Internet: Its Past, Present and The Future
•Download as PPTX, PDF•
0 likes•33 views
Hey guys, here is a brief account of the past, present, and future aspects of the internet and how it helps us analyze things around us in a better way. //KUDOS
Report
Share
Report
Share
Recommended
Edge computing offloading: status & perspectives

Multi-access edge computing is a fundamental pillar of future 5G mobile networks. One of the most promising applications is computation offloading: the mobile user outsources computational-heavy tasks to devices in the edge tier, which is intermediate between user devices and remote clouds. While most research studies so far focus on reducing energy consumption of mobile devices, the importance of this metric may shrink in the future due to an increase of the number of dedicated engines in mobile phones/tables. However, new devices will appear that have _no_ computational power at all (such as smart glasses/contact lenses) for which computational offloading will be a key enabler.
“Memory Allocation in AI and Computer Vision Applications,” a Presentation fr...

“Memory Allocation in AI and Computer Vision Applications,” a Presentation fr...Edge AI and Vision Alliance
For the full video of this presentation, please visit:
https://www.edge-ai-vision.com/2020/11/memory-allocation-in-ai-and-computer-vision-applications-a-presentation-from-ceva/
For more information about edge AI and computer vision, please visit:
https://www.edge-ai-vision.com
Rami Drucker, Machine Learning System Team Leader at CEVA, presents the “Memory Allocation in AI and Computer Vision Applications” tutorial at the September 2020 Embedded Vision Summit.
Efficient edge computing is the foundation underlying AI and computer vision applications in autonomous vehicles, cameras, drones and many other applications. Because deep neural networks (DNNs) are memory intensive, creating efficient implementations of DNNs requires efficient use of memory and memory bandwidth.
In this talk, Drucker presents CEVA’s novel approach to enable efficient memory allocation to enable implementing DNNs under strict size and power constraints. The company’s approach utilizes a unified computational graph and takes into account the differing characteristics of different classes of memory (on-chip L1 and L2 SRAM and external DDR). Drucker also introduces CEVA’s XM6 and SensPro processors for vision and AI.IoT Meets the Cloud: The Origins of Edge Computing

History of edge computing: IoT meets the cloud. Lecture delivered as part of Duke University Electrical and Computer Engineering / Computer Science Special Topics course on Edge Computing designed and developed by the instructor.
Io t presentation

The IoT has exploded over the past years and will continue to grow. To handle mission-critical workloads and act as an enabler driving innovation at rapid scale, IoT demands a lot of capacity. What if you could deliver on the vision of constant experimentation and innovation at the speed of light? What if you could differentiate yourself from your competitors by innovating more quickly and releasing new products and services faster? Talking about fast, how do you make this possible from an infrastructure perspective? We need infrastructure beyond scalability and availability. How is this achieved?
Industry Transformation

Presentation on industry transformation at Södra's annual management strategy conference in Malmö March 2016.
presentation on Edge computing

Edge computing allows data produced by internet of things (IoT) devices to be processed closer to where it is created instead of sending it across long routes to data centers or clouds.
Doing this computing closer to the edge of the network lets organizations analyze important data in near real-time – a need of organizations across many industries, including manufacturing, health care, telecommunications and finance.Edge computing deployments are ideal in a variety of circumstances. One is when IoT devices have poor connectivity and it’s not efficient for IoT devices to be constantly connected to a central cloud.
Other use cases have to do with latency-sensitive processing of information. Edge computing reduces latency because data does not have to traverse over a network to a data center or cloud for processing. This is ideal for situations where latencies of milliseconds can be untenable, such as in financial services or manufacturing.
Wearable Photogrammetry - What to Wear for Work #COMIT2017

Presentation by Stuart Young at the 2017 COMIT Annual Conference 'Mobilising Digital Assets', to be held at The Building Centre in London on Wednesday 24th and Thursday 25th of May 2017. More information: http://www.comit.org.uk/live-blog-comit2017
Recommended
Edge computing offloading: status & perspectives

Multi-access edge computing is a fundamental pillar of future 5G mobile networks. One of the most promising applications is computation offloading: the mobile user outsources computational-heavy tasks to devices in the edge tier, which is intermediate between user devices and remote clouds. While most research studies so far focus on reducing energy consumption of mobile devices, the importance of this metric may shrink in the future due to an increase of the number of dedicated engines in mobile phones/tables. However, new devices will appear that have _no_ computational power at all (such as smart glasses/contact lenses) for which computational offloading will be a key enabler.
“Memory Allocation in AI and Computer Vision Applications,” a Presentation fr...

