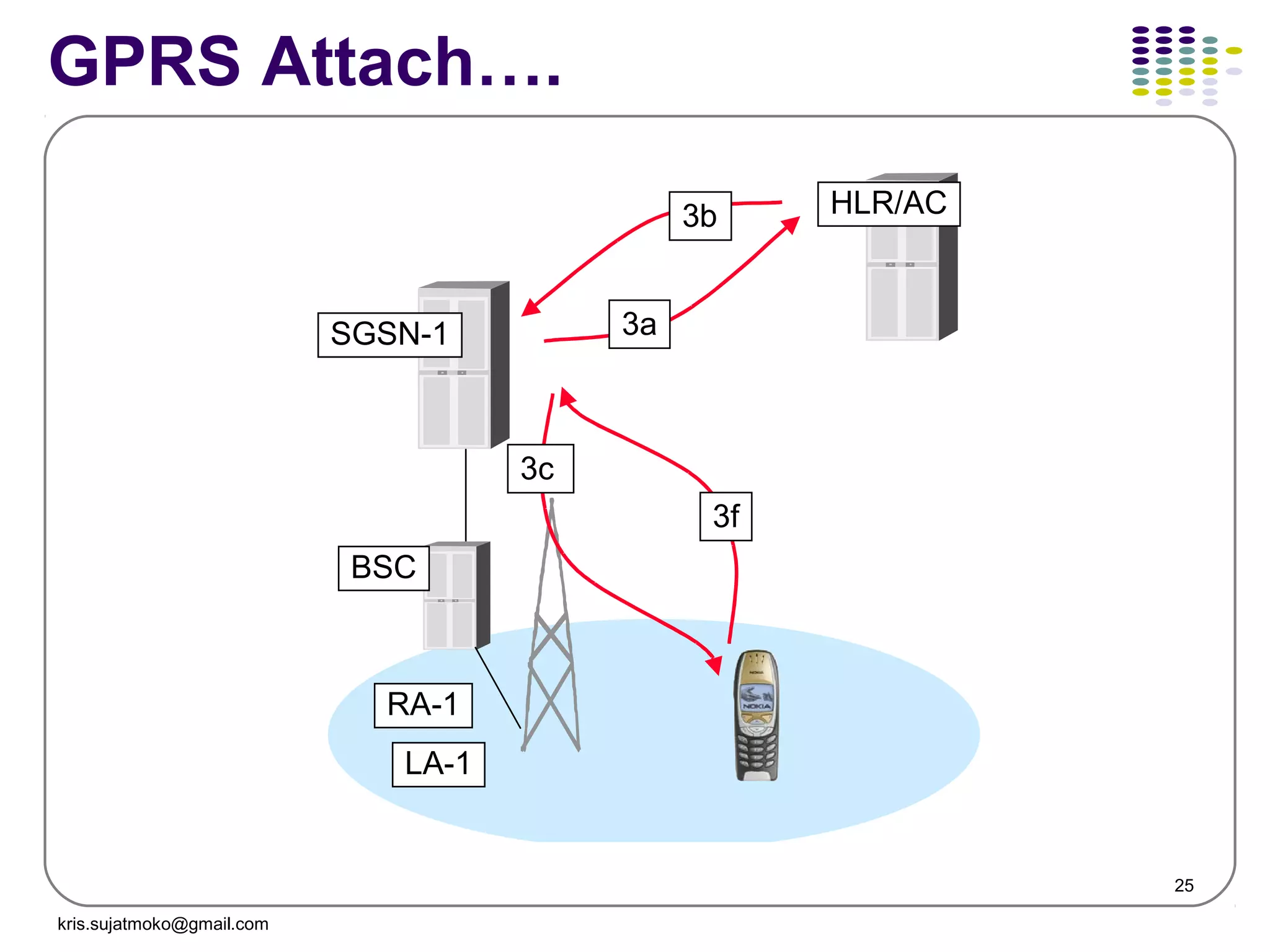
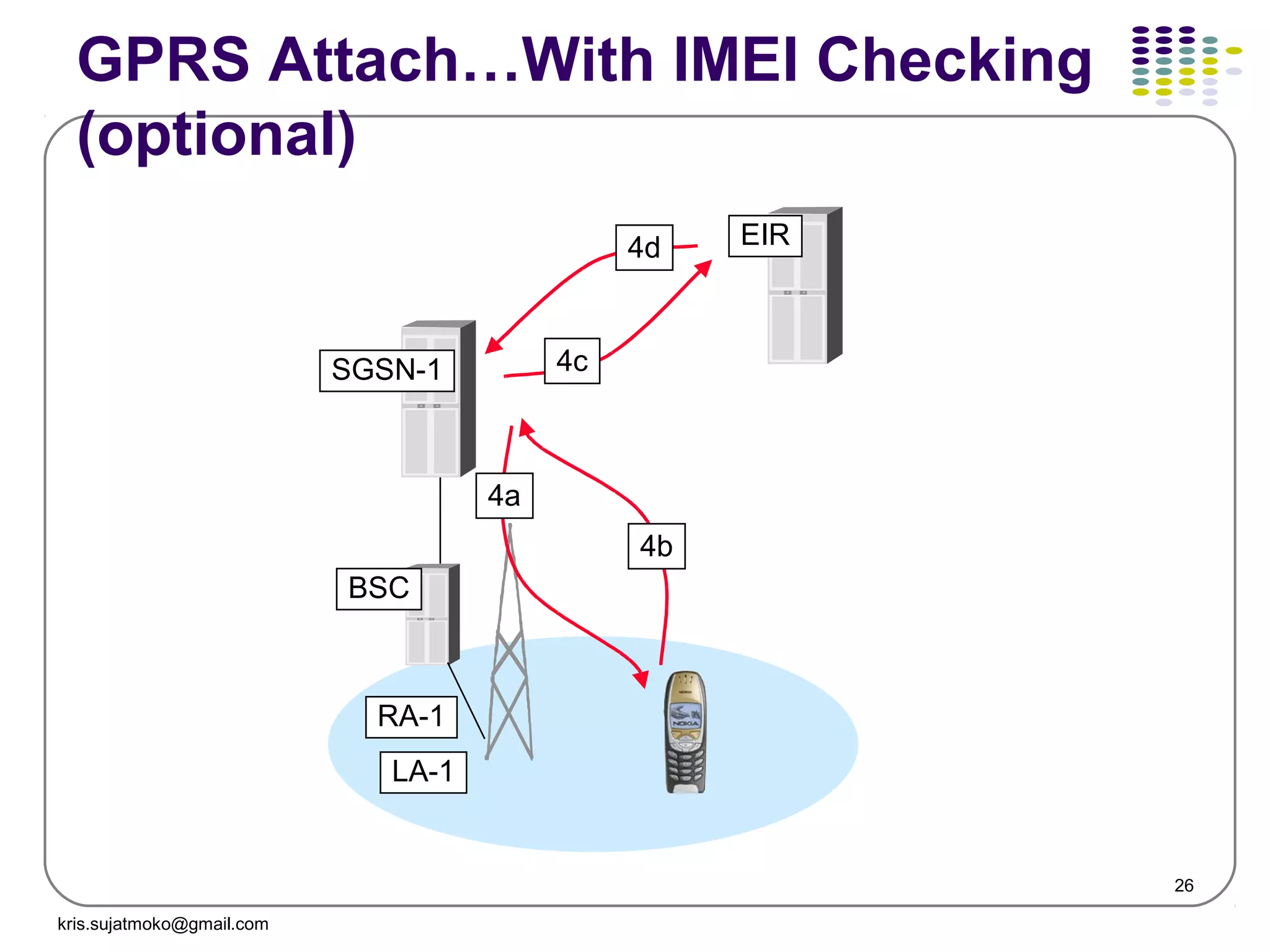
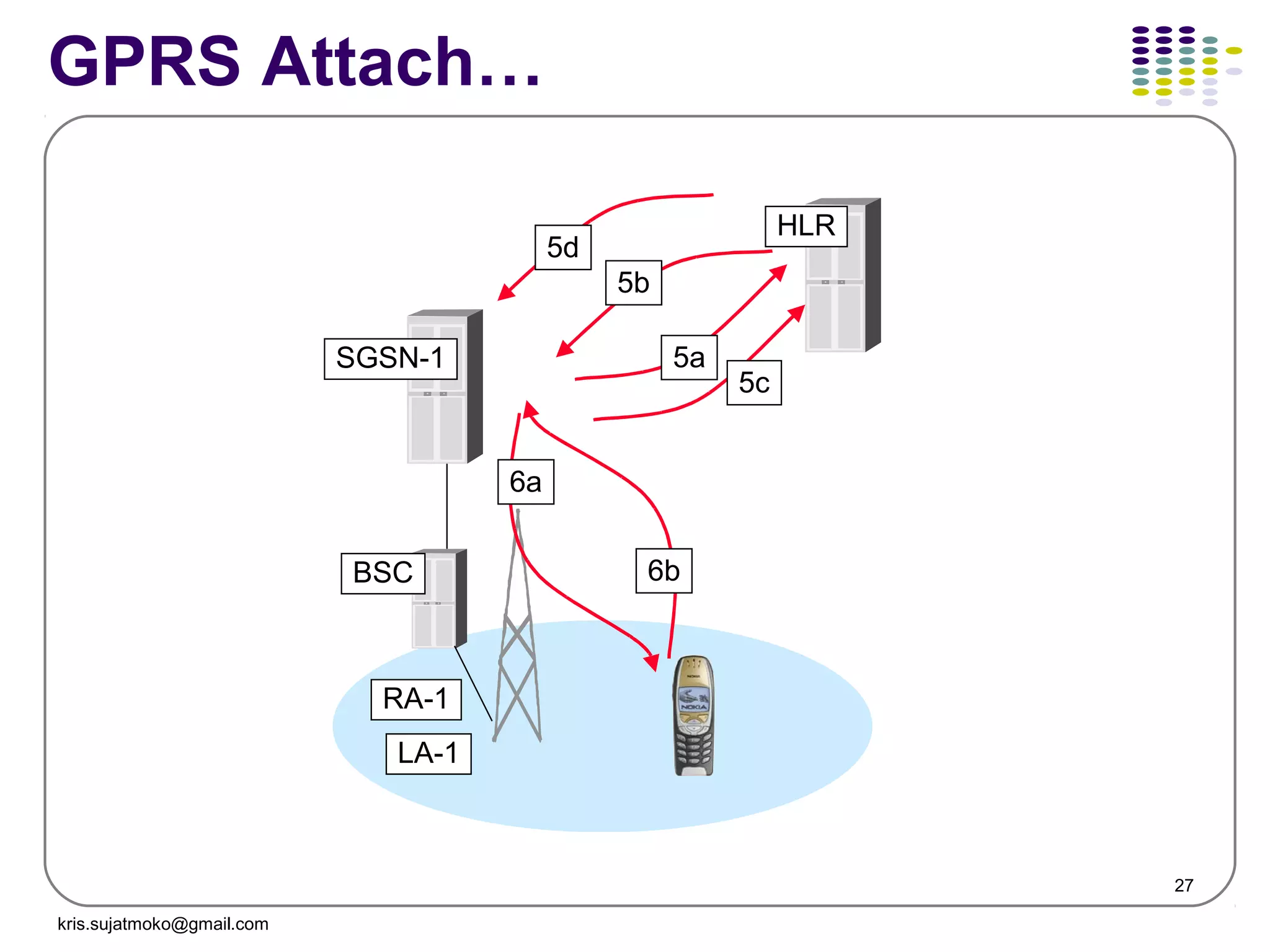
