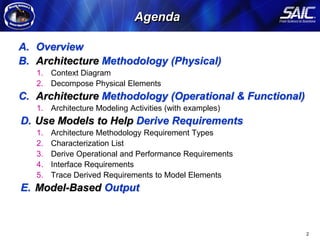
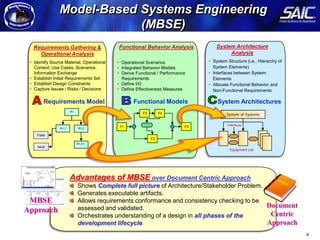
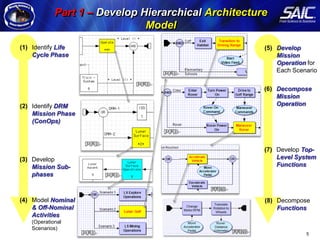
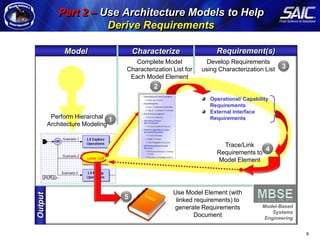
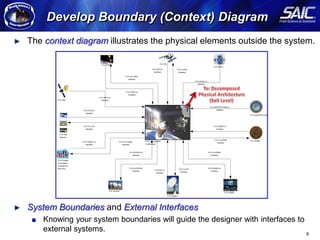
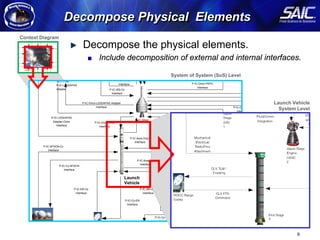
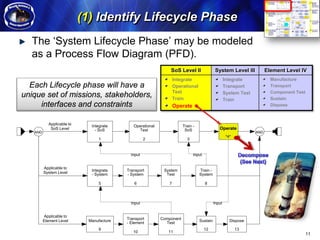
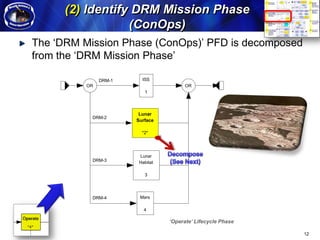
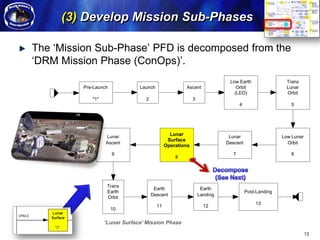
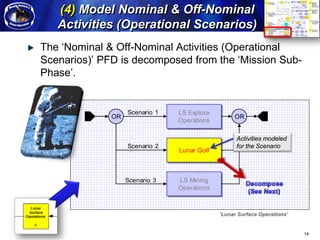
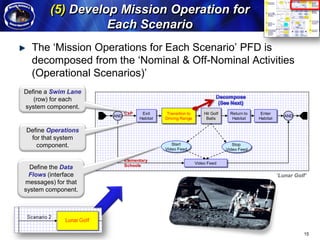
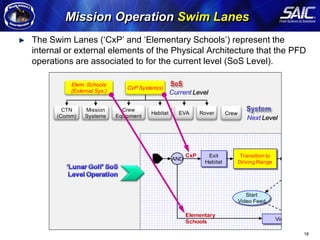
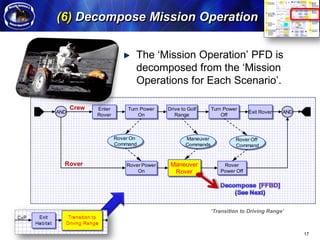
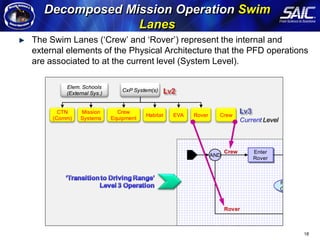
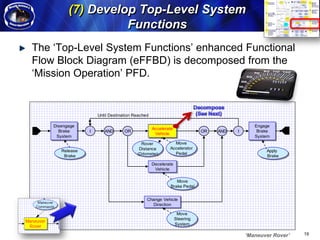
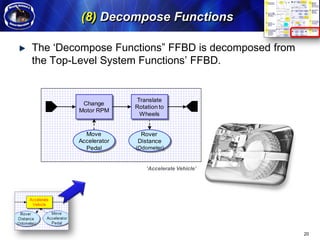
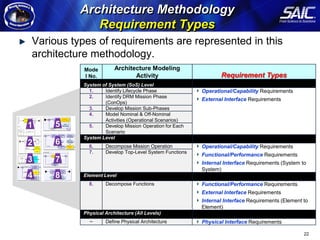
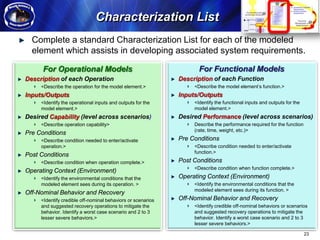
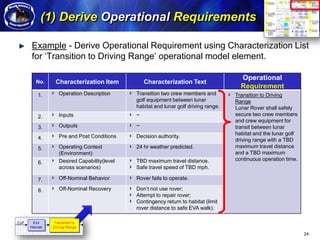
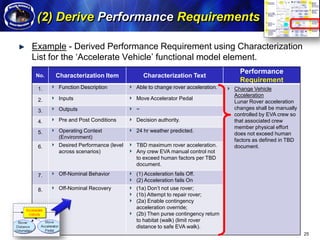
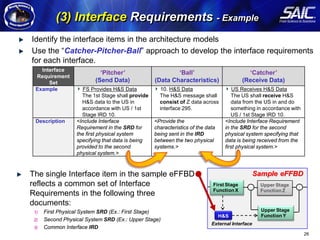
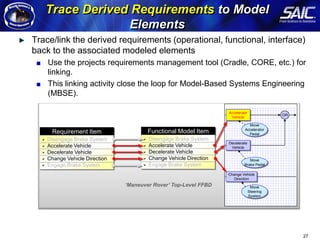
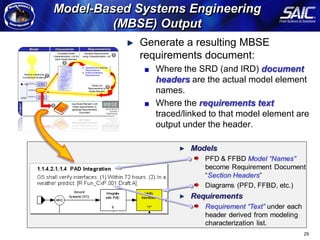