“Memory Allocation in AI and Computer Vision Applications,” a Presentation fr...Edge AI and Vision Alliance
For the full video of this presentation, please visit:
https://www.edge-ai-vision.com/2020/11/memory-allocation-in-ai-and-computer-vision-applications-a-presentation-from-ceva/
For more information about edge AI and computer vision, please visit:
https://www.edge-ai-vision.com
Rami Drucker, Machine Learning System Team Leader at CEVA, presents the “Memory Allocation in AI and Computer Vision Applications” tutorial at the September 2020 Embedded Vision Summit.
Efficient edge computing is the foundation underlying AI and computer vision applications in autonomous vehicles, cameras, drones and many other applications. Because deep neural networks (DNNs) are memory intensive, creating efficient implementations of DNNs requires efficient use of memory and memory bandwidth.
In this talk, Drucker presents CEVA’s novel approach to enable efficient memory allocation to enable implementing DNNs under strict size and power constraints. The company’s approach utilizes a unified computational graph and takes into account the differing characteristics of different classes of memory (on-chip L1 and L2 SRAM and external DDR). Drucker also introduces CEVA’s XM6 and SensPro processors for vision and AI.IoT Meets the Cloud: The Origins of Edge Computing

History of edge computing: IoT meets the cloud. Lecture delivered as part of Duke University Electrical and Computer Engineering / Computer Science Special Topics course on Edge Computing designed and developed by the instructor.
Io t presentation

The IoT has exploded over the past years and will continue to grow. To handle mission-critical workloads and act as an enabler driving innovation at rapid scale, IoT demands a lot of capacity. What if you could deliver on the vision of constant experimentation and innovation at the speed of light? What if you could differentiate yourself from your competitors by innovating more quickly and releasing new products and services faster? Talking about fast, how do you make this possible from an infrastructure perspective? We need infrastructure beyond scalability and availability. How is this achieved?
Industry Transformation

Presentation on industry transformation at Södra's annual management strategy conference in Malmö March 2016.
presentation on Edge computing

Edge computing allows data produced by internet of things (IoT) devices to be processed closer to where it is created instead of sending it across long routes to data centers or clouds.
Doing this computing closer to the edge of the network lets organizations analyze important data in near real-time – a need of organizations across many industries, including manufacturing, health care, telecommunications and finance.Edge computing deployments are ideal in a variety of circumstances. One is when IoT devices have poor connectivity and it’s not efficient for IoT devices to be constantly connected to a central cloud.
Other use cases have to do with latency-sensitive processing of information. Edge computing reduces latency because data does not have to traverse over a network to a data center or cloud for processing. This is ideal for situations where latencies of milliseconds can be untenable, such as in financial services or manufacturing.
Wearable Photogrammetry - What to Wear for Work #COMIT2017

Presentation by Stuart Young at the 2017 COMIT Annual Conference 'Mobilising Digital Assets', to be held at The Building Centre in London on Wednesday 24th and Thursday 25th of May 2017. More information: http://www.comit.org.uk/live-blog-comit2017
Innovations in Edge Computing and MEC

A revolution is going on at the Edge of the Network.
Why Edge is important?
How Edge Computing is shaping the way we do IoT, AR/VR, Big Data, Machine Learning and Analytics applications.
What are the important problems and who’s problem is this?
What solutions Industry is looking into right now?
This review of the "Industry report by SDxCentral" summarizes what is going on in the Industry.
Edge computing

Through this presentation, you will get to know about Edge computing and explore the fields where it is needed.
You can start exploring the technical knowledge by seeing what industries are working on now-days
Edge Computing

A talk presented at IEEE ComSoc workshop on Evolution of Data-centers in the context of 5G.
Discuss about what is edge computing and management issues in Edge Computing
“How Containerization Unblocks Barriers to Fast, Easy Deployment of AI-Driven...