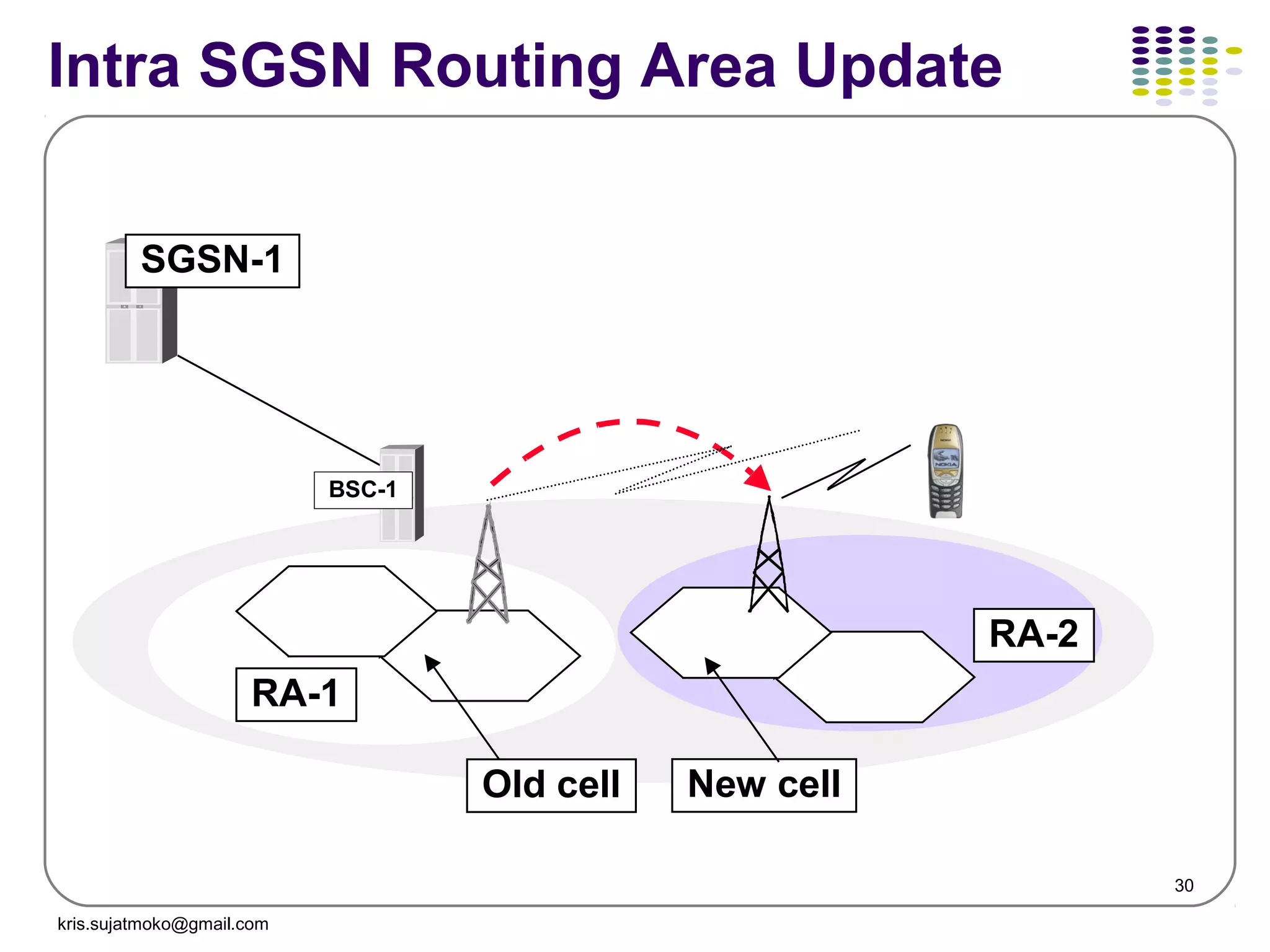
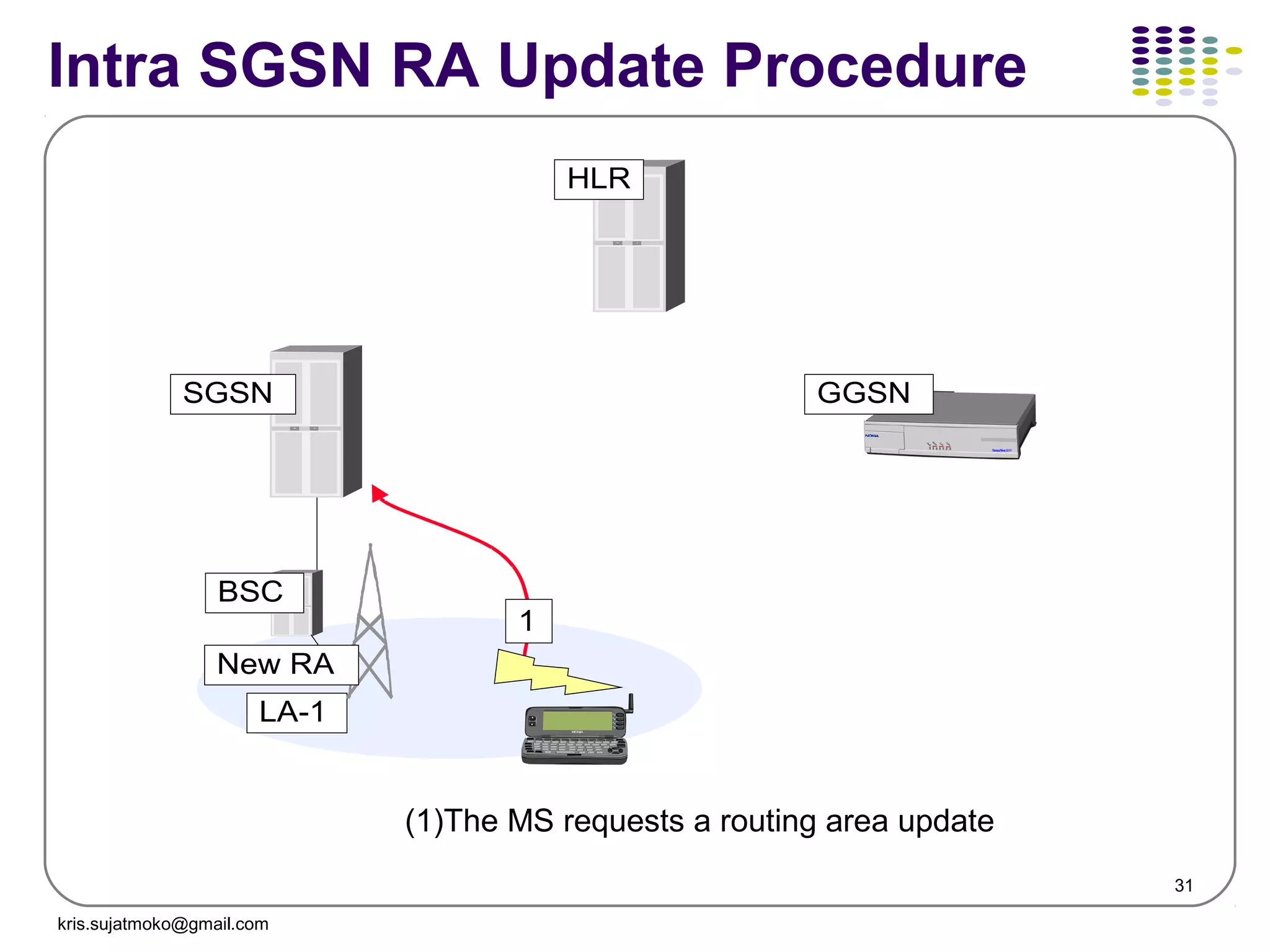
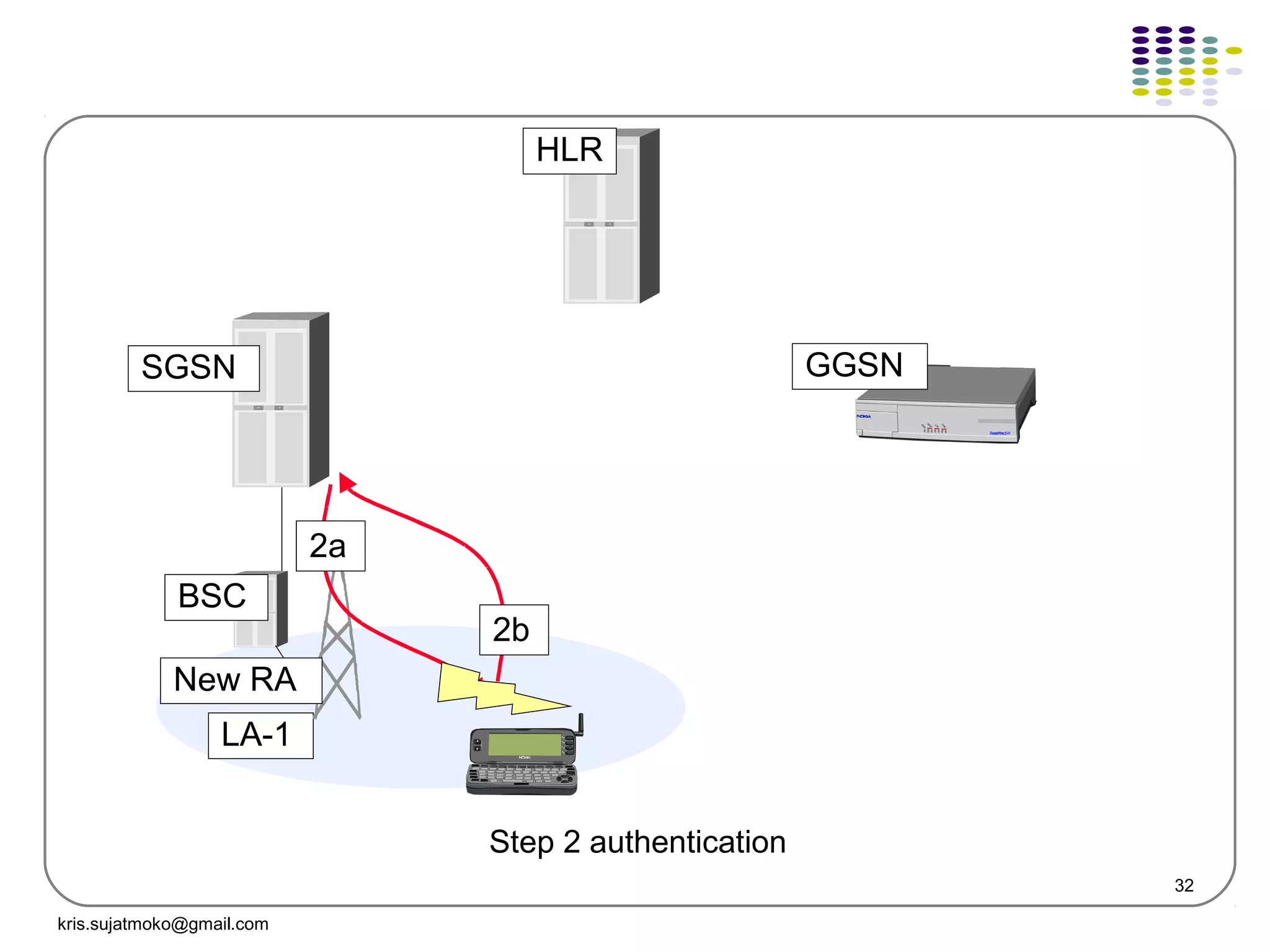
