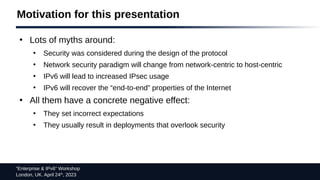
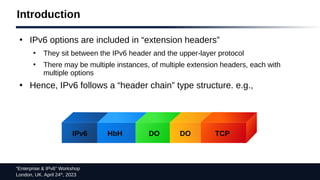
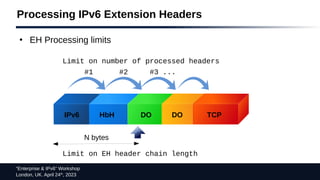
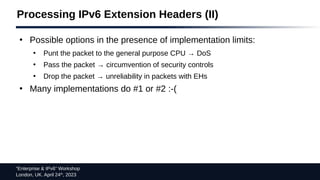
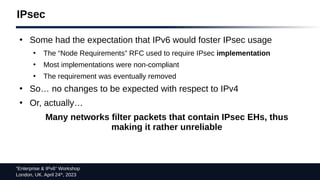
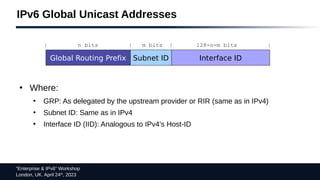
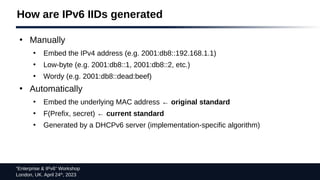
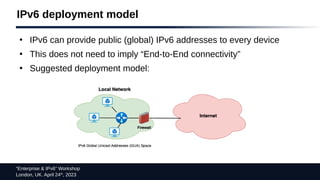
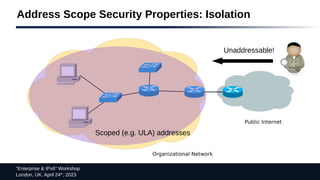
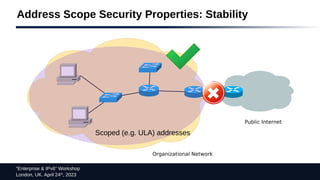
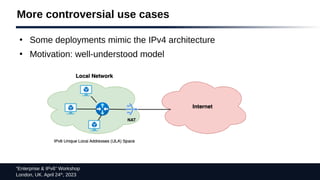
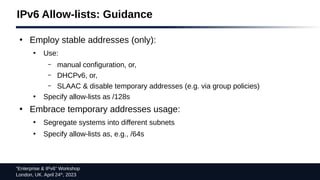
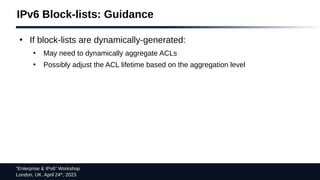
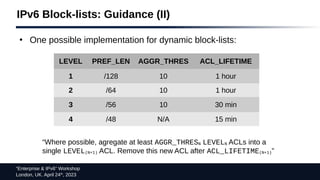
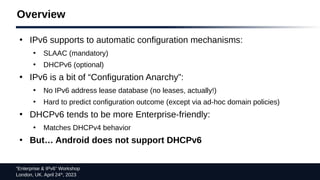
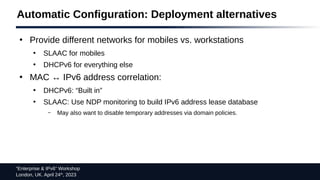
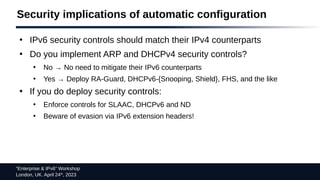
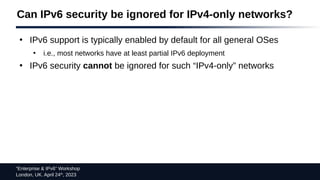
This document summarizes Fernando Gont's presentation on "IPv6 Security & Myth Busting" given at the "Enterprise & IPv6" Workshop in London on April 24th, 2023. The presentation aimed to dispel common myths around IPv6 security by highlighting that security was considered in IPv6's design, the network security paradigm will not change, and IPv6 will not necessarily increase IPsec usage or recover the Internet's end-to-end properties. It also discussed general IPv6 security considerations and specific topics like extension headers, addressing, and access control lists.