“How Containerization Unblocks Barriers to Fast, Easy Deployment of AI-Driven...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2021/09/how-containerization-unblocks-barriers-to-fast-easy-deployment-of-ai-driven-visual-recognition-applications-a-presentation-from-camio/
Rakshit Agrawal, Director of Research and Development at Camio, presents the “How Containerization Unblocks Barriers to Fast, Easy Deployment of AI-Driven Visual Recognition Applications” tutorial at the May 2021 Embedded Vision Summit.
Recent progress in machine learning algorithms has been meteoric. Yet their implementation in real-world embedded applications crawls at a snail’s pace, in large part due to inconsistent and inefficient software architectures.
In this session, Agrawal introduces the concept of software containerization, explains how it works, and examines how a containerized deployment methodology at the edge can circumvent barriers that currently hinder the deployment of new and improved ML algorithms. He also explores the trade-offs and limitations of using containerization, and shows how his company has used containerization to enable new capabilities like mask detection and license plate recognition to be quickly deployed on to existing cameras.EDGE COMPUTING

Edge computing is a method of enabling small processing units near to the source of the data from sensors and central data servers. It utilizes cloud computing systems by performing data processing at the edge of the network, near the source of the data. This reduces the communications bandwidth needed between sensors by performing analytics and data processing.
Enabling Advanced Automation with Network-friendly Machine Learning

Talk at the Applied Machine Learning Days - AMLD 2019, 3rd edition of the emerging flagship conference on AI/ML. Examples of ML for network automation use cases.
Towards Intent-driven and Cognitive Network Operations

Talk at the ETSI 5G Summit 2017. Overcome operational complexity of networks by a radical shift in their usability: intent-based interfaces and empowerment of network components with superior cognitive capabilities are essential enablers.
ASIS 2013: Extending Surveillance Through Wireless Communications

ASIS 2013: Extending Surveillance Through Wireless Communications & Radar
The Automation Continuum

Keynote talk at iPOP 2018 conference. Develop a vision and components for "wide" and "deep" network automation.
Internet of Things from a Networked Society perspective

Like the pre-industrial and industrial worlds that preceded it, the Networked Society represents a fundamental paradigm shift for people, business and society. One in which new resources are continuously discovered, new forms of value are unleashed, and the most basic logics of life and business are transformed as a result. (Ericsson IoT Conference December 2014)
Recent Advances in Network Automation Standards

Keynote talk at IEEE CSCN 2018 Conference on Standards for Communications and Networking. Highlighting challenges and directions of zero-touch and automation in the networking industry and providing insights on recent standardization activities.
Your Network - Now Pay-Per-Use with Network on Demand Services

Pay-per-use LAN and Wi-Fi network infrastructure is available to help your business :
- Pay only for what is used (AND no capital investment is required)
- Minimize paying for unused infrastructure, so infrastructure costs align with business revenues
- Refocus your IT staff on business applications and communications
And don't miss slide 11...on the 10 differences from other offers.
CD December 2015 - IFS showcase

Presentation by IFS at the COMIT 2015 winter community day. Held in High Wycombe 3/12/2015 and hosted by IFS.
IoT technology considerations

With Internet of Things we are now entering a reality where billions of physical objects are being embedded with online intelligence and layer upon layer of digital interactivity. These connections, whether between wearable devices, cars and home automation systems, or among networked urban infrastructure and sensor-equipped industrial machinery, will serve as enablers for much more dynamic “things” enhanced with a wealth of new services that bring innovation with improved product performance and achievement of new levels efficiency. (Ericsson IoT Conference December 2014)
Mobile: the up and downside of risk

What are the opportunities and threats that come with IoT, BYOeverything, traditional systems and the need to have your workforce as productive as possible? Presentation delivered at Apps World London 12 November 2014
Aggregating IOT data for operators NFV cloud

Sumedha Swamy, Sr. Product Marketing Manager and Samita ChakrabartI, Principal Engineer at Ericsson presented at
Smart Parking Concept - An Internet of Things Solution