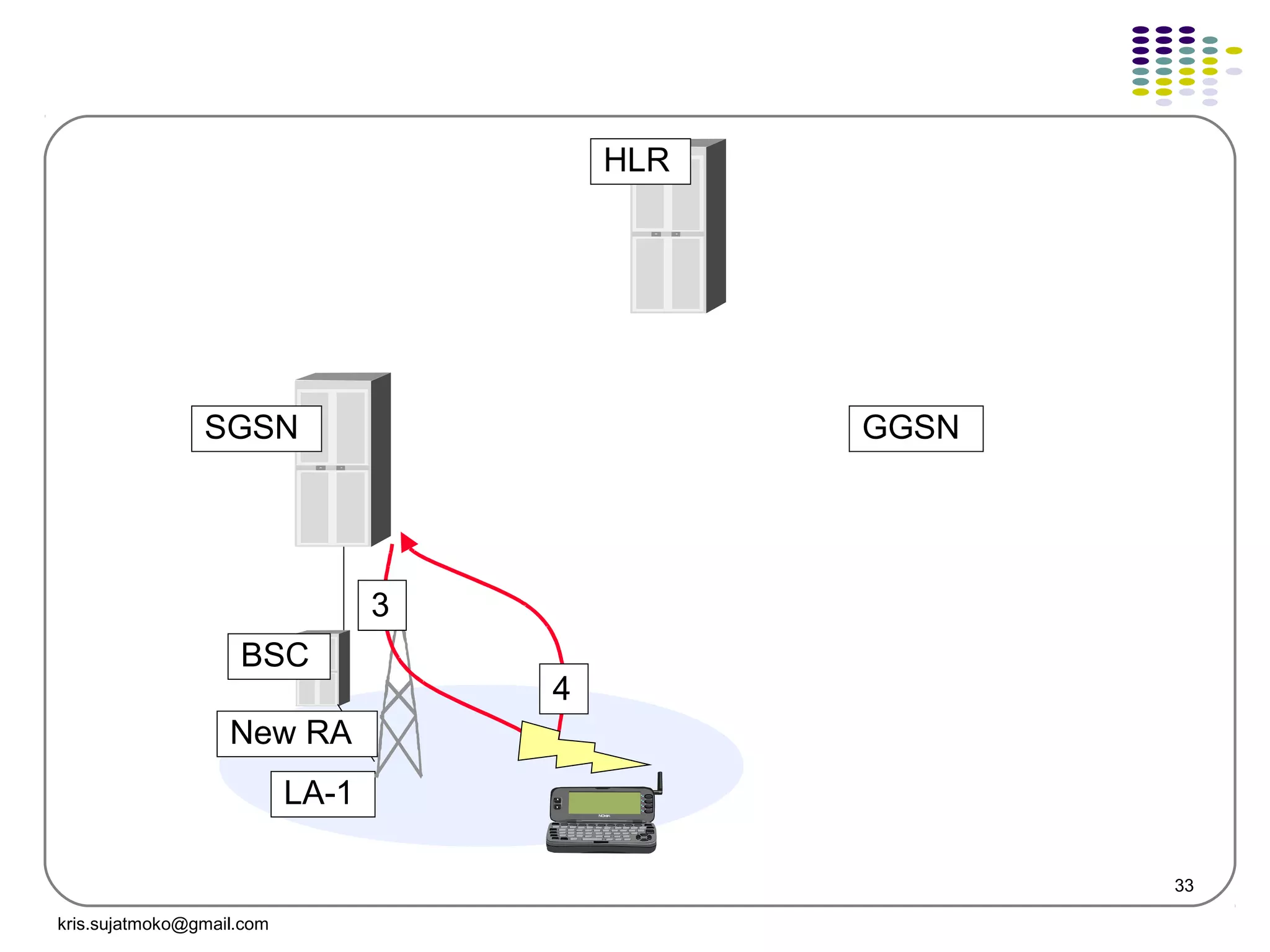
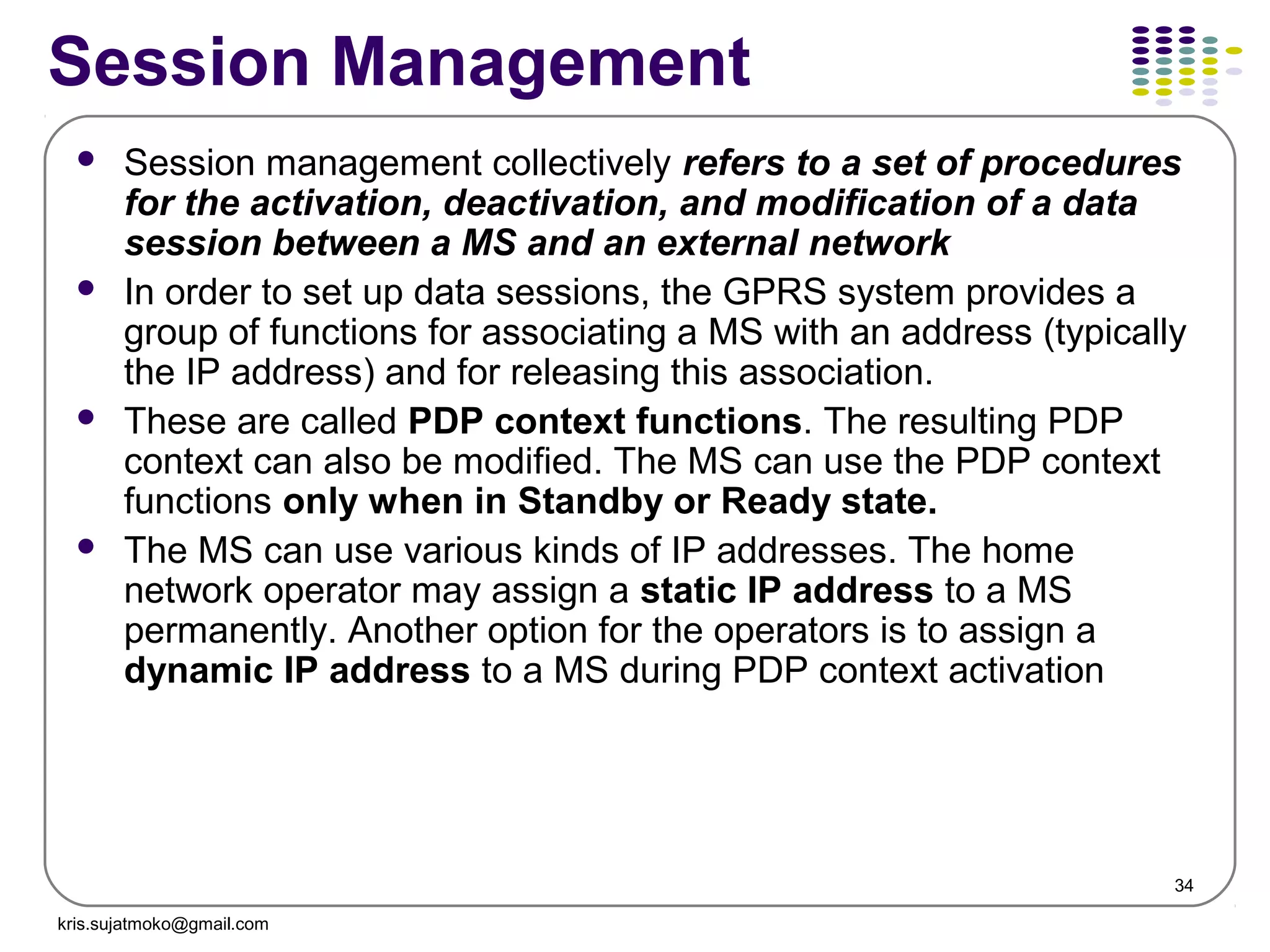
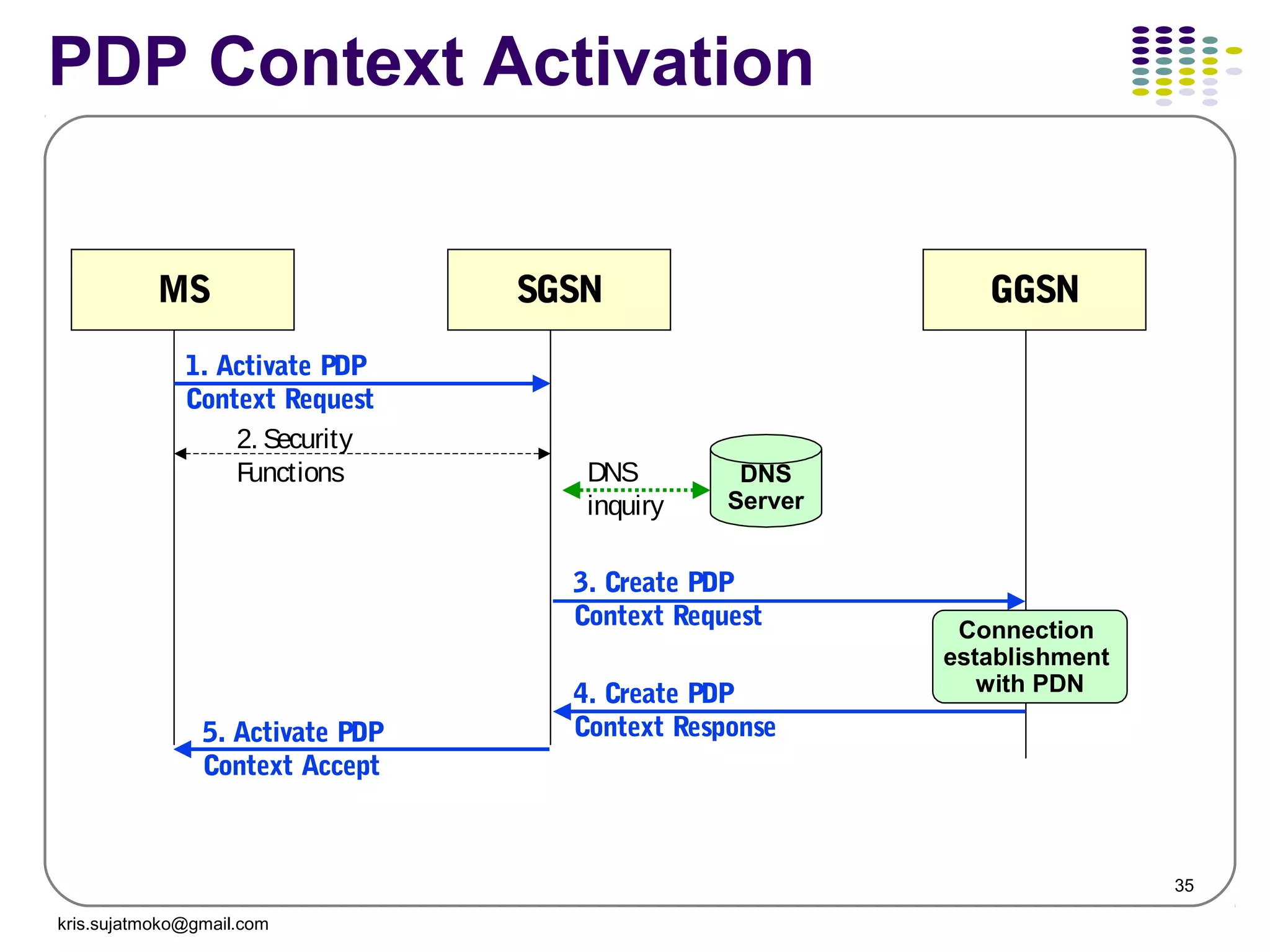
