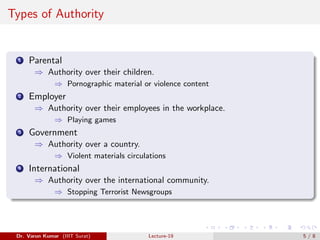
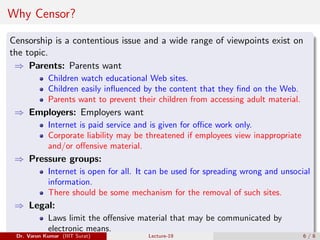
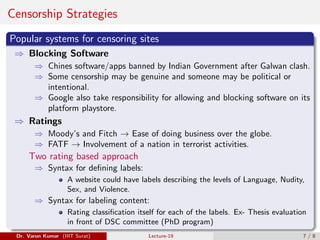
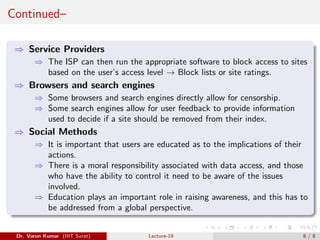
The document discusses the concept of censorship, highlighting its necessity in various contexts such as parental control, workplace regulations, and government oversight to protect users, especially children, from harmful content. It explains different censorship strategies and authorities involved, such as parents, employers, and legal frameworks, and emphasizes the balance between freedom of speech and social security. The document also advocates for user education regarding responsible internet use and the implications of data access.