Universal access to computational power and bandwidth has allowed people and governments to accept and adopt new technologies that make life easier for everybody. A surge in the availability of low cost connected devices has paved the way for powerful technological advances towards the goal of building smart cities. This eBook presents the concept of smart parking that empowers communities to harness connectivity to manage traffic and optimize parking space that scales alongside demand.
Company: rapidBizApps
Website: www.rapidbizapps.com
More Related Content
What's hot
Innovations in Edge Computing and MEC

A revolution is going on at the Edge of the Network.
Why Edge is important?
How Edge Computing is shaping the way we do IoT, AR/VR, Big Data, Machine Learning and Analytics applications.
What are the important problems and who’s problem is this?
What solutions Industry is looking into right now?
This review of the "Industry report by SDxCentral" summarizes what is going on in the Industry.
Edge computing

Through this presentation, you will get to know about Edge computing and explore the fields where it is needed.
You can start exploring the technical knowledge by seeing what industries are working on now-days
Edge Computing

A talk presented at IEEE ComSoc workshop on Evolution of Data-centers in the context of 5G.
Discuss about what is edge computing and management issues in Edge Computing
“How Containerization Unblocks Barriers to Fast, Easy Deployment of AI-Driven...

“How Containerization Unblocks Barriers to Fast, Easy Deployment of AI-Driven...Edge AI and Vision Alliance
For the full video of this presentation, please visit: https://www.edge-ai-vision.com/2021/09/how-containerization-unblocks-barriers-to-fast-easy-deployment-of-ai-driven-visual-recognition-applications-a-presentation-from-camio/
Rakshit Agrawal, Director of Research and Development at Camio, presents the “How Containerization Unblocks Barriers to Fast, Easy Deployment of AI-Driven Visual Recognition Applications” tutorial at the May 2021 Embedded Vision Summit.
Recent progress in machine learning algorithms has been meteoric. Yet their implementation in real-world embedded applications crawls at a snail’s pace, in large part due to inconsistent and inefficient software architectures.
In this session, Agrawal introduces the concept of software containerization, explains how it works, and examines how a containerized deployment methodology at the edge can circumvent barriers that currently hinder the deployment of new and improved ML algorithms. He also explores the trade-offs and limitations of using containerization, and shows how his company has used containerization to enable new capabilities like mask detection and license plate recognition to be quickly deployed on to existing cameras.EDGE COMPUTING

Edge computing is a method of enabling small processing units near to the source of the data from sensors and central data servers. It utilizes cloud computing systems by performing data processing at the edge of the network, near the source of the data. This reduces the communications bandwidth needed between sensors by performing analytics and data processing.
Enabling Advanced Automation with Network-friendly Machine Learning

Talk at the Applied Machine Learning Days - AMLD 2019, 3rd edition of the emerging flagship conference on AI/ML. Examples of ML for network automation use cases.
Towards Intent-driven and Cognitive Network Operations

Talk at the ETSI 5G Summit 2017. Overcome operational complexity of networks by a radical shift in their usability: intent-based interfaces and empowerment of network components with superior cognitive capabilities are essential enablers.
ASIS 2013: Extending Surveillance Through Wireless Communications

ASIS 2013: Extending Surveillance Through Wireless Communications & Radar
The Automation Continuum

Keynote talk at iPOP 2018 conference. Develop a vision and components for "wide" and "deep" network automation.
Internet of Things from a Networked Society perspective

Like the pre-industrial and industrial worlds that preceded it, the Networked Society represents a fundamental paradigm shift for people, business and society. One in which new resources are continuously discovered, new forms of value are unleashed, and the most basic logics of life and business are transformed as a result. (Ericsson IoT Conference December 2014)
Recent Advances in Network Automation Standards

Keynote talk at IEEE CSCN 2018 Conference on Standards for Communications and Networking. Highlighting challenges and directions of zero-touch and automation in the networking industry and providing insights on recent standardization activities.
Your Network - Now Pay-Per-Use with Network on Demand Services

Pay-per-use LAN and Wi-Fi network infrastructure is available to help your business :
- Pay only for what is used (AND no capital investment is required)
- Minimize paying for unused infrastructure, so infrastructure costs align with business revenues
- Refocus your IT staff on business applications and communications
And don't miss slide 11...on the 10 differences from other offers.
CD December 2015 - IFS showcase

