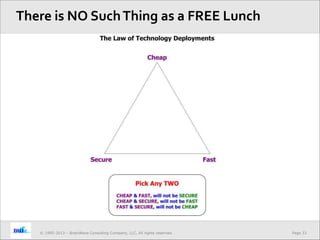
The document discusses approaches for ensuring IT security for NGOs with global presences and limited resources. It emphasizes managing security through the lens of people, procedures, and tools. The presentation outlines key premises of information security, such as treating it as a lifestyle rather than an event. It provides suggestions for dealing with challenges like maintaining security on a limited budget and in a global setting. It stresses the importance of having the right people, clear and simple procedures, and tools used to implement security policies.