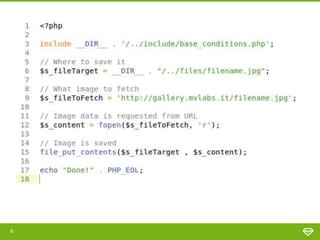
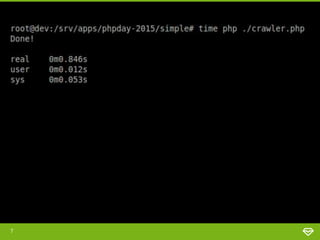
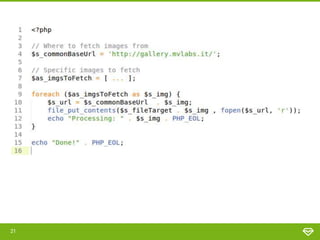
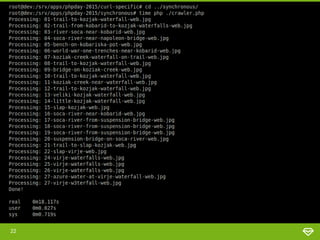
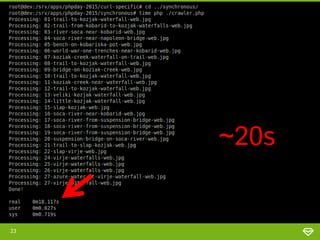
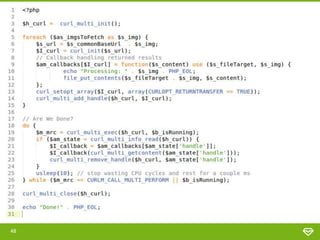
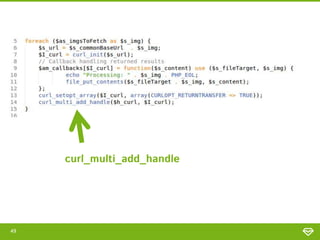
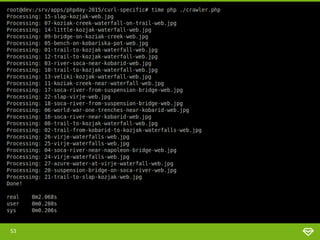
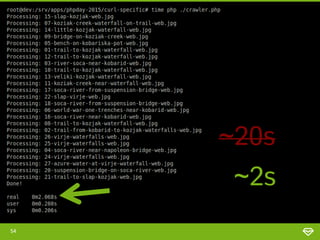
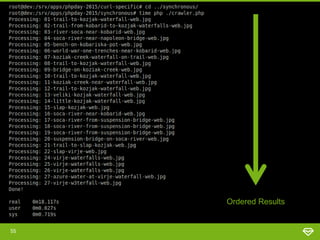
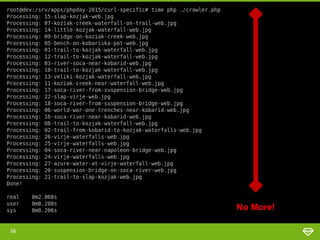
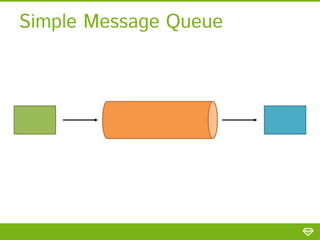
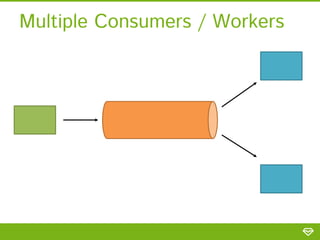
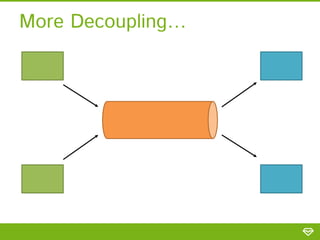
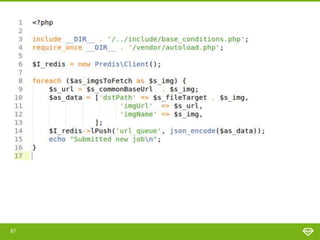
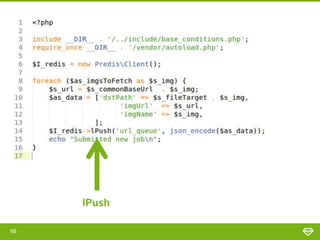
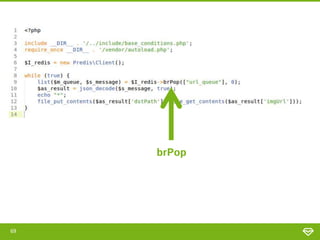
