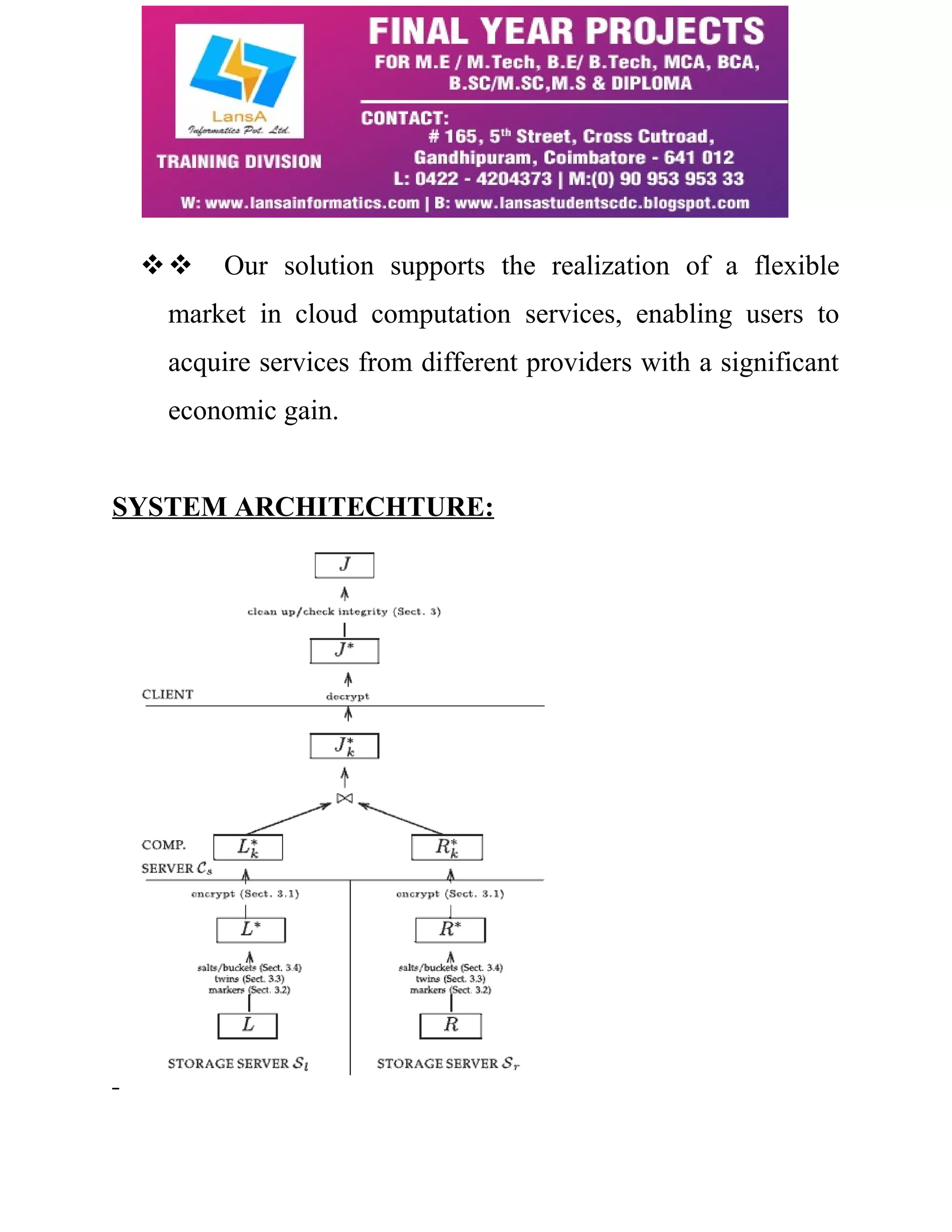
