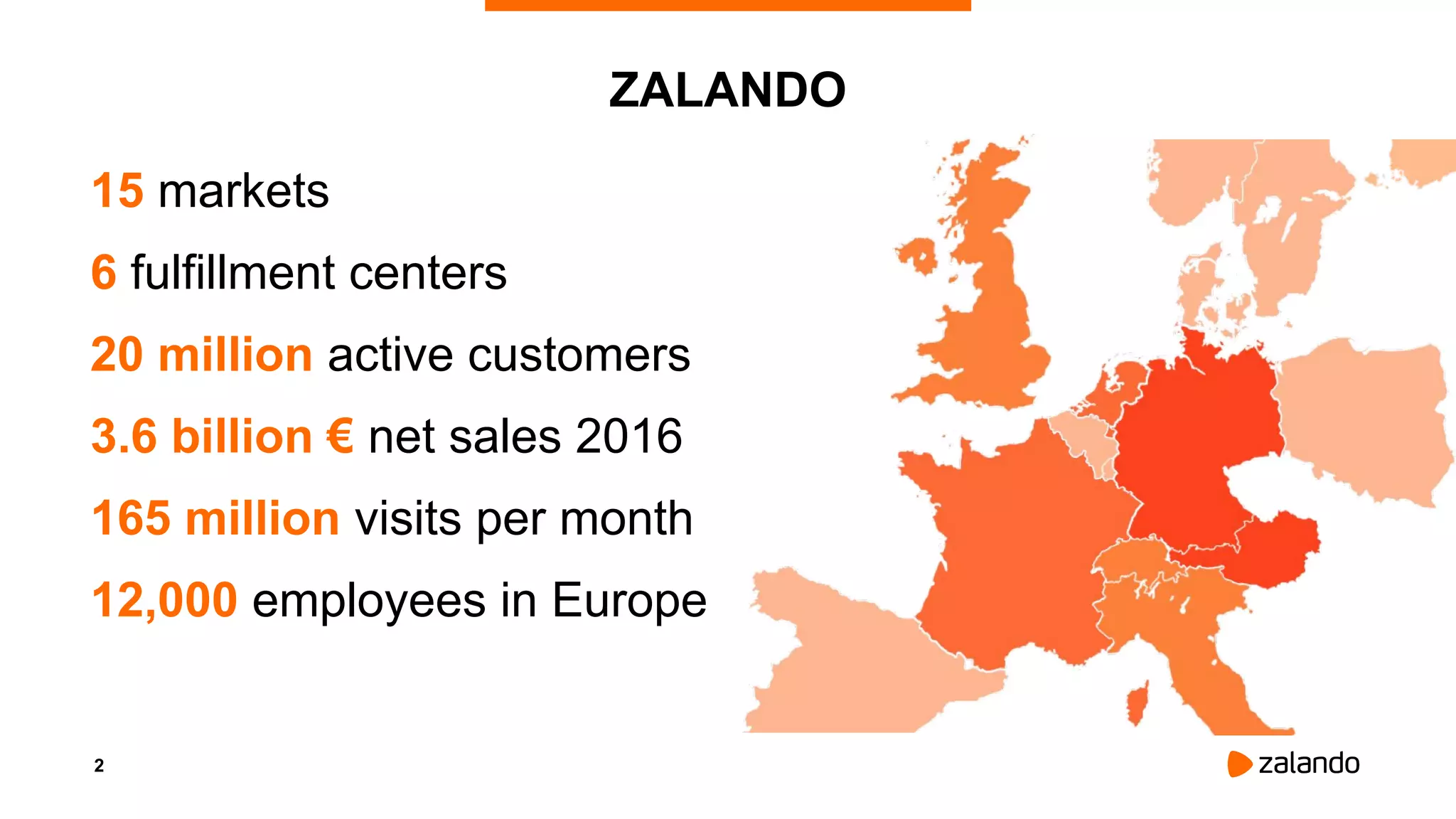
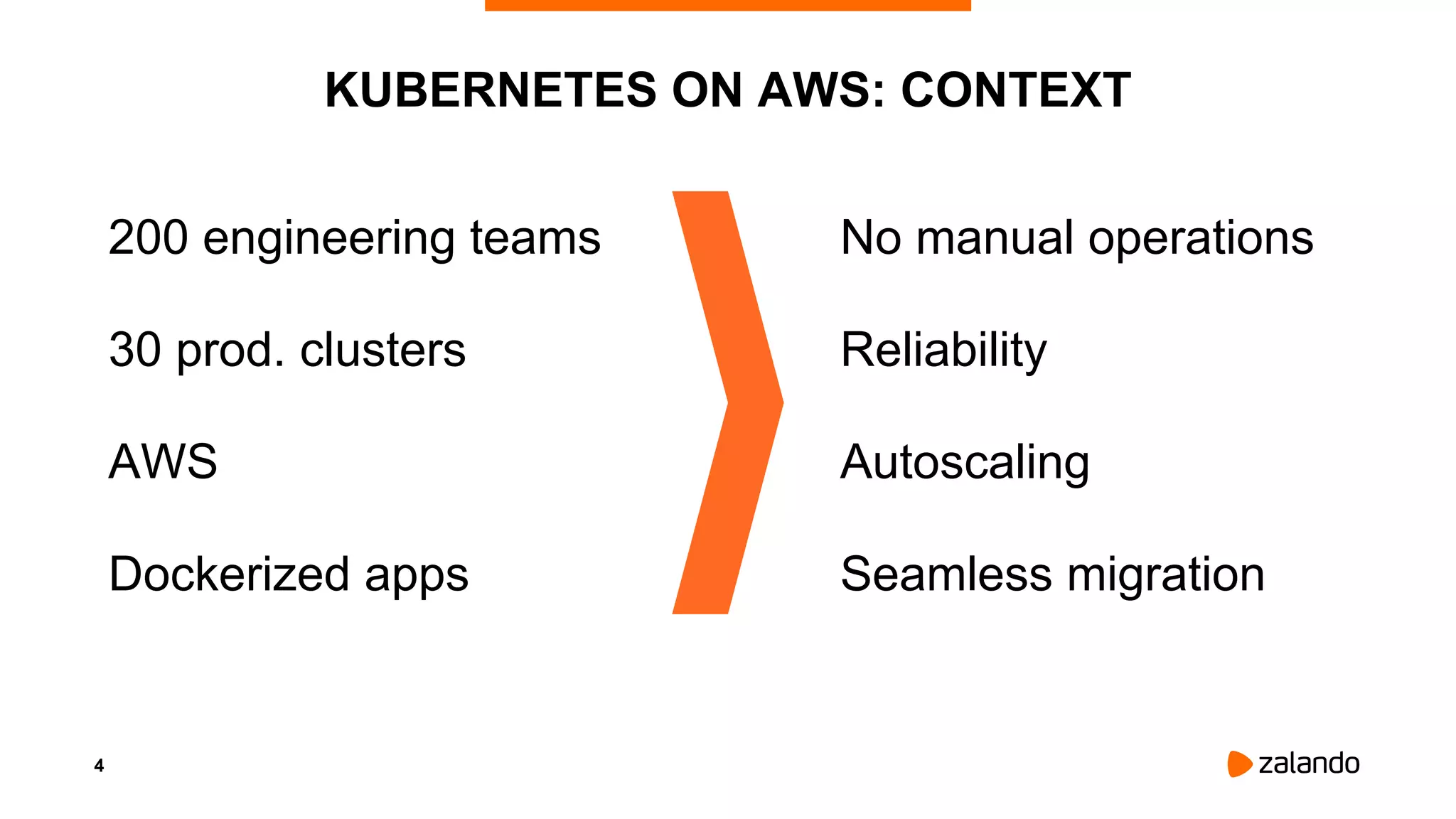
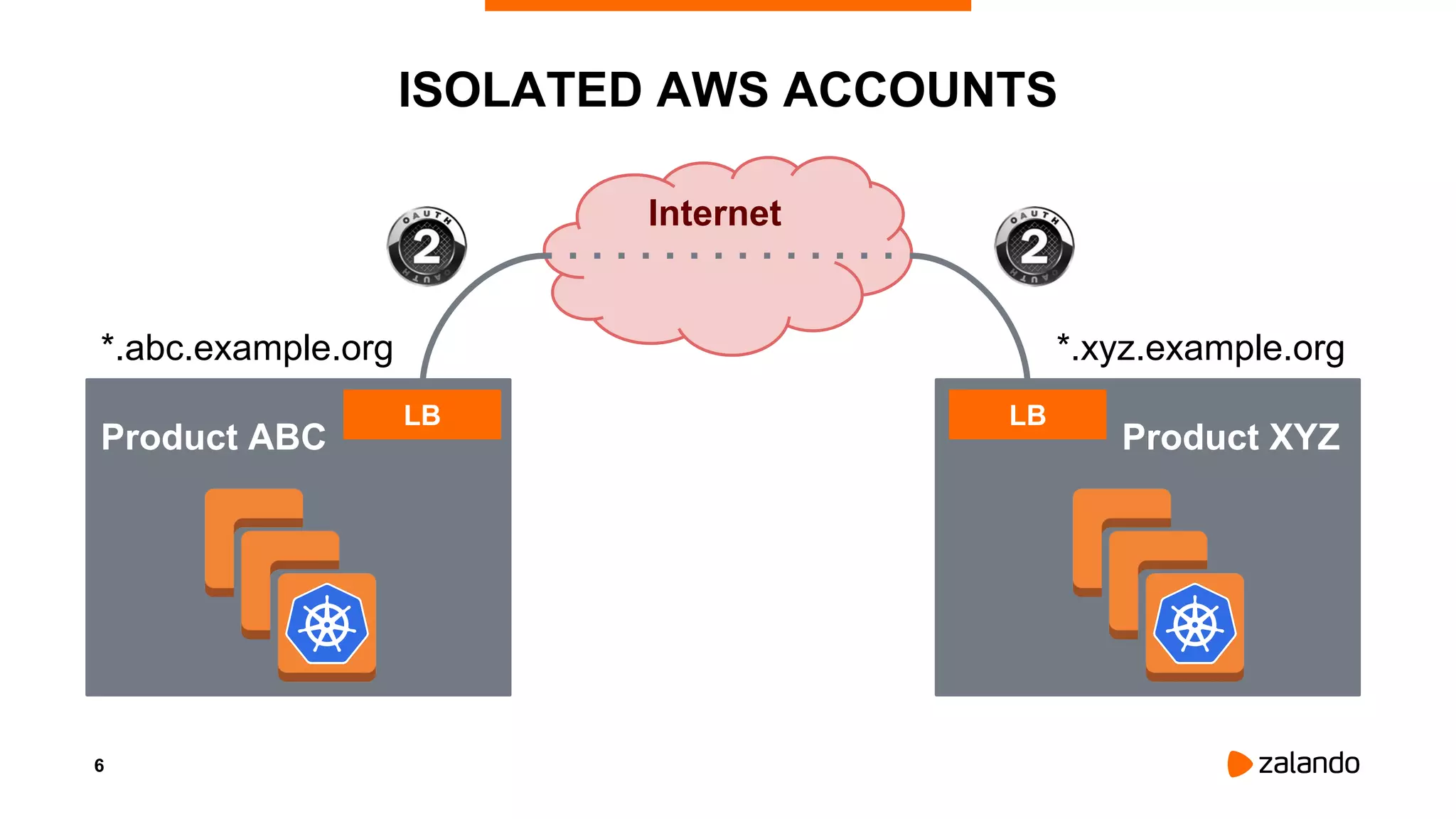
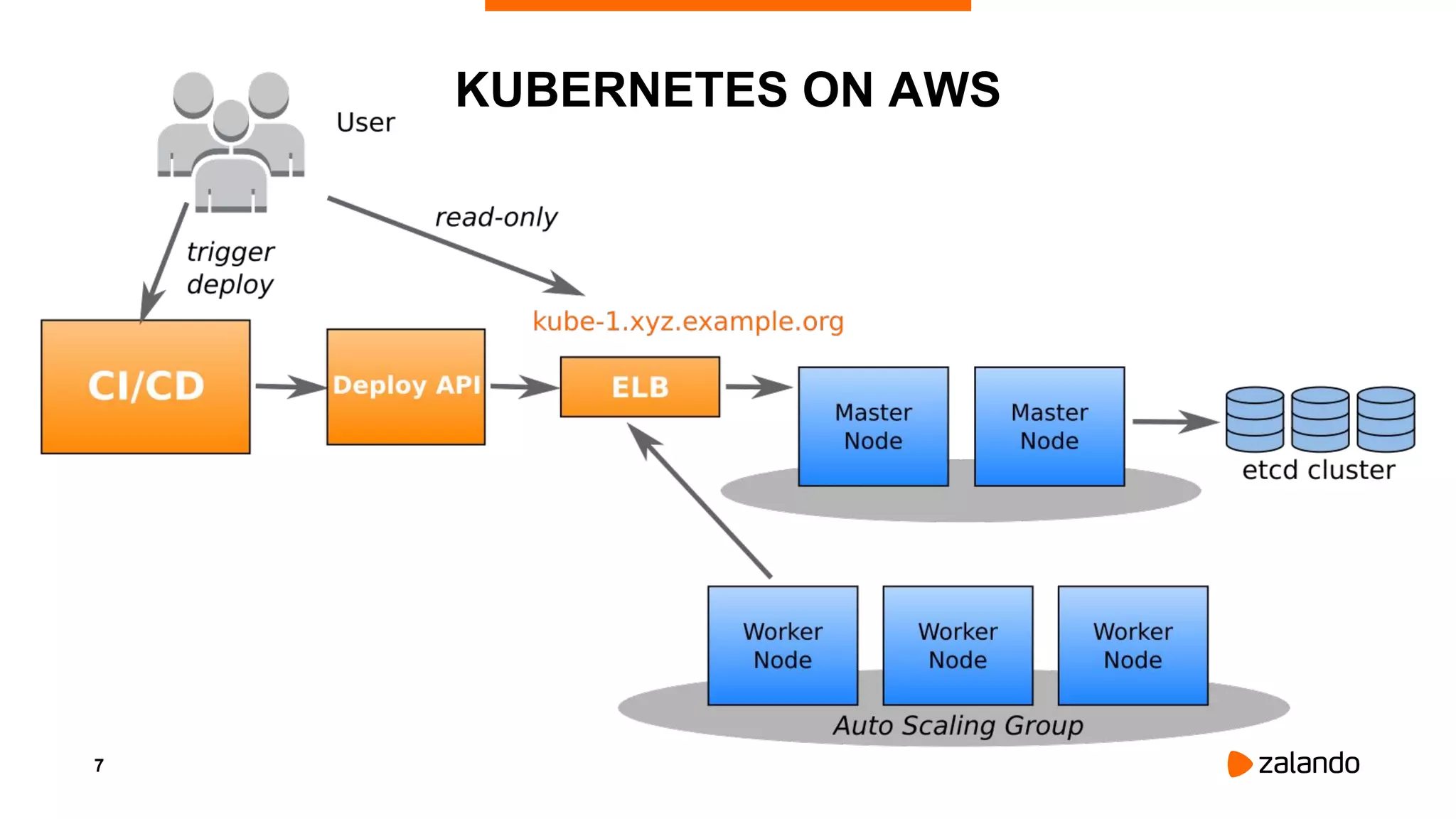
