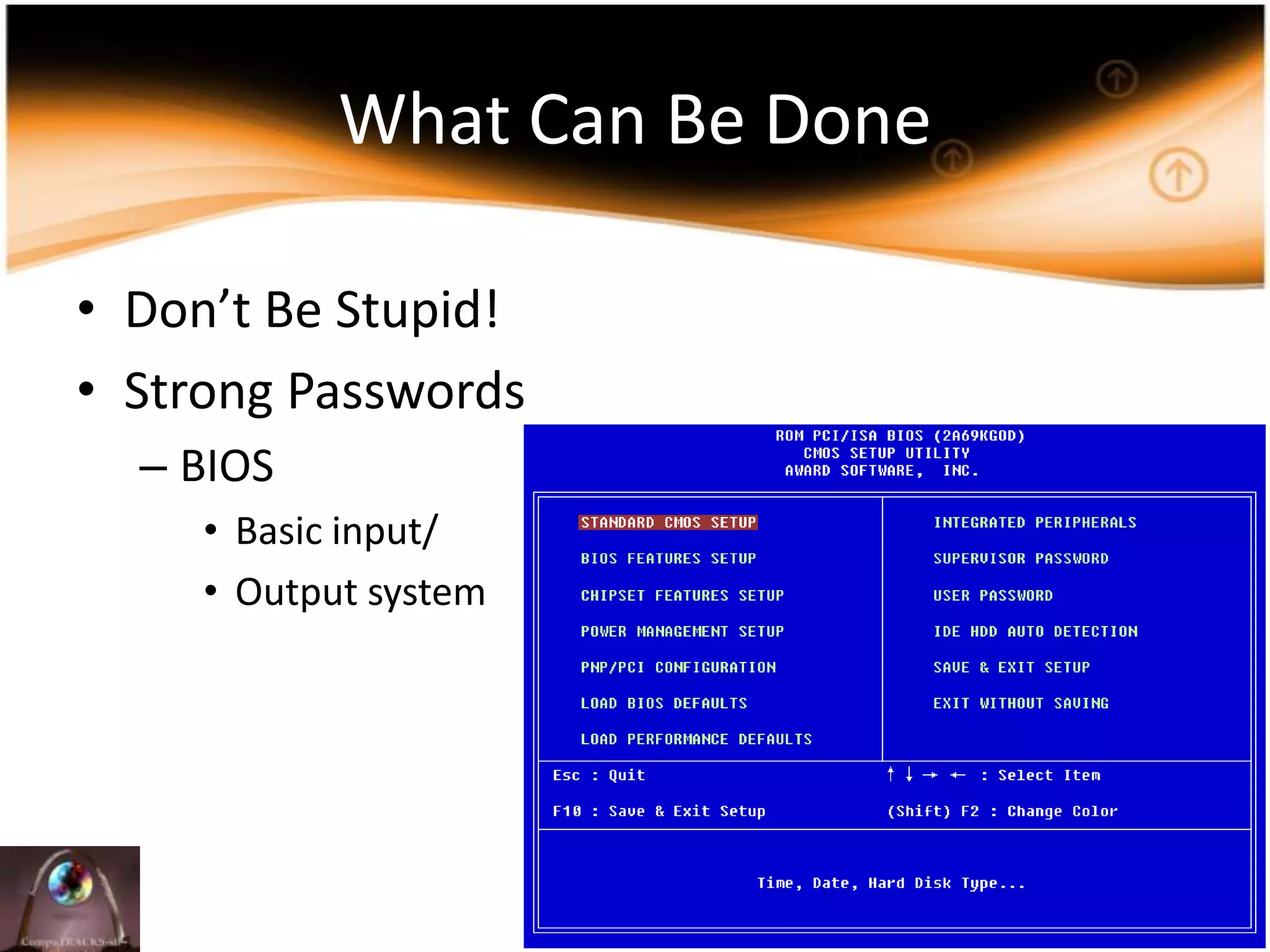
This document discusses laptop security and the costs of lost or stolen laptops. It notes that 100 laptops are lost each day in the US, with 1 in 10 laptops containing sensitive data. The average cost of a lost laptop is $49,246, with 80% of the cost coming from the lost data. Implementing security policies and practices like strong passwords, backups, and laptop locks can help reduce theft by 43% and better protect sensitive data.