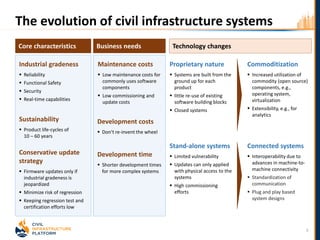
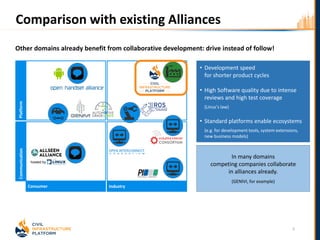
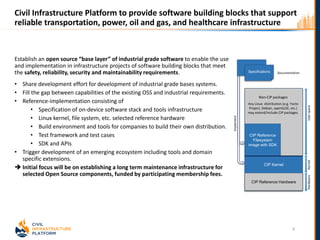
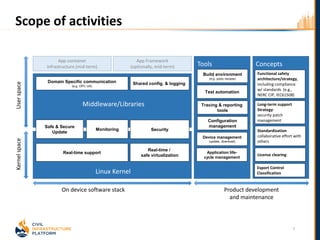
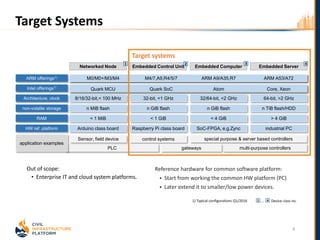
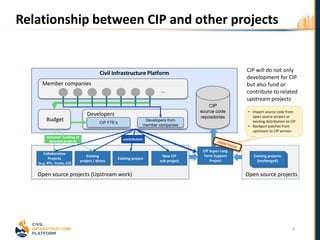
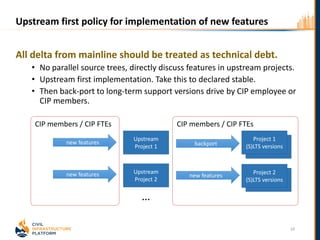
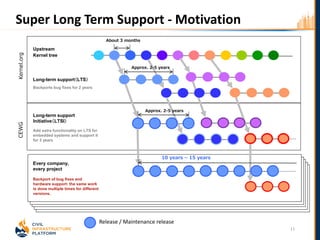
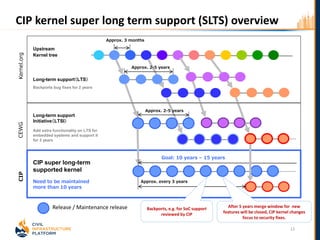
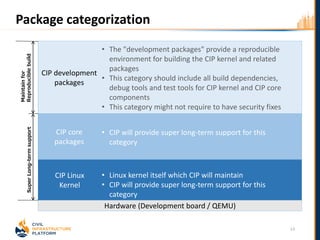
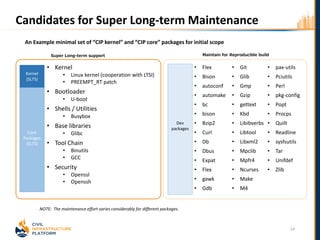
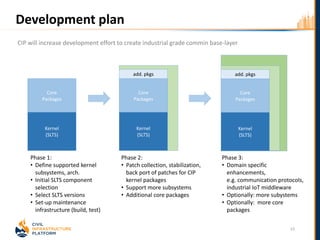
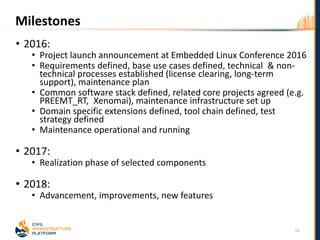
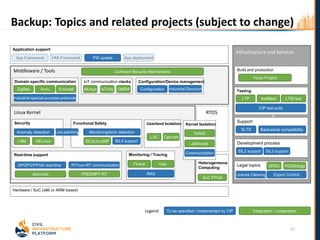
The Civil Infrastructure Platform (CIP) aims to create an open-source, industrial-grade software base for civil infrastructure systems, enhancing safety, reliability, and security. It promotes collaborative development while addressing the unique challenges of long-term maintenance and project sustainability. The initiative seeks to standardize software components and fill gaps between current available open-source solutions and industrial requirements, thereby accelerating development and improving quality across various infrastructure sectors.