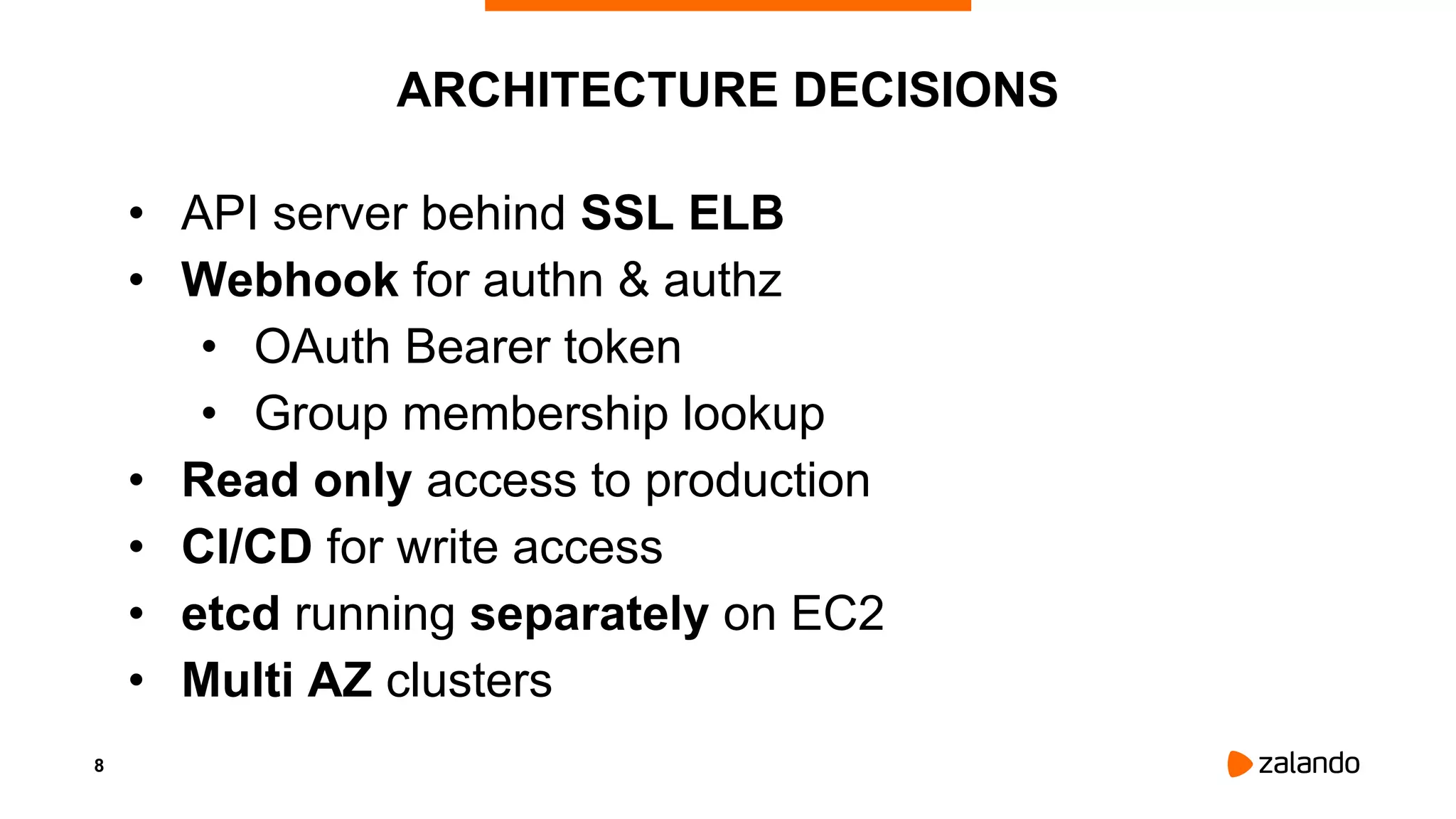
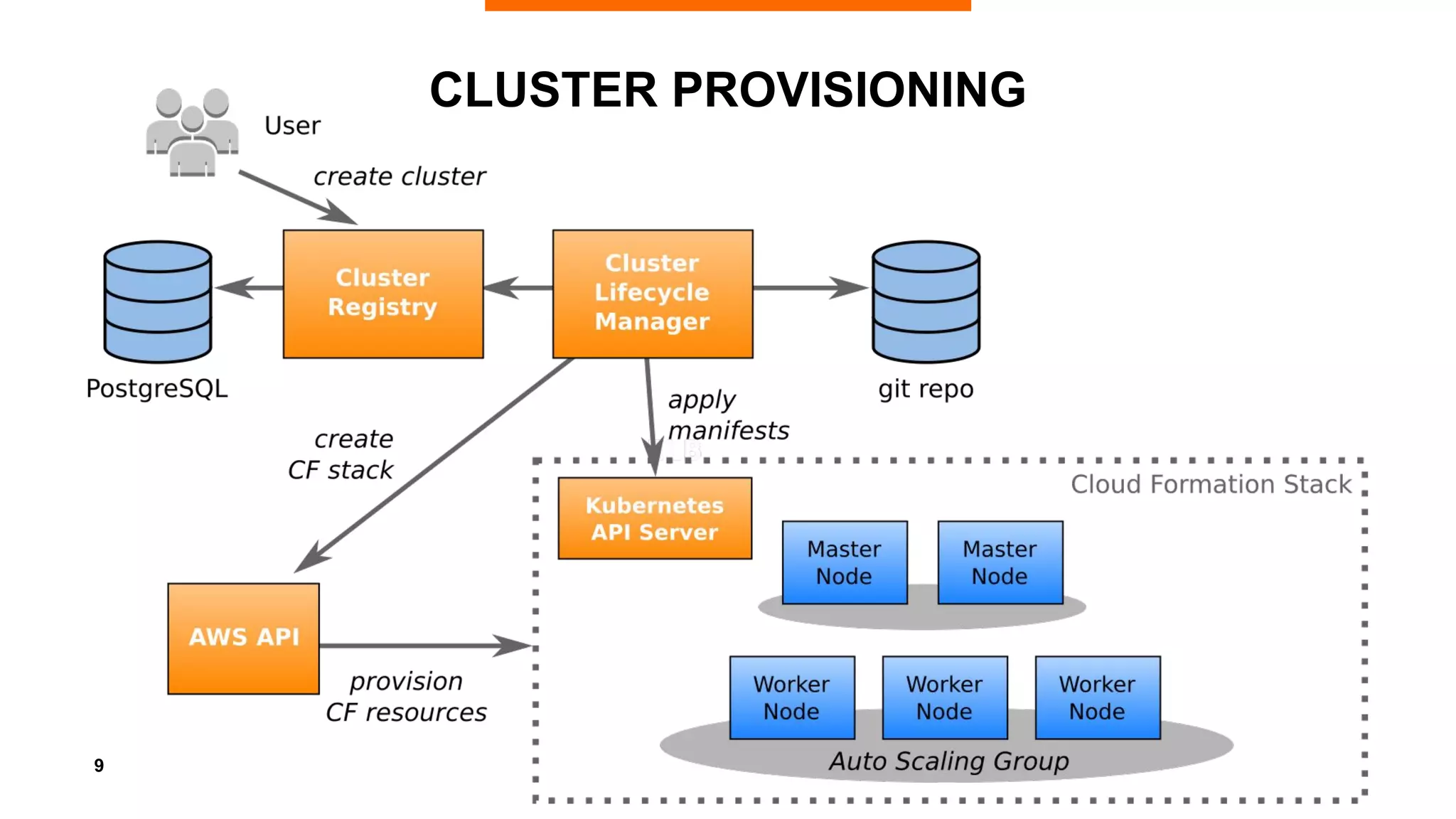
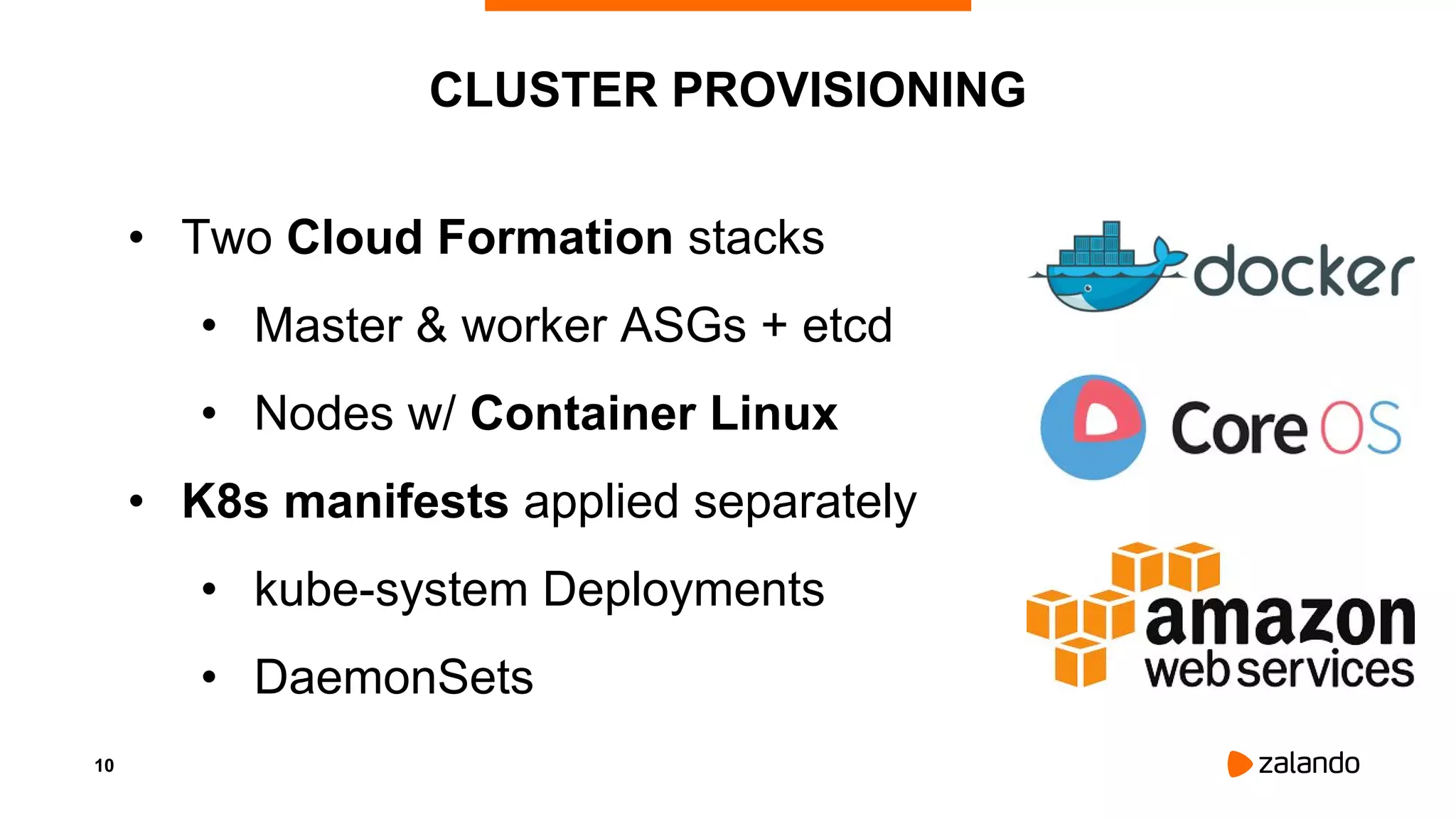
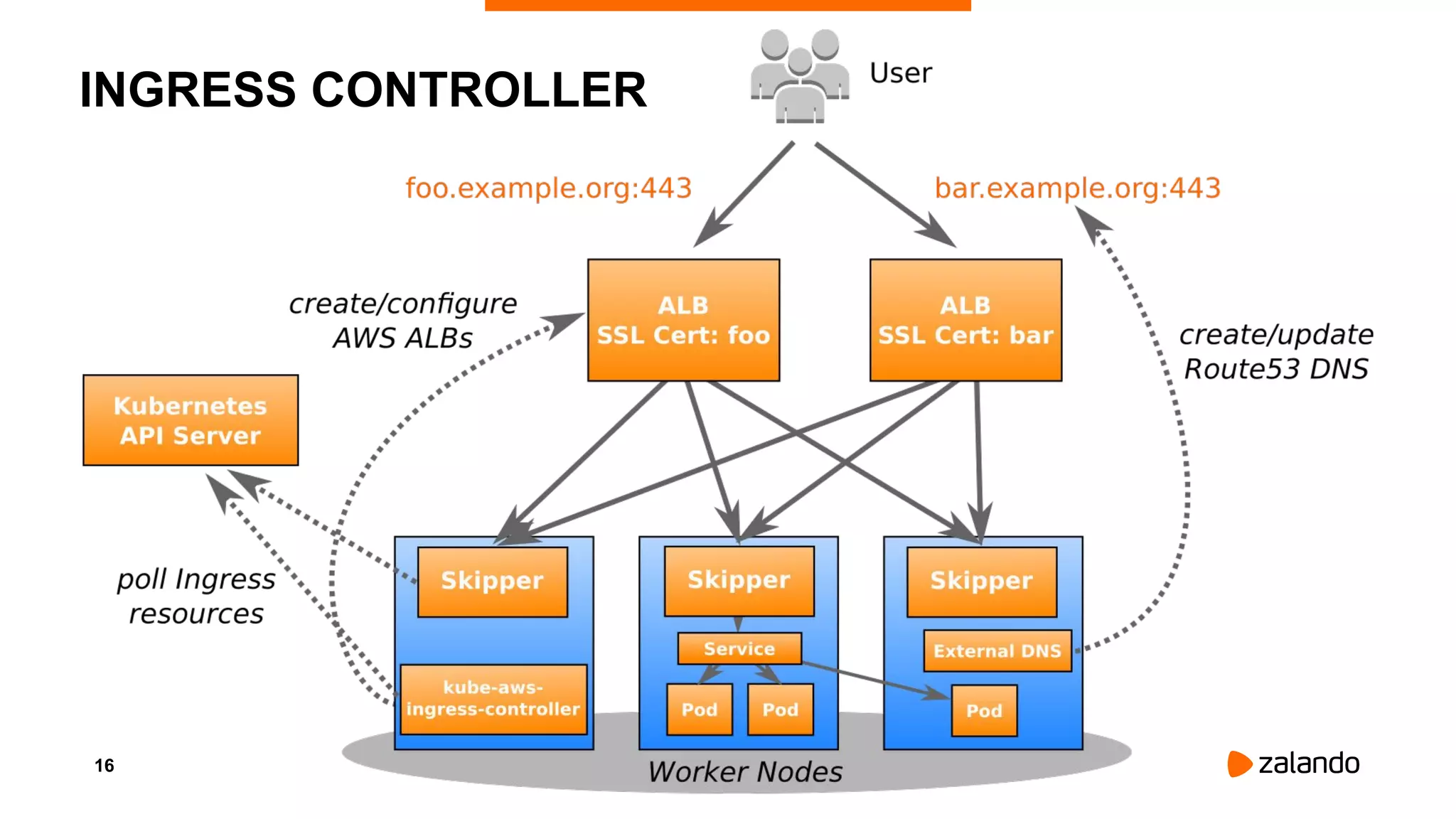
