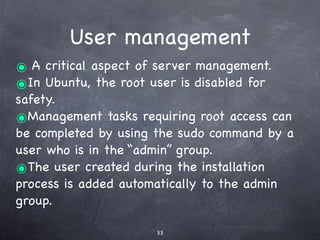
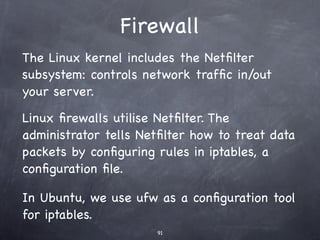
This document describes a one-day Linux workshop led by Peter Dalmaris, focusing on Ubuntu server management without requiring prior knowledge of Linux. It covers topics like virtual machines, user management, networking, backup strategies, and server software. The workshop aims to equip participants with practical skills and understanding of Linux server administration principles.

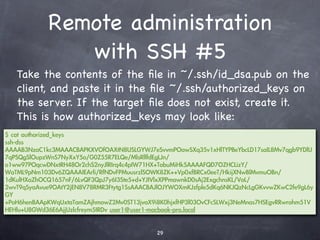
![NCAR's newest supercomputer: On 12 July
2004, SCD took delivery of lightning, a new
Linux cluster manufactured by IBM. The 1.1-
teraflop system is now installed in the NCAR
Computer Room
Motorola RAZR², an advanced
embedded system using embedded
Linux
The Nokia N810 features the Maemo
Linux distribution,[2] based on
Maemo 4.0, which features MicroB
(a Mozilla-based mobile browser), a
GPS navigation application, new
media player, and a refreshed
interface.
The WRT54G is notable for Ubuntu Linux on
being the first consumer- Macbook Pro
level network device that
had its firmware source code
released to satisfy the
obligations of the GNU
GPL.](https://image.slidesharecdn.com/linuxworkshop1-day-090710101225-phpapp01/85/Linux-beginner-s-Workshop-14-320.jpg)










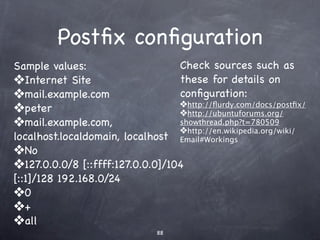
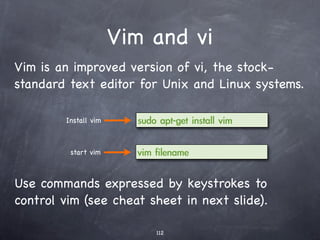
![Postfix configuration
Check sources such as
Sample values:
these for details on
❖Internet Site configuration:
❖mail.example.com ❖http://flurdy.com/docs/postfix/
❖peter ❖http://ubuntuforums.org/
showthread.php?t=780509
❖mail.example.com, ❖http://en.wikipedia.org/wiki/
localhost.localdomain, localhost Email#Workings
❖No
❖127.0.0.0/8 [::ffff:127.0.0.0]/104 [::
1]/128 192.168.0/24
❖0
❖+
❖all](https://image.slidesharecdn.com/linuxworkshop1-day-090710101225-phpapp01/85/Linux-beginner-s-Workshop-126-320.jpg)

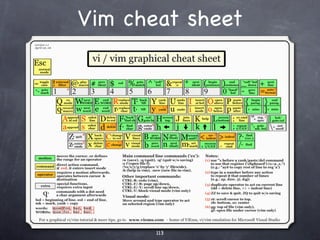
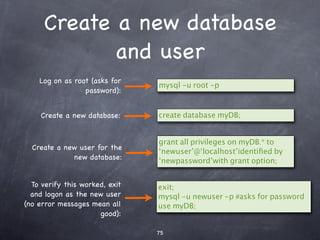
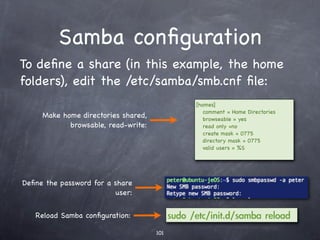
![Samba configuration
To define a share (in this example, the home
folders), edit the /etc/samba/smb.cnf file:
[homes]
Make home directories shared, comment = Home Directories
browseable = yes
browsable, read-write: read only =no
create mask = 0775
directory mask = 0775
valid users = %S
Define the password for a share
user:
Reload Samba configuration:](https://image.slidesharecdn.com/linuxworkshop1-day-090710101225-phpapp01/85/Linux-beginner-s-Workshop-142-320.jpg)

