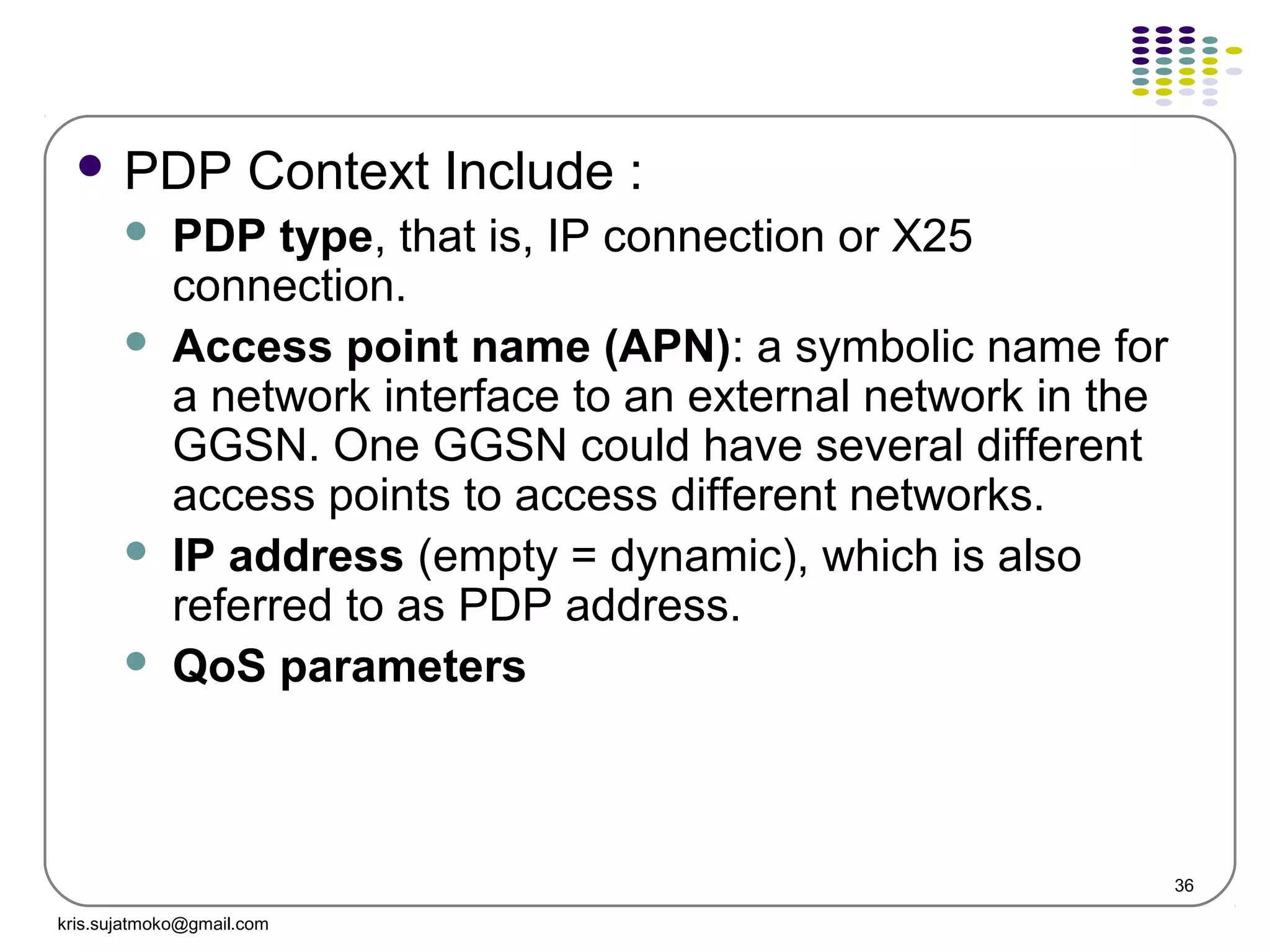
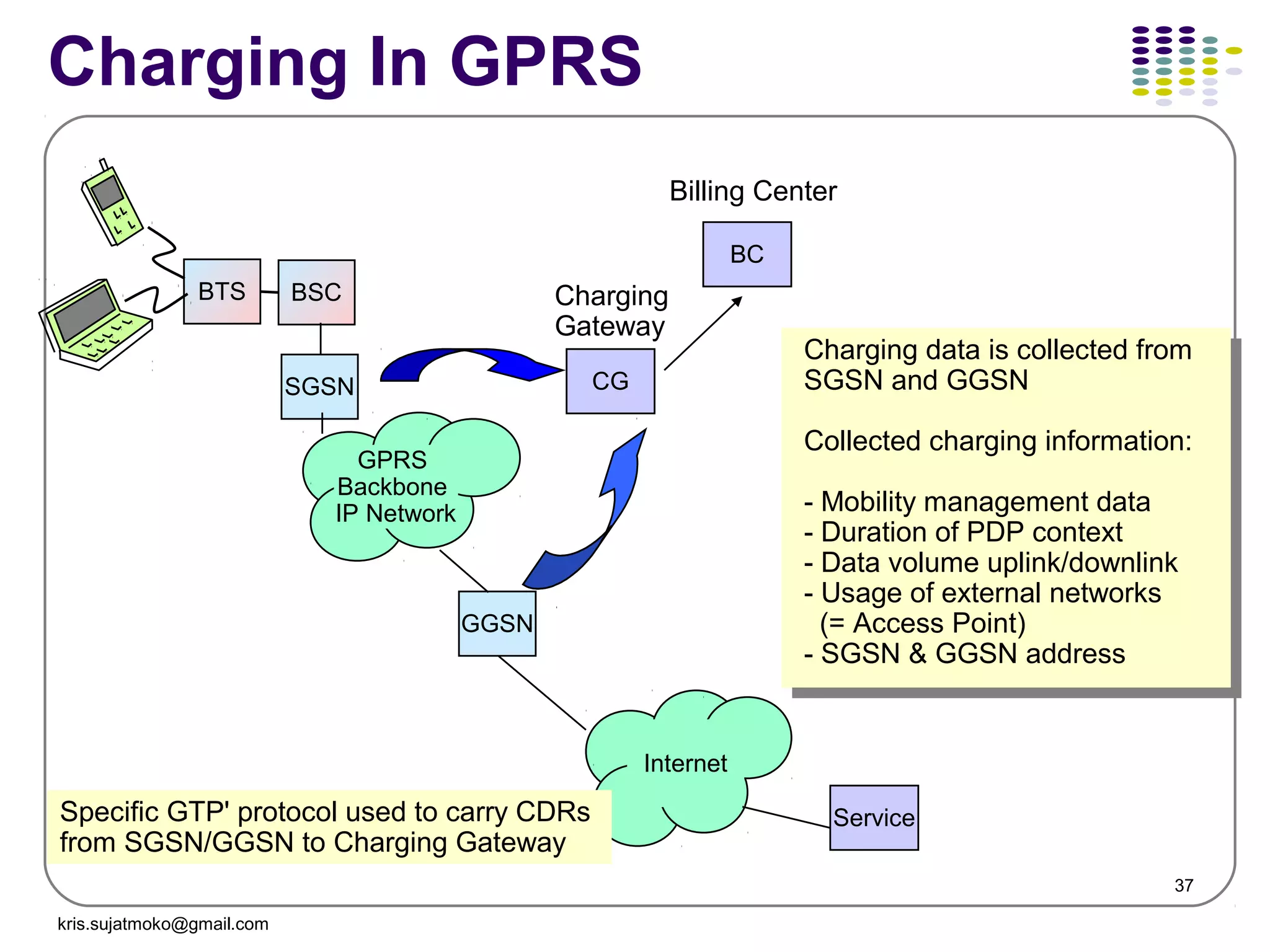
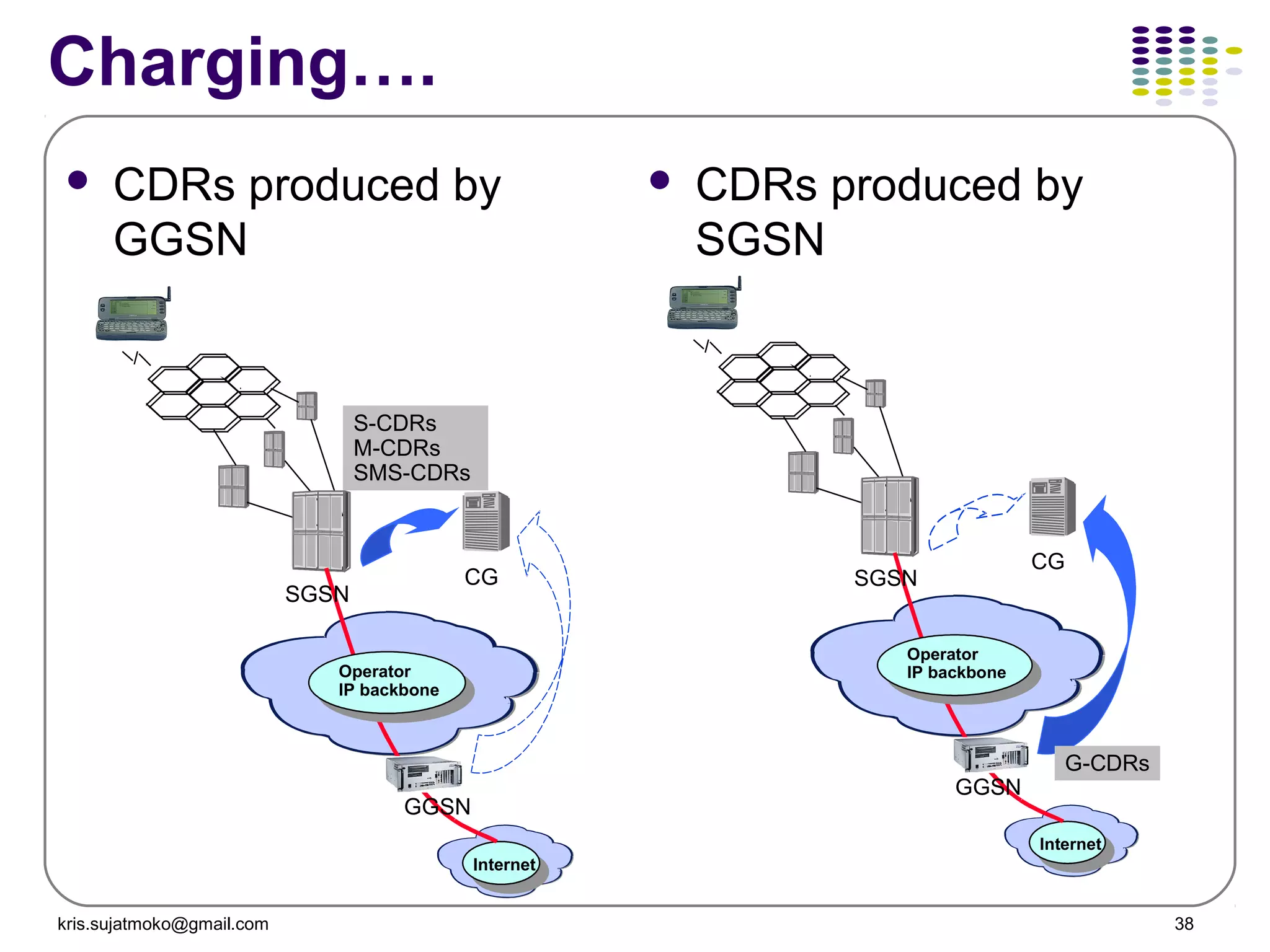