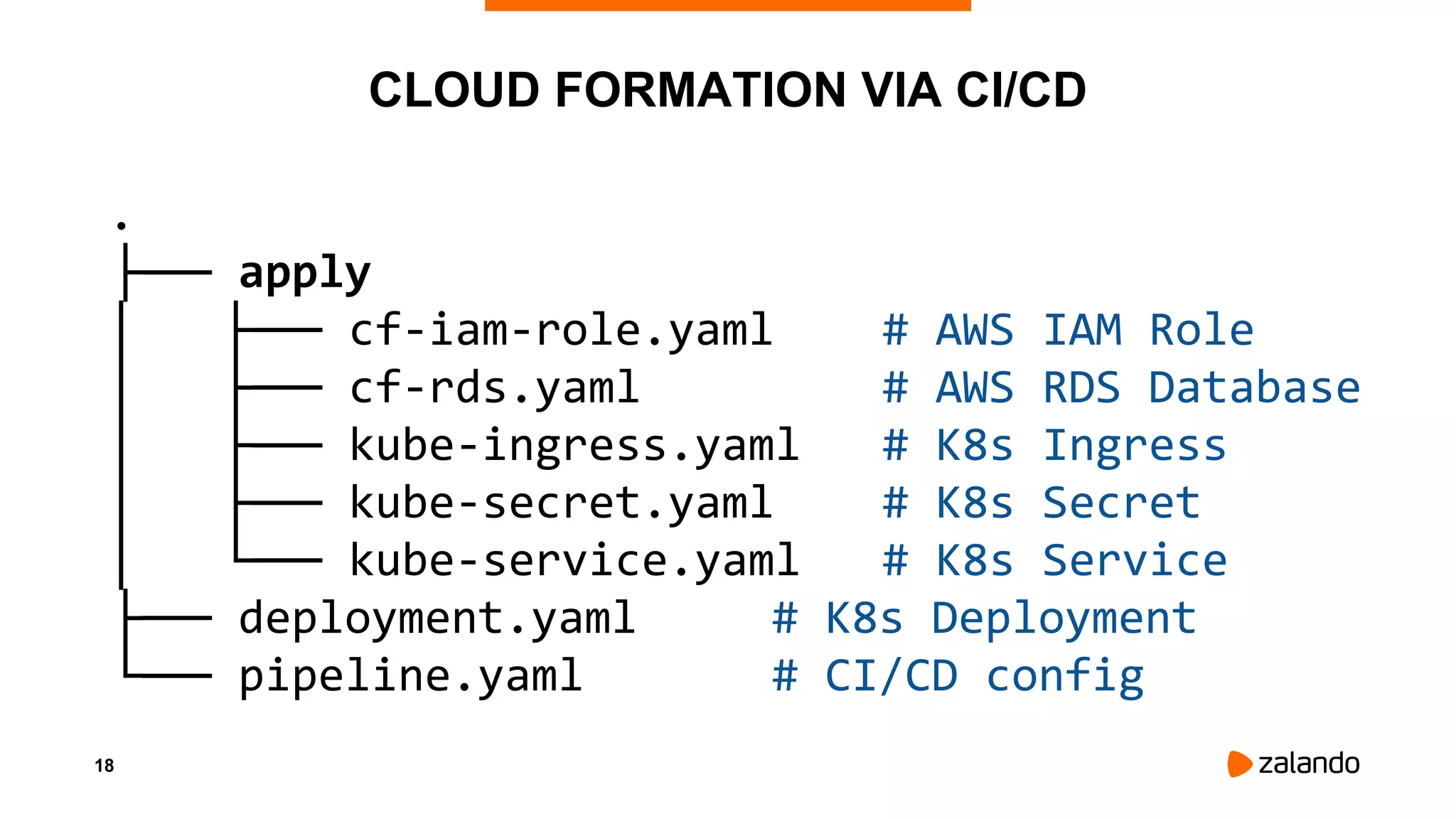
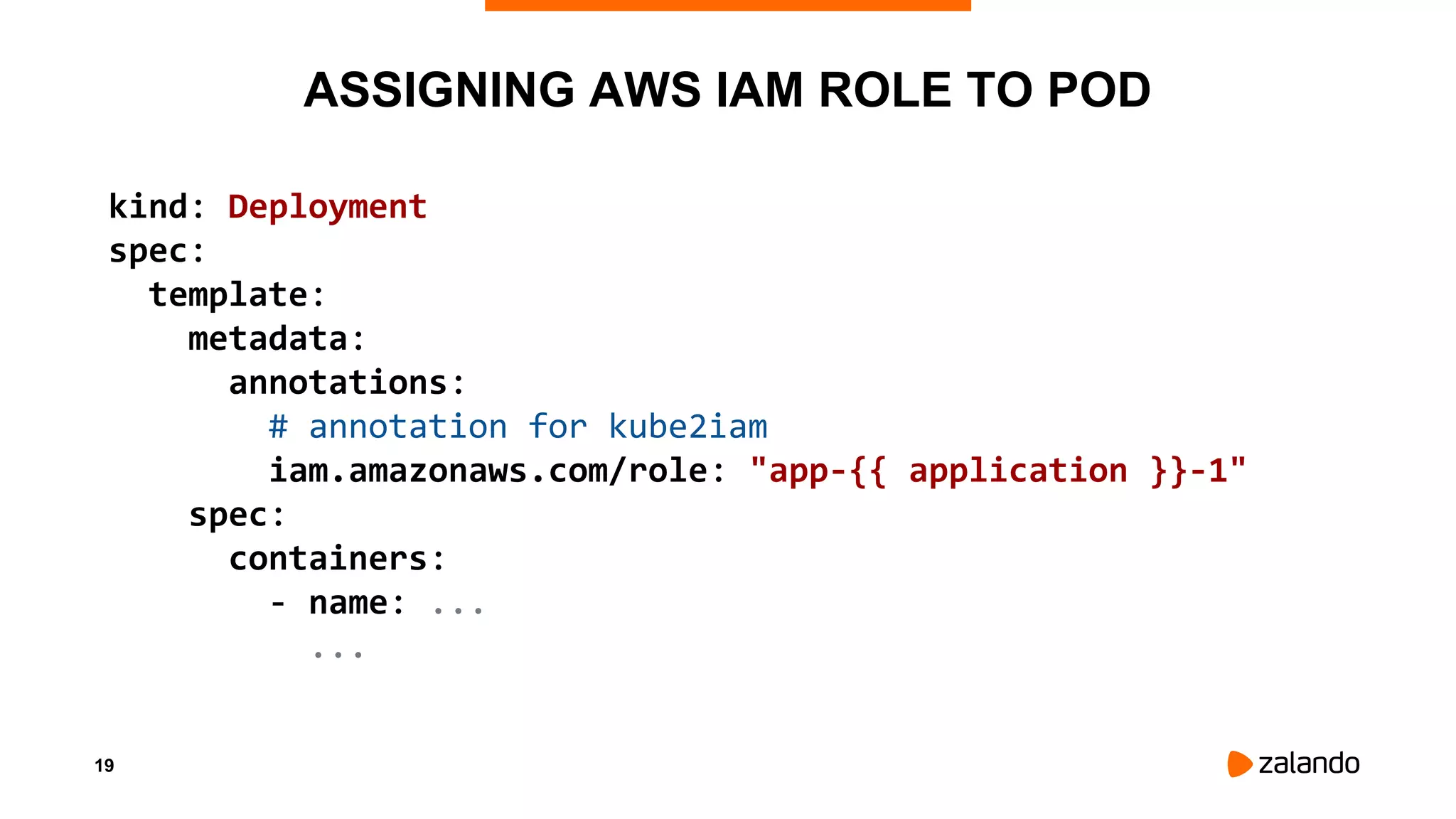
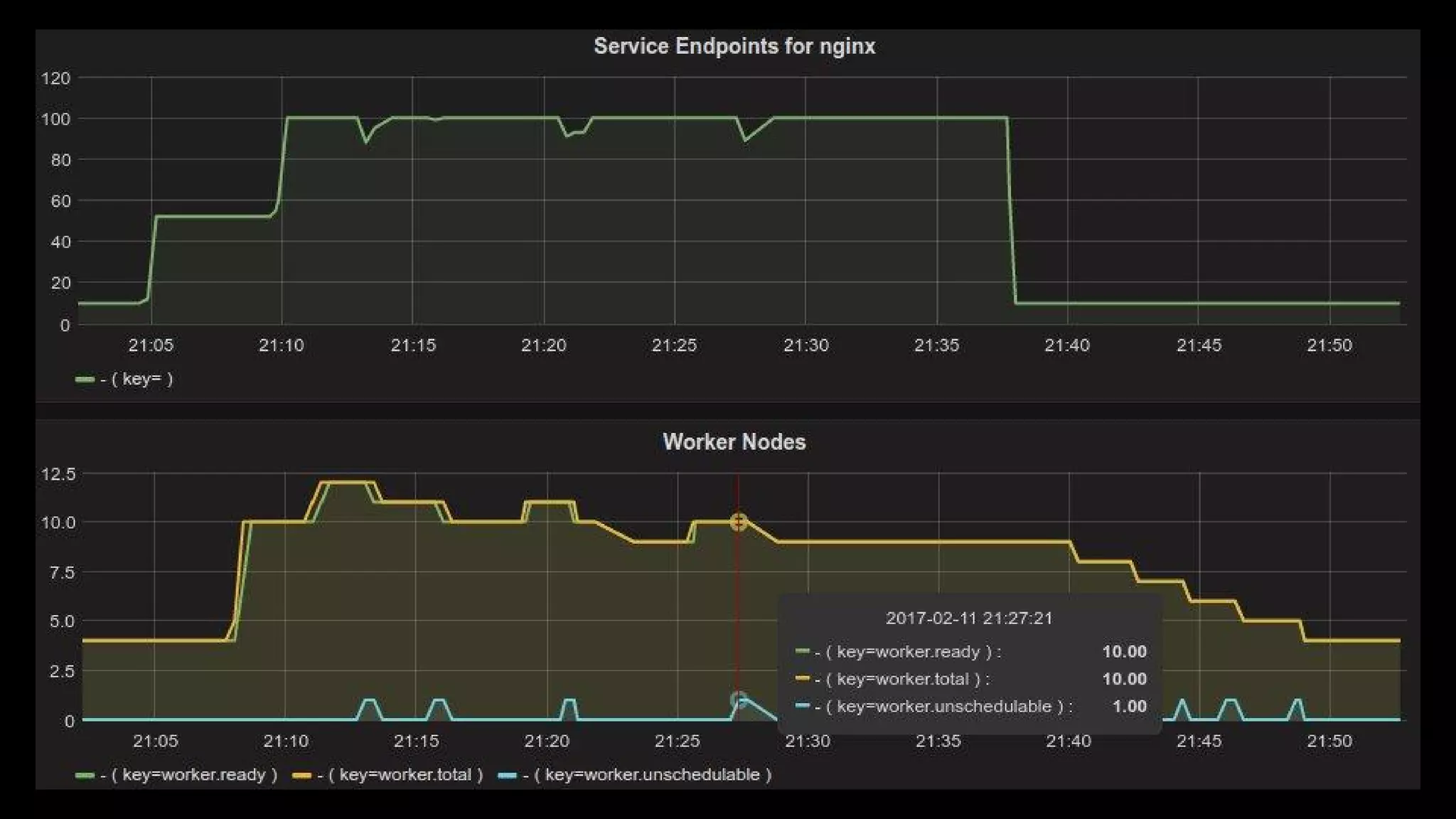
