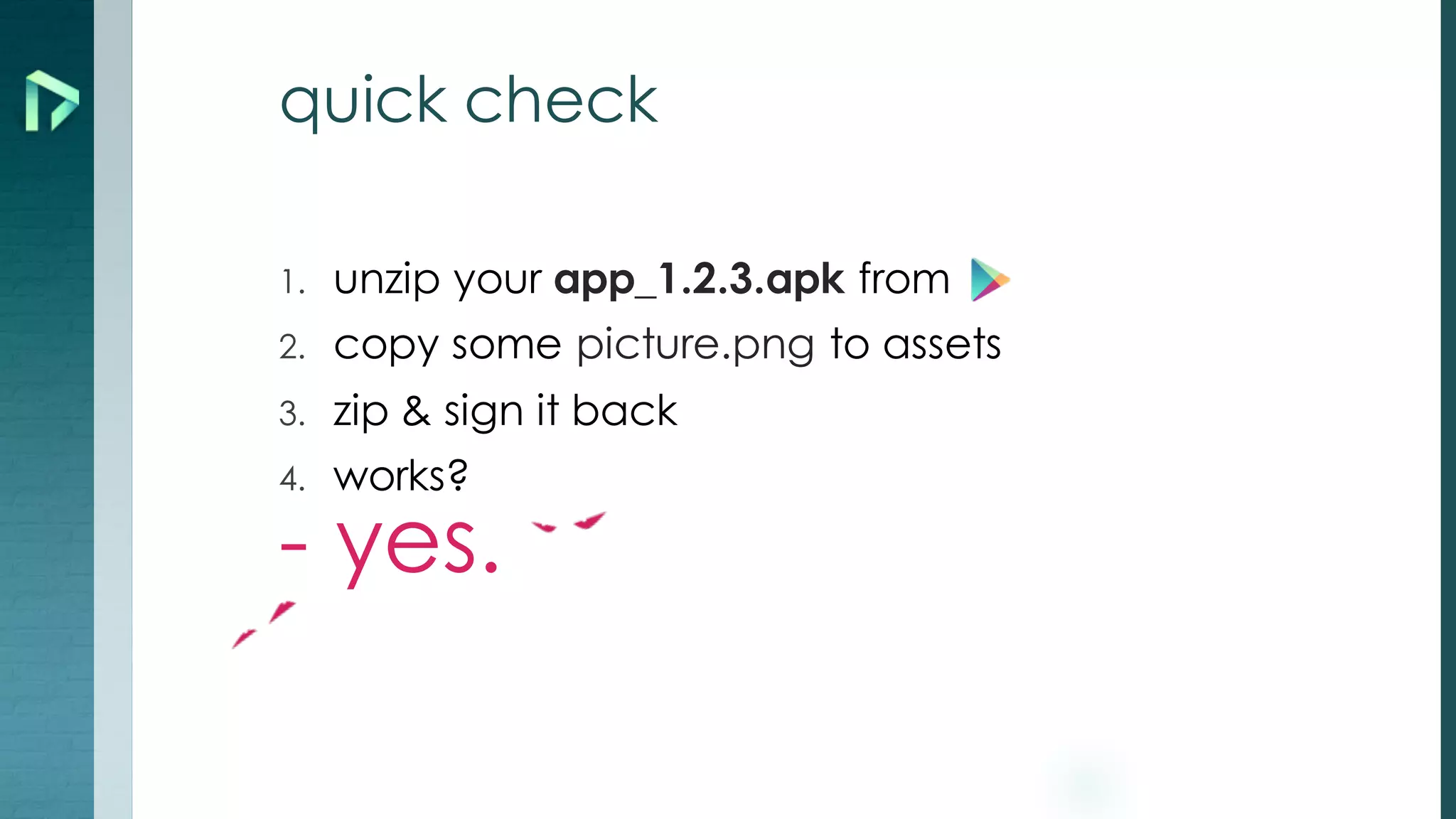
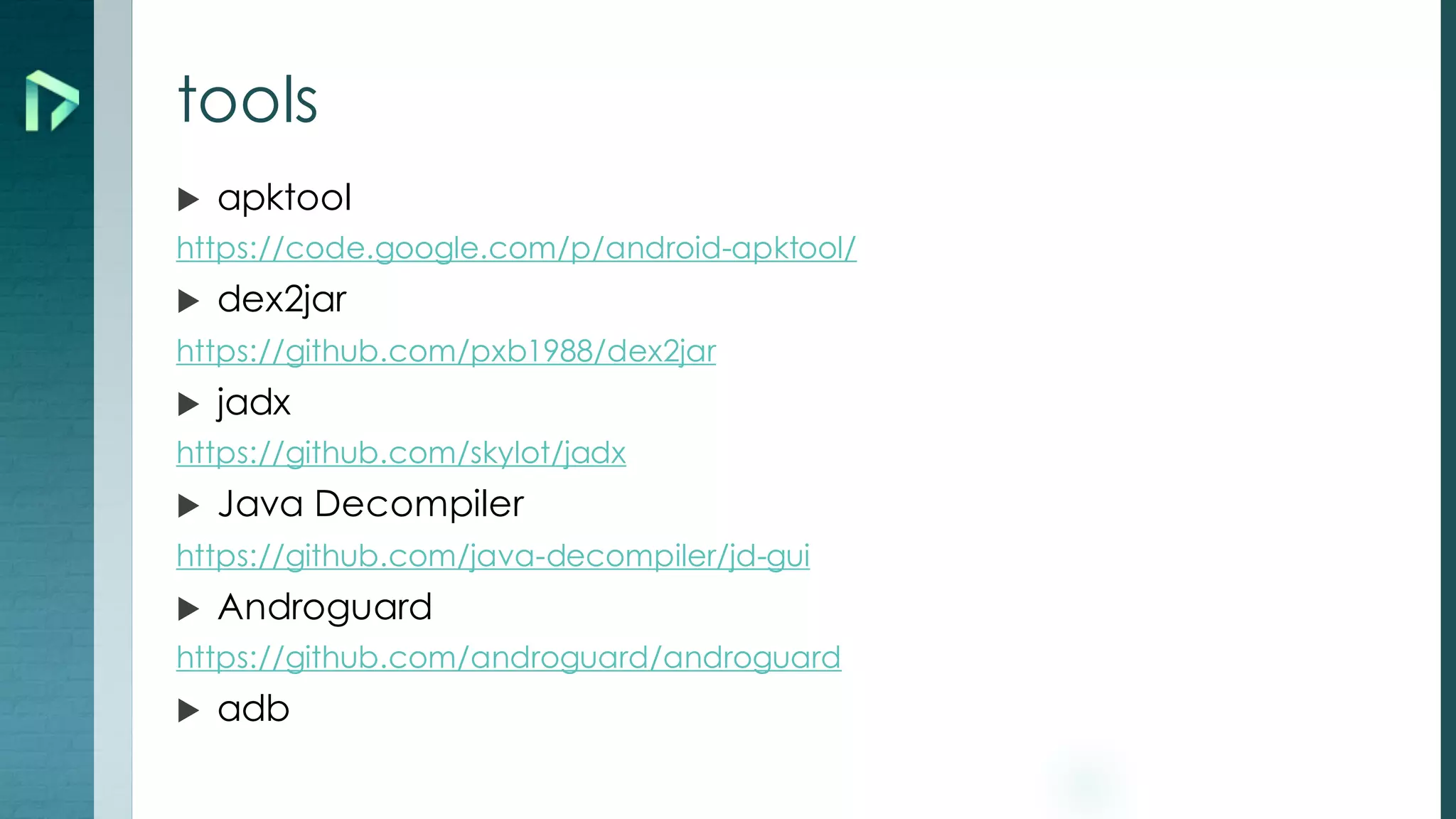
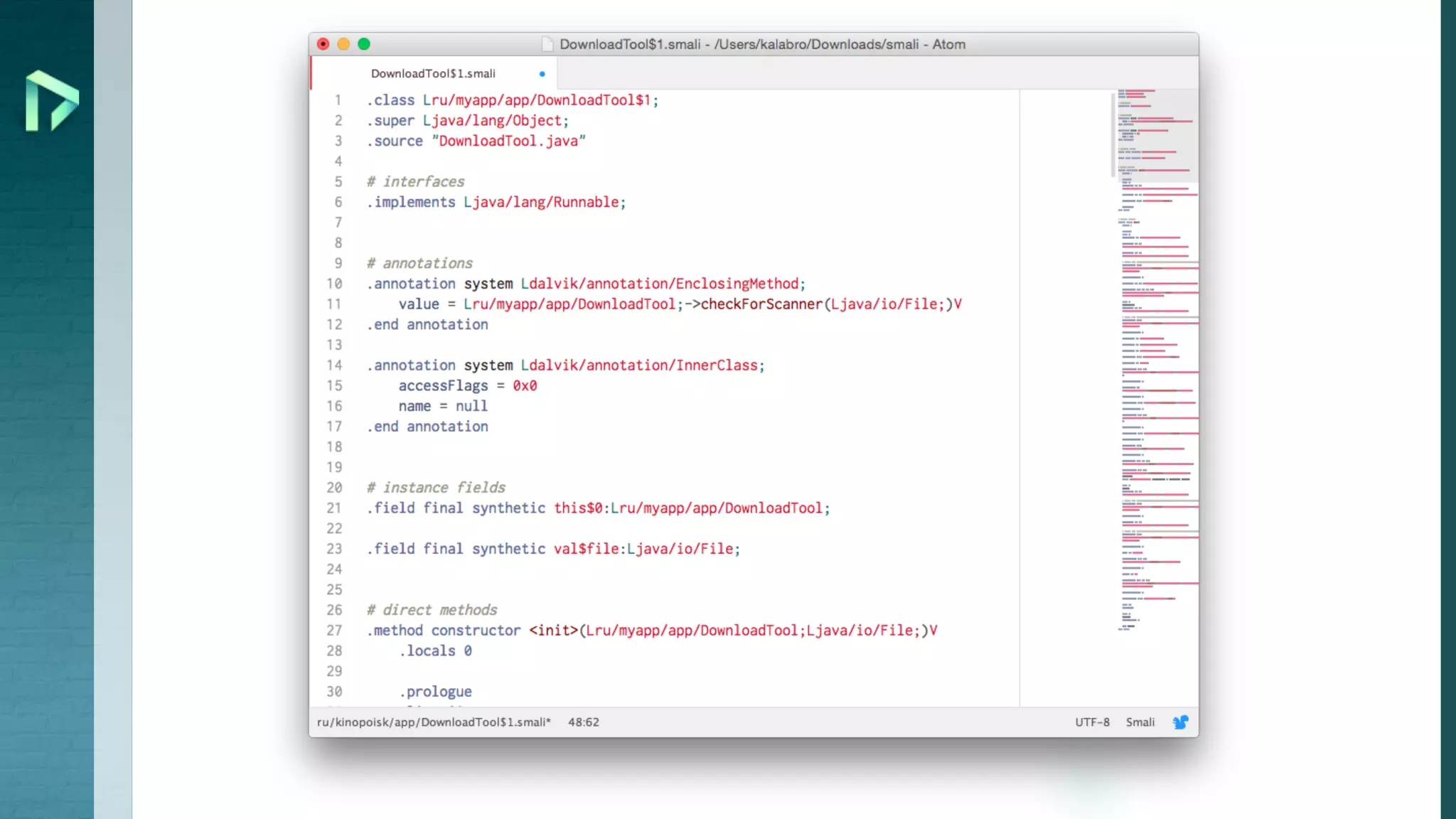
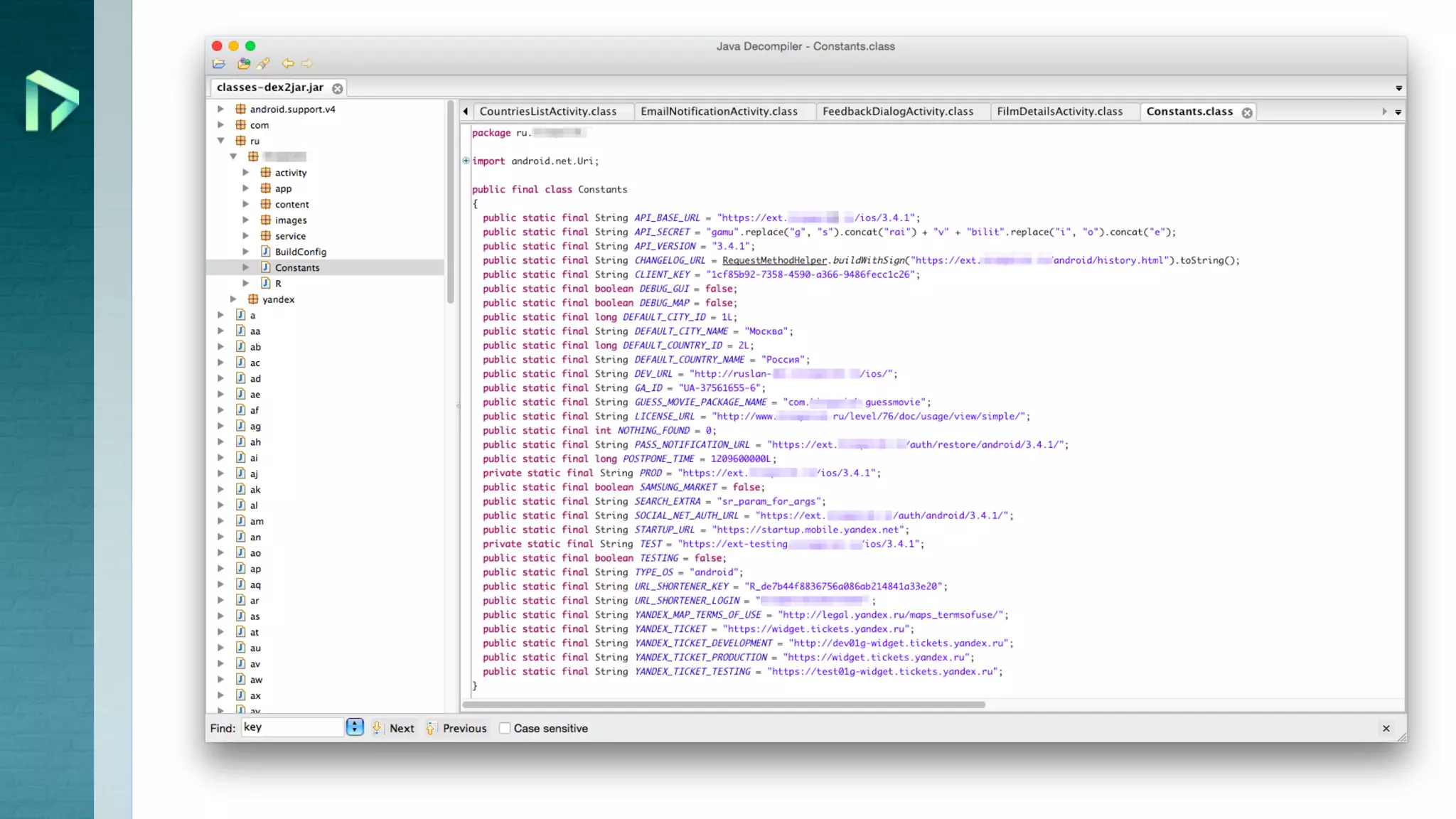
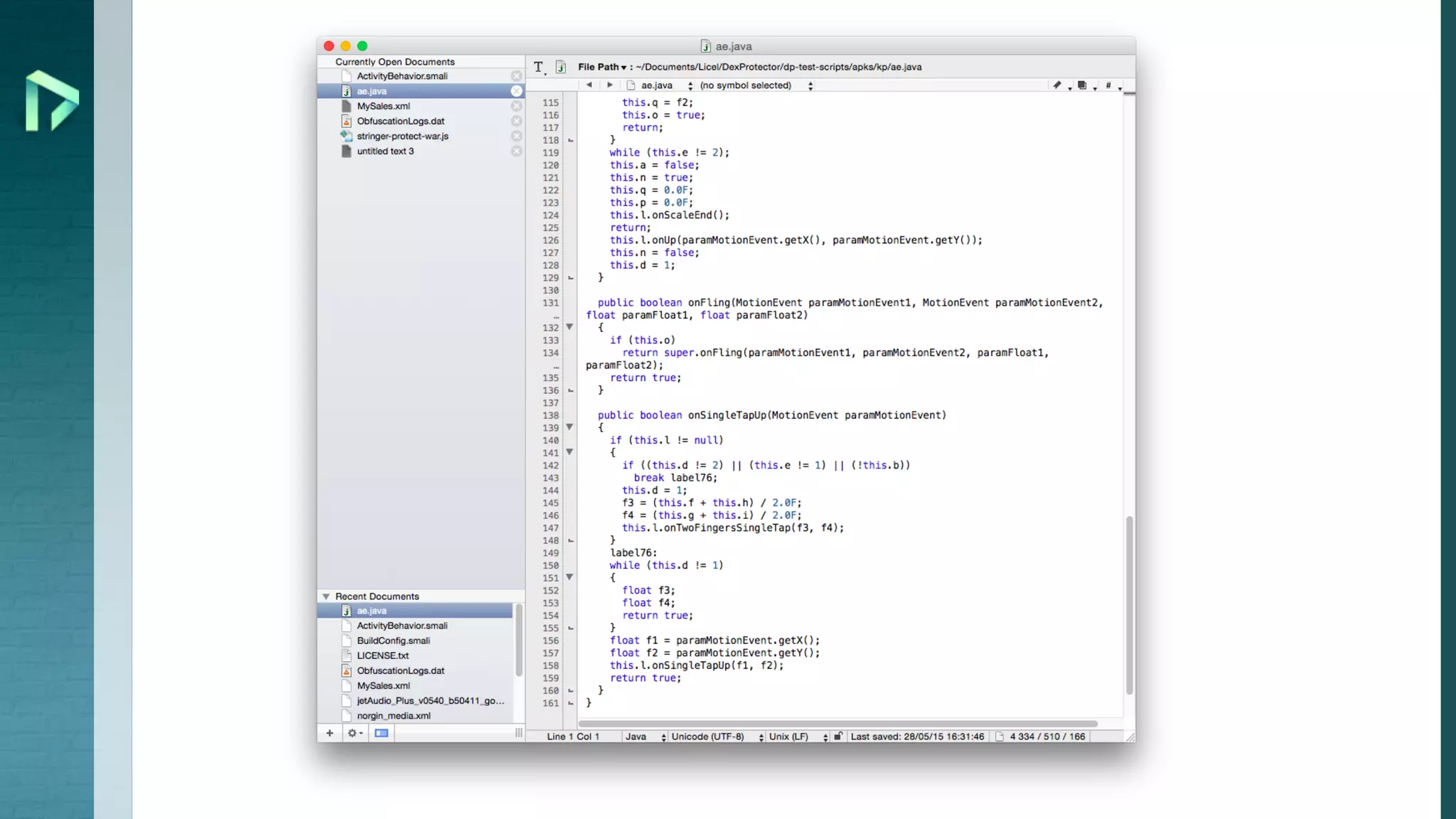
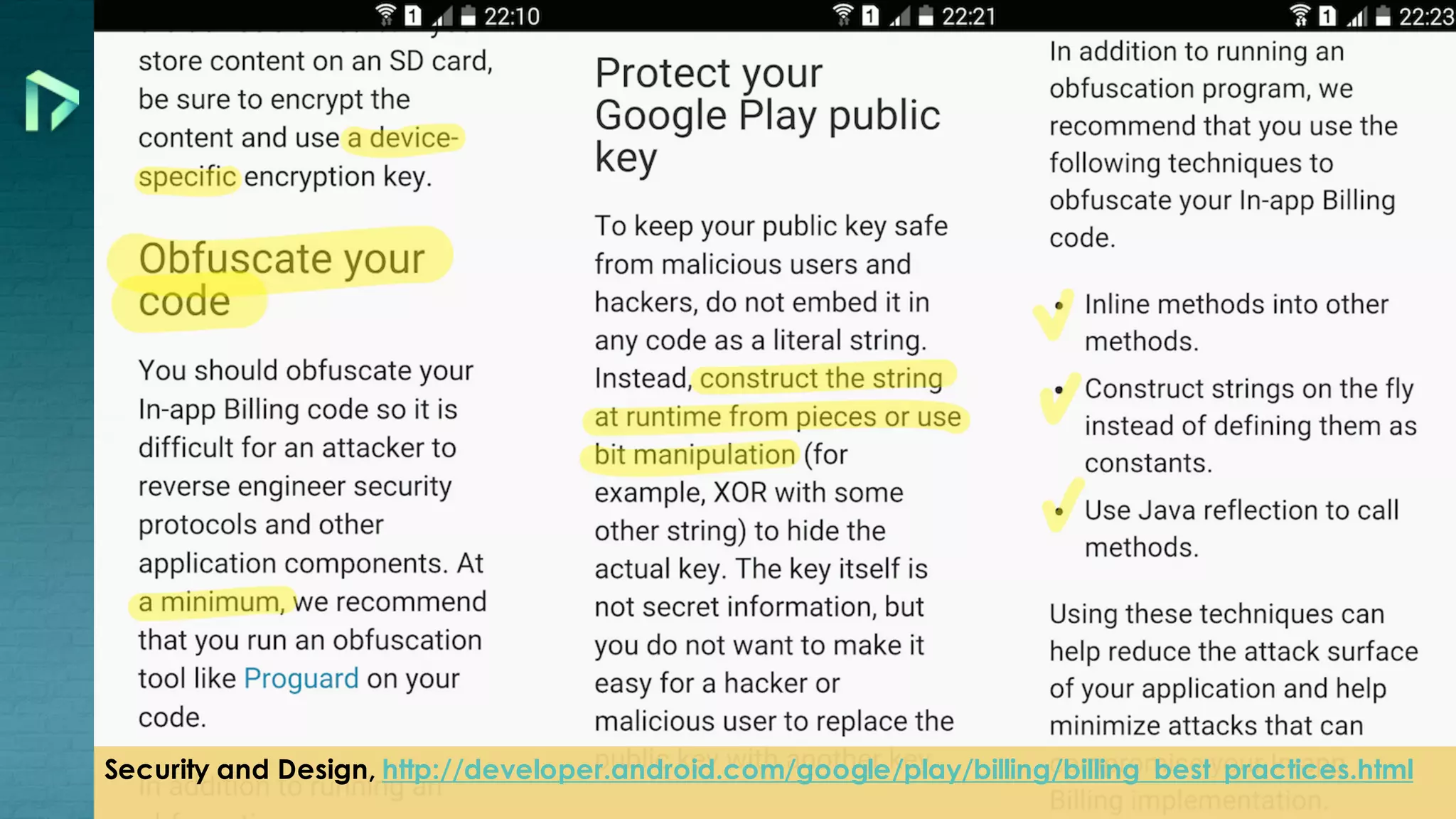
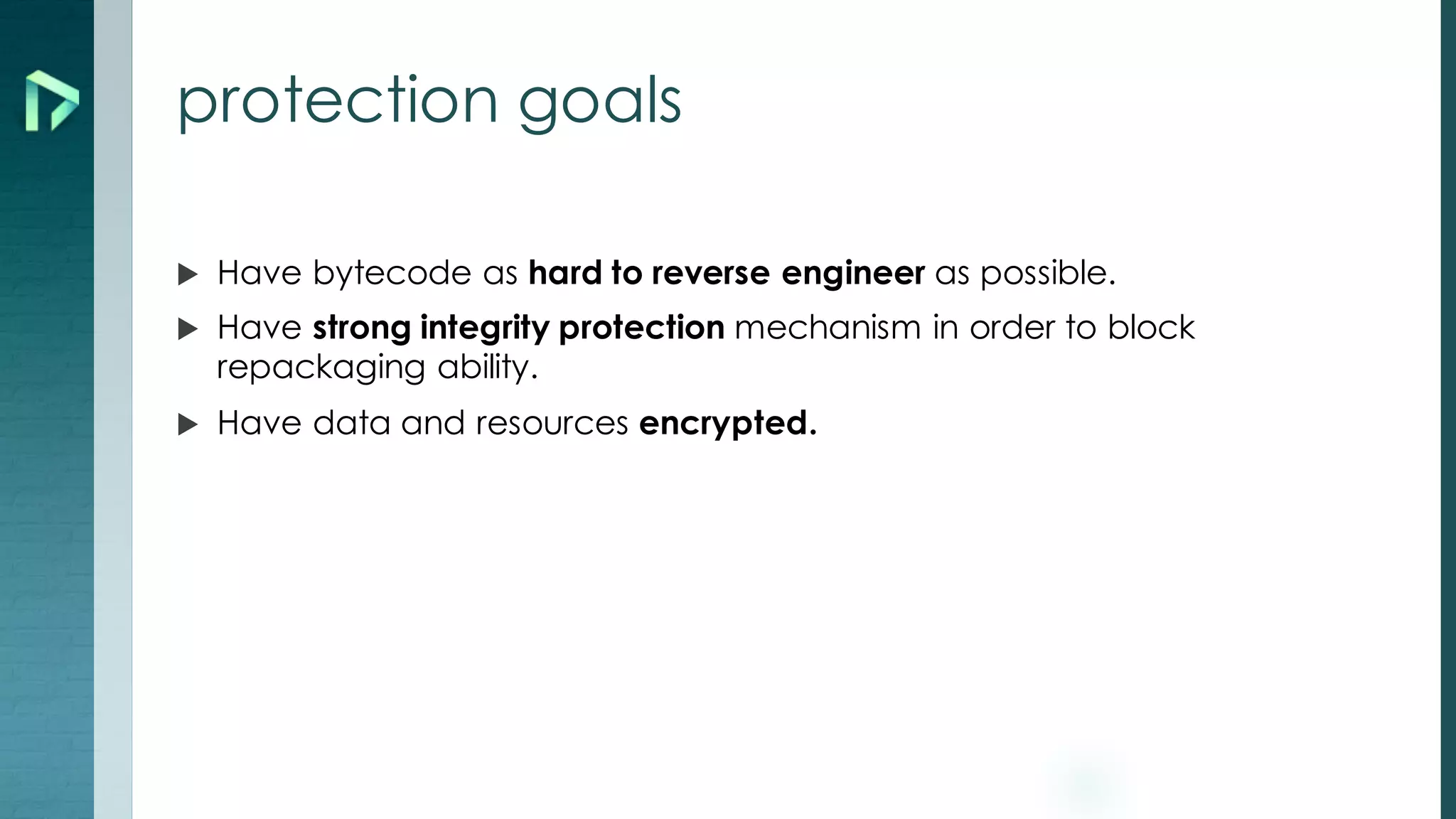
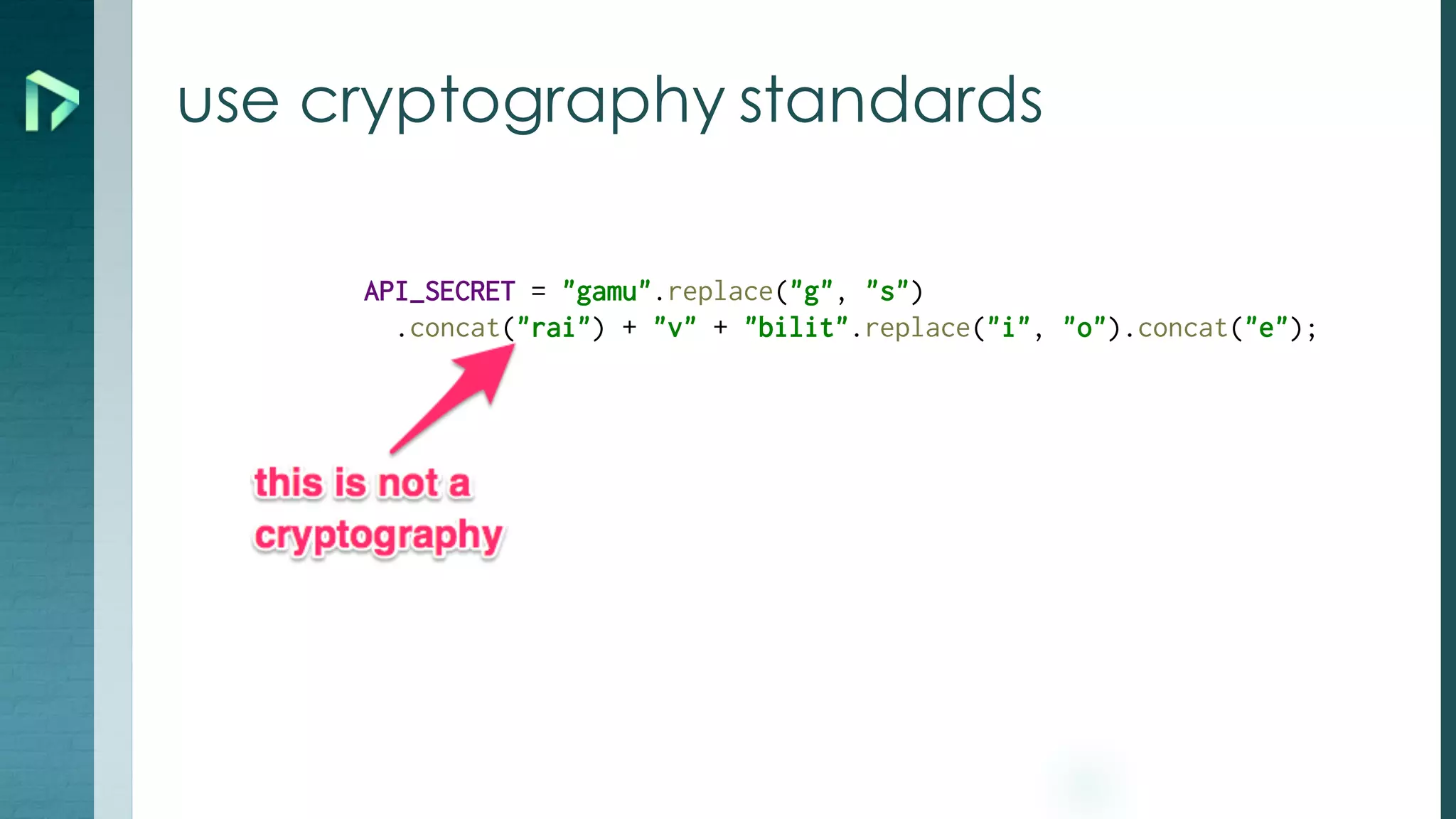
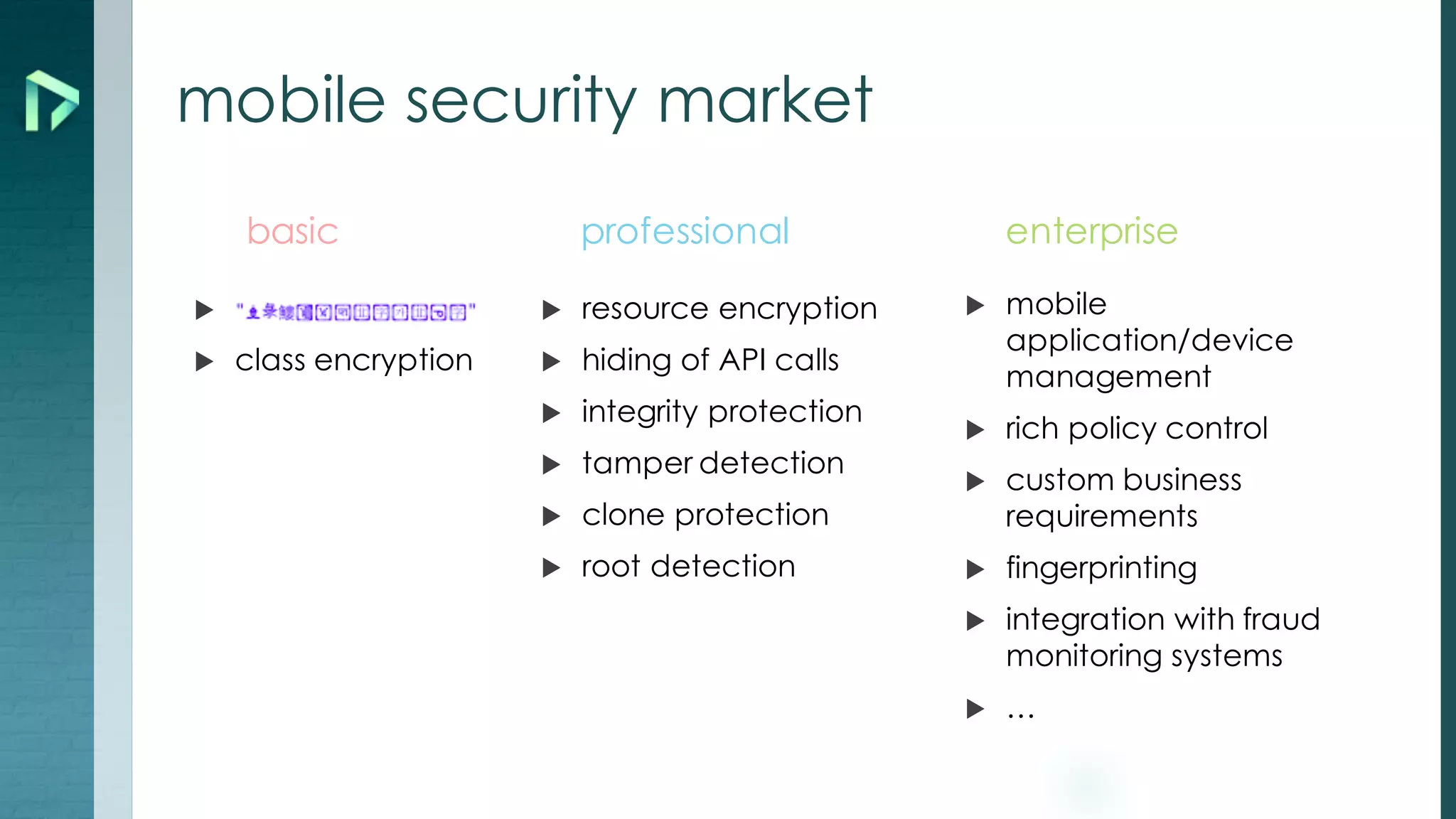
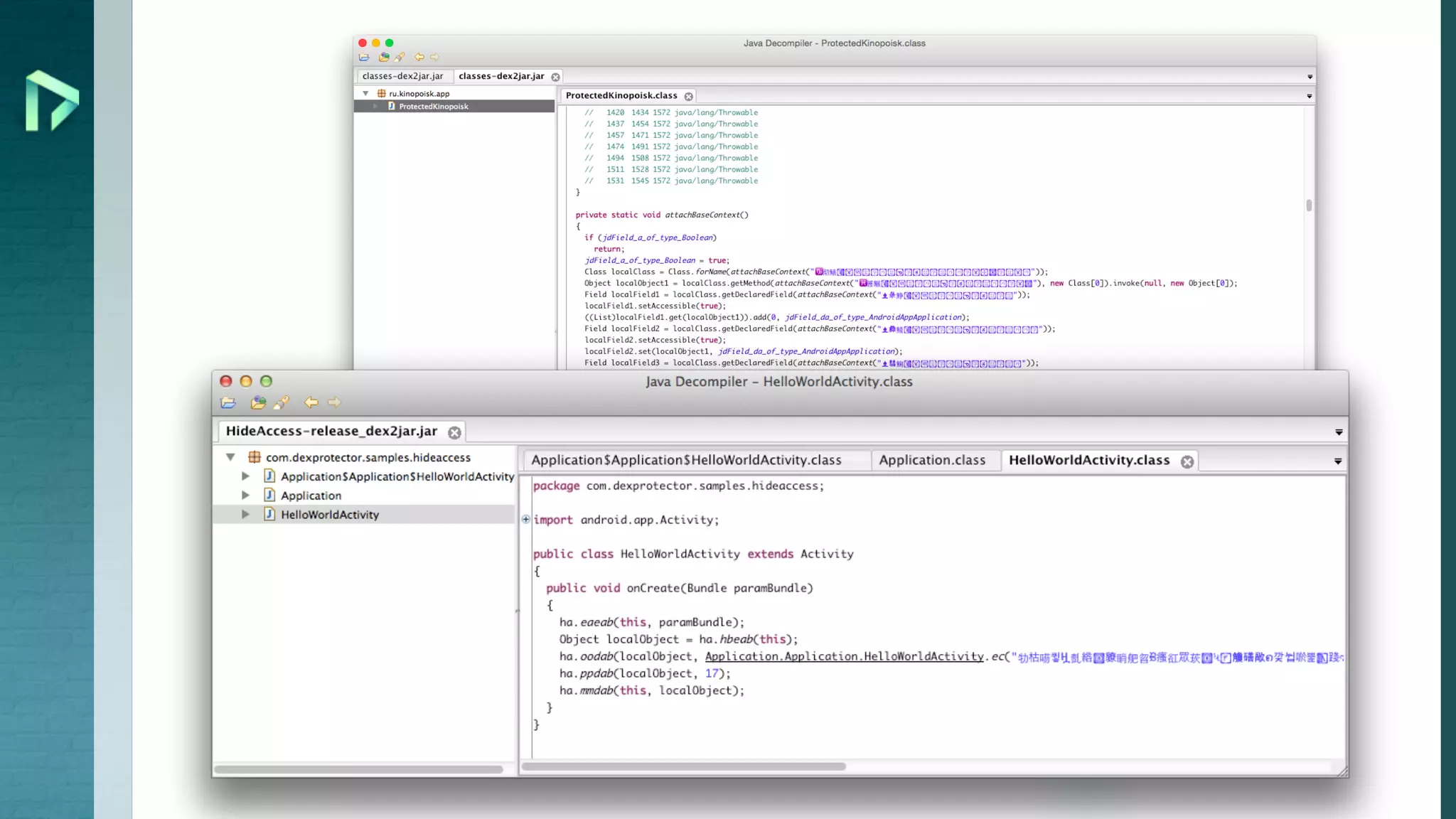
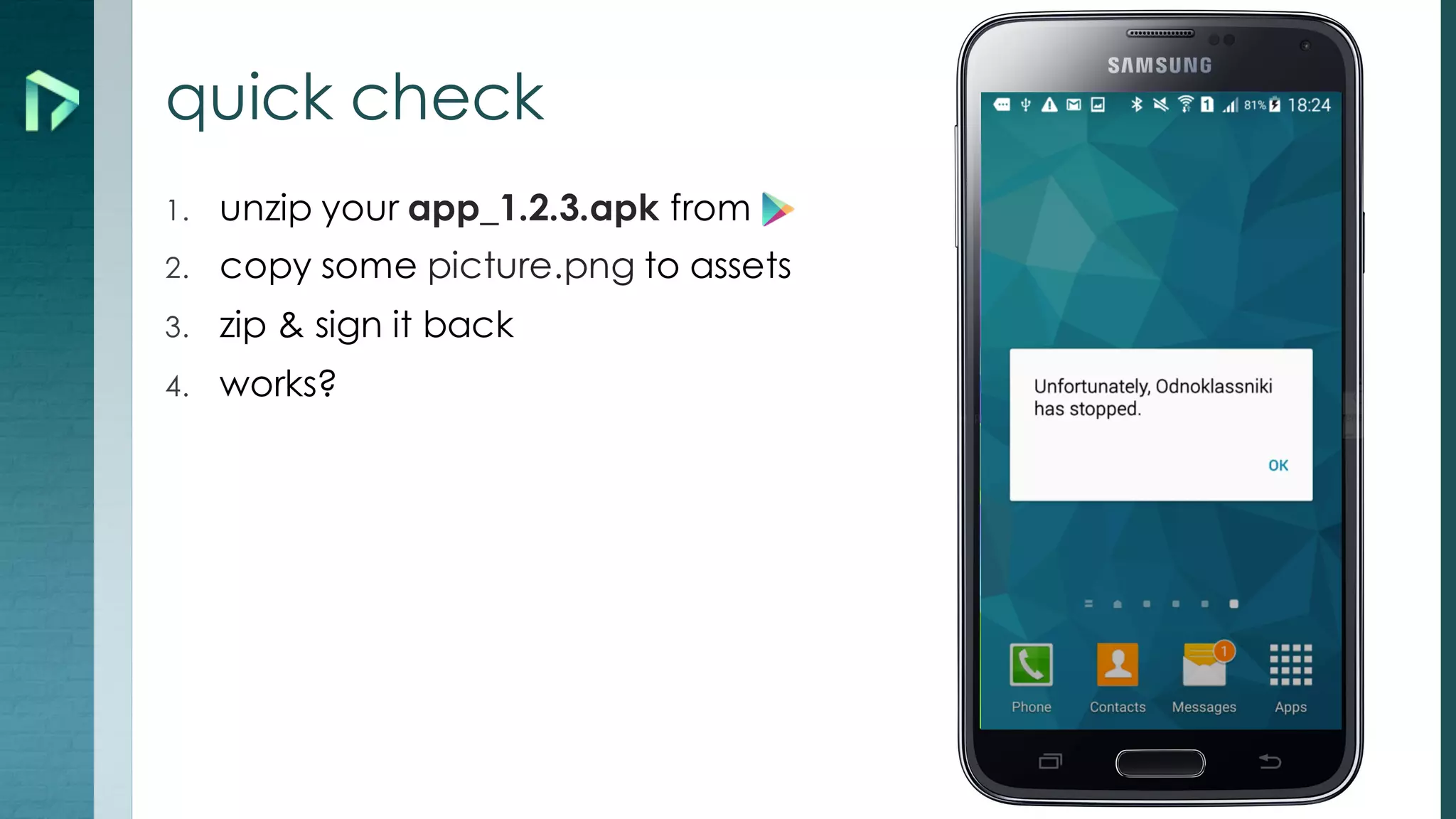
This document discusses how mobile apps can be hacked and provides tips to develop more secure apps. It notes that apps are hackable if users have root access to their devices. Various tools for hacking apps like apktool, dex2jar, and jadx are listed. The document recommends techniques like using an obfuscator, encrypting data and resources, implementing integrity protection, and detecting tampering to make apps harder to reverse engineer and repackage. It emphasizes moving critical logic to native code, using SSL, minimizing stored data, and not trusting apps.