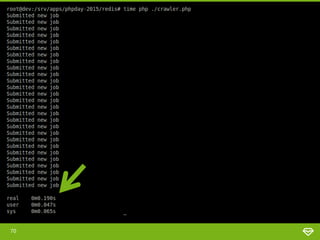
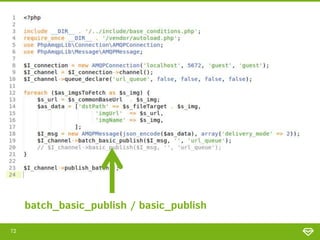
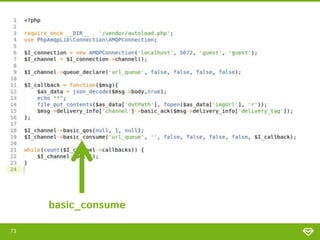
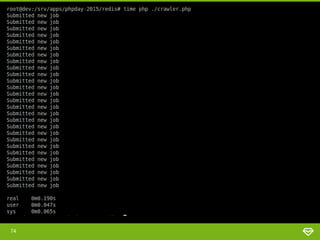
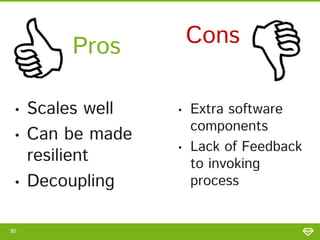
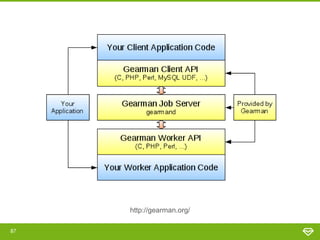
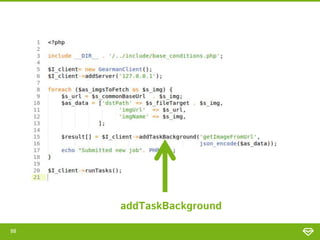
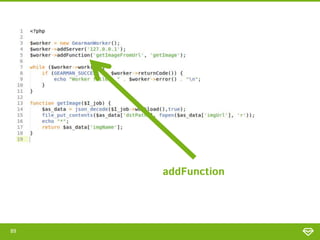
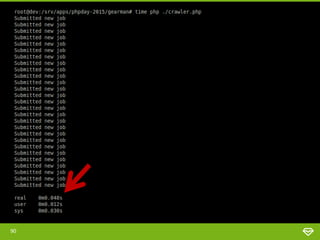
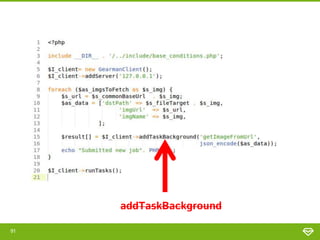
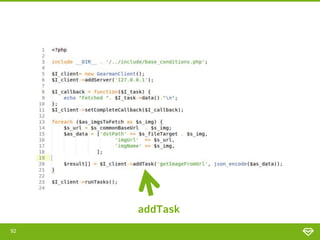
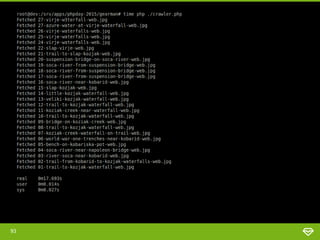
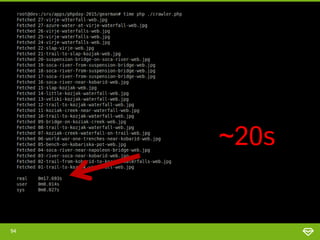
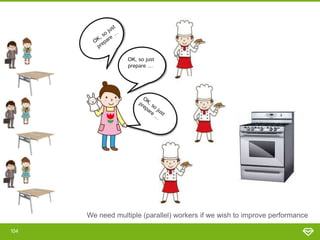
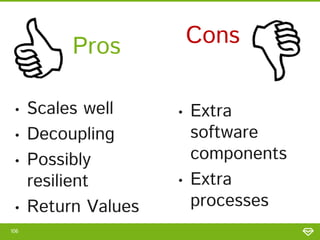
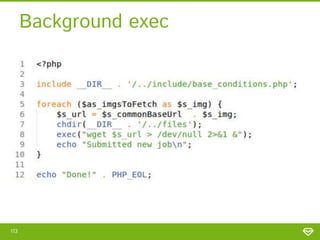
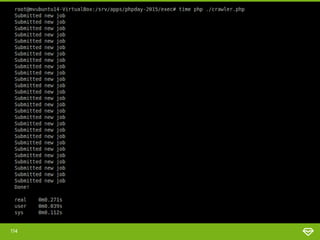
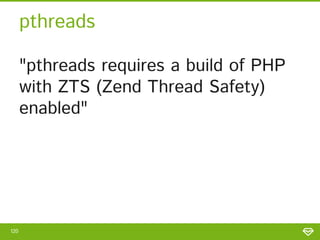