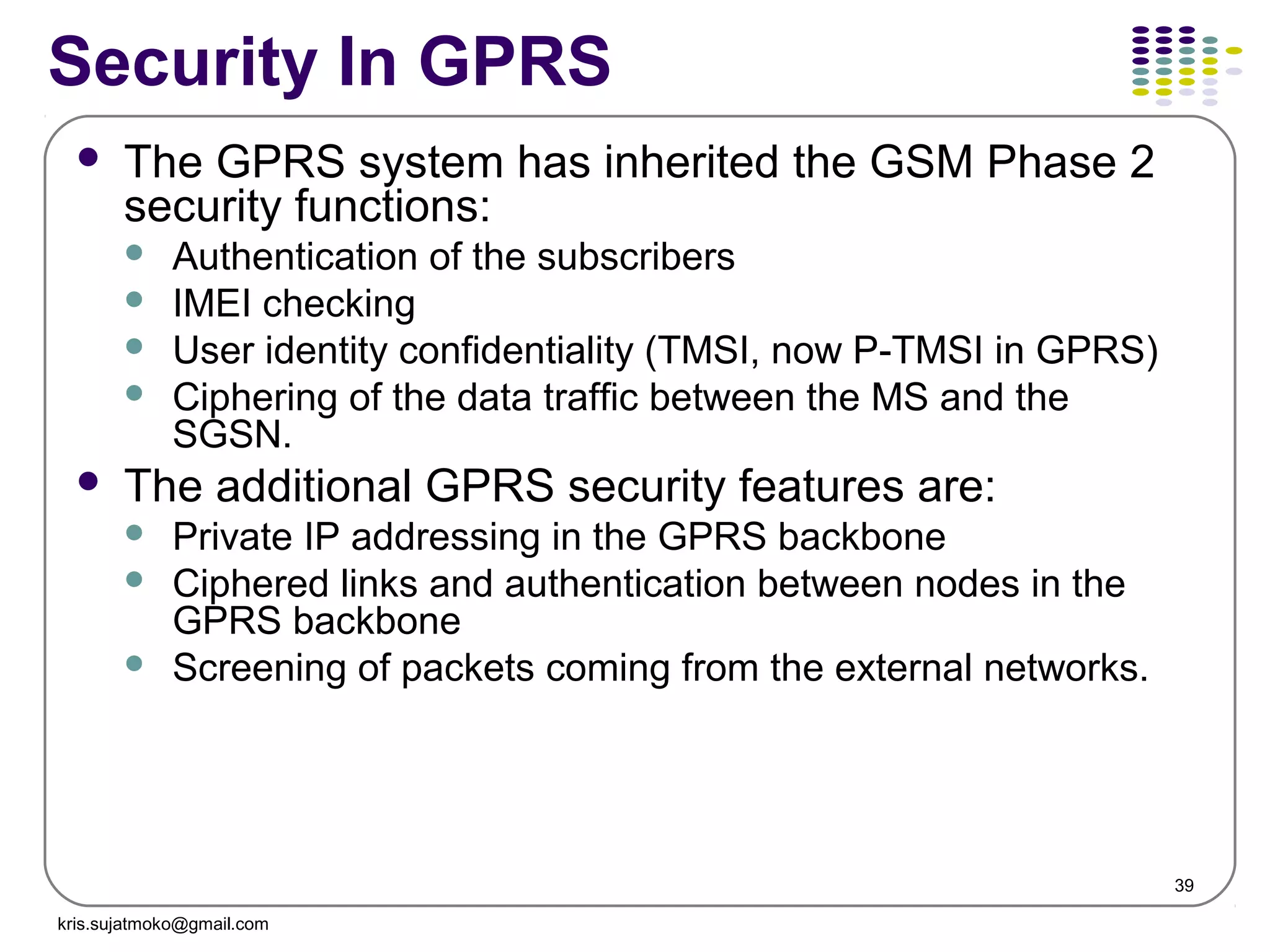
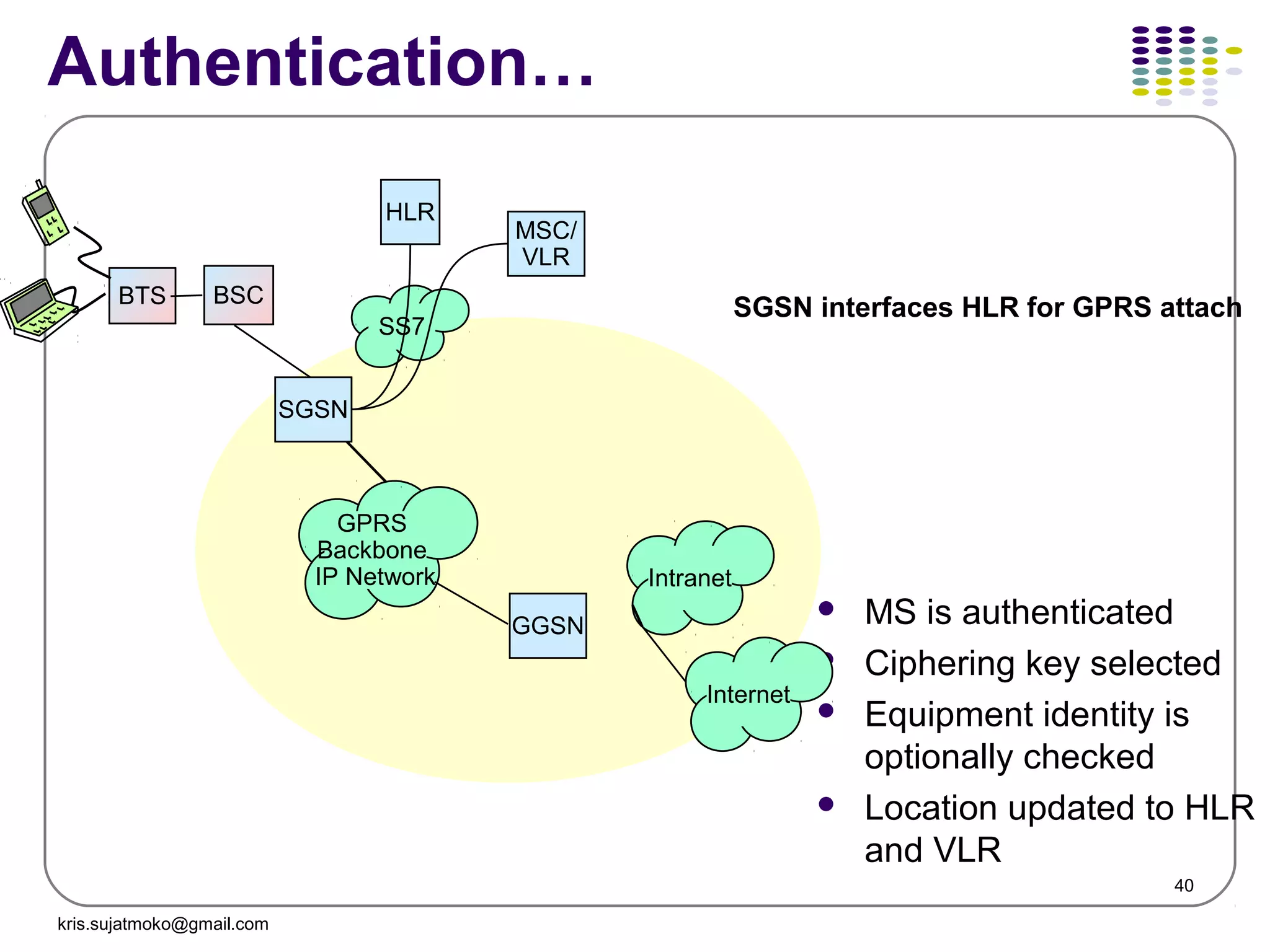
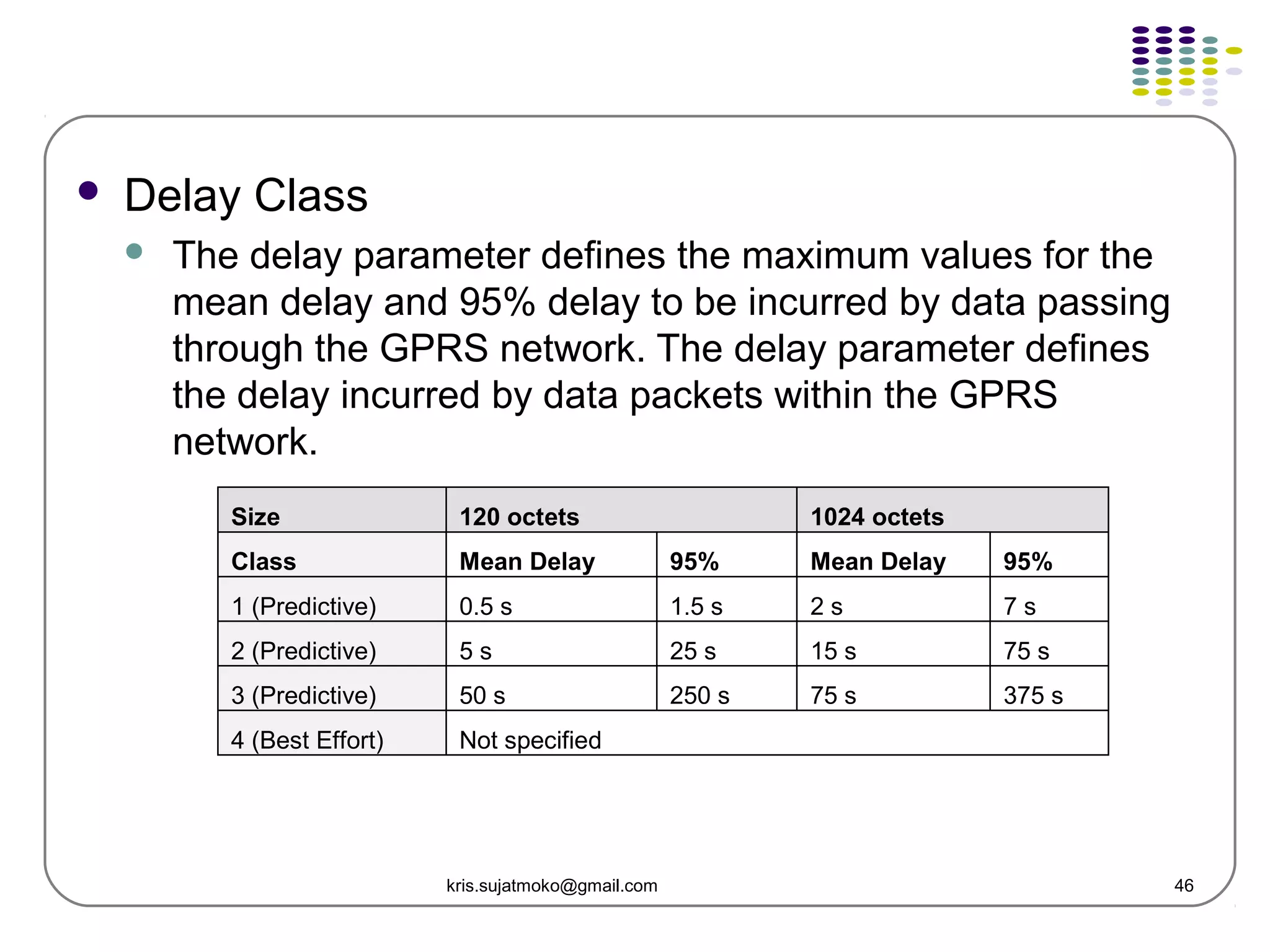
The document discusses GPRS operations and procedures. It provides an overview of GPRS architecture, protocols used in GPRS, mobility management procedures like GPRS attach and routing area update, and location management in GPRS. Diagrams are included to illustrate logical architecture, data transfer between network elements, and mobility states of a GPRS mobile station.