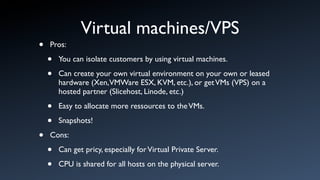
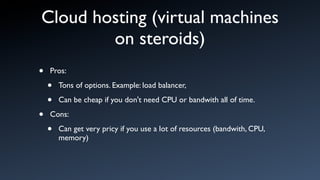
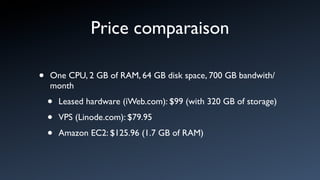
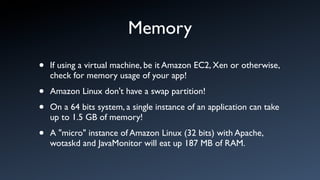
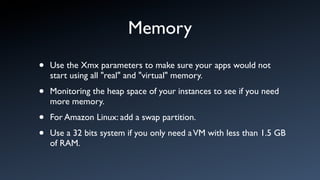
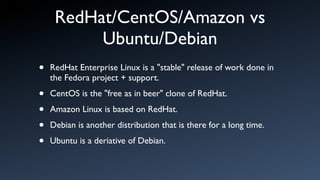
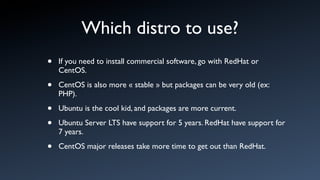
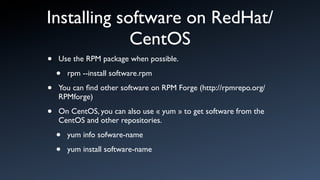
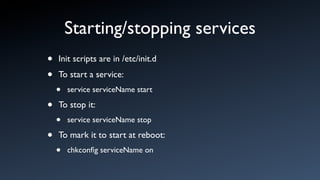
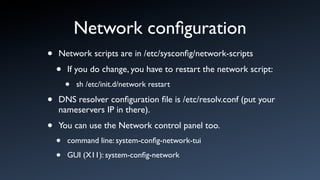
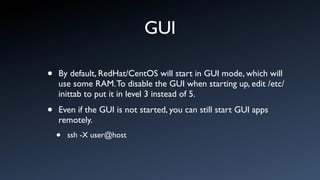
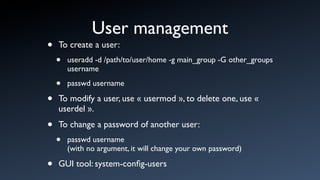
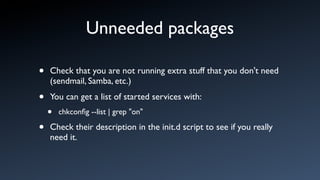
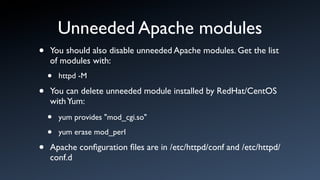
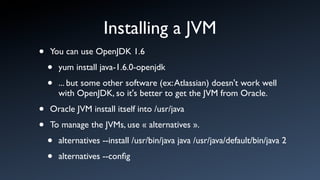
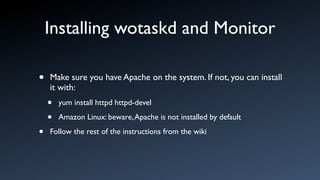
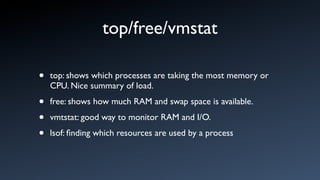
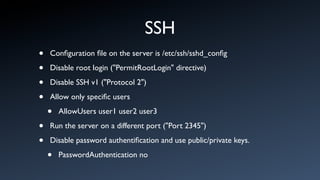
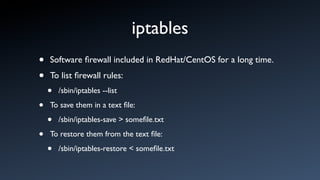
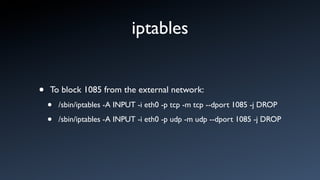
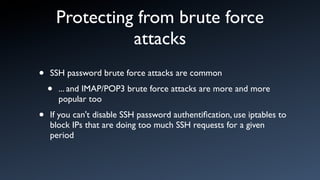
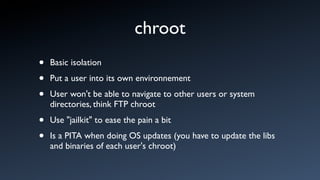
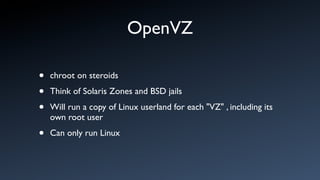
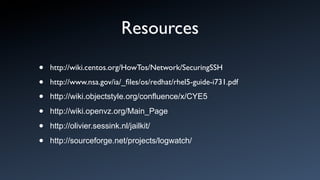
The document discusses various deployment options for server environments, including using personal hardware, leased hardware, virtual machines, and cloud hosting, along with their pros and cons. It explores different Linux distributions, such as RedHat/CentOS and Ubuntu, and provides guidance on software installation, network configuration, user management, performance monitoring, and security practices. It emphasizes the importance of managing resources effectively and securing server environments against various threats.