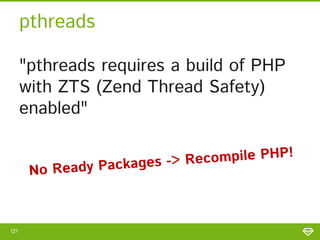
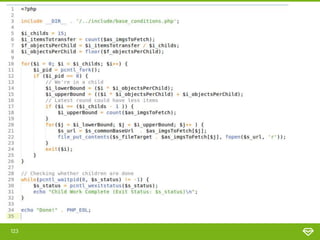
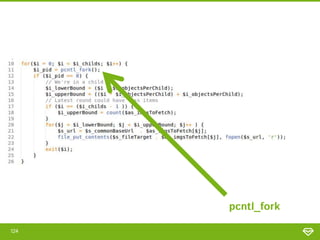
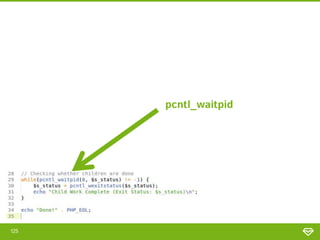
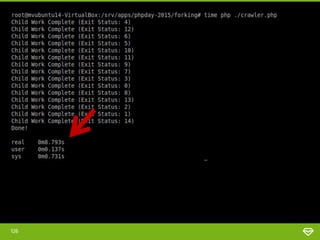
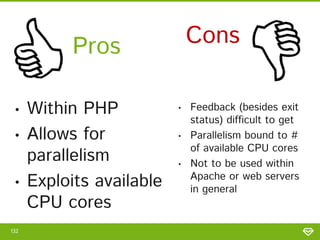
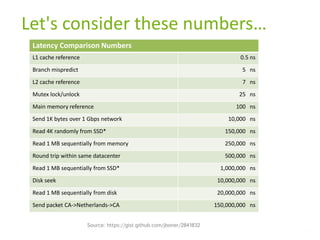
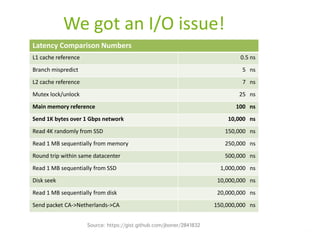
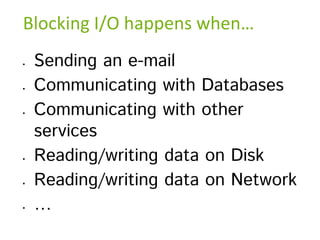
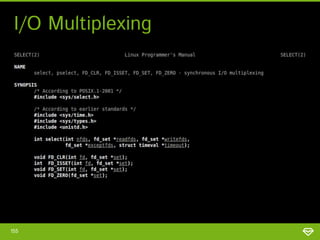
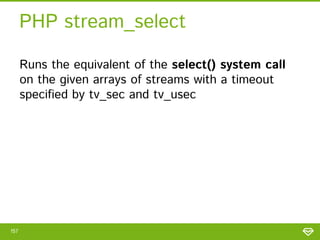
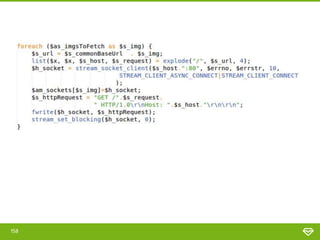
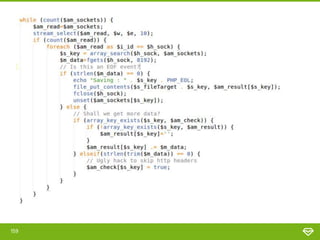
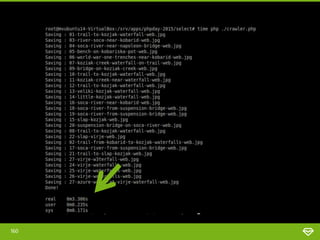
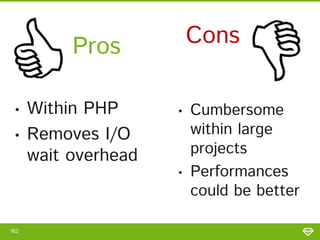
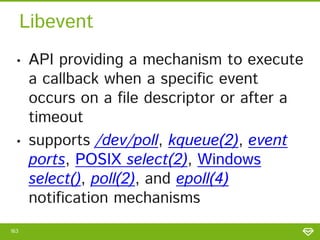
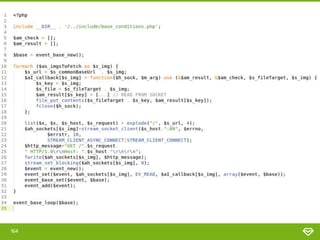
