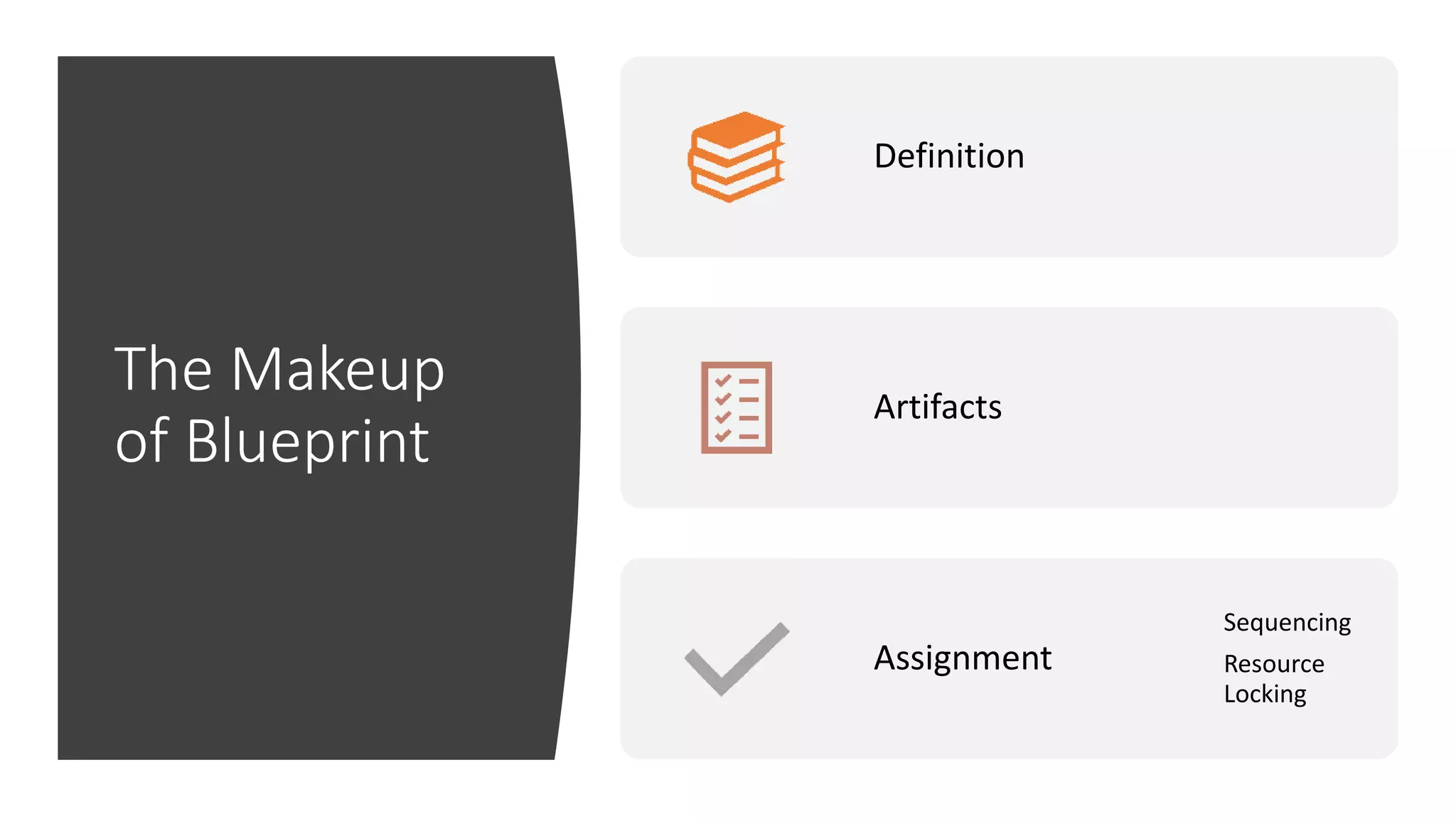
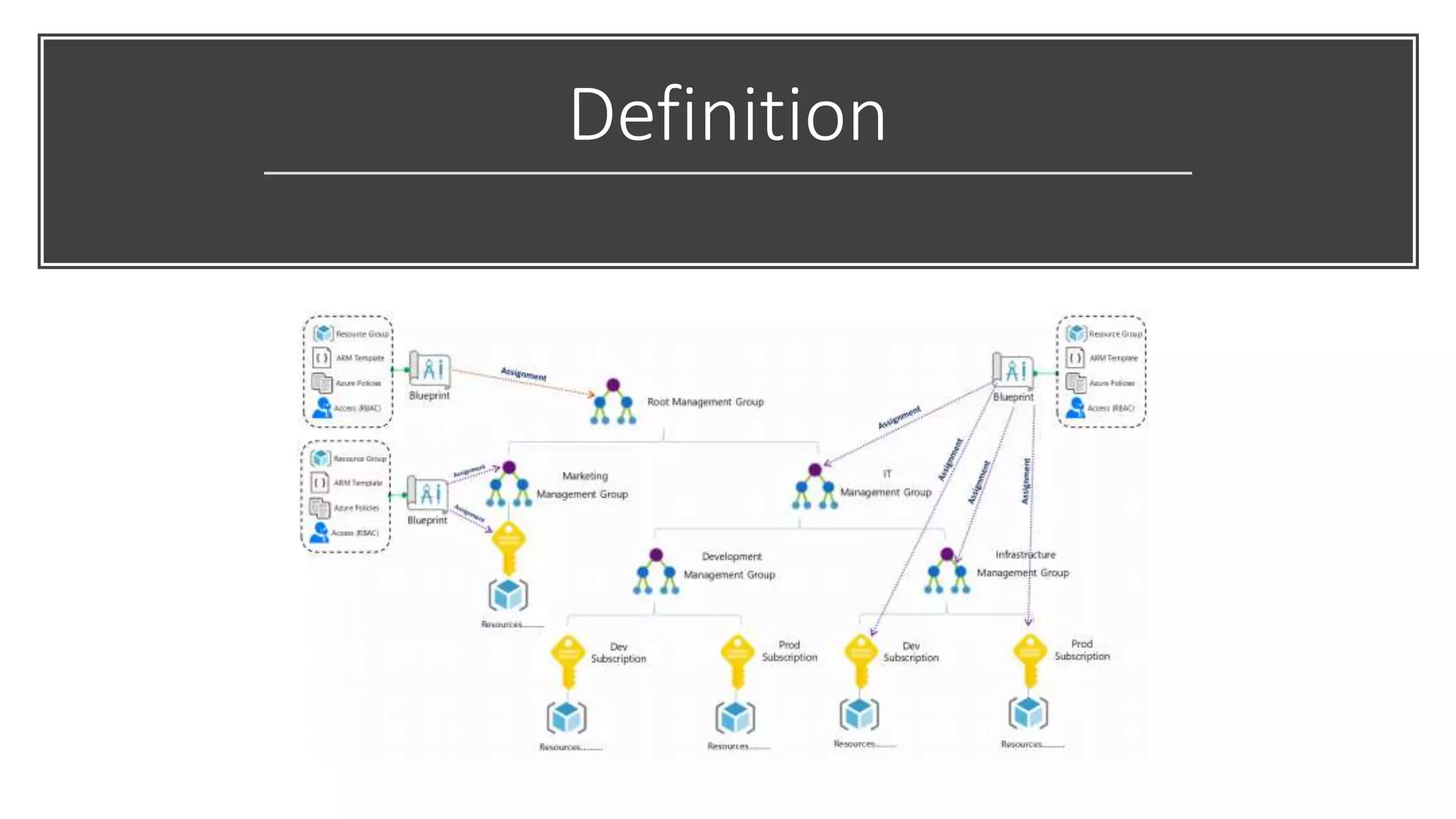
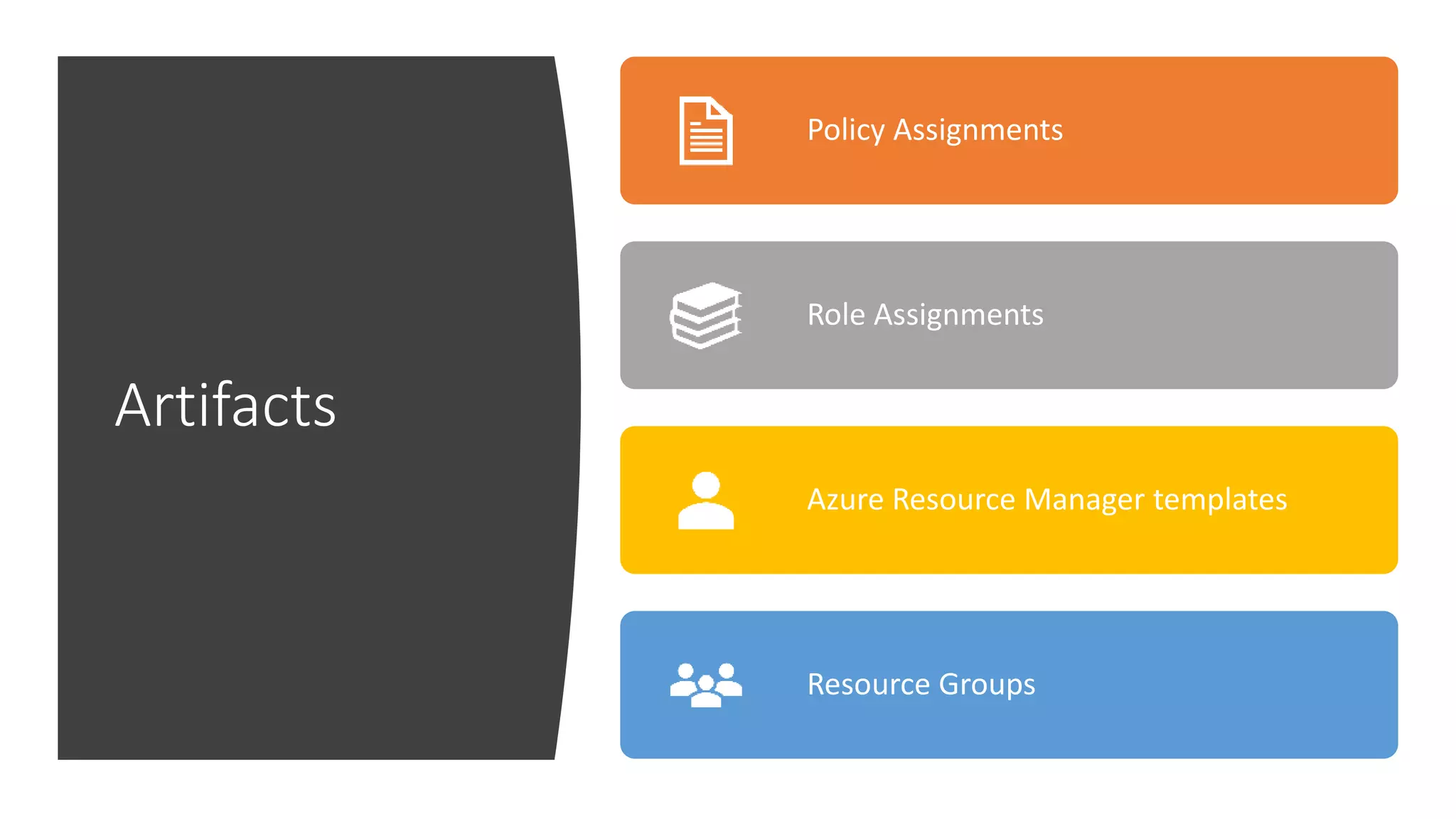
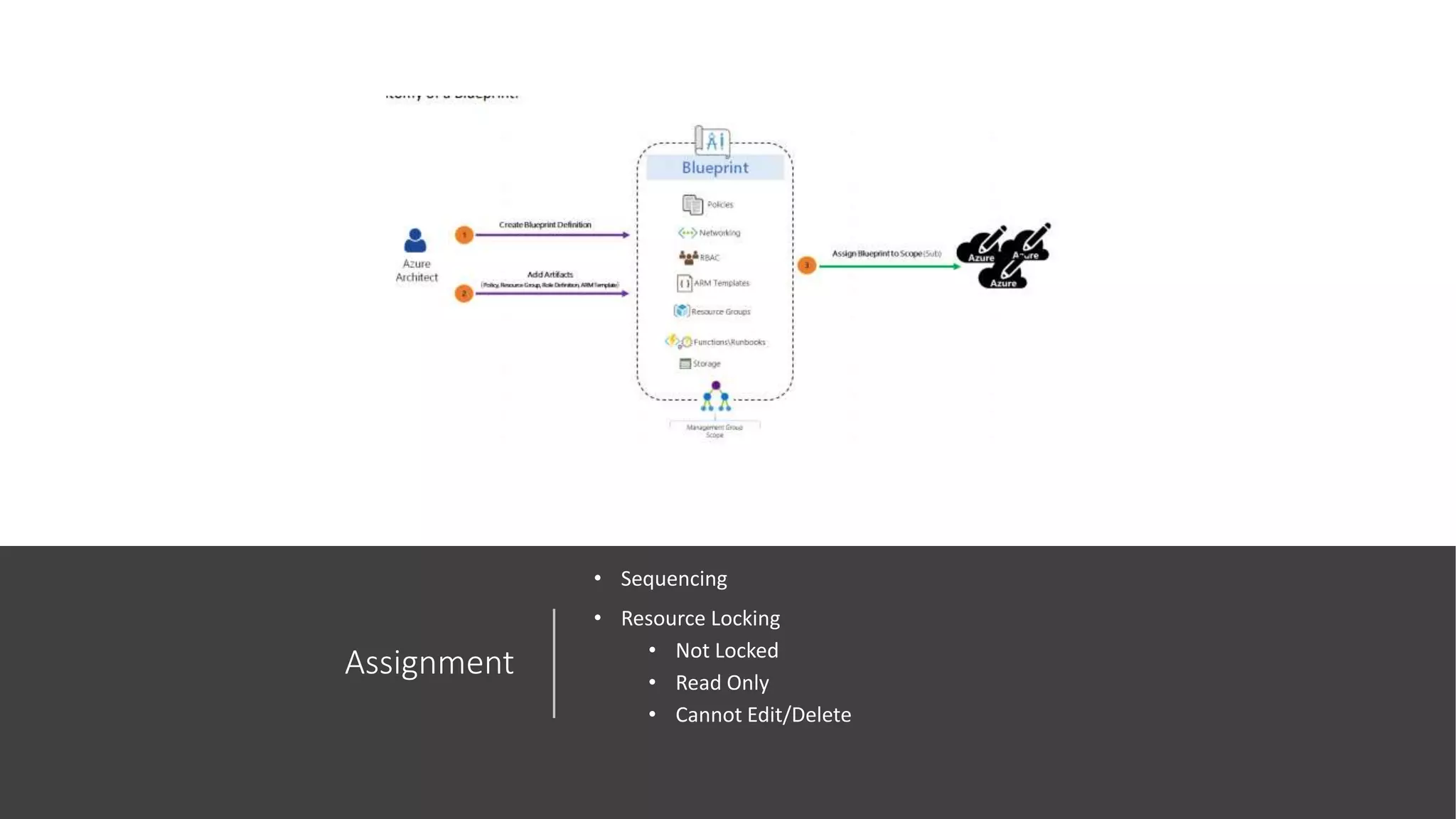
