This document provides an overview of Linux including:
- Its origins from Unix developed at Bell Labs in the late 1960s
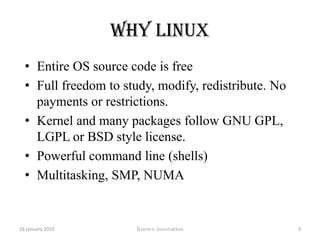
- Why Linux was created with its entire source code being free and open
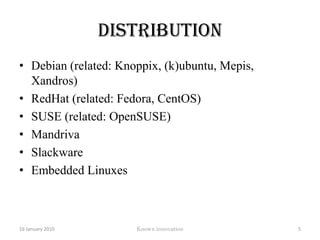
- Popular Linux distributions like Debian, RedHat, SUSE, and others
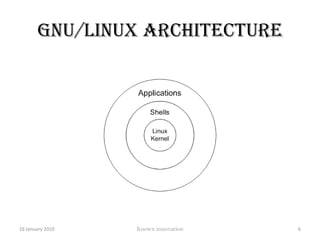
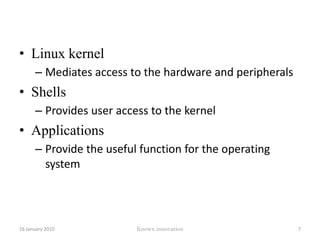
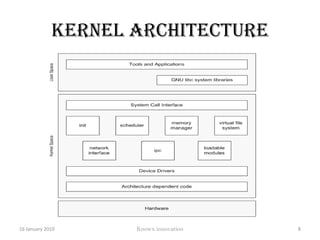
- The GNU/Linux architecture including the kernel, shells, and applications
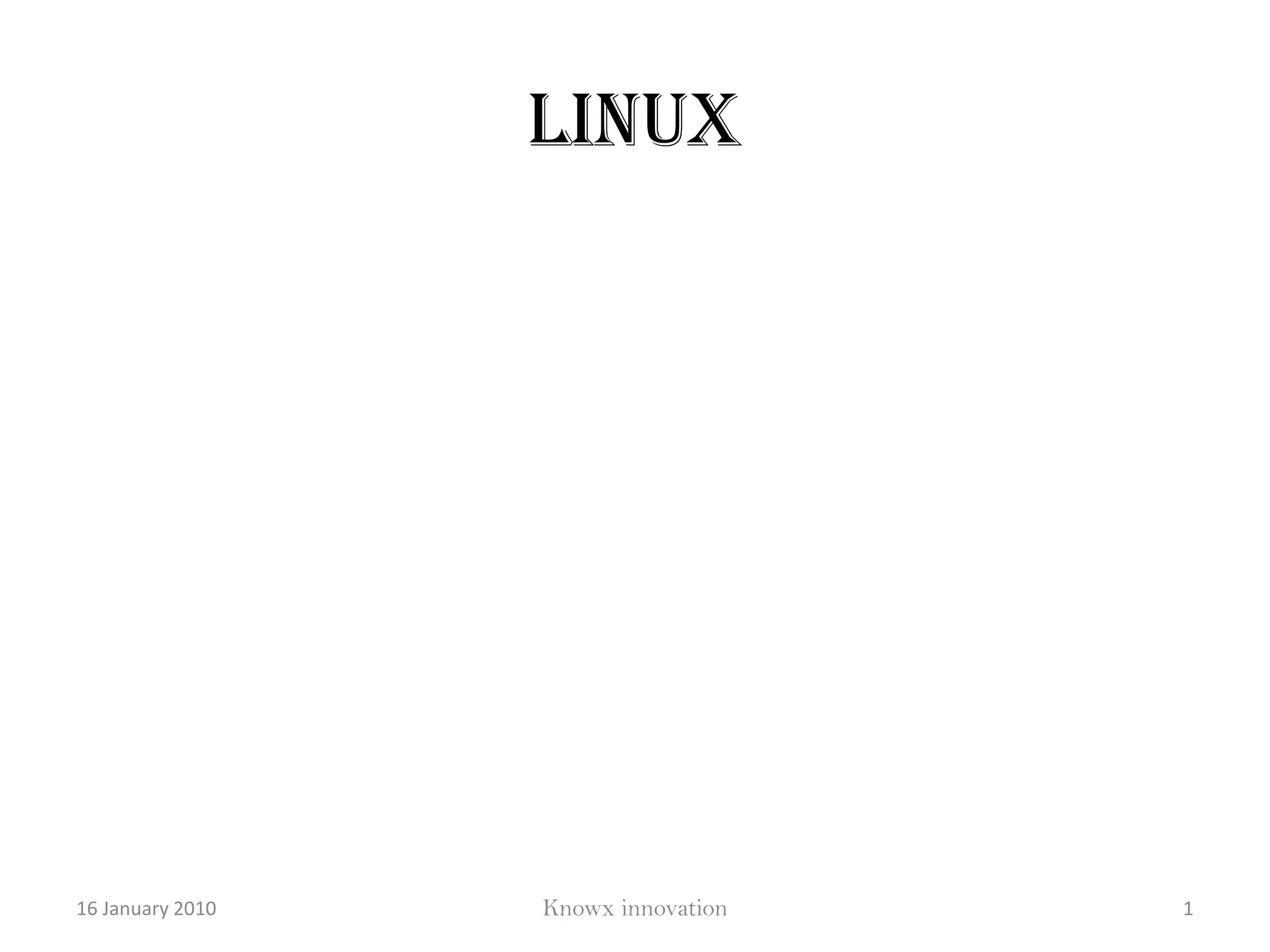
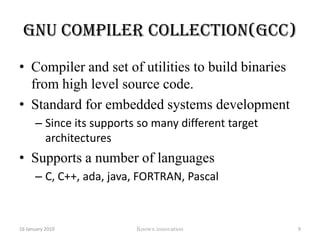
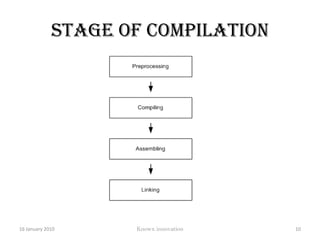
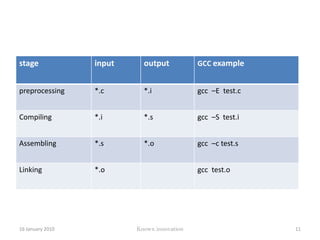
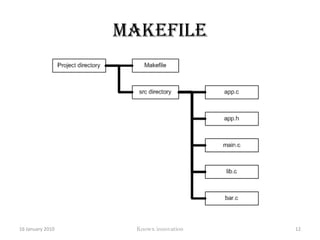
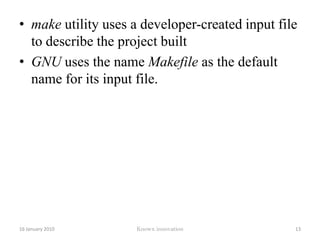
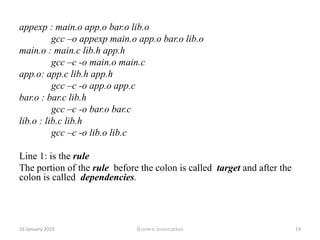
- Key components like the GNU compiler collection (GCC) and makefiles
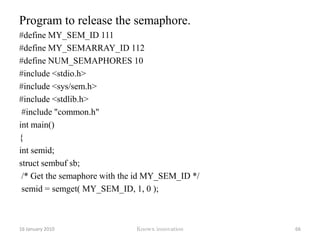
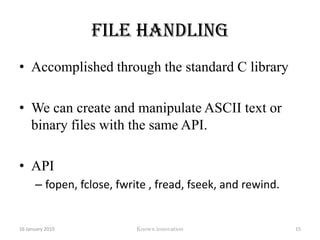
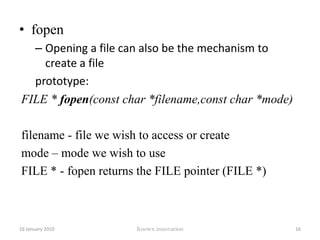
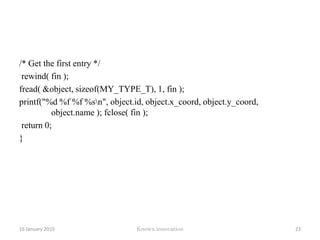
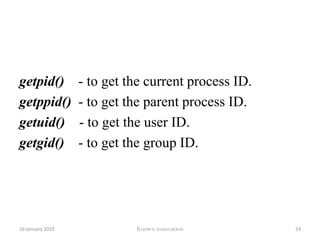
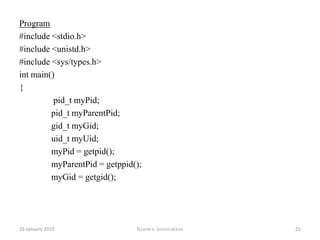
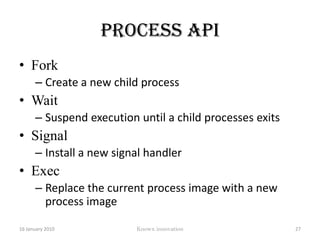
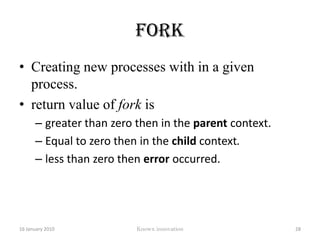
