Embed presentation
Download to read offline

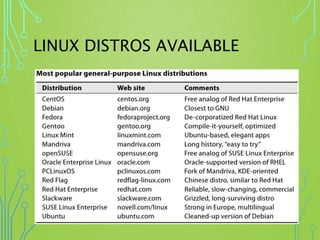


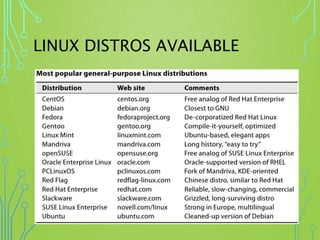
This document provides an overview of Linux, describing it as a widely used open source operating system that interacts between software and computer hardware. It discusses available Linux distributions in the market and offers resources for practicing basic Linux commands. The author's email is provided for further queries.