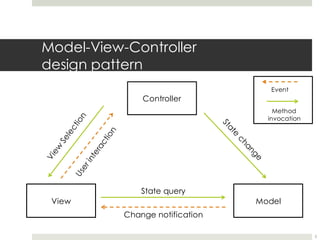
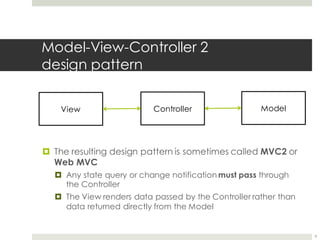
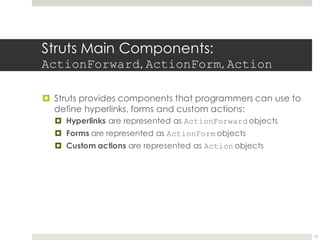
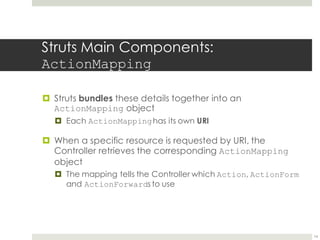
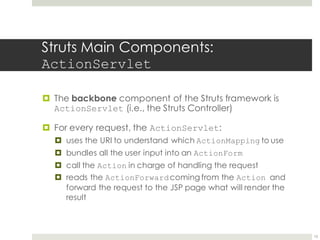
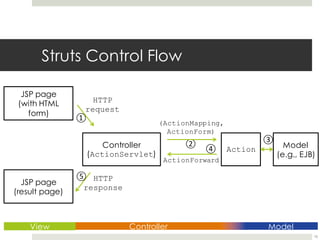
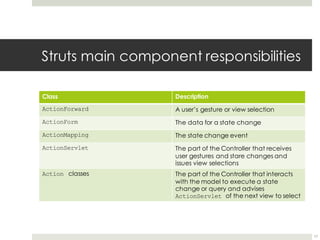
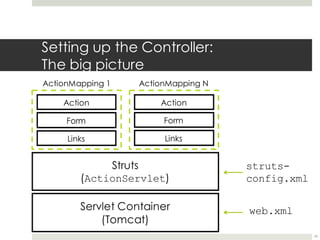
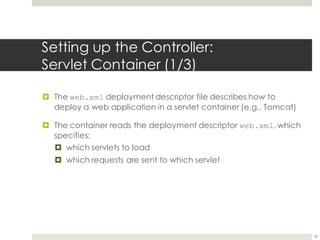
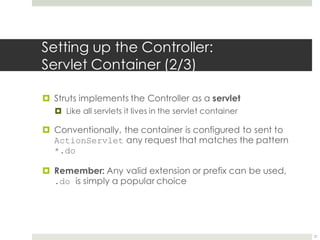
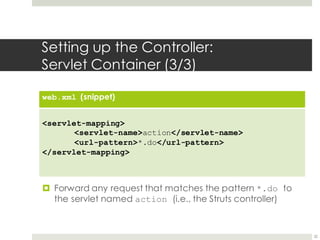
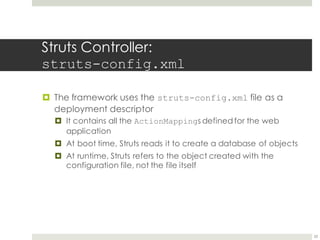
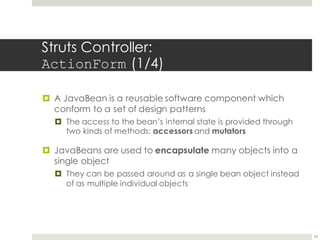
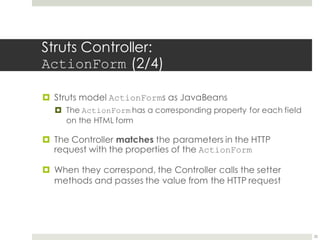
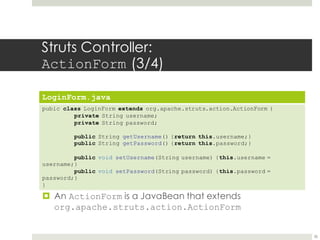
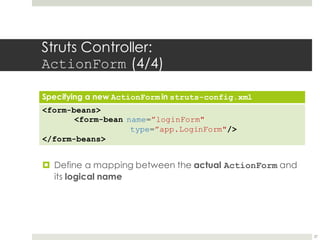
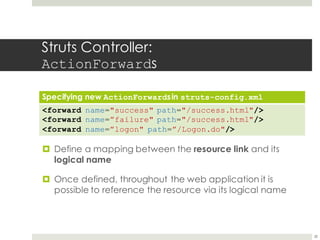
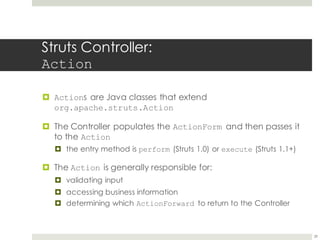
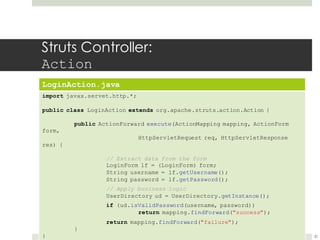
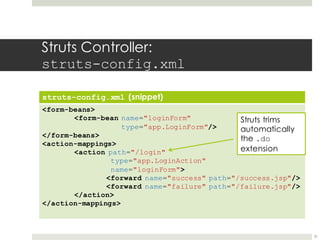
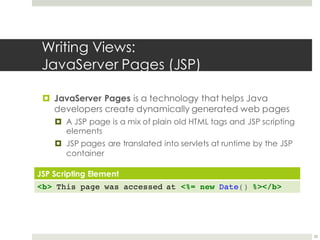
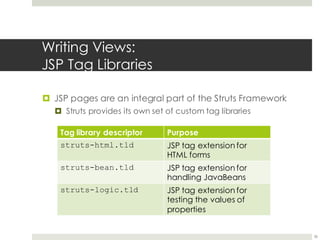
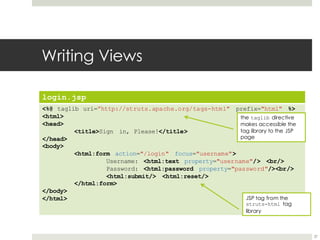
This document provides an introduction to Jakarta Struts 1.3, an open source MVC framework for building Java web applications. It discusses the limitations of using the traditional MVC pattern for web applications due to HTTP's stateless nature. Struts implements an MVC2 pattern to address this, using the controller to manage state. The core Struts components like ActionForms, Actions, and ActionMappings are explained. It also covers setting up the Struts controller through configuration files, defining forms and actions, and creating views with JSP and custom tag libraries.