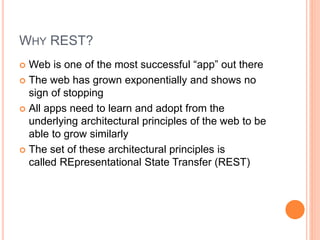
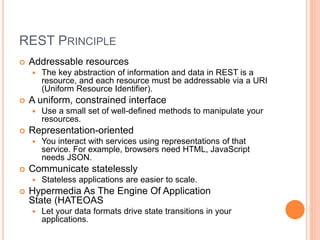
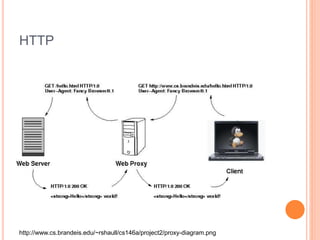
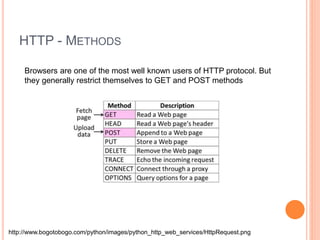
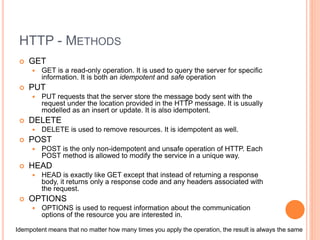
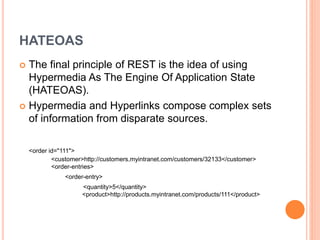
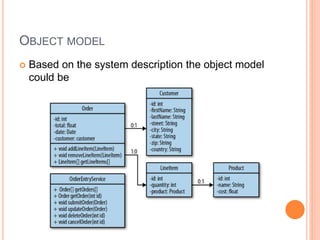
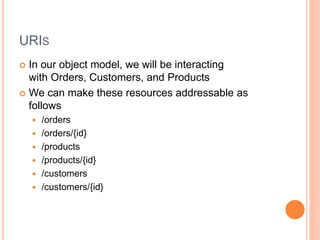
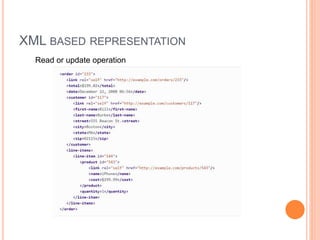
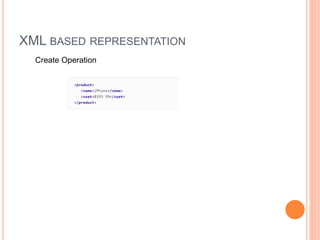
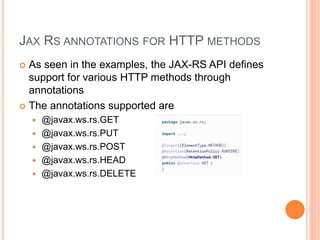
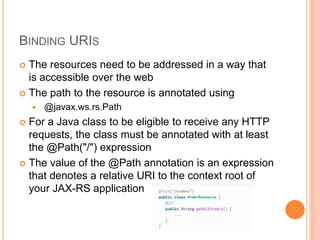
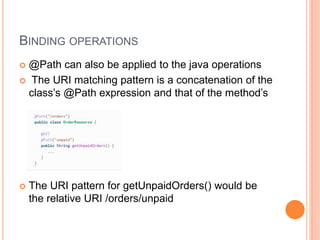
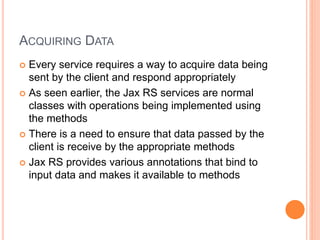
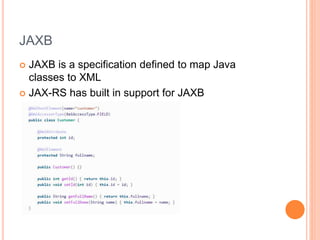
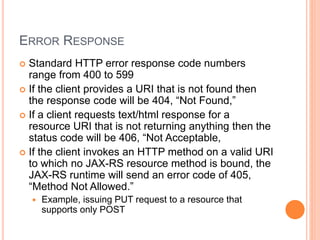
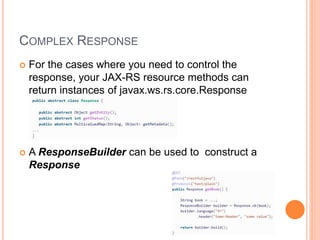
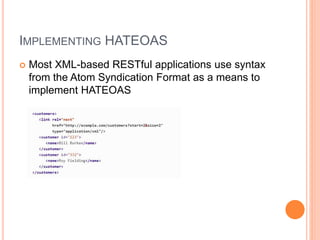
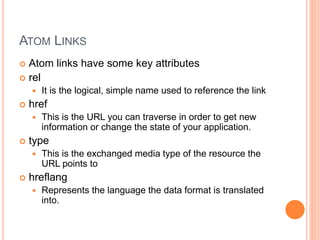
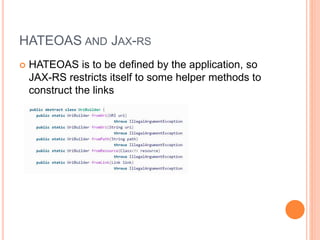
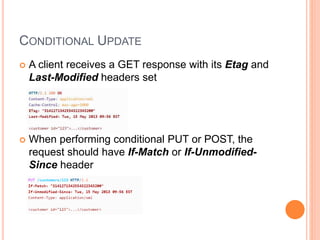
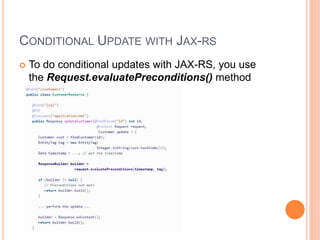
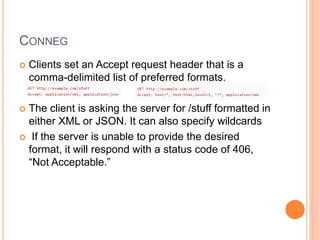
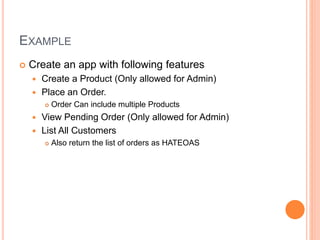
The document outlines Jerry Kurian's extensive experience in developing RESTful applications using JAX-RS, as well as the principles and practices involved in REST architecture. It describes the key concepts of REST, including addressable resources, stateless communication, and the use of HTTP methods for CRUD operations. Additionally, it provides guidance on building Java-based RESTful applications, including object modeling, URI definition, and JAX-RS annotations for handling HTTP requests and responses.