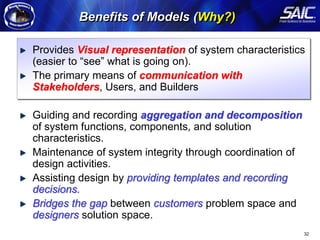
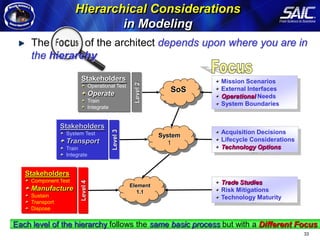
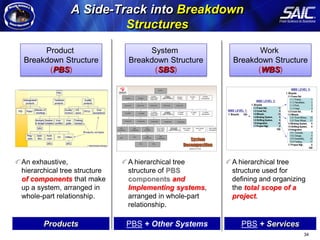
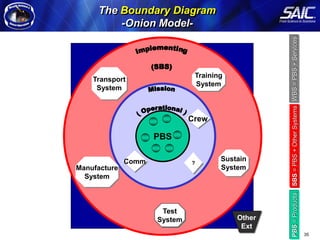
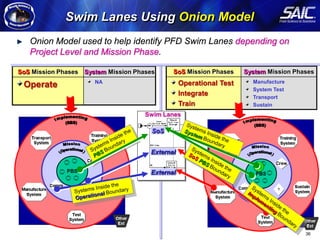
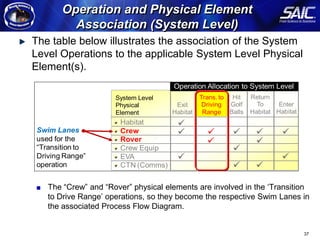
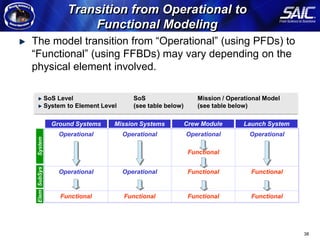
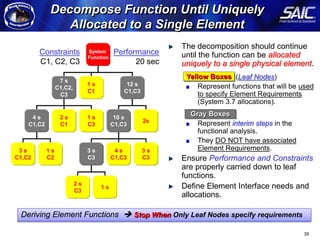
The document discusses an architecture modeling methodology for model-based systems engineering projects. It involves developing hierarchical architecture models, using the models to derive requirements, and tracing requirements to model elements. The methodology includes context diagrams to illustrate physical elements outside the system, decomposing physical and operational/functional elements, and using operational scenarios to develop mission operations and system functions. The modeling approach aims to generate a complete picture of the architecture and stakeholder problem.