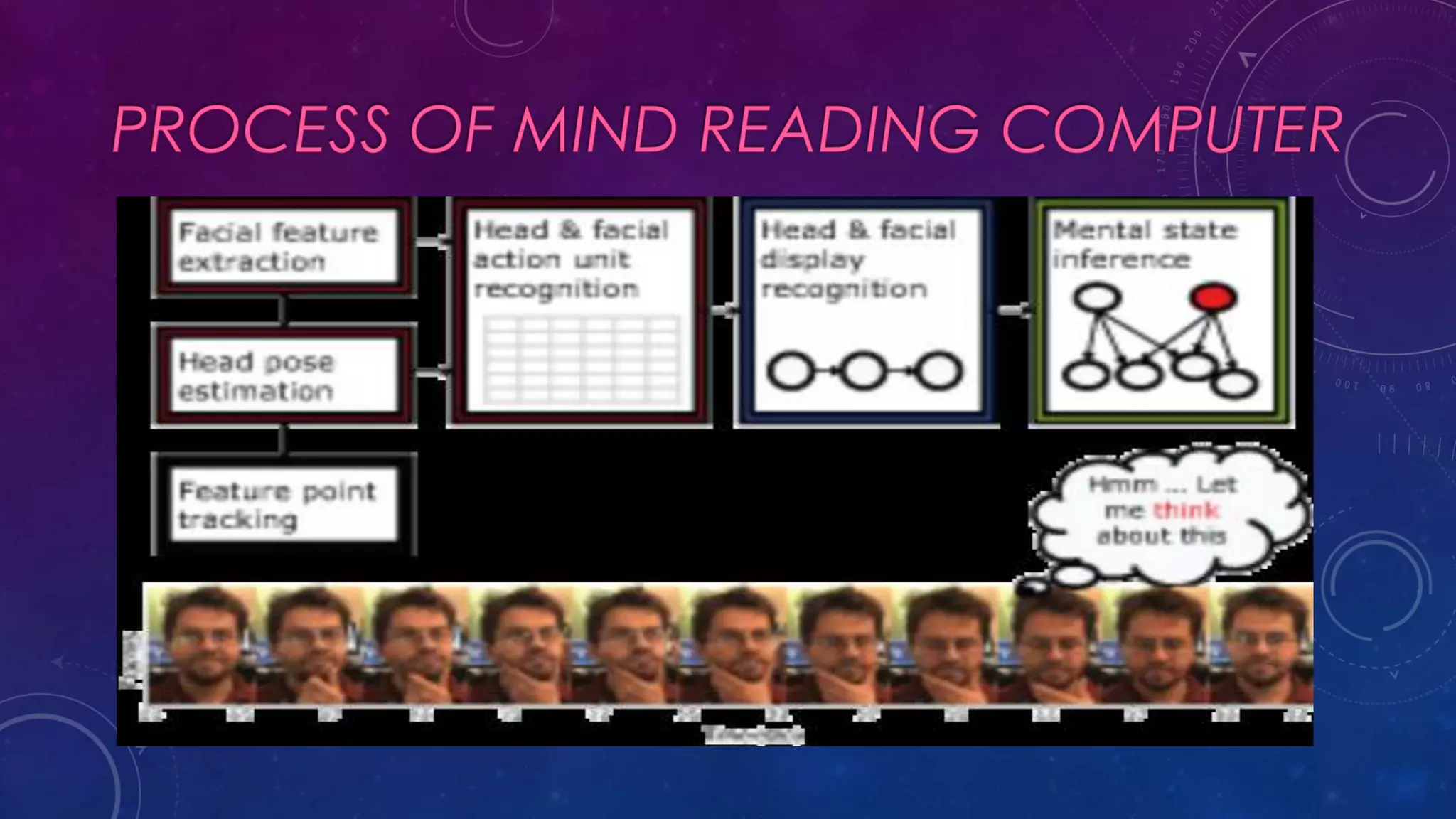
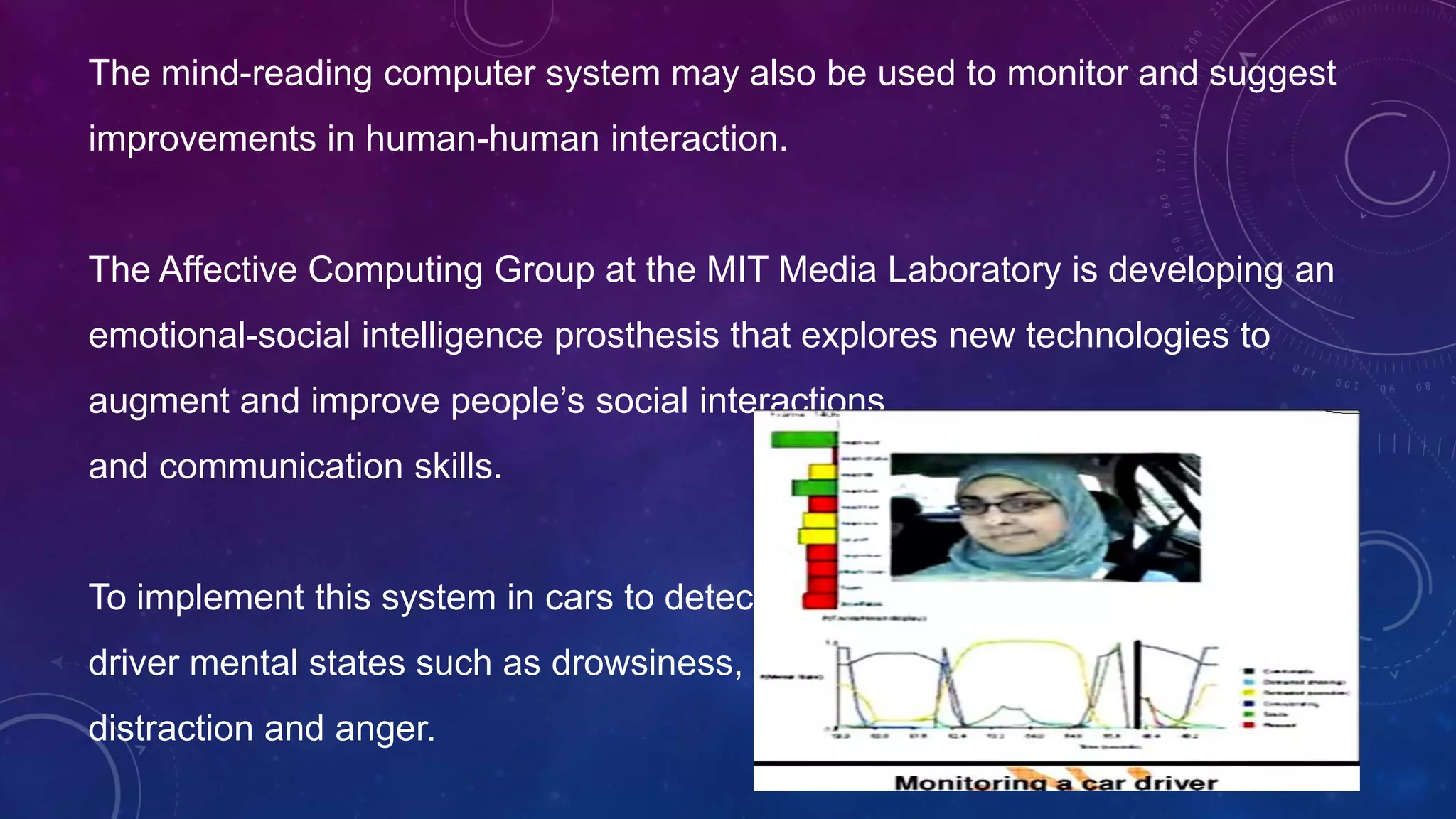
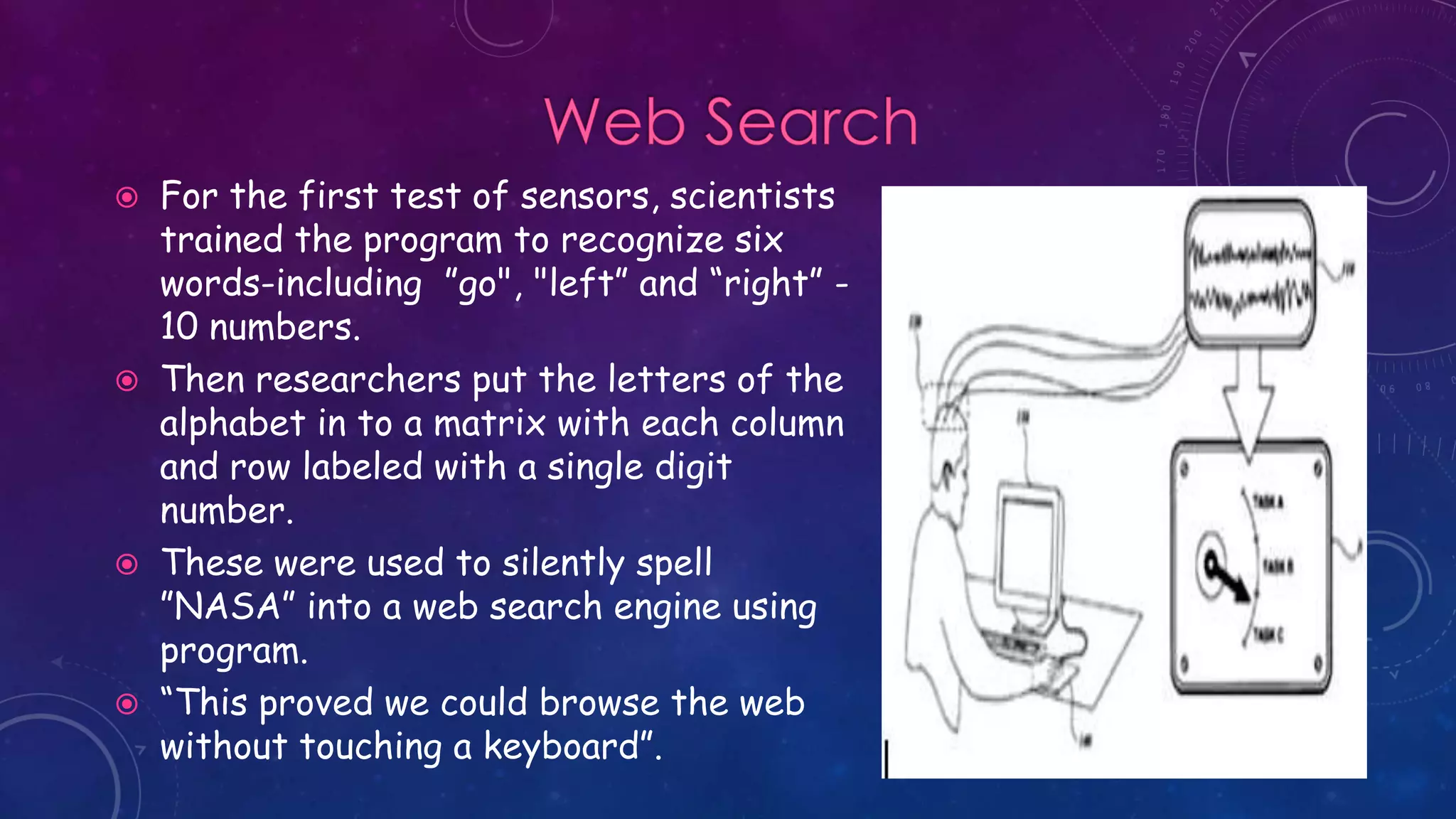
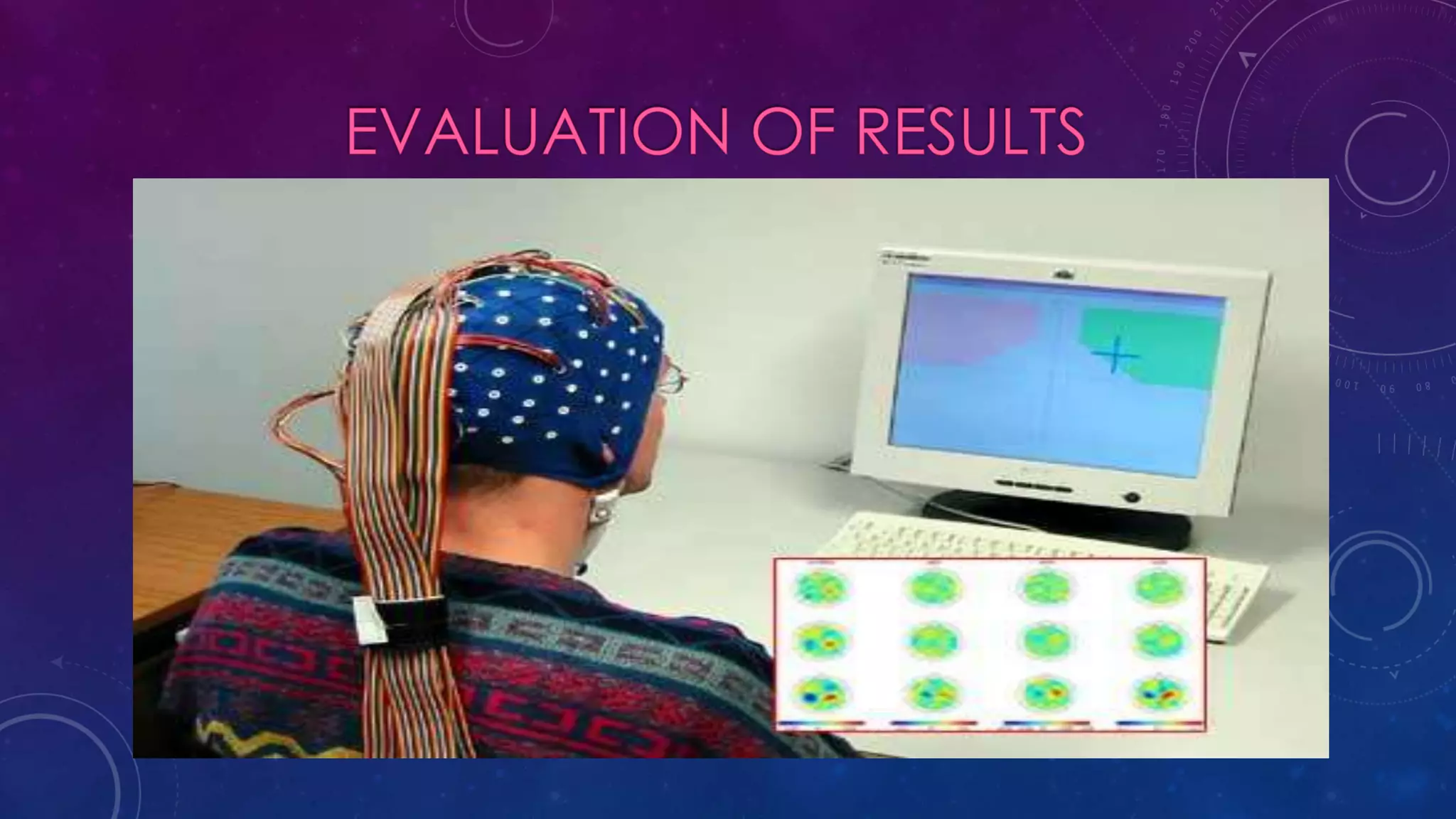
The document summarizes a seminar presentation on mind reading computers. It describes how computational models can infer mental states from facial expressions and gestures by analyzing features captured by sensors. Advantages include helping disabled people communicate and monitoring driver attention. Challenges include privacy concerns if the technology is misused to extract confidential information. The presentation demonstrates the ability to silently use a search engine by thinking letters and numbers detected from blood oxygen levels measured on the forehead.