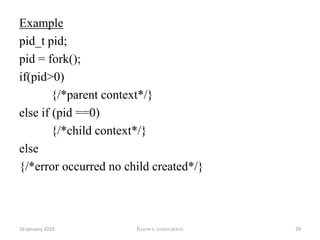
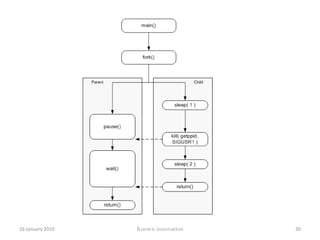
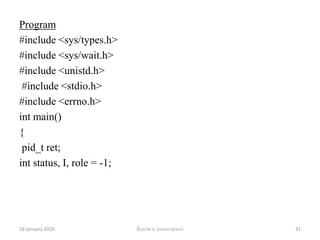
- File handling and process APIs in Linux
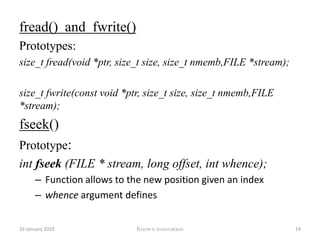
![Program#include <stdio.h>#define MAX_LINE 40 #define FILENAME "myfile.txt“typedef struct { int id; float x_coord; float y_coord; char name[MAX_LINE+1]; }MY_TYPE_T; MY_TYPE_T object;int main() {int i;FILE *fin; fin = fopen( FILENAME, "r" ); /* Open the input file */12 January 2010Knowx innovation21](https://image.slidesharecdn.com/linux-100116110123-phpapp02/85/Linux-26-320.jpg)

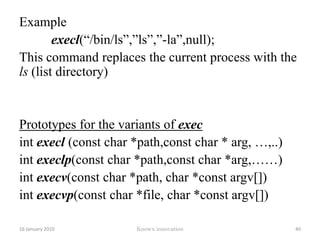
![Example execl(“/bin/ls”,”ls”,”-la”,null);This command replaces the current process with the ls (list directory)Prototypes for the variants of execint execl (const char *path,const char * arg, …,..)int execlp(const char *path,const char *arg,……)int execv(const char *path, char *const argv[])int execvp(const char *file, char *const argv[])12 January 2010Knowx innovation40](https://image.slidesharecdn.com/linux-100116110123-phpapp02/85/Linux-45-320.jpg)
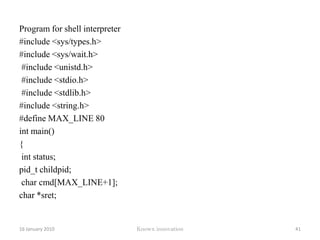