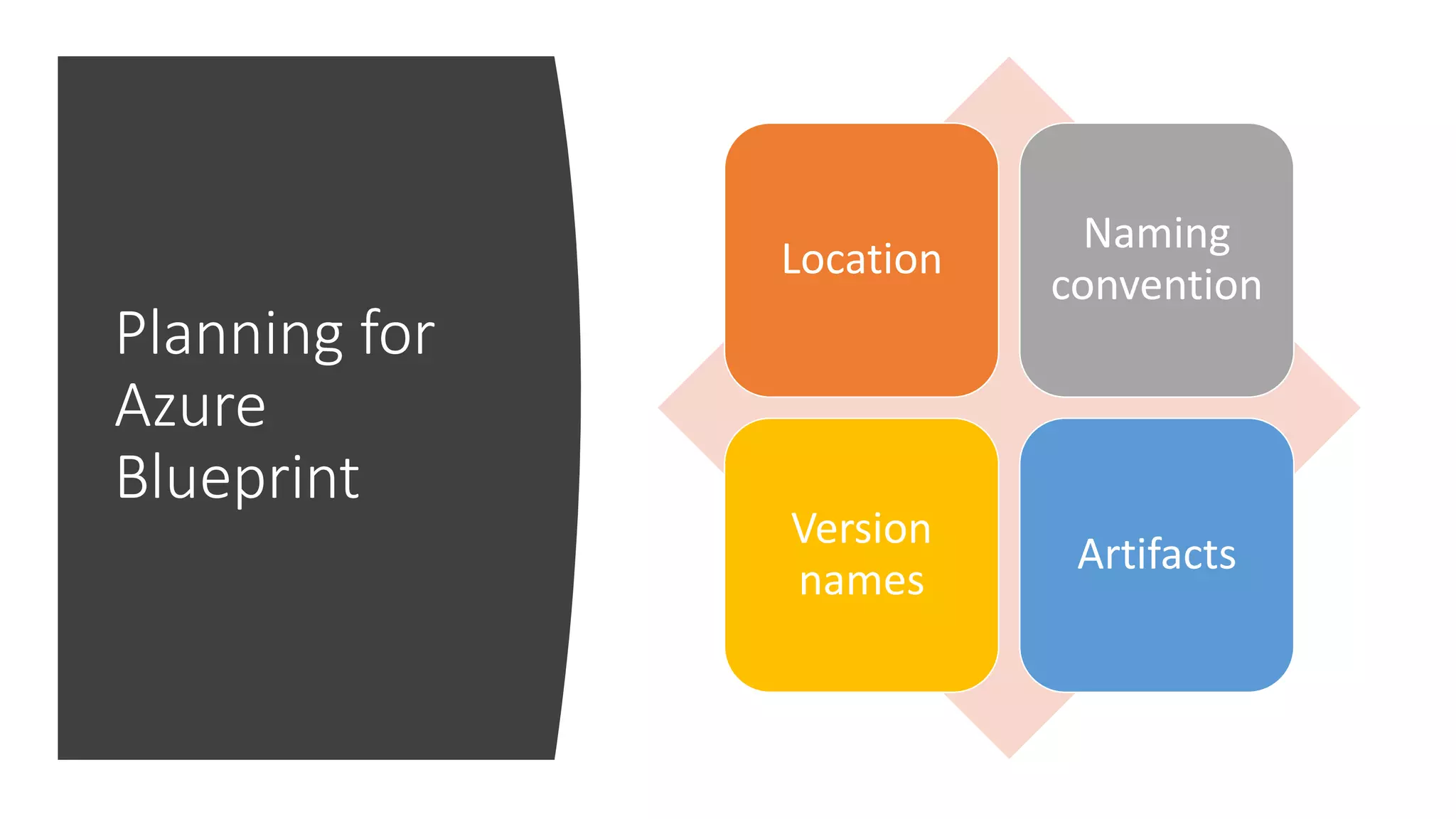
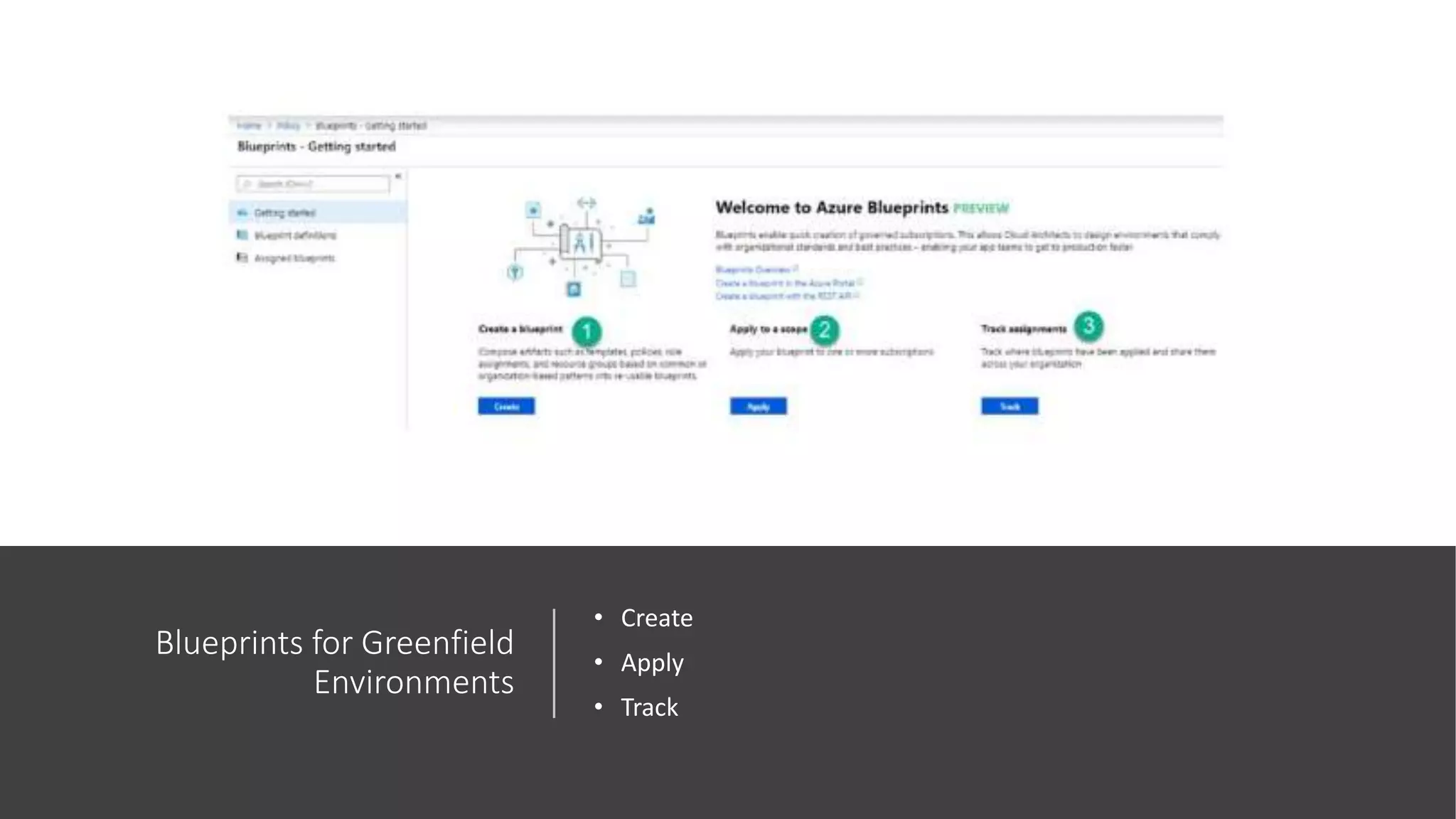
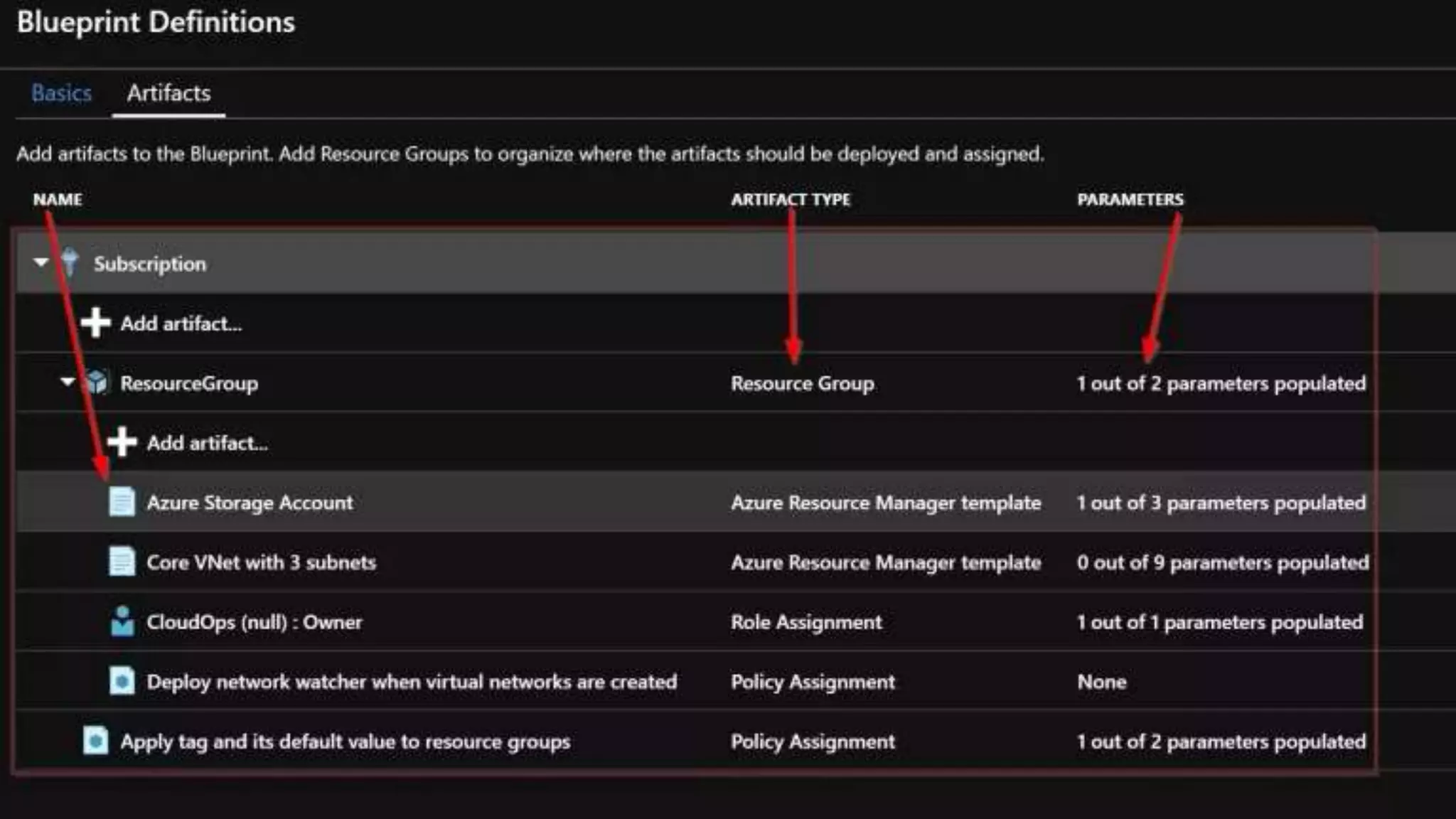
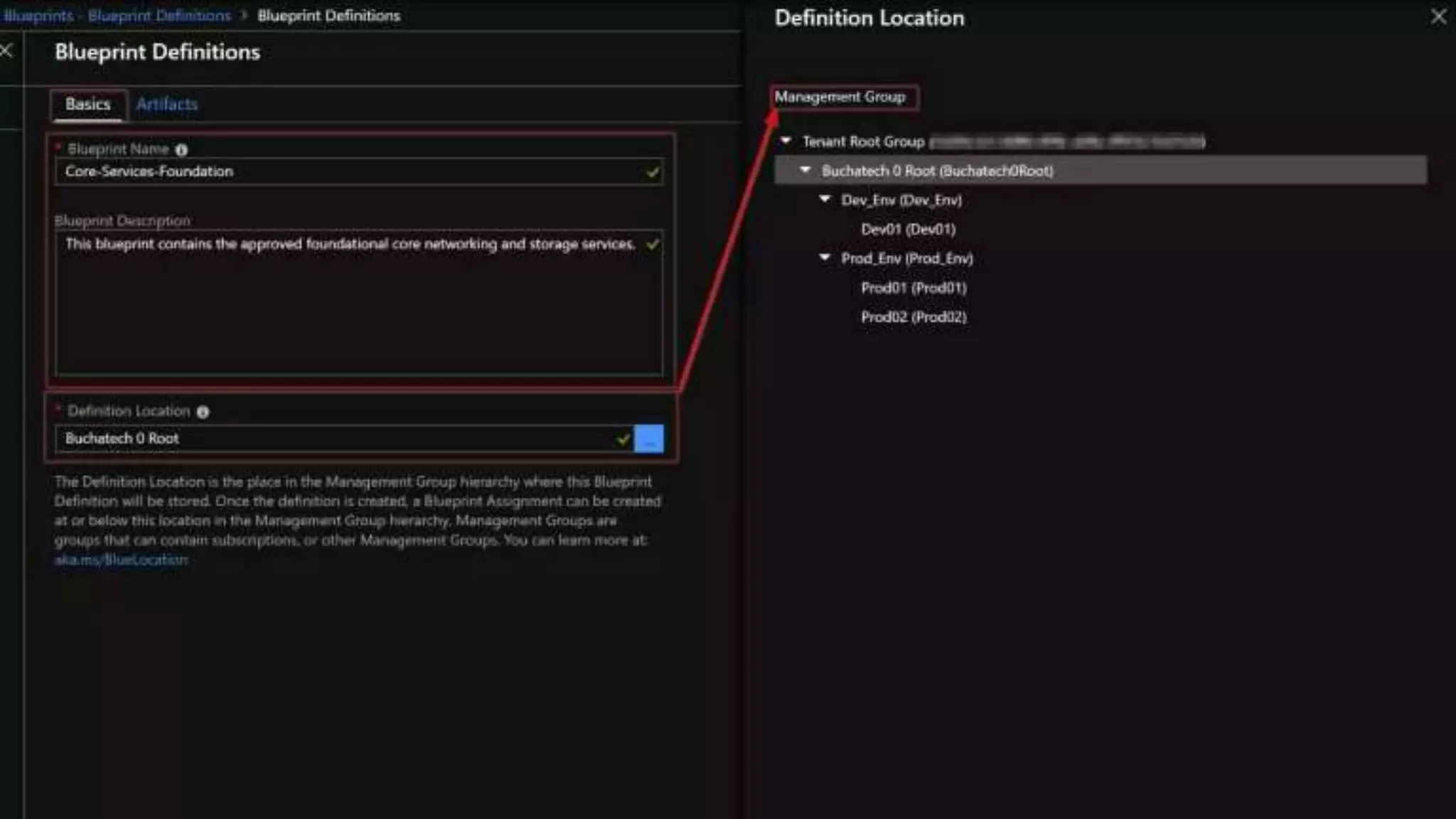