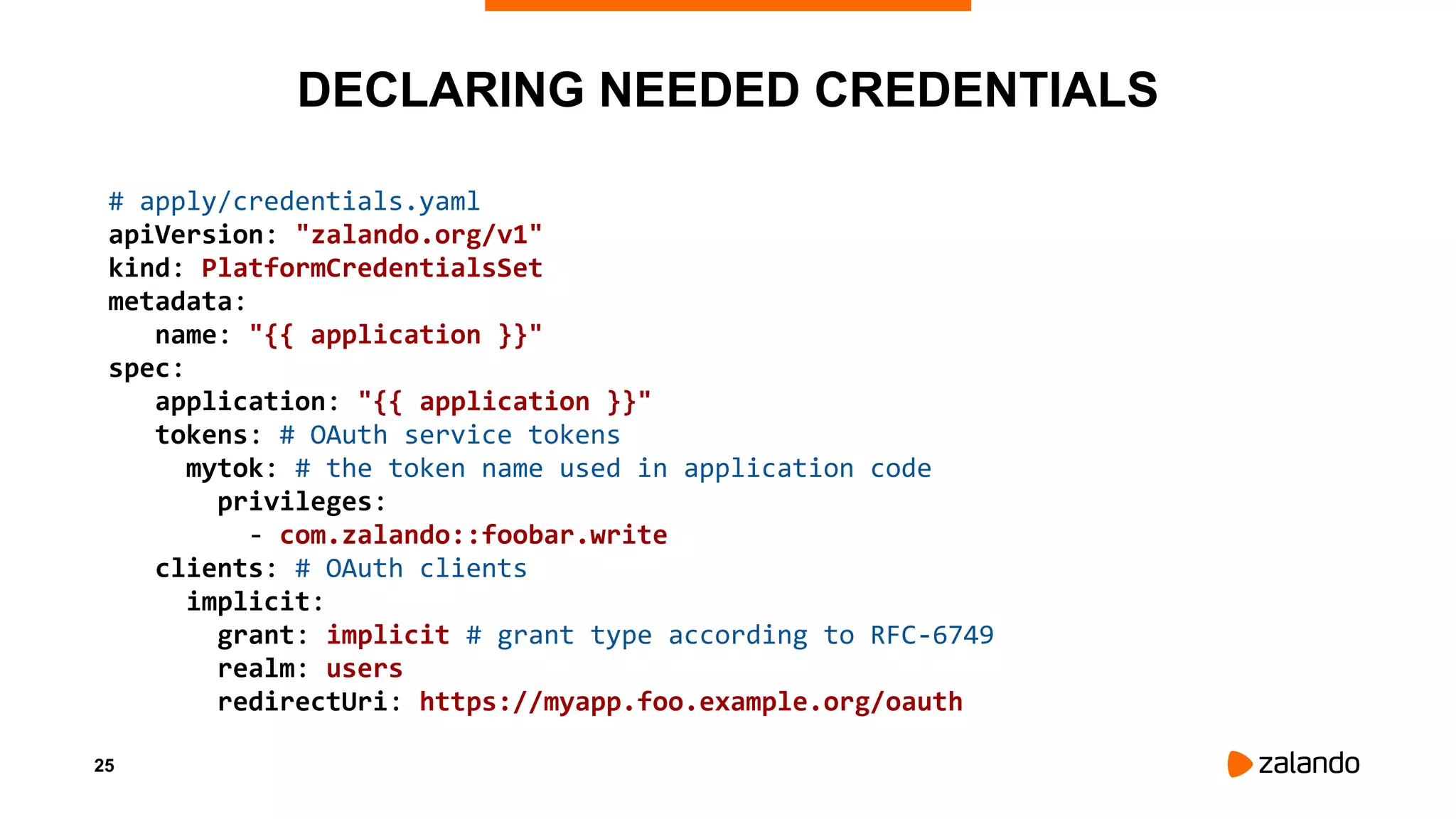
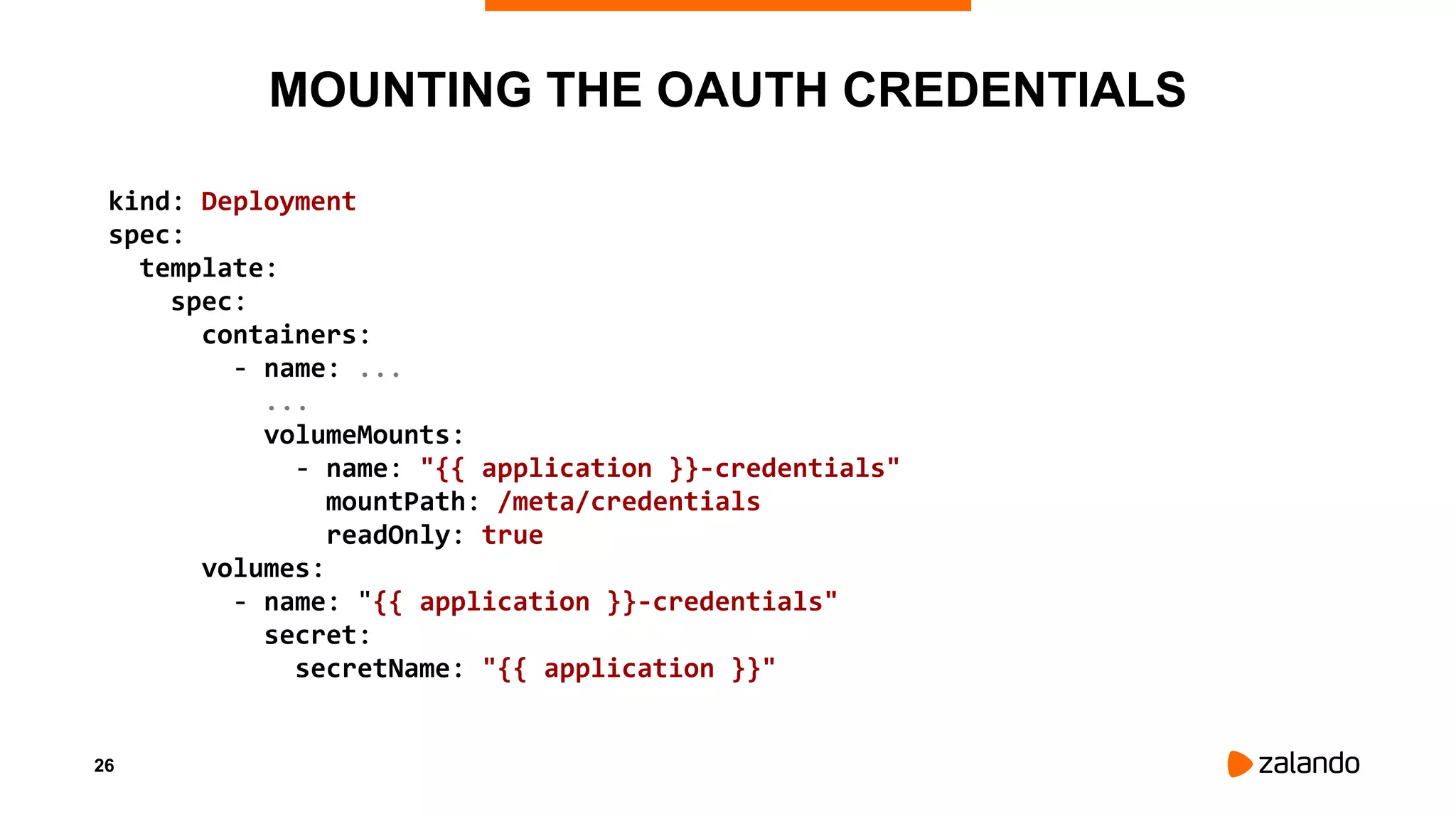
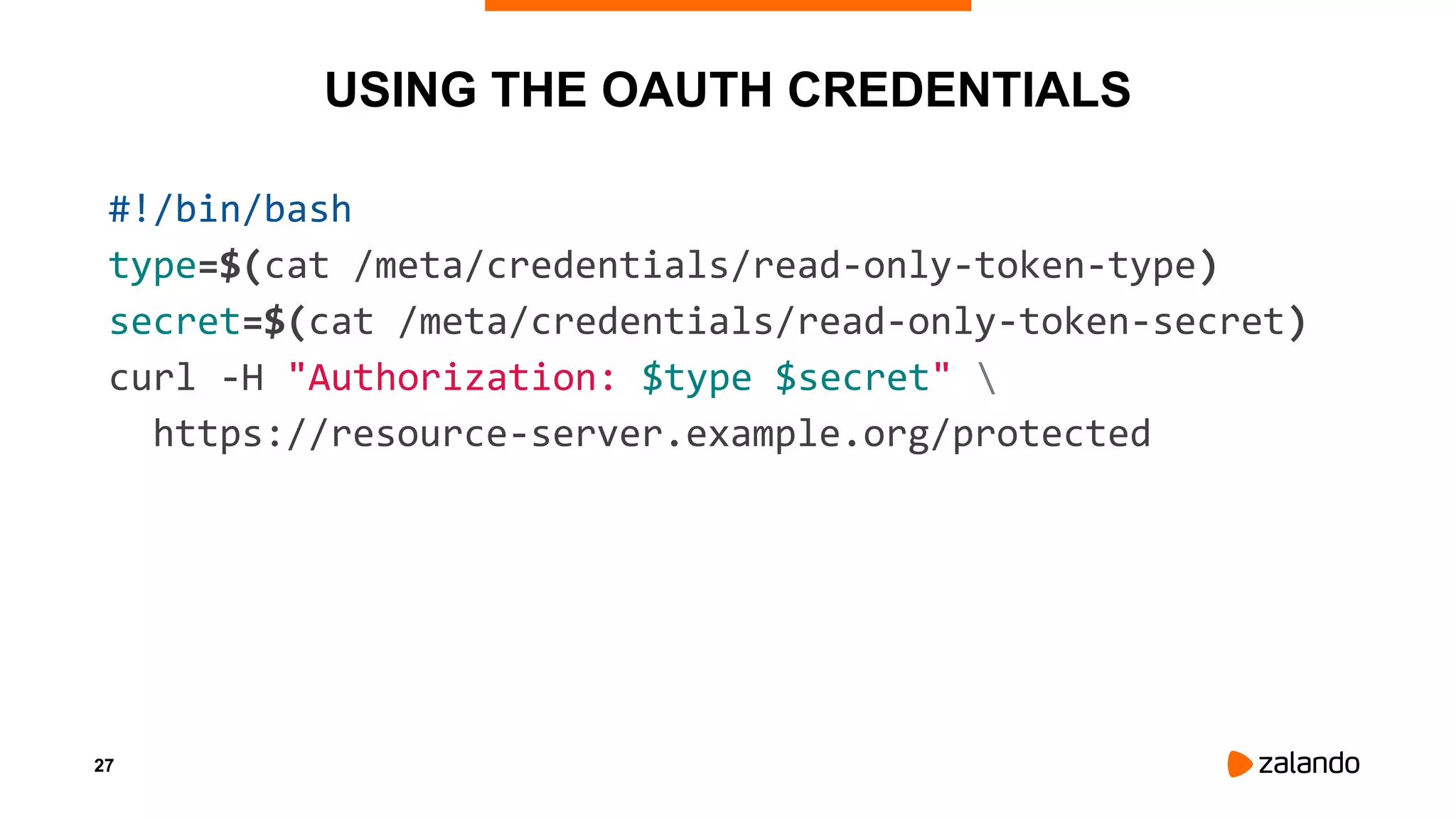
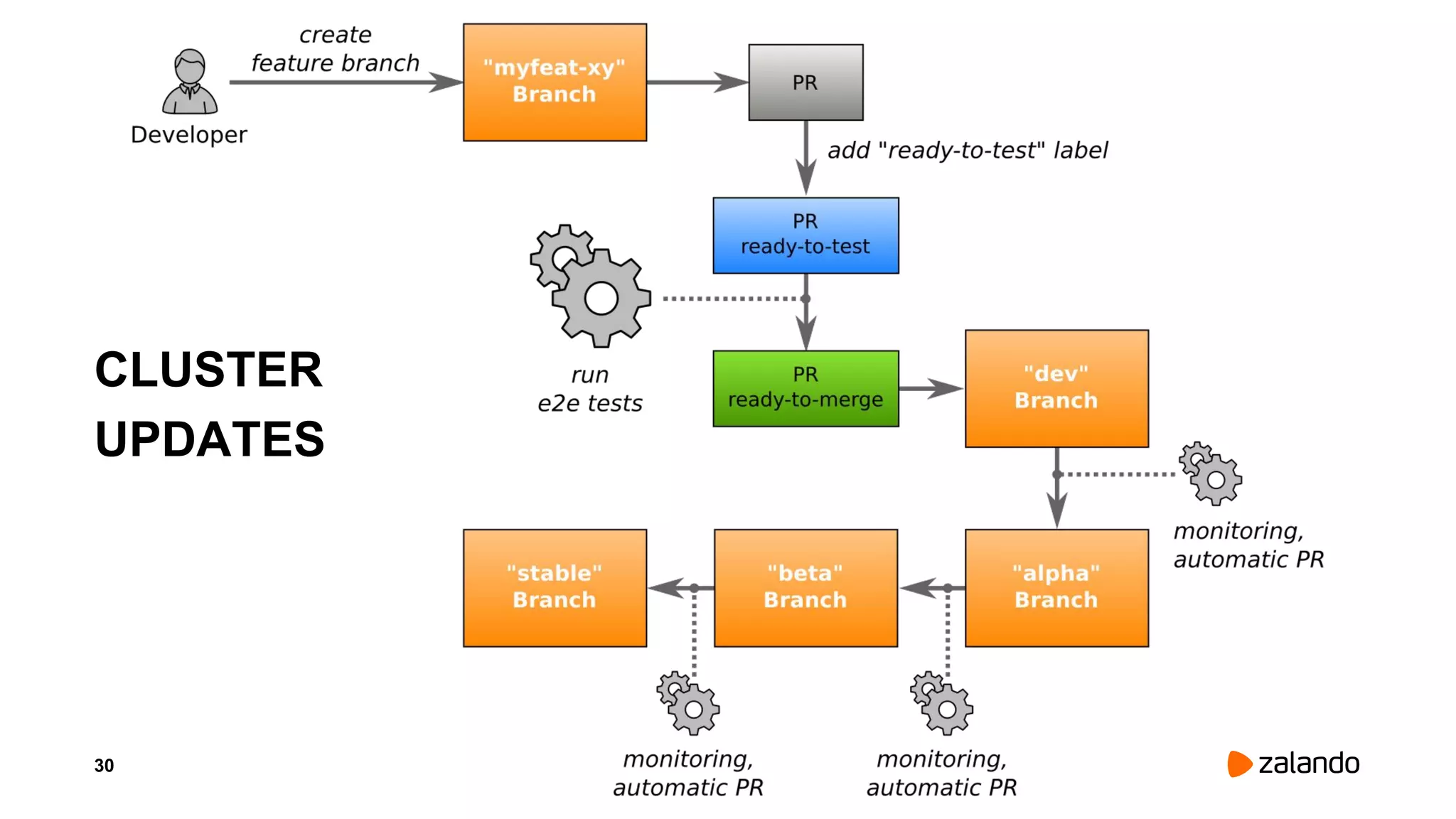