Presentation by IFS at the COMIT 2015 winter community day. Held in High Wycombe 3/12/2015 and hosted by IFS.
IoT technology considerations

With Internet of Things we are now entering a reality where billions of physical objects are being embedded with online intelligence and layer upon layer of digital interactivity. These connections, whether between wearable devices, cars and home automation systems, or among networked urban infrastructure and sensor-equipped industrial machinery, will serve as enablers for much more dynamic “things” enhanced with a wealth of new services that bring innovation with improved product performance and achievement of new levels efficiency. (Ericsson IoT Conference December 2014)
Mobile: the up and downside of risk

What are the opportunities and threats that come with IoT, BYOeverything, traditional systems and the need to have your workforce as productive as possible? Presentation delivered at Apps World London 12 November 2014
Aggregating IOT data for operators NFV cloud

Sumedha Swamy, Sr. Product Marketing Manager and Samita ChakrabartI, Principal Engineer at Ericsson presented at
What's hot (20)
“How Containerization Unblocks Barriers to Fast, Easy Deployment of AI-Driven...

“How Containerization Unblocks Barriers to Fast, Easy Deployment of AI-Driven...
Next-Generation Closed-Loop Automation - an Inside View

Next-Generation Closed-Loop Automation - an Inside View
Enabling Advanced Automation with Network-friendly Machine Learning

Enabling Advanced Automation with Network-friendly Machine Learning
Towards Intent-driven and Cognitive Network Operations

Towards Intent-driven and Cognitive Network Operations
Edge Computing: Bringing the Internet Closer to You

Edge Computing: Bringing the Internet Closer to You
ASIS 2013: Extending Surveillance Through Wireless Communications

ASIS 2013: Extending Surveillance Through Wireless Communications
Internet of Things from a Networked Society perspective

Internet of Things from a Networked Society perspective
Your Network - Now Pay-Per-Use with Network on Demand Services

Your Network - Now Pay-Per-Use with Network on Demand Services
Similar to Internet: Its Past, Present and The Future
Smart Parking Concept - An Internet of Things Solution

Universal access to computational power and bandwidth has allowed people and governments to accept and adopt new technologies that make life easier for everybody. A surge in the availability of low cost connected devices has paved the way for powerful technological advances towards the goal of building smart cities. This eBook presents the concept of smart parking that empowers communities to harness connectivity to manage traffic and optimize parking space that scales alongside demand.
Company: rapidBizApps
Website: www.rapidbizapps.com
The Cloud and the Car

Cloud computing is being adopted rapidly today, fueled by the explosion in mobile devices. The car is the third-fastest-growing mobile 'device'. Mandated use of the Cloud by the American government is pushing even faster growth. The shift to electric vehicles adds even more urgency. Here is a view of how the car is becoming a moving information transceiver for the Cloud...a mobile sensor that feeds the Cloud. See also some work on a First Responder Test-Bed in Canada
Internet of things - Introduction and Variations (Architecture)

The slides includes the IOT Architecture introduction and how that is being used in certain use cases around the industries.
Topics include :
Introduction
Trends and Hype cycle
Major IOT Players
Real World Problems
IOT Architecture and variations
Challenges and Tools
Difference between M2M and IOT practice.
KPI and Criteria
Evaluation and Decision
Conclusion
Informix internet of things

Informix - Internet of Things, "Internet of Things: Intelligent Database of Choice - Embedded database for Devices and Enterprise database for the Cloud" Sandor Szabo
Optimization of Fog computing for Industrial IoT applications

Presentation at Southern Africa Telecommunication Networks and Applications Conference (SATNAC) 2019
Particle Keynote with Zach Supalla

The latest new products and announcements from Particle CEO and Co-founder Zach Supalla, with some special surprise guests.
Semicon west monetizing the internet of things

Everyone wants the Internet of Things to be huge, but so far, nobody has cracked the code. In this presentation, I argue that our failure to focus on driving ROI from assets and creating real value for consumers and enterprises is at fault and suggest some ways we can do better.
Hugo Fiennes - Security and the IoT - Electric Imp

