Embed presentation

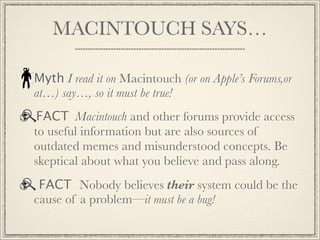
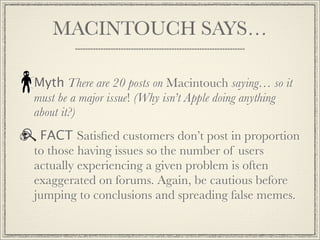
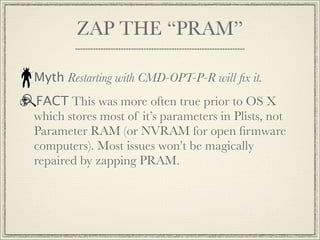

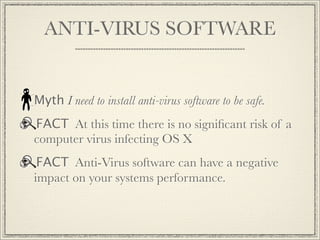
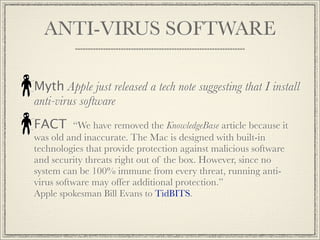
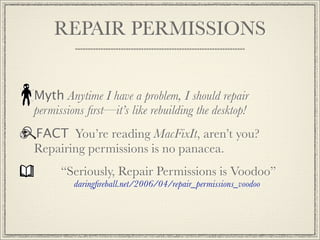
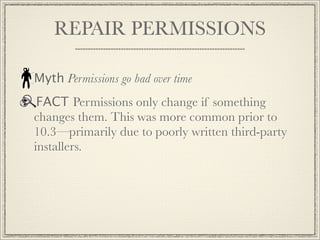
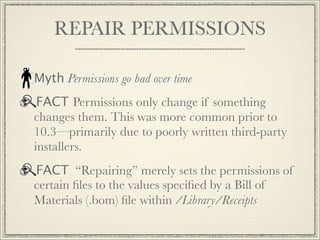
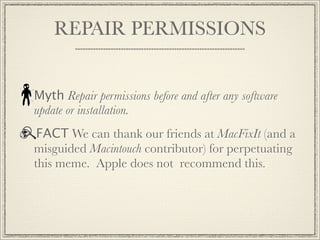

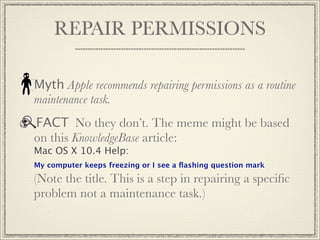


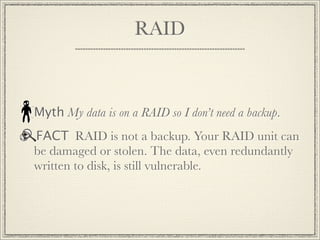
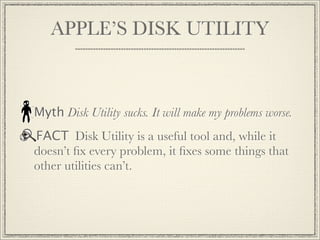
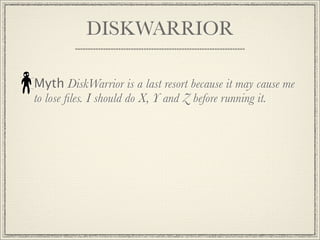




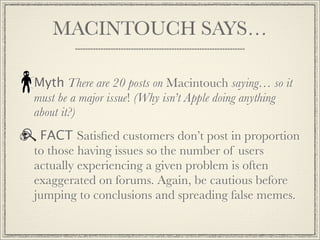
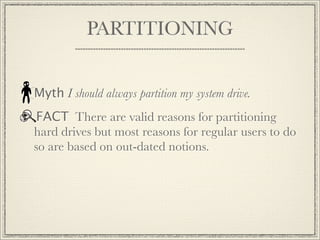
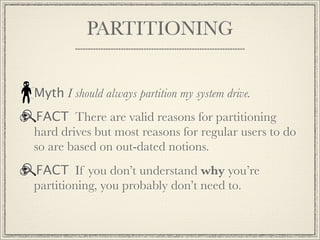
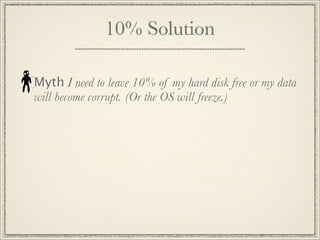
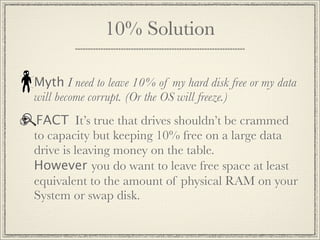
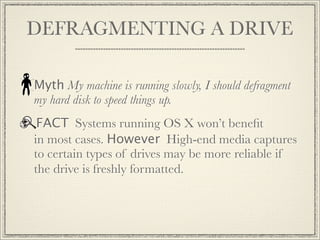
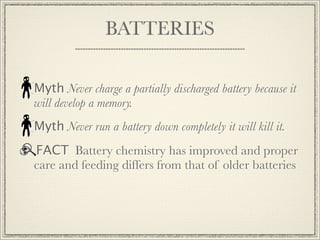
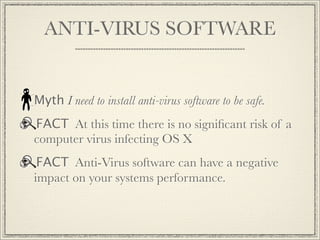
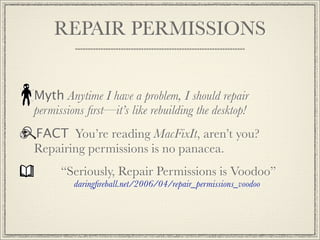
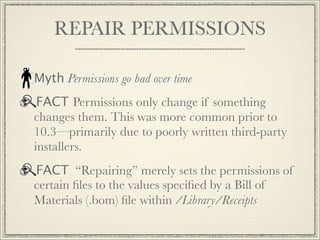
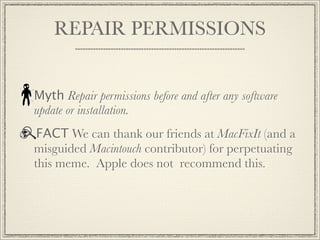
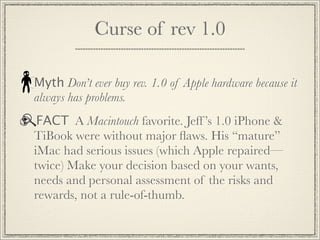
The document addresses common myths and misconceptions about Macintosh troubleshooting, emphasizing that reliance on sources like forums can lead to outdated and biased information. It stresses the importance of skepticism regarding widely held beliefs about tech fixes, partitioning, and software use, indicating that many practices may be based on outdated ideas or misinformation. Additionally, it highlights that certain practices, such as repairing permissions, may not be as beneficial as assumed and that RAID is not a substitute for backups.