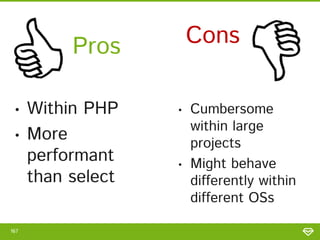
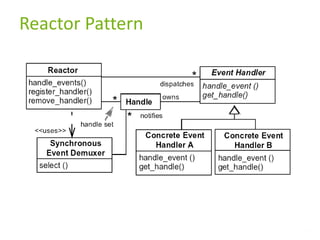
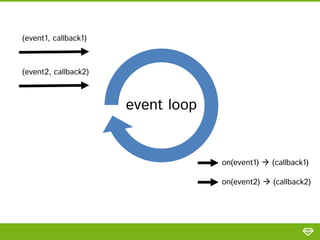
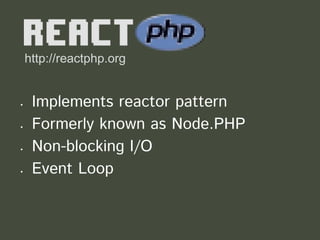
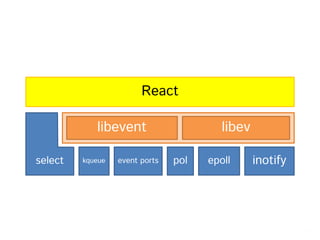
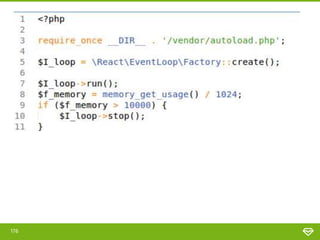
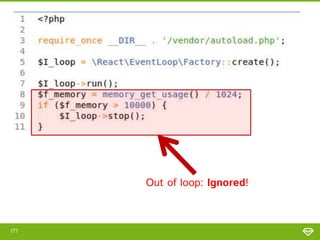
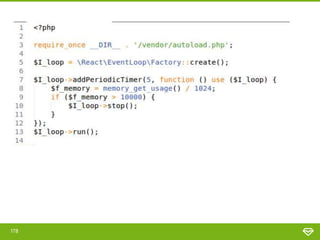
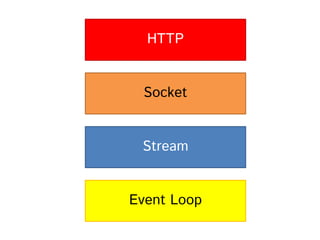
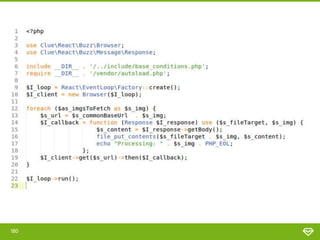
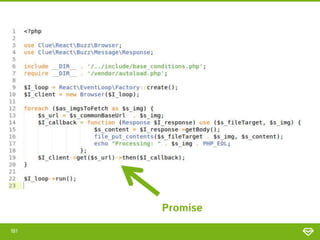
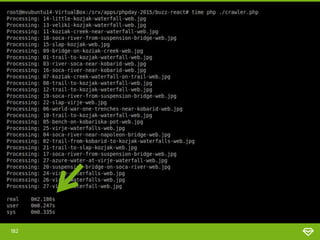
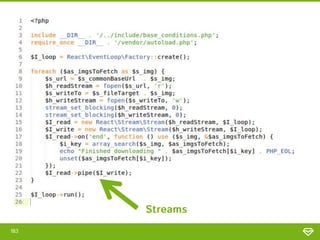
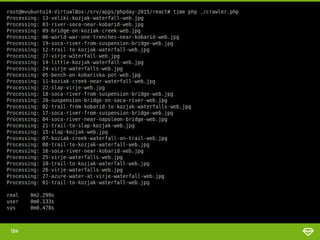
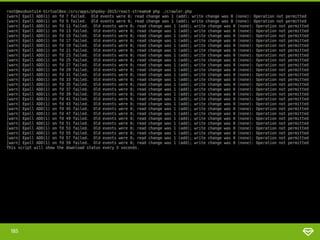
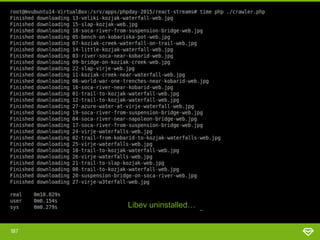
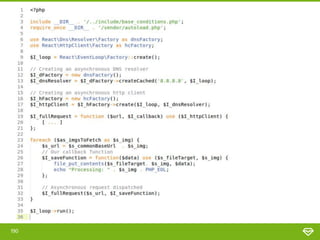