Though the potential of the IoT is vast, adoption can easily be curtailed by security worries. No company wants their products to be a victim of a hack, yet many do not appear to consider security as a primary driver of design decisions. This presentation will look at IoT security and describe what product designers – regardless of platform – need to be aware of if they want to build a secure and successful device.
IoT security encompasses requirements that are new for many product designers – such as provisioning, authentication, OTA upgrades and link encryption – and weaknesses in any one could potentially be used to compromise the security of the end product. From physical attacks to analysis of communications channels, there are many possible attack vectors that need to be considered.
From hacked routers to refrigerators sending spam email, there have been a lot of scary news stories about Internet of Things (IoT) security, or lack of it. According to the 2014 Hewlett-Packard Internet of Things Research Study, 70% of Internet connected devices they surveyed didn’t even use encrypted network connections. The US Federal Trade Commission (FTC) recently weighed in on the issue too, releasing a report that outlines potential IoT security risks, ranging from unauthorized access and misuse of personal information, to facilitation of attacks on other systems and risks to personal safety.
Disruptive Trends Fueled by AI & Camera Edge Analytics

Disruptive Trends Fueled by AI & Camera Edge Analytics. Memoori is joined by Nikolas Fröhle from German Startup company Security and Safety Things for an in-depth discussion into the trends disrupting the Video Surveillance industry; including Artificial Intelligence Software and Edge Analytics on the camera.
Global C4IR-1 Masterclass Adryan - Zuehlke Engineering 2017

IoT Analytics: there's not just predictive maintenance.
The global C4IR(TM) event series is available to franchise via www.cir-strategy.com as C4IRx.
Unveiling the Sydney IoT Landscape

The "Internet of Things" (IoT) has been around a long time and is becoming an increasingly growing topic. It has already impacted on our everyday lives at the workplace and at home.
Come and dive in for a night of exploration as we speak about some amazing products, IoT trends, current landscape and what the future will hold
There will be short IoT presentations as well as a panel of IoT panel speakers for you to engage and ask questions.
Speaking at John Carrol University on the Internet of Things

I was honored to have been invited to speak at John Carroll University on “The Internet of Things - Making the Physical World Smarter.” It was an extremely fun and engaging audience and I enjoyed every minute of the presentation. I hope you enjoy it as well and please don't hesitate to reach out with any questions.
Session 1908 connecting devices to the IBM IoT Cloud

IBM MessageSight and the IBM Internet of Things cloud enable connectivity across a wide variety of devices - from existing devices in silos and systems through the wide range of new devices that are appearing on a daily basis. This session covers patterns of connectivity, how to make it happen, including sending events like measurements and receiving of commands. The session goes into detail on how to use the industry standard MQ Telemetry Transport protocol to achieve this and encompasses best practices for topics and message format.
Internet of things basics

A slightly updated version of the Internet of Things presentation previously uploaded.
Patentabilityof Software & Business Methods

Patentabilityof Software & Business Methods
Contact Us for Intellectual Property Services
BananaIP Counsels
Regd Office
No.40,3rd Main Road,JC Industrial Estate,
Kanakapura Road,Bangalore – 560 062.
Email: contact@bananaip.com
Telephone: +91-80-26860414 /24/34
Similar to Internet: Its Past, Present and The Future (20)
Cata i canada the cloud and the car diva presentation aug 31 12

Cata i canada the cloud and the car diva presentation aug 31 12
Smart Parking Concept - An Internet of Things Solution

Smart Parking Concept - An Internet of Things Solution
Internet of things - Introduction and Variations (Architecture)

Internet of things - Introduction and Variations (Architecture)
Optimization of Fog computing for Industrial IoT applications

Optimization of Fog computing for Industrial IoT applications
Hugo Fiennes - Security and the IoT - Electric Imp

Hugo Fiennes - Security and the IoT - Electric Imp
Disruptive Trends Fueled by AI & Camera Edge Analytics

Disruptive Trends Fueled by AI & Camera Edge Analytics
Global C4IR-1 Masterclass Adryan - Zuehlke Engineering 2017

