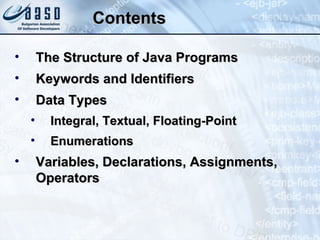
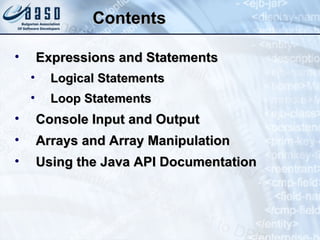
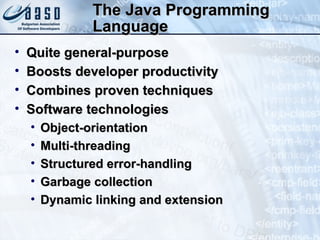
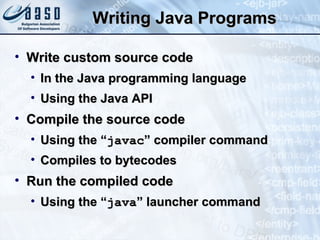
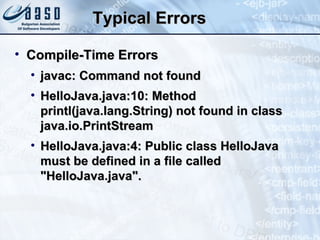
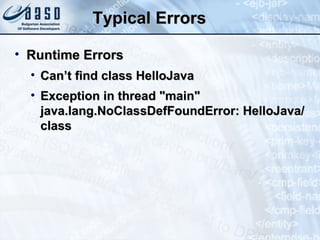
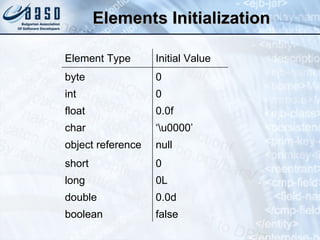
This document provides an overview of the Java programming language, including its structure, keywords, data types, variables, operators, expressions, statements, and control flow structures. It discusses the structure of Java programs, including classes, packages, and the main method. It also covers Java APIs, documentation, errors, and examples of basic Java programs.


![Java Program – Example public class HelloJava { public static void main(String[] args) { System.out.println("Hello, Java!"); } } HelloJava.java javac HelloJava.java java –cp . HelloJava Hello, Java!](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-11-320.jpg)

![Java Programs Java programs are sets of class definitions The main() method is the entry point for standalone Java applications The signature for main() is : T he name args is purely arbitrary: A ny legal identifier may be used, provided the array is a single-dimension array of String objects public static void main(String[] args)](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-18-320.jpg)
![Programs, Classes, and Packages – Example package jeecourse.example; import java.io.*; public class SomeClass { private static int mValue = 5; public static void printValue() { System.out.println("mValue = " + mValue); } public static void main(String[] args) { System.out.println("Some Class"); printValue(); } }](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-19-320.jpg)


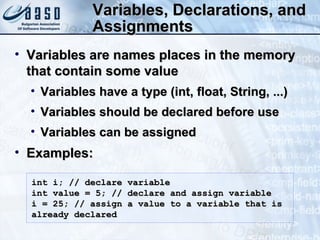
![Variables, Declarations, and Assignments – Examples public class Assignments { public static void main(String args []) { int x, y; // declare int variables float z = 3.414f; // declare and assign float double w = 3.1415; // declare and assign double boolean b = true; // declare and assign boolean char ch; // declare character variable String str; // declare String variable String s = "bye"; // declare and assign String ch = 'A'; // assign a value to char variable str = "Hi out there!"; // assign value to String x = 6; // assign value to int variable y = 1000; // assign values to int variable ... } }](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-41-320.jpg)
![Operator Evaluation Order In Java, the order of evaluation of operands in an expression is fixed – left to right Consider this code fragment: In this case, it might be unclear which element of the array is modified: Which value of b is used to select the array element, 0 or 1 int[] a = {4, 4}; int b = 1; a[b] = b = 0;](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-52-320.jpg)

