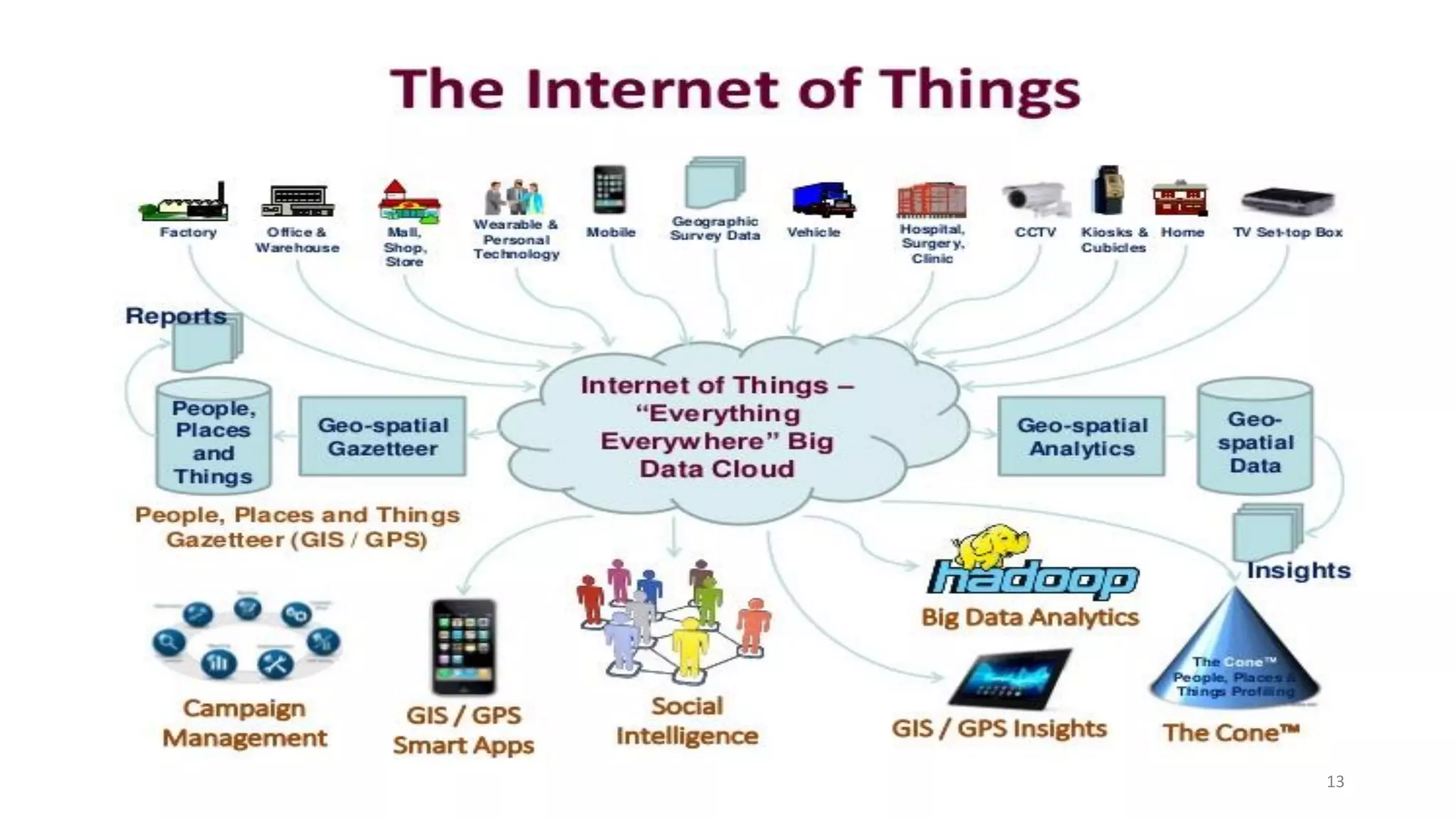
This document provides an overview of the Internet of Things (IoT). It begins by defining IoT and describing its key features such as artificial intelligence, connectivity, sensors, active engagement, and use of small devices. It then explains how IoT works and describes its architecture which includes sensing, network, data processing, and application layers. The document discusses the history of IoT and provides examples of its applications in various domains like smart homes, healthcare, transportation, and agriculture. It also outlines some of the pros and cons of IoT such as improved customer engagement but also security and privacy risks. In the end, the document discusses some IoT tools and platforms.