Global C4IR-1 Masterclass Adryan - Zuehlke Engineering 2017
Speaking at John Carrol University on the Internet of Things

Speaking at John Carrol University on the Internet of Things
Session 1908 connecting devices to the IBM IoT Cloud

Session 1908 connecting devices to the IBM IoT Cloud
More from Abhishek Tonpe
Business Analyst VS. System Analyst

Hey guys, here is a brief descriptive study about the differences between the systems analyst and business analyst. Also, to back it up we have presented a case of Airbnb.
//KUDOS
Generations of Computers 

Hey guys, here is a brief account of the first, second, and third generations of computing and the evolution of computers.
//KUDOS
Metronidazole: A Comparison Between Dosage Forms 

Hey guys, here is a comparison between the Tablet and Gel form of Metronidazole in regards to the marketing aspect of the drug.
//KUDOS
Cath Lab: A presentation about all the aspects regarding management

Hey guys, here is a presentation regarding the managerial aspects of a catheterization laboratory. Also, ppt includes a case study.
// KUDOS
Chatbot: Recent developments and Trends

Here is a brief ppt that gives you a basic idea about what chatbots are and the recent technological trends.
// Kudos.
Business plan- A model assignment exploring the different aspects of business...

Hey buddy! here is a business modeling blueprint that might help you sort out your queries regarding a business plan.
Cheers!
More from Abhishek Tonpe (6)
Cath Lab: A presentation about all the aspects regarding management

Cath Lab: A presentation about all the aspects regarding management
Business plan- A model assignment exploring the different aspects of business...

Business plan- A model assignment exploring the different aspects of business...
Recently uploaded
1.Wireless Communication System_Wireless communication is a broad term that i...

Wireless communication involves the transmission of information over a distance without the help of wires, cables or any other forms of electrical conductors.
Wireless communication is a broad term that incorporates all procedures and forms of connecting and communicating between two or more devices using a wireless signal through wireless communication technologies and devices.
Features of Wireless Communication
The evolution of wireless technology has brought many advancements with its effective features.
The transmitted distance can be anywhere between a few meters (for example, a television's remote control) and thousands of kilometers (for example, radio communication).
Wireless communication can be used for cellular telephony, wireless access to the internet, wireless home networking, and so on.
The+Prospects+of+E-Commerce+in+China.pptx

The Prospects of E-commerce in China,www.cfye-commerce.shop
急速办(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单原版一模一样

原版纸张【微信:741003700 】【(bedfordhire毕业证书)英国贝德福特大学毕业证成绩单】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
History+of+E-commerce+Development+in+China-www.cfye-commerce.shop

History+of+E-commerce+Development+in+China-www.cfye-commerce.shop
This 7-second Brain Wave Ritual Attracts Money To You.!

Discover the power of a simple 7-second brain wave ritual that can attract wealth and abundance into your life. By tapping into specific brain frequencies, this technique helps you manifest financial success effortlessly. Ready to transform your financial future? Try this powerful ritual and start attracting money today!
ER(Entity Relationship) Diagram for online shopping - TAE

https://bit.ly/3KACoyV
The ER diagram for the project is the foundation for the building of the database of the project. The properties, datatypes, and attributes are defined by the ER diagram.
原版仿制(uob毕业证书)英国伯明翰大学毕业证本科学历证书原版一模一样

原版纸张【微信:741003700 】【(uob毕业证书)英国伯明翰大学毕业证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines

Talk presented at Kubernetes Community Day, New York, May 2024.
Technical summary of Multi-Cluster Kubernetes Networking architectures with focus on 4 key topics.
1) Key patterns for Multi-cluster architectures
2) Architectural comparison of several OSS/ CNCF projects to address these patterns
3) Evolution trends for the APIs of these projects
4) Some design recommendations & guidelines for adopting/ deploying these solutions.
test test test test testtest test testtest test testtest test testtest test ...

salamsasalamlamsalamsalamsalamsalamsalamsalamsalam
How to Use Contact Form 7 Like a Pro.pptx

Contact Form 7 is a popular plugins for WordPress. This is an introduction into its features and usage.
1比1复刻(bath毕业证书)英国巴斯大学毕业证学位证原版一模一样