![If Statement – Example public static void main(String[] args) { int radius = 5; double surface = Math.PI * radius * radius; if (surface > 100) { System.out.println("The circle is too big!"); } else if (surface > 50) { System.out.println( "The circle has acceptable size!"); } else { System.out.println( "The circle is too small!"); } }](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-58-320.jpg)
![Looping Statements The enhanced for statement: Example: for ( Type variable : some collection ) { statement or block; } public static void main(String[] args) { String[] towns = new String[] { "Sofia", "Plovdiv", "Varna" }; for (String town : towns) { System.out.println(town); } }](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-62-320.jpg)
![Looping Statements The do/while loop: Example: do { statement or block; } while (boolean condition); public static void main(String[] args) { int counter=100; do { System.out.println("counter=" + counter); counter = counter - 5; } while (counter>=0); }](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-64-320.jpg)
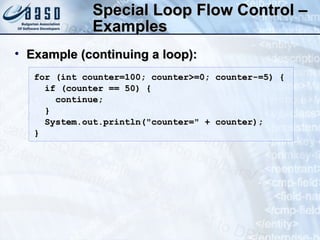
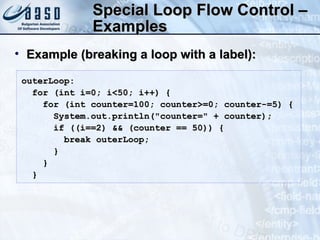
![Special Loop Flow Control Some special operators valid in loops: break [label]; continue [label]; label: statement; // Where statement should be a loop Example (breaking a loop): for (int counter=100; counter>=0; counter-=5) { System.out.println("counter=" + counter); if (counter == 50) break; }](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-65-320.jpg)
![Scanner – Example import java.util.Scanner; public class ScannerDemo { public static void main(String[] args) { Scanner console = new Scanner(System.in); // Get the first input System.out.print("What is your name? "); String name = console.nextLine(); // Get the second input System.out.print("How old are you? "); int age = console.nextInt(); // Display output on the console System.out.println("Hello, " + name + ". " + "Next year, you'll be " + (age + 1)); } }](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-74-320.jpg)
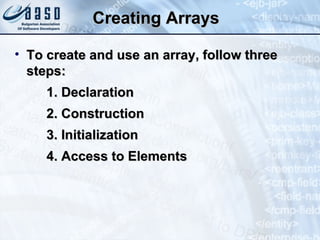
![Array Declaration Declaration tells the compiler the array’s name and what type its elements will be For example: The square brackets can come before or after the array variable name: int[] ints; Dimensions[] dims; float[][] twoDimensions; int ints[];](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-78-320.jpg)
![Array Construction The declaration does not specify the size of an array Size is specified at runtime, when the array is allocated via the new keyword For example: Declaration and construction may be performed in a single line: int[] ints; // Declaration ints = new int[25]; // Construction int[] ints = new int[25];](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-79-320.jpg)
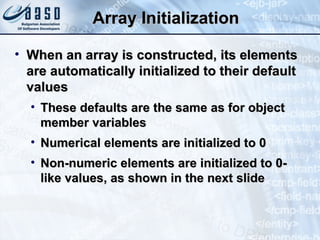
![Array Elements Initialization Initial values for the elements can be specified at the time of declaration and initialization: The array size is inferred from the number of elements within the curly braces float[] diameters = {1.1f, 2.2f, 3.3f, 4.4f, 5.5f};](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-82-320.jpg)
![Access to Elements Accessing array elements: Elements access is range checked Arrays has field length that contains their number of elements int[] arr = new int[10]; arr[3] = 5; // Writing element int value = arr[3]; // Reading element int[] arr = new int[10]; int value = arr[10]; // ArrayIndexOutOfBoundsException](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-83-320.jpg)
![Arrays – Example // Finding the smallest and largest // elements in an array int[] values = {3,2,4,5,6,12,4,5,7}; int min = values[0]; int max = values[0]; for (int i=1; i<values.length; i++) { if (values[i] < min) { min = values[i]; } else if (values[i] > max) { max = values[i]; } } System.out.printf("MIN=%d\n", min); System.out.printf("MAX=%d\n", max);](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-84-320.jpg)
![M ulti-dimension al A rrays Multidimensional arrays in Java are actually arrays of arrays Defining matrix: Accessing matrix elements: Getting the number of rows/columns: int[][] matrix = new int[3][4]; matrix[1][3] = 42; int rows = matrix.length; int colsInFirstRow = matrix[0].length;](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-85-320.jpg)
![M ulti-dimension al A rrays Consider this declaration plus initialization: It’s natural to assume that the myInts contains 12 ints and to imagine them as organized into rows and columns, as shown : WRONG ! int[][] myInts = new int[3][4];](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-86-320.jpg)
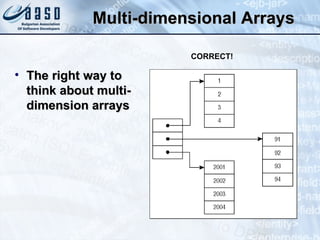
![M ulti-dimension al A rrays The subordinate arrays in a multi-dimension array don’t have to all be the same length Such an array may be created like this: int[][] myInts = { {1, 2, 3}, {91, 92, 93, 94}, {2001, 2002} };](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-88-320.jpg)
![M ulti-dimension al A rrays – Example // Finding the sum of all positive // cells from the matrix int[][] matrix = {{2,4,-3}, {8,-1,6}}; int sum = 0; for (int row=0; row<matrix.length; row++) { for (int col=0; col<matrix[row].length; col++) { if (matrix[row][col] > 0) { sum += matrix[row][col]; } } } System.out.println("Sum = " + sum);](https://image.slidesharecdn.com/introduction-to-programming-1-0-101012075937-phpapp01/85/Introduction-to-programming-89-320.jpg)