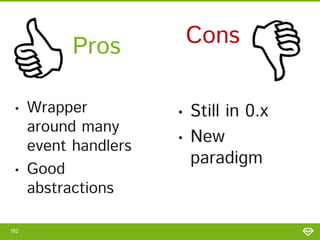
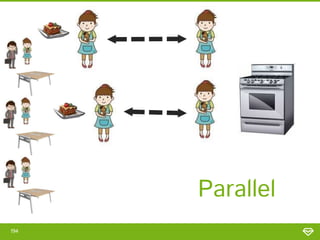
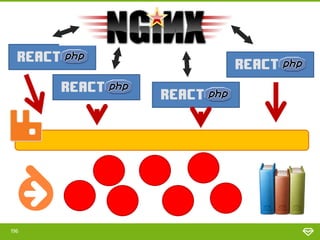
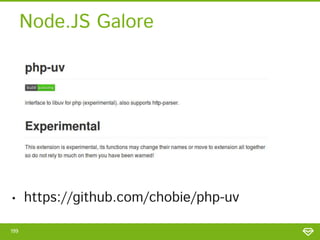
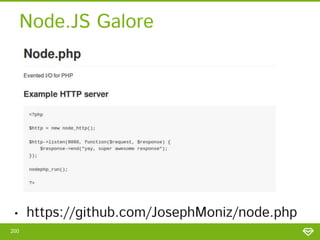
Steve Maraspin gave a presentation on asynchronous and parallel PHP. He began by demonstrating how blocking I/O calls can slow down PHP applications and presented several approaches to address this issue including asynchronous calls, message queues, job servers, forking processes, stream_select, libevent, and React. He discussed the pros and cons of each approach and provided code examples. He concluded by discussing additional asynchronous options for PHP like Hack and Node.js and thanked the audience.