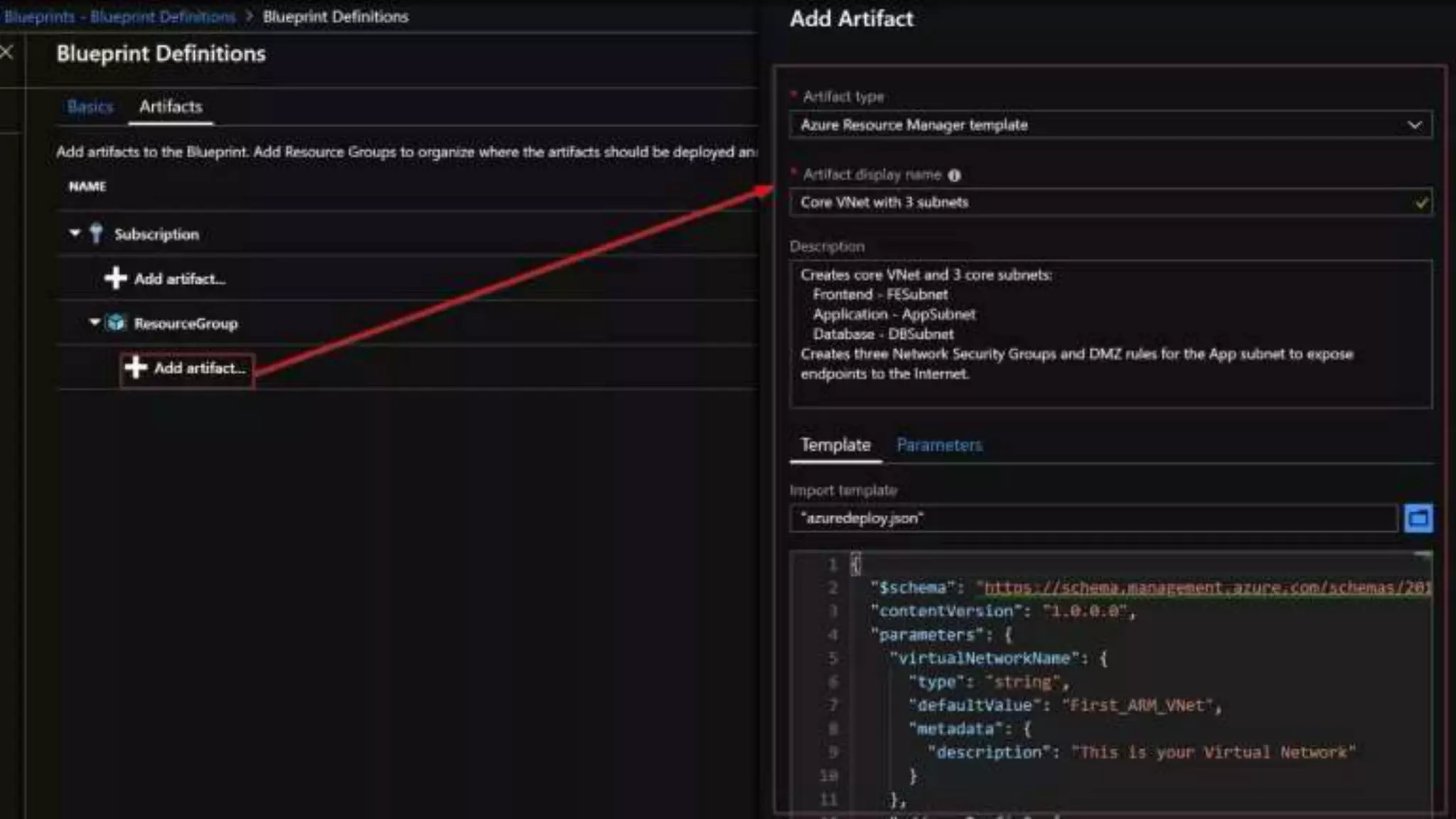
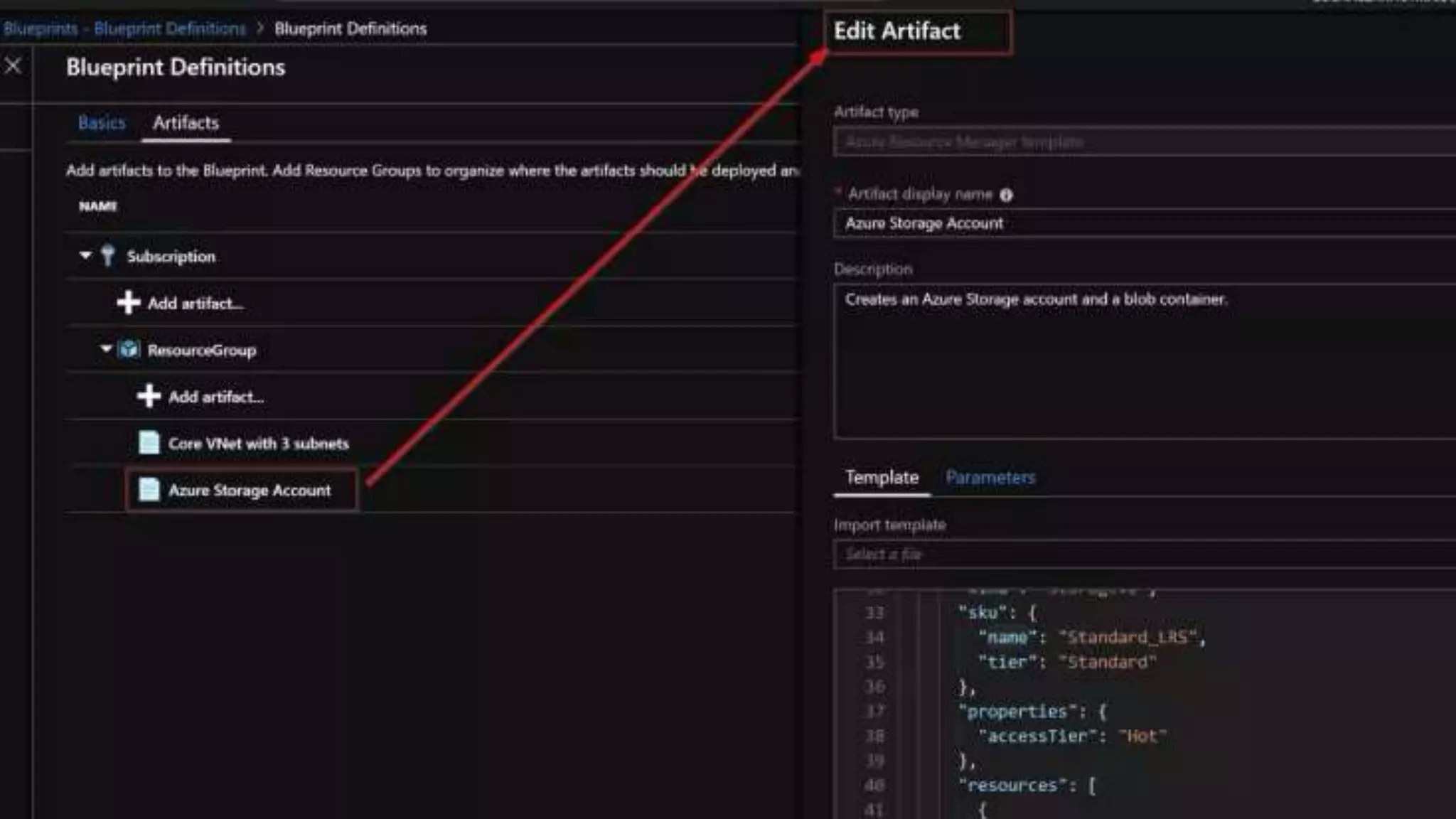
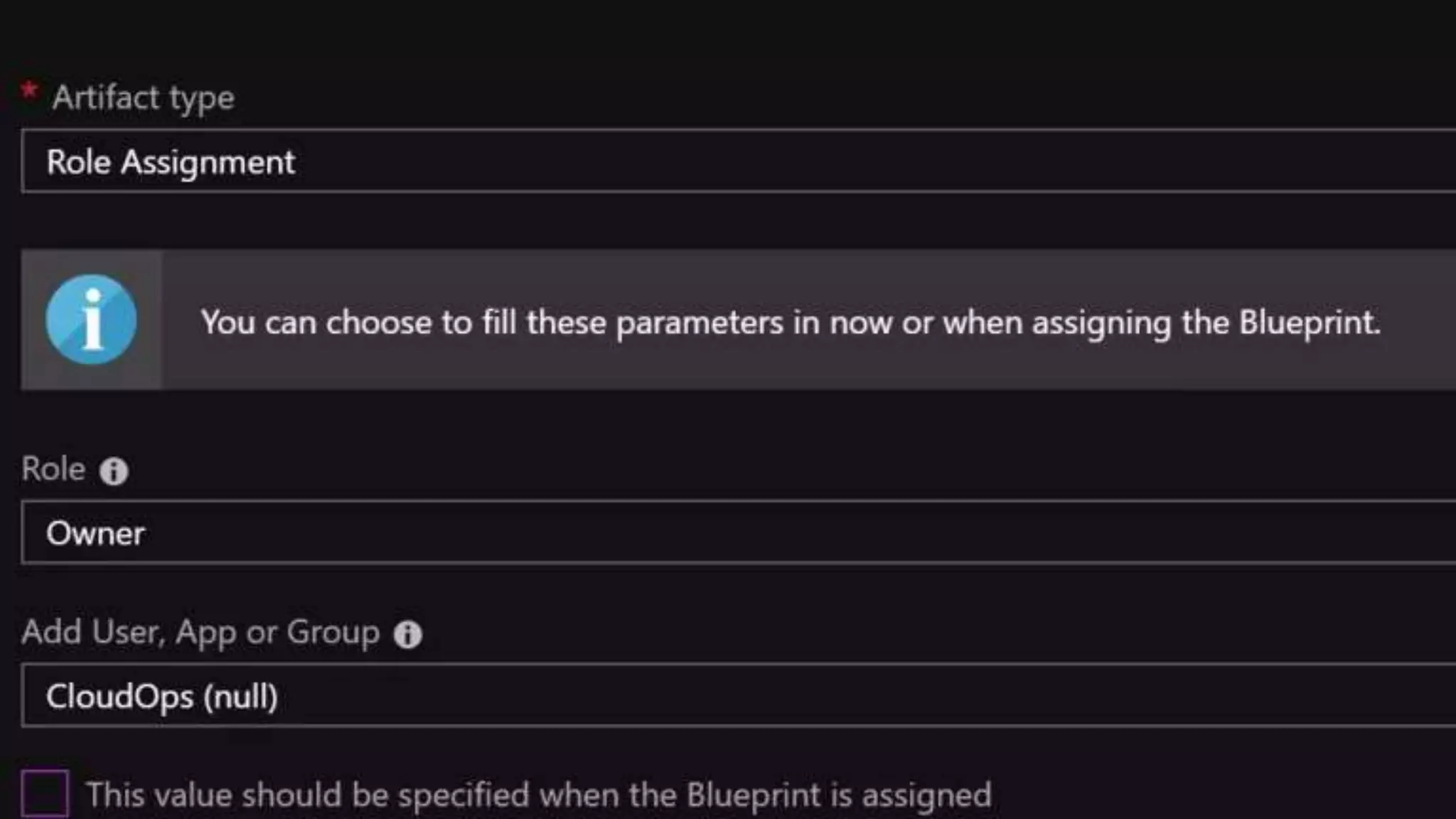
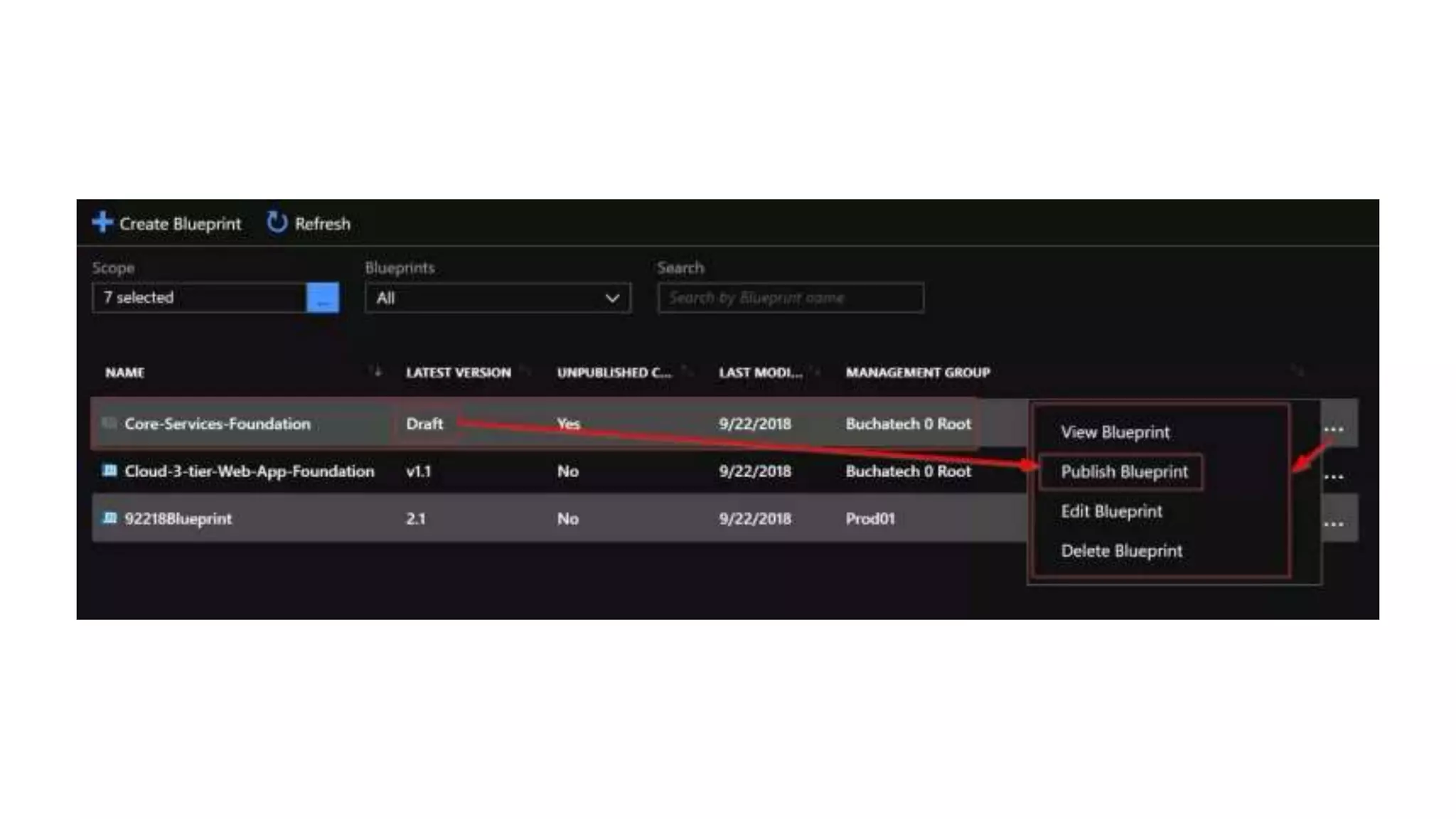