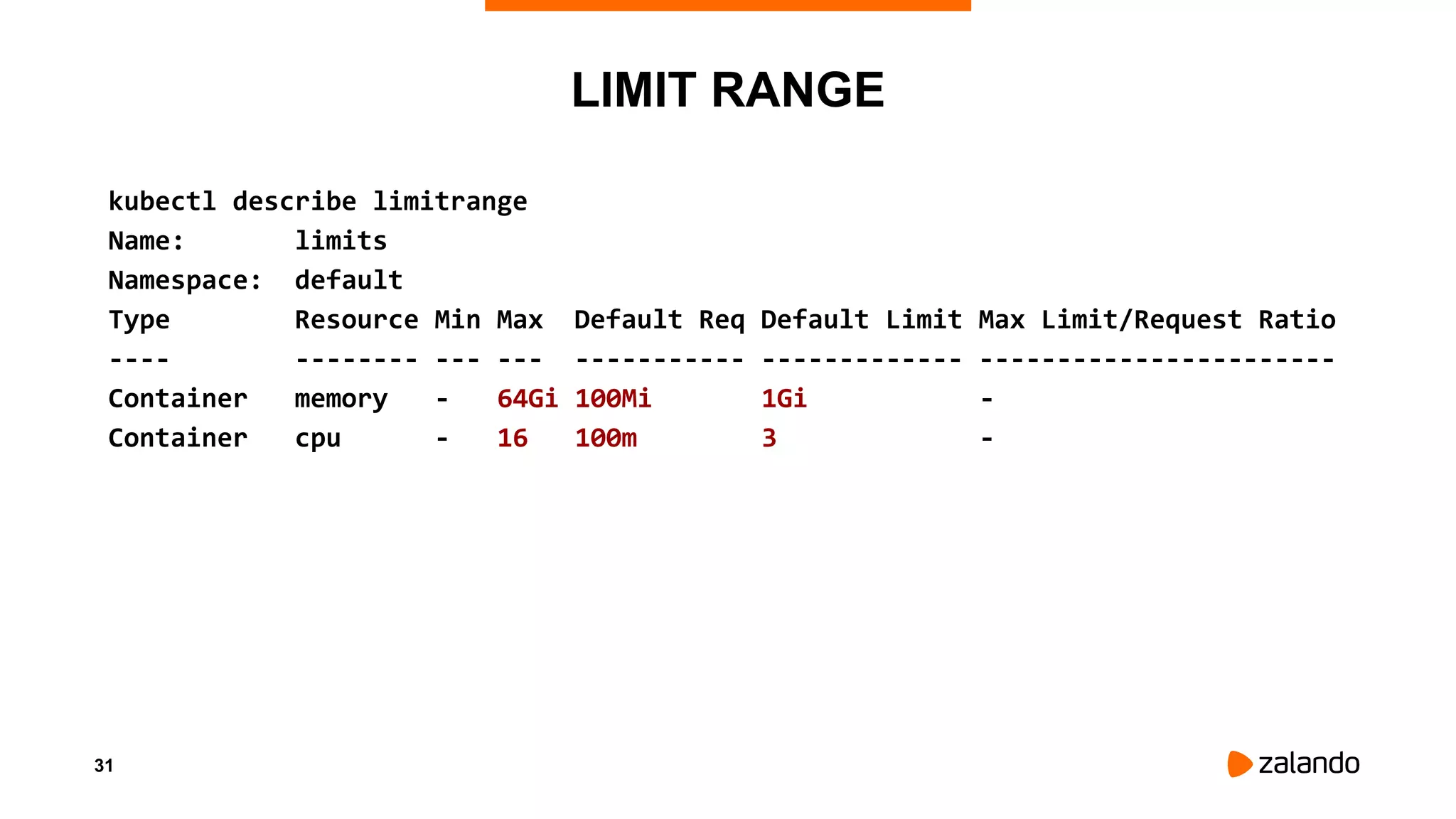
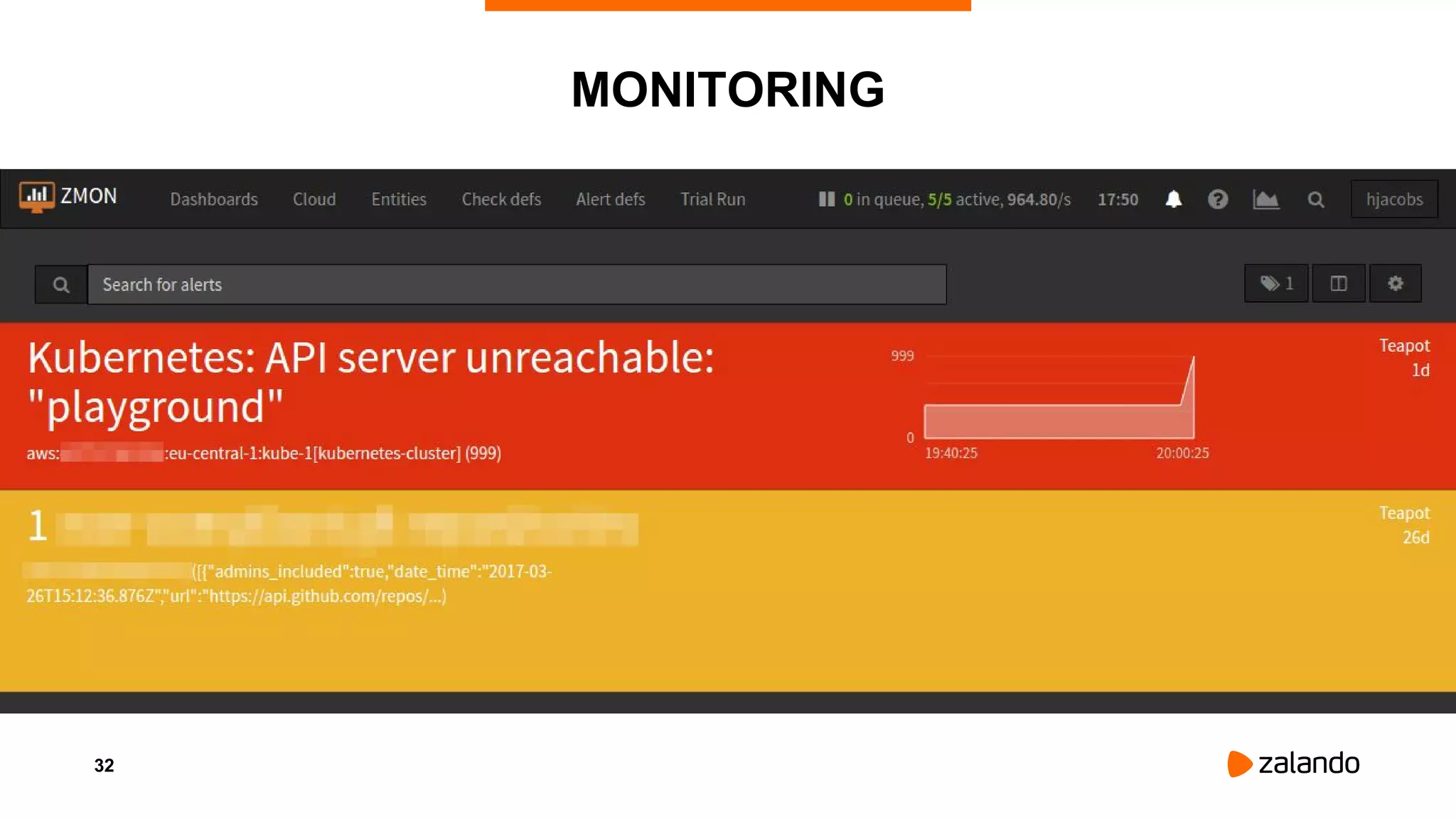
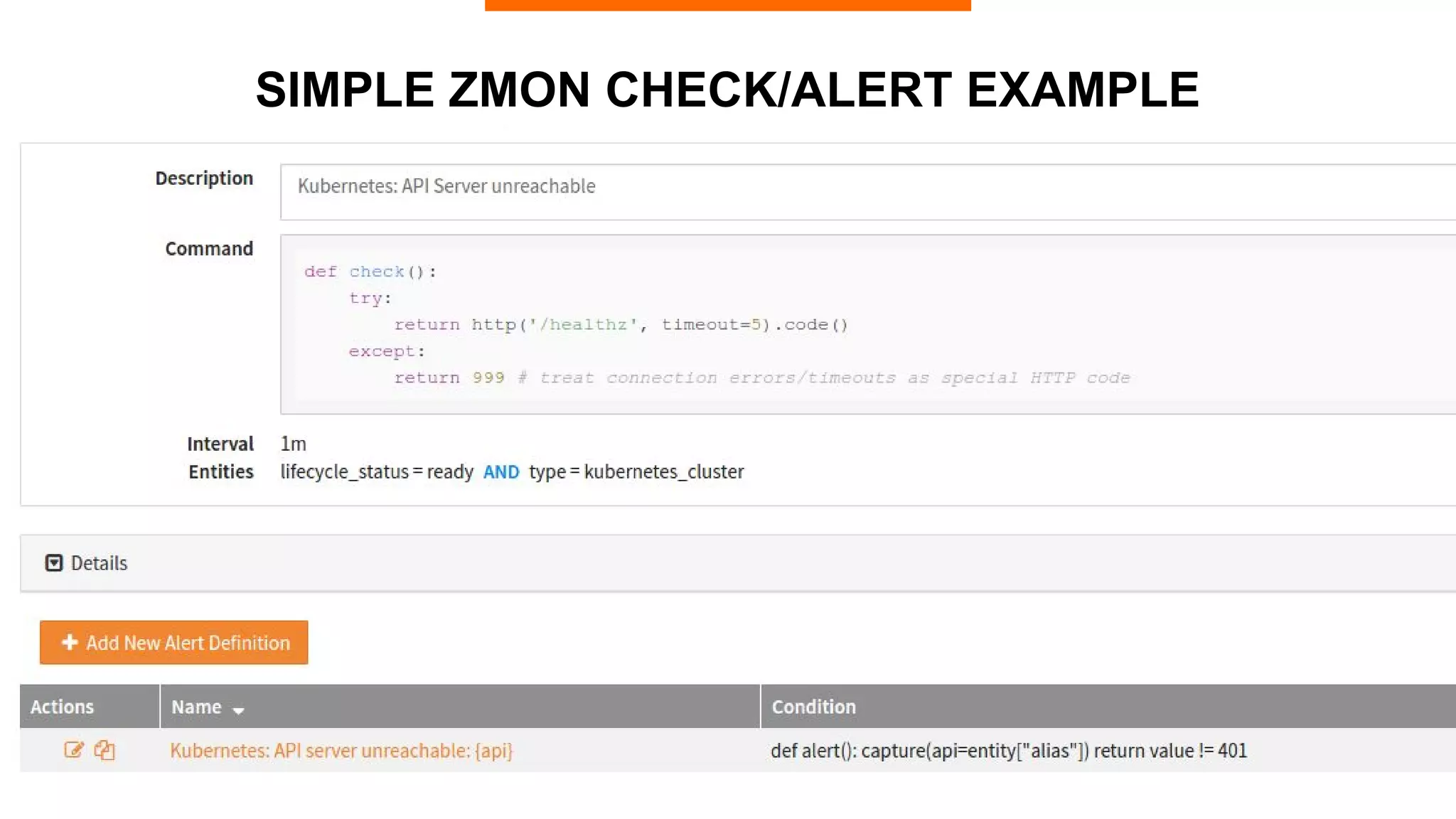
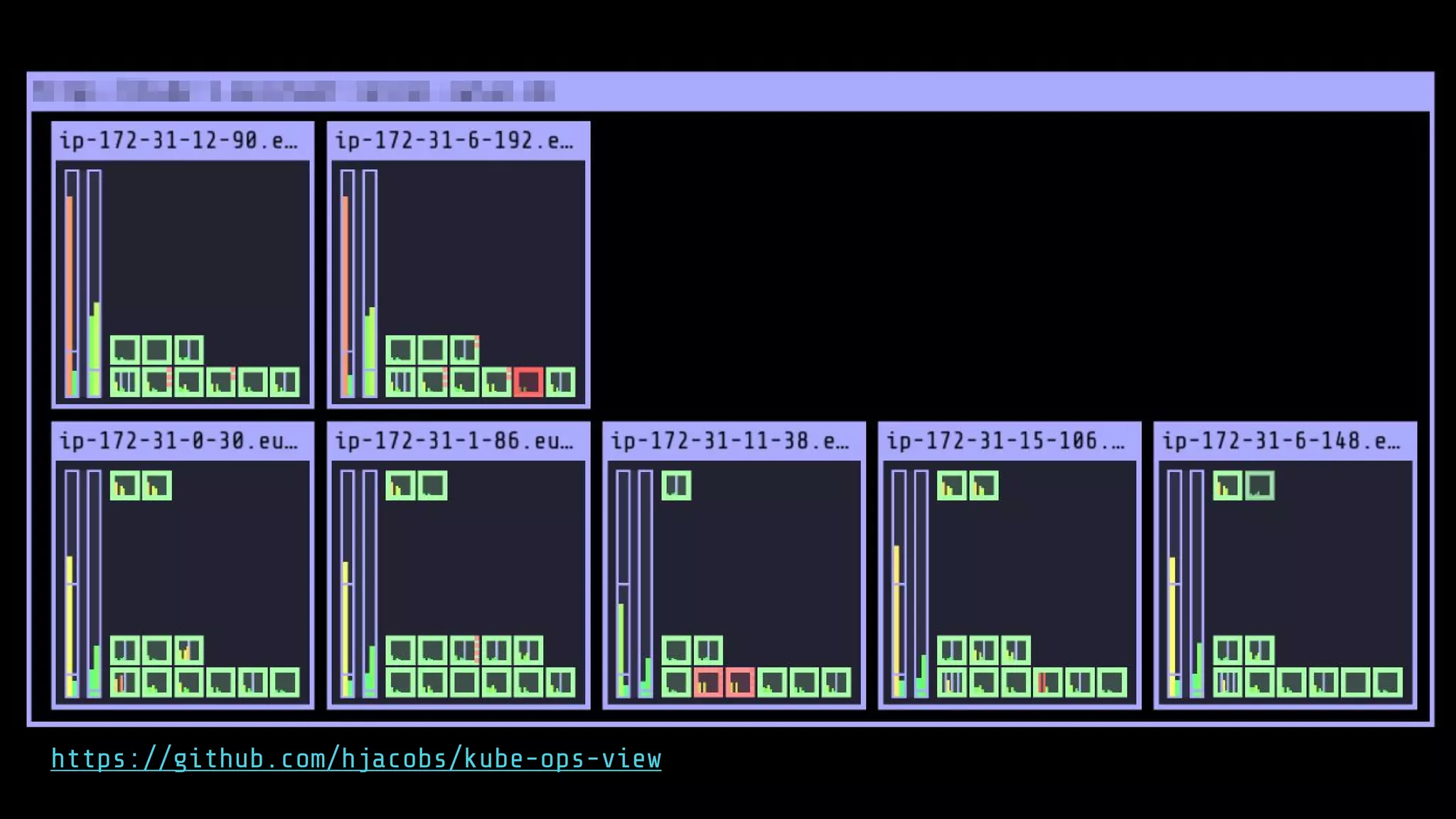
Zalando, Europe's leading online fashion platform, utilizes Kubernetes on AWS to manage over 200 engineering teams and 30 production clusters, accommodating 20 million active customers. The architecture features isolated AWS accounts, automated deployment and scaling, and integrates OAuth for authentication and authorization. Cloud formation allows for CI/CD pipeline management, while monitoring and operations are executed through ZMON to ensure reliable performance.