原版纸张【微信:741003700 】【(bath毕业证书)英国巴斯大学毕业证学位证】【微信:741003700 】学位证,留信认证(真实可查,永久存档)offer、雅思、外壳等材料/诚信可靠,可直接看成品样本,帮您解决无法毕业带来的各种难题!外壳,原版制作,诚信可靠,可直接看成品样本。行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备。十五年致力于帮助留学生解决难题,包您满意。
本公司拥有海外各大学样板无数,能完美还原海外各大学 Bachelor Diploma degree, Master Degree Diploma
1:1完美还原海外各大学毕业材料上的工艺:水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠。文字图案浮雕、激光镭射、紫外荧光、温感、复印防伪等防伪工艺。材料咨询办理、认证咨询办理请加学历顾问Q/微741003700
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
Recently uploaded (16)
1.Wireless Communication System_Wireless communication is a broad term that i...

1.Wireless Communication System_Wireless communication is a broad term that i...
guildmasters guide to ravnica Dungeons & Dragons 5...

guildmasters guide to ravnica Dungeons & Dragons 5...
History+of+E-commerce+Development+in+China-www.cfye-commerce.shop

History+of+E-commerce+Development+in+China-www.cfye-commerce.shop
This 7-second Brain Wave Ritual Attracts Money To You.!

This 7-second Brain Wave Ritual Attracts Money To You.!
ER(Entity Relationship) Diagram for online shopping - TAE

ER(Entity Relationship) Diagram for online shopping - TAE
Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines

Multi-cluster Kubernetes Networking- Patterns, Projects and Guidelines
test test test test testtest test testtest test testtest test testtest test ...

test test test test testtest test testtest test testtest test testtest test ...
Living-in-IT-era-Module-7-Imaging-and-Design-for-Social-Impact.pptx

Living-in-IT-era-Module-7-Imaging-and-Design-for-Social-Impact.pptx
Internet: Its Past, Present and The Future
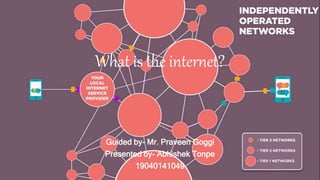
- 1. What is the internet? Guided by- Mr. Praveen Goggi Presented by- Abhishek Tonpe 19040141049
- 2. The beginning • Vincent Cerf & Bob Kahn began working on the internet, which was the result of an experiment ARPANET. It was a defence department project. • Paul Baran proposed the idea of a system that could survive a nuclear attack through decentralization of data. • Communication is done via internet protocol suit (TCP/ip)
- 3. Current situation Internet of things (Case Example)
- 4. • A minor problem with the break liners occur in a person’s car. • The gateway sorts the data and relevant data is sent to the manufacturer’s platform. The platform stores thousands of bits of information from multiple cars. • The manufacture uses the platform to create and manage applications that solve specific issues. Example: Asset Management System. Asset management system over sees all their customers car on road as well as parts in the warehouse. • Using this the algorithms • Potential date and time for service appointment is suggested. • Directions to the nearest certified dealer. • Coupon for the service. • App insures that the brakes are covered under warranty. • Order of correct replacement part. (specific model number et cetera) • Sending these parts to the dealership before your arrival. • These systems not only benefit the customers but also the manufacturers. • The manufacturer can see if multiple cars had the same problem. • Thus narrowing down to the manufacturing date. • The production unit and the specific production line. • Providing a better view you’re the root of problem. Enhanced root cause analysis.
- 5. The prospect ahead • 5G technology: Data can be gathered, analyzed and managed in real time, virtually without delays, greatly broadening potential Iot applications. • Implants & glasses: Toby Negrin, Wikimedia Foundation’s Chief Product Officer, compared the internet to electricity as it becomes an “omnipresent utility, something we expect to always be available and around us... intertwined in our daily lives.” • Edge computing: This is basically the exact opposite of cloud computing. By storing data locally, it offers a cheaper, faster, and more efficient approach to data processing. • Increased security concern: despite the promise that Iot holds for us, it carries a dual edged sword for making us more vulnerable.