![Program for shell interpreter#include <sys/types.h> #include <sys/wait.h>#include <unistd.h>#include <stdio.h>#include <stdlib.h> #include <string.h> #define MAX_LINE 80 int main() {int status; pid_t childpid;char cmd[MAX_LINE+1]; char *sret;12 January 2010Knowx innovation41](https://image.slidesharecdn.com/linux-100116110123-phpapp02/85/Linux-46-320.jpg)
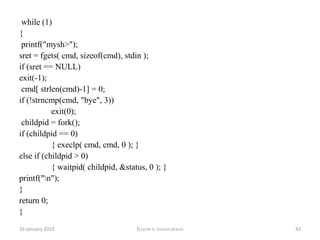
![while (1) {printf("mysh>"); sret = fgets( cmd, sizeof(cmd), stdin ); if (sret == NULL) exit(-1);cmd[ strlen(cmd)-1] = 0; if (!strncmp(cmd, "bye", 3)) exit(0);childpid = fork(); if (childpid == 0) { execlp( cmd, cmd, 0 ); }else if (childpid > 0) { waitpid( childpid, &status, 0 ); } printf("\n"); } return 0;} 12 January 2010Knowx innovation42](https://image.slidesharecdn.com/linux-100116110123-phpapp02/85/Linux-47-320.jpg)
![Sending the messageAPIint msgsnd (int msqid, const void *msgp, size_t msgsz, int msgflg); Takes 4 parametersmsqid is the queue id of the existing queue.msgp is the pointer that contains the address of the structure that holds the message and type.struct message{ long mtype; //The message type.prioritychar mesg [MSGSZ];//The message is of length MSGSZ. }; 12 January 2010Knowx innovation46](https://image.slidesharecdn.com/linux-100116110123-phpapp02/85/Linux-51-320.jpg)
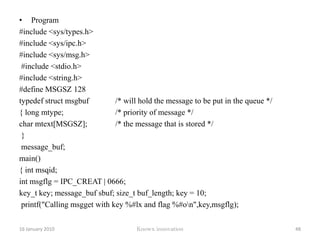
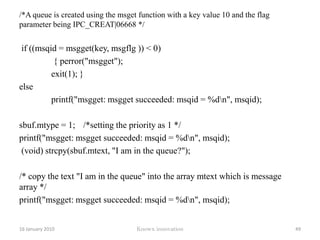
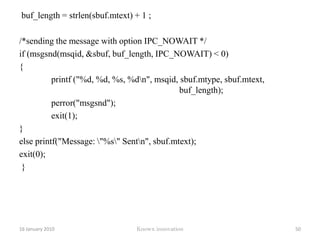
![Program#include <sys/types.h> #include <sys/ipc.h> #include <sys/msg.h>#include <stdio.h> #include <string.h> #define MSGSZ 128 typedef struct msgbuf /* will hold the message to be put in the queue */{ long mtype; /* priority of message */char mtext[MSGSZ]; /* the message that is stored */ }message_buf; main() { int msqid; int msgflg = IPC_CREAT | 0666; key_t key; message_buf sbuf; size_t buf_length; key = 10;printf("Calling msgget with key %#lx and flag %#o\n",key,msgflg);12 January 2010Knowx innovation48](https://image.slidesharecdn.com/linux-100116110123-phpapp02/85/Linux-53-320.jpg)
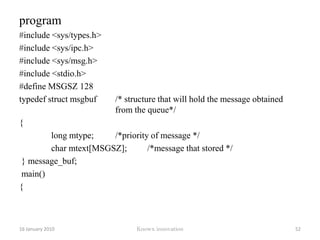
![program#include <sys/types.h> #include <sys/ipc.h> #include <sys/msg.h> #include <stdio.h> #define MSGSZ 128 typedef struct msgbuf /* structure that will hold the message obtained from the queue*/{ long mtype; /*priority of message */ char mtext[MSGSZ]; /*message that stored */} message_buf;main() {12 January 2010Knowx innovation52](https://image.slidesharecdn.com/linux-100116110123-phpapp02/85/Linux-57-320.jpg)