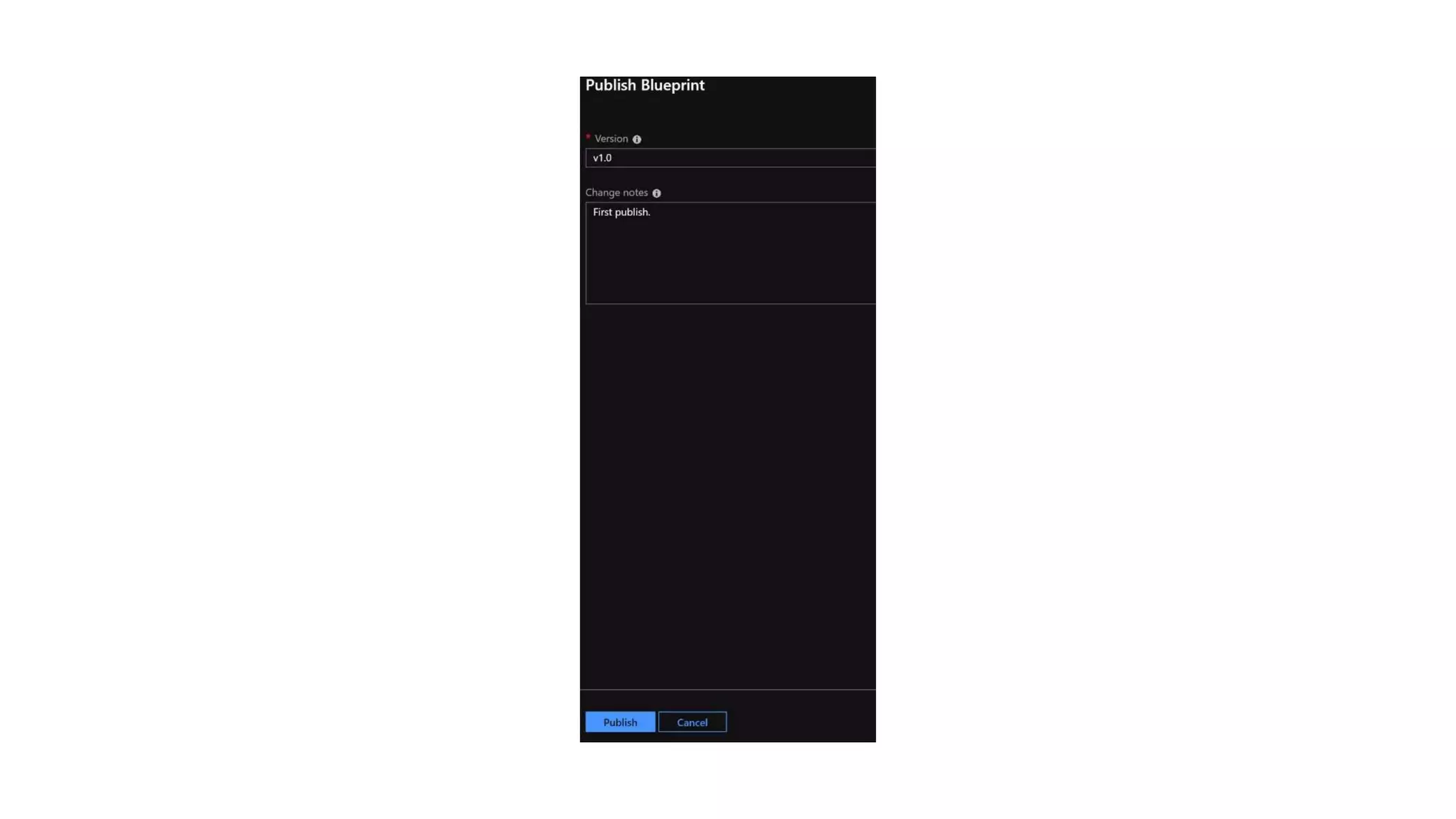
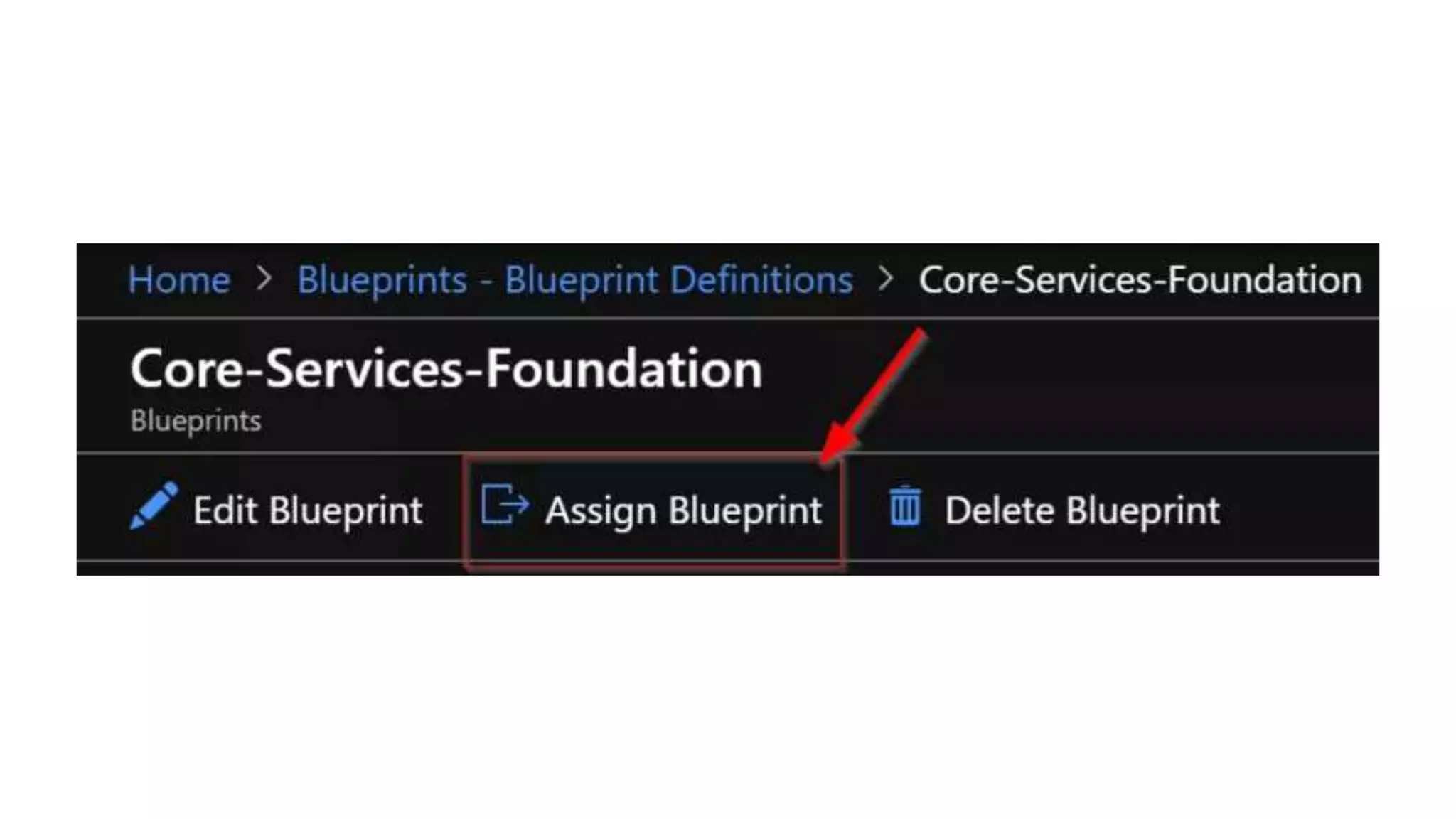
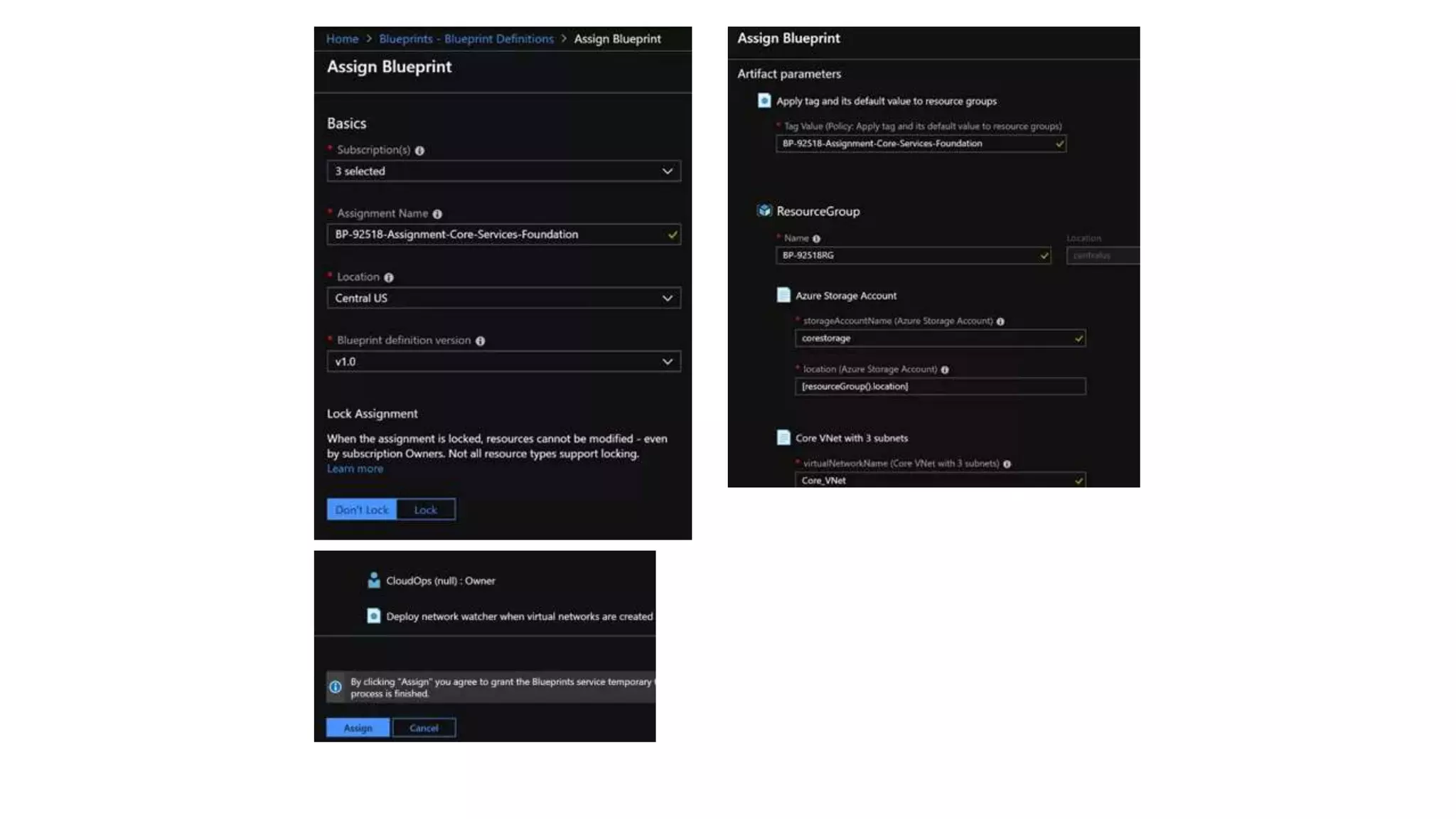
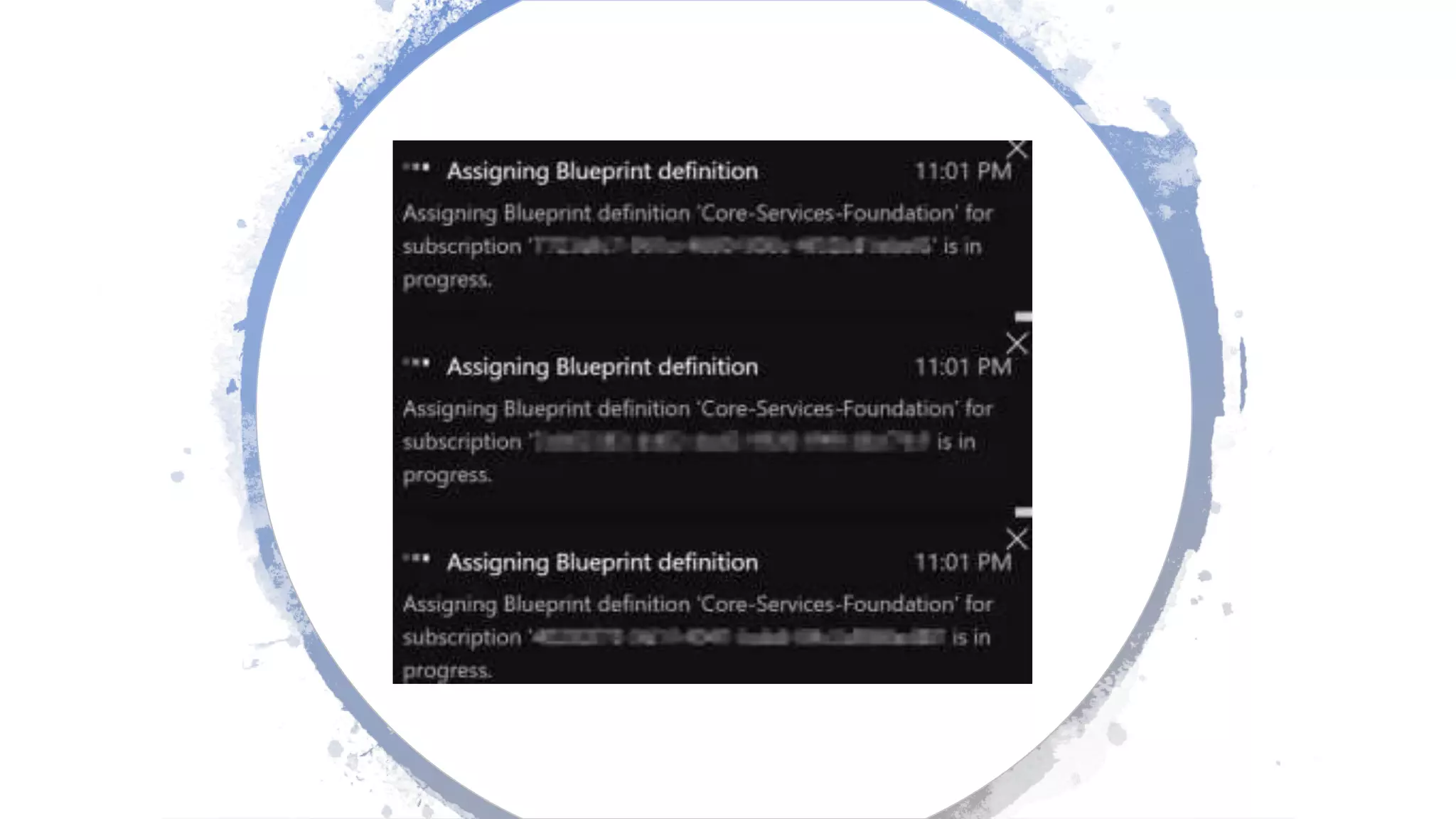
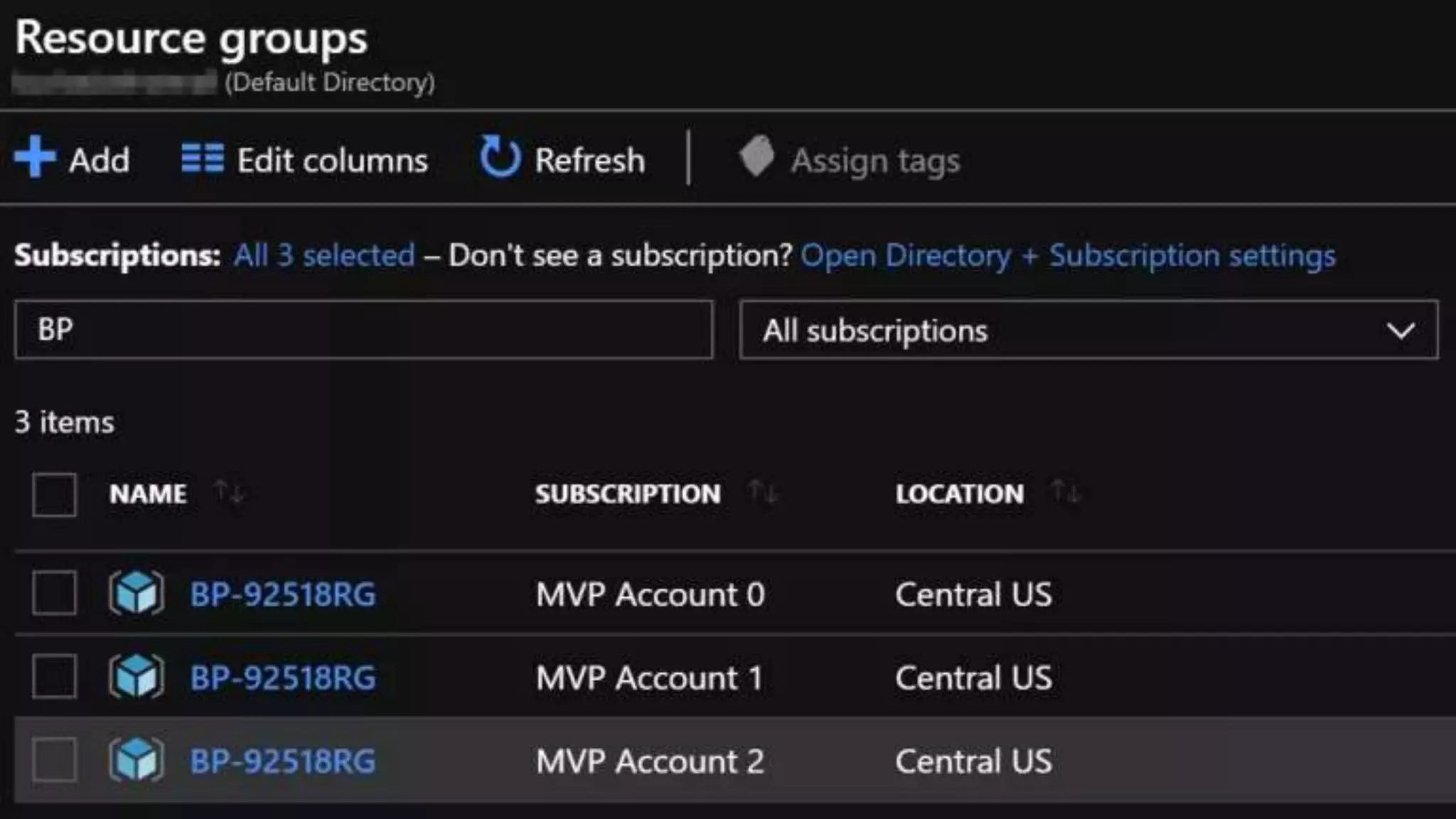
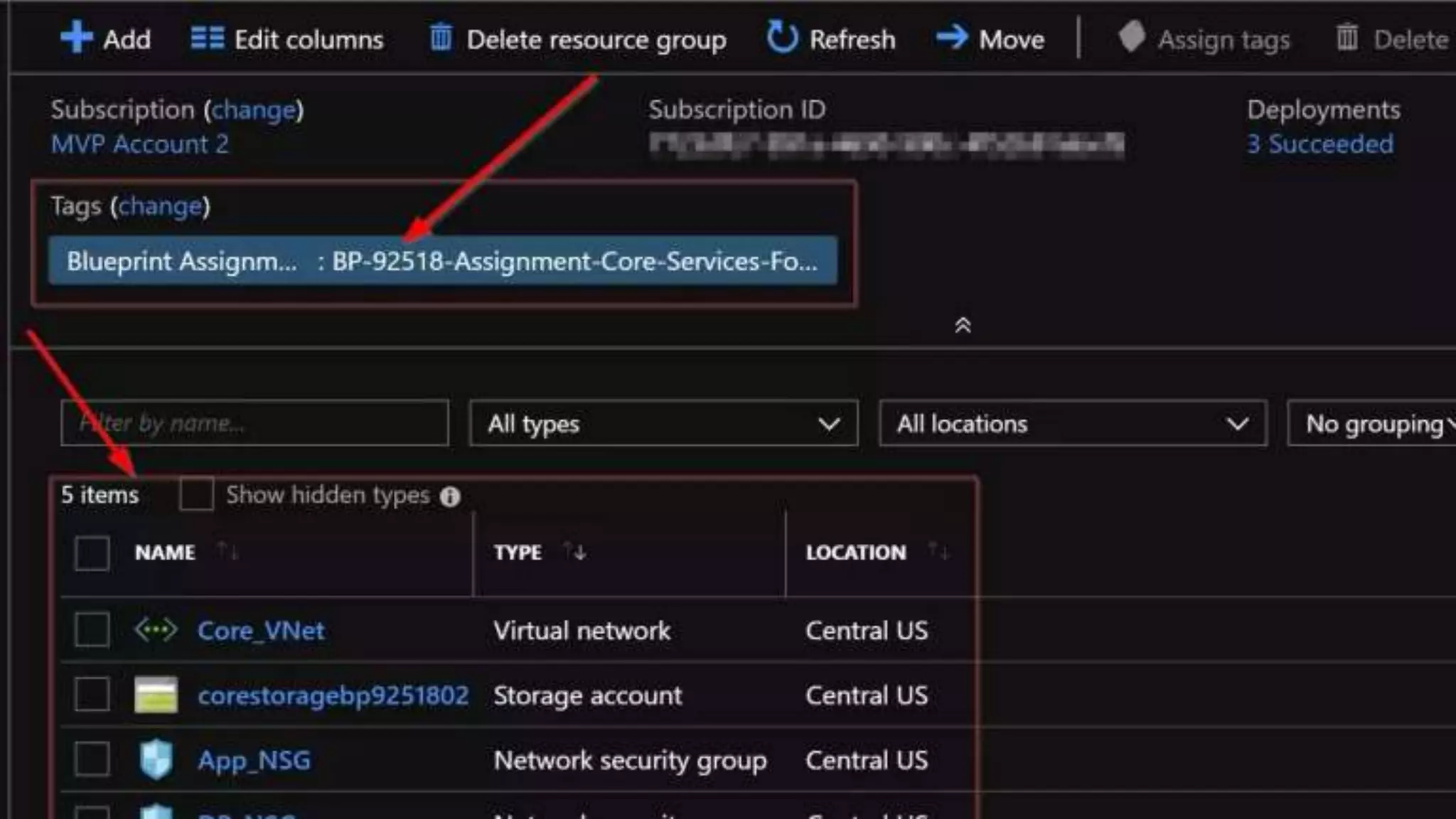
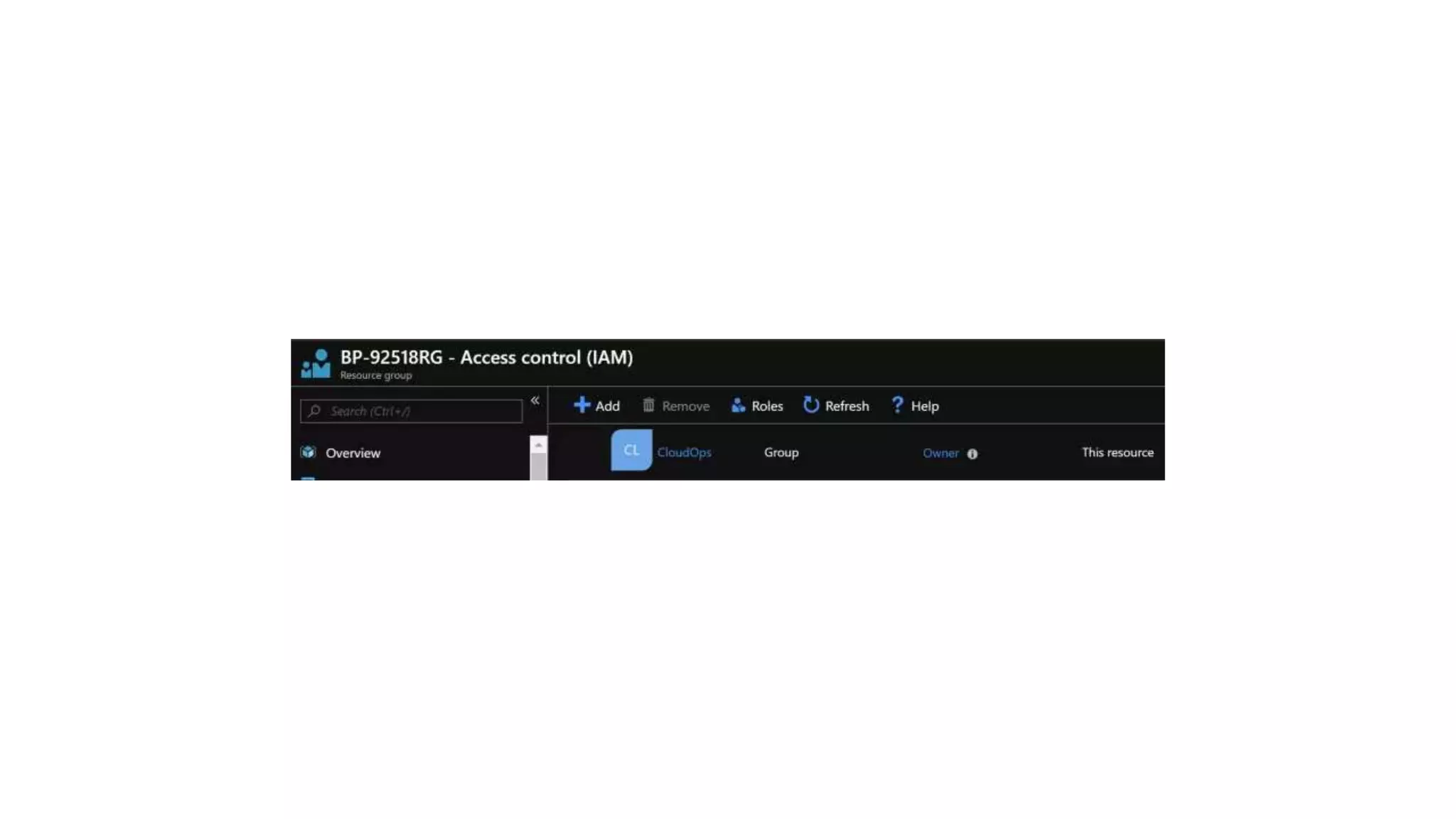
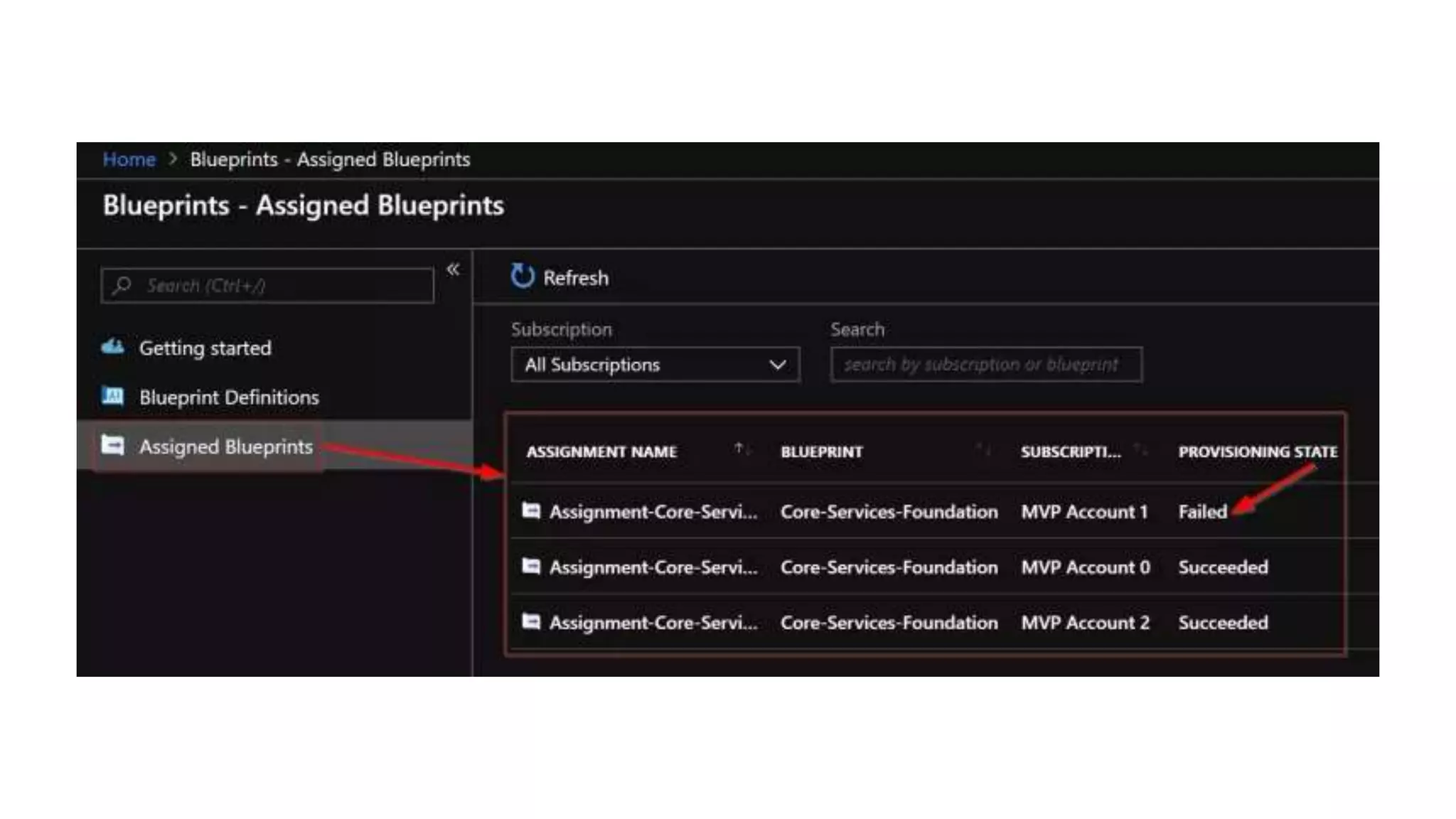
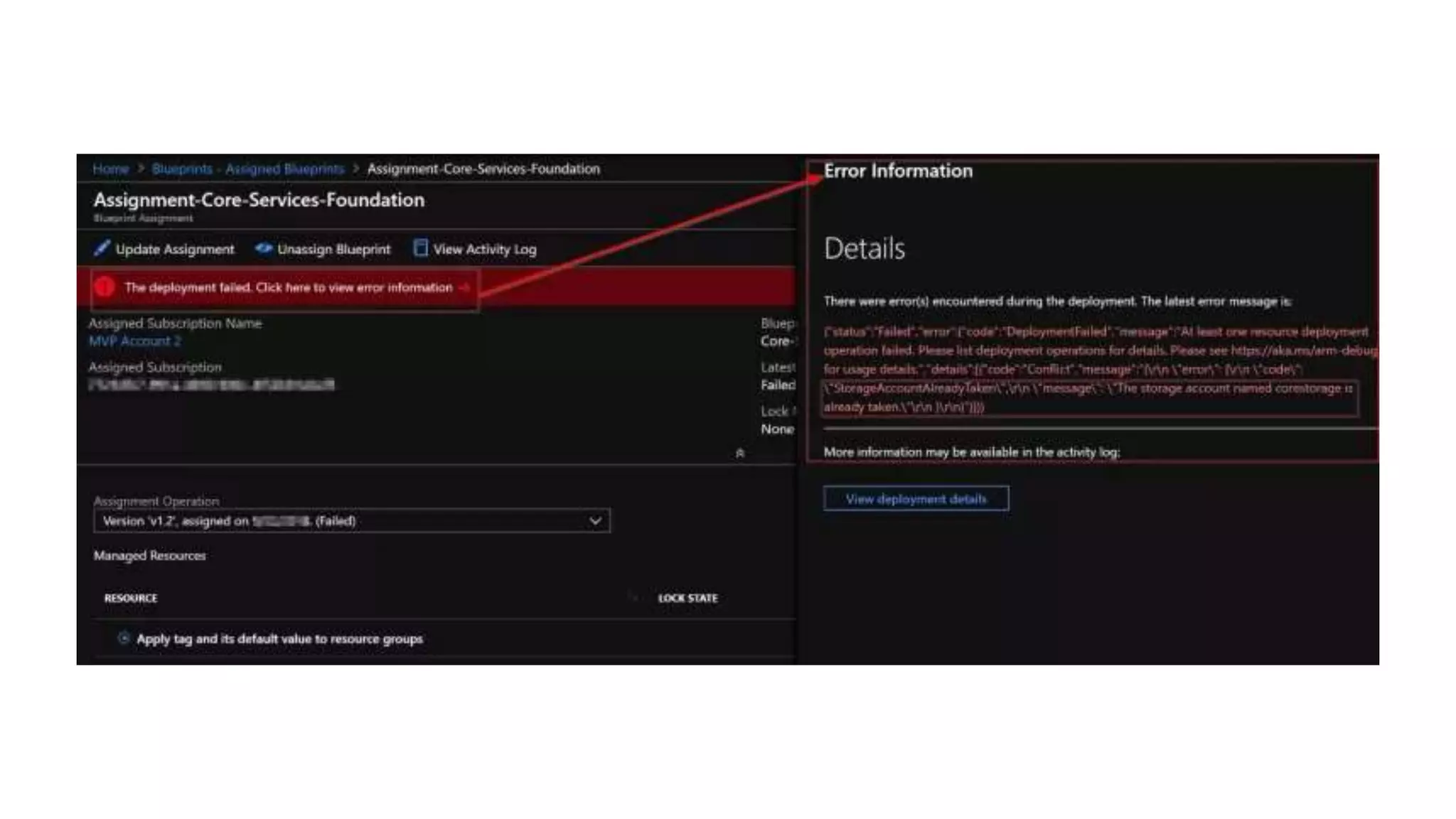
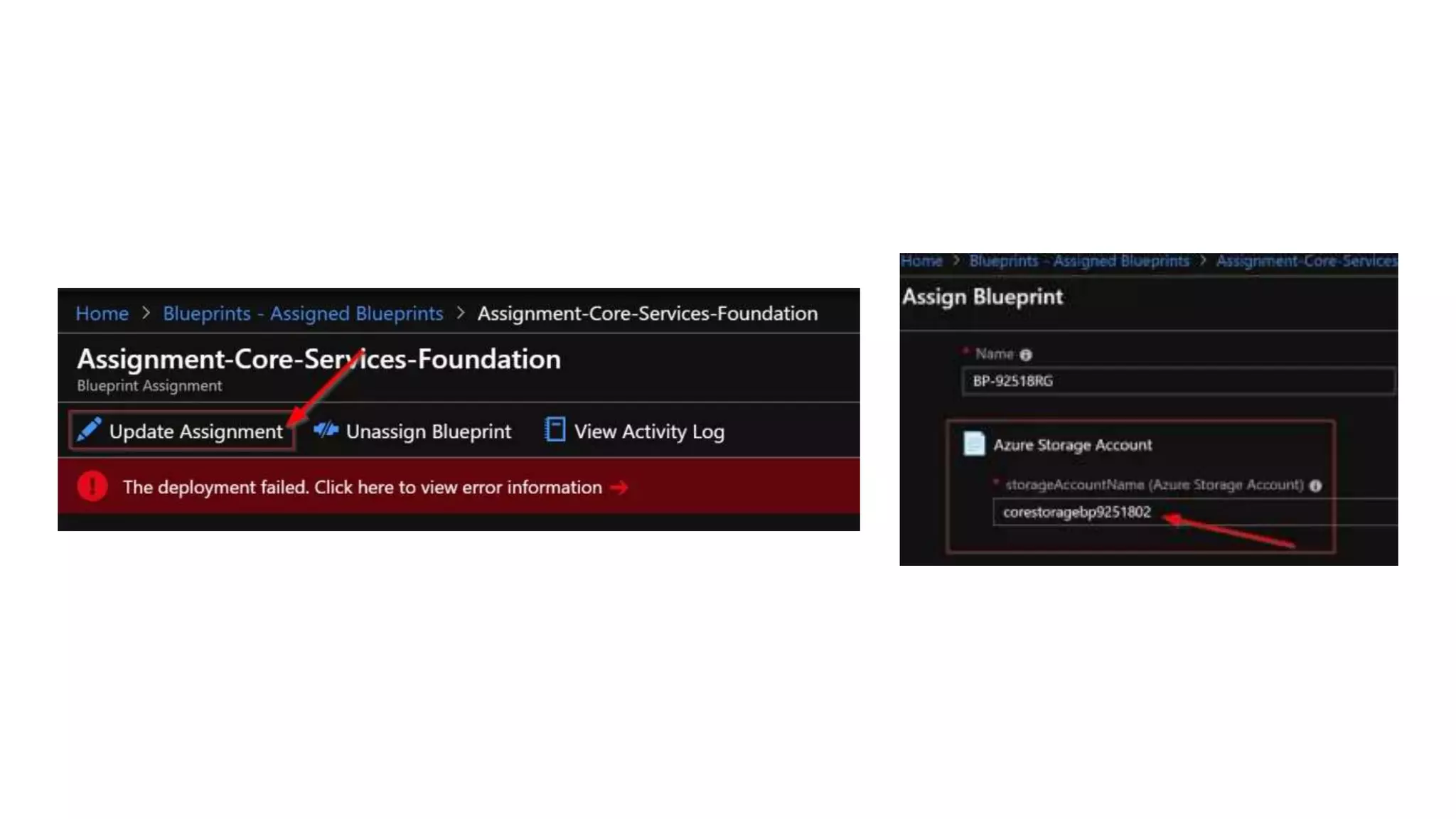
Azure Blueprints allows cloud architects to create a repeatable set of Azure resources that align with organizational standards. This tool facilitates rapid environment setup while ensuring compliance through built-in components. It includes features such as assignment sequencing, resource locking, and various artifact management for organized deployment.