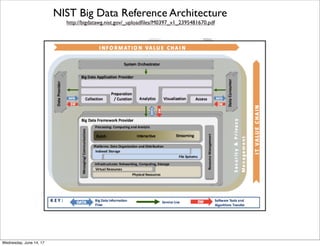
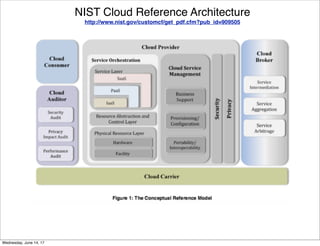
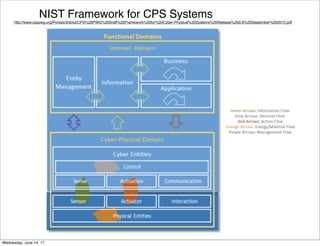
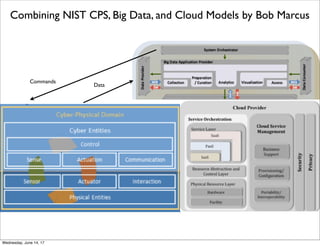
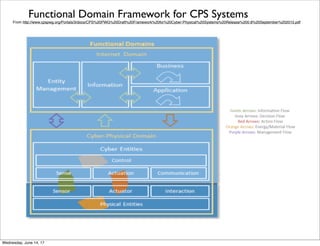
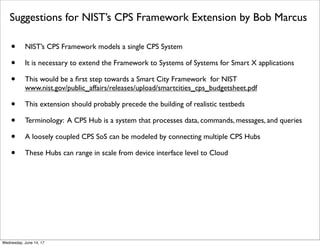
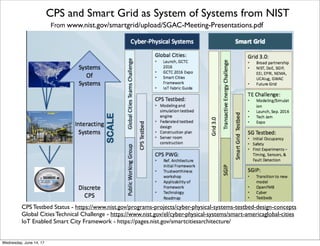
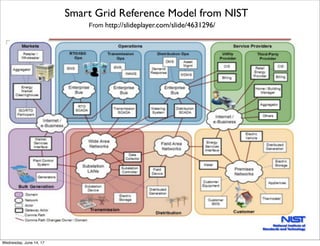
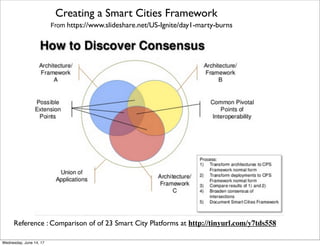
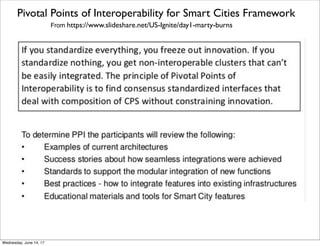
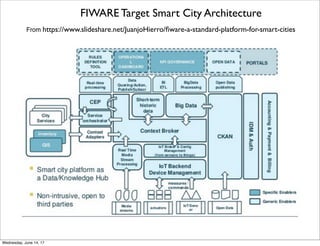
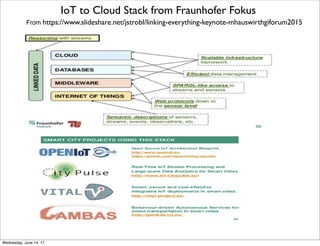
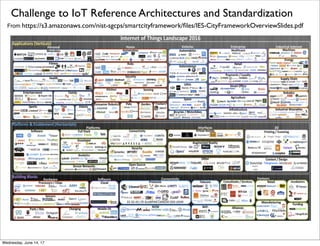
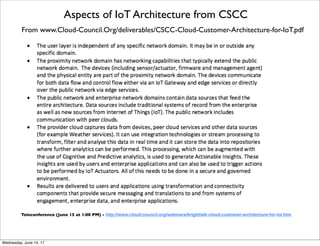
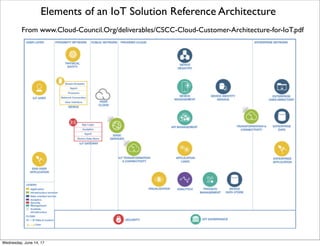
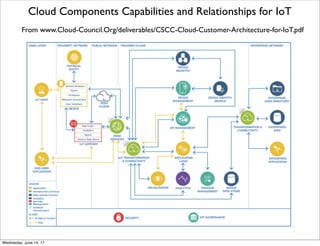
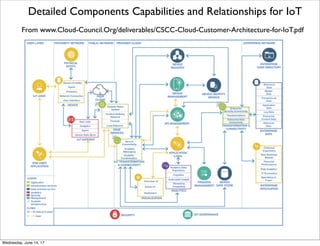
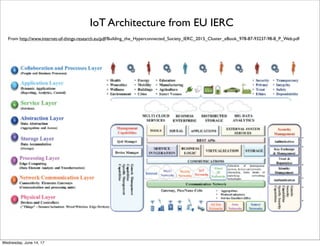
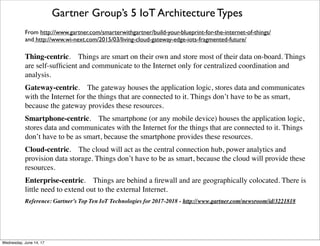
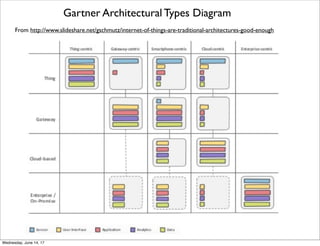
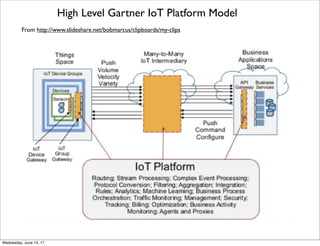
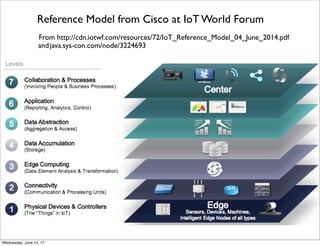
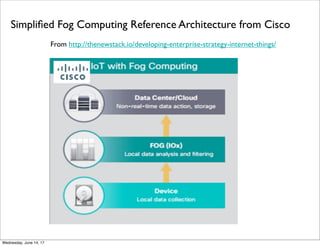
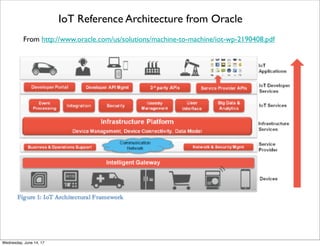
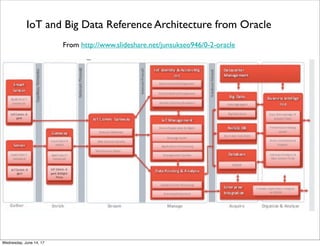
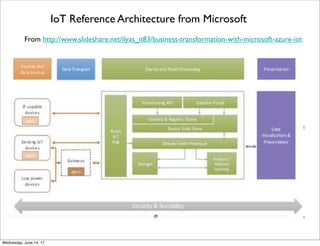
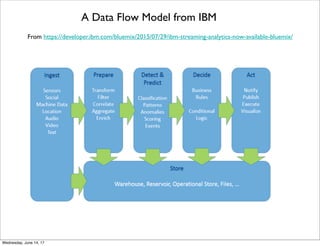
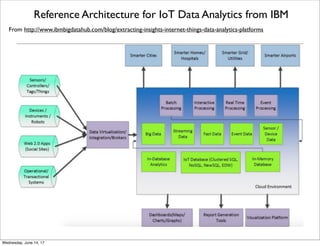
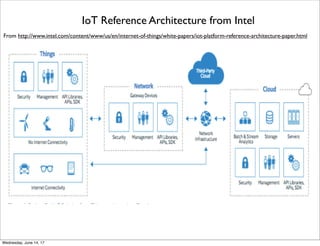
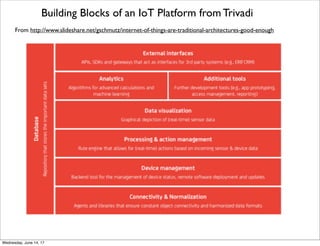
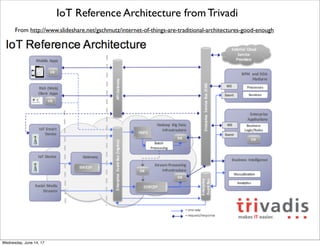
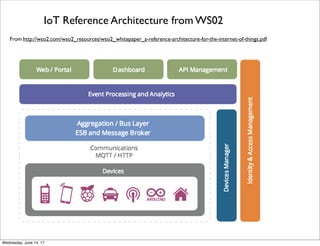
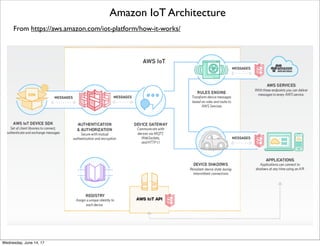
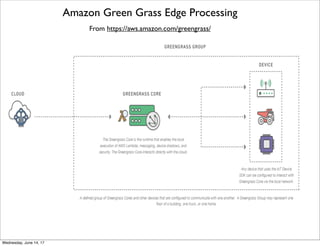
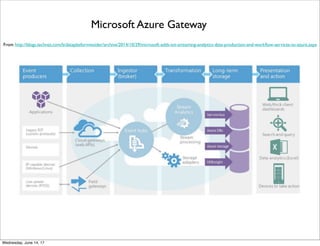
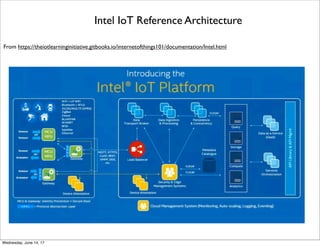
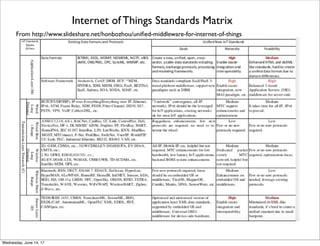
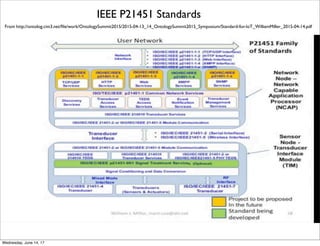
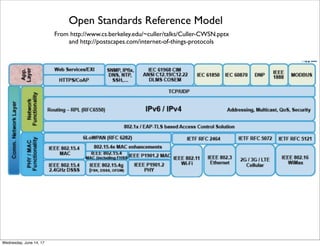
This document provides an overview of various Internet of Things (IoT) reference architectures from standards organizations, consortia, analysts, and industry. It begins with an outline describing NIST models for cyber-physical systems, big data, cloud computing, and their combinations. It then discusses extending NIST frameworks to system of systems and outlines reference architectures from groups like IIC, oneM2M, FIWARE, and analysts like Gartner. Next, it summarizes industry architectures from Cisco, Oracle, Microsoft, and others. It concludes with potential IoT standards. The document aims to provide a comprehensive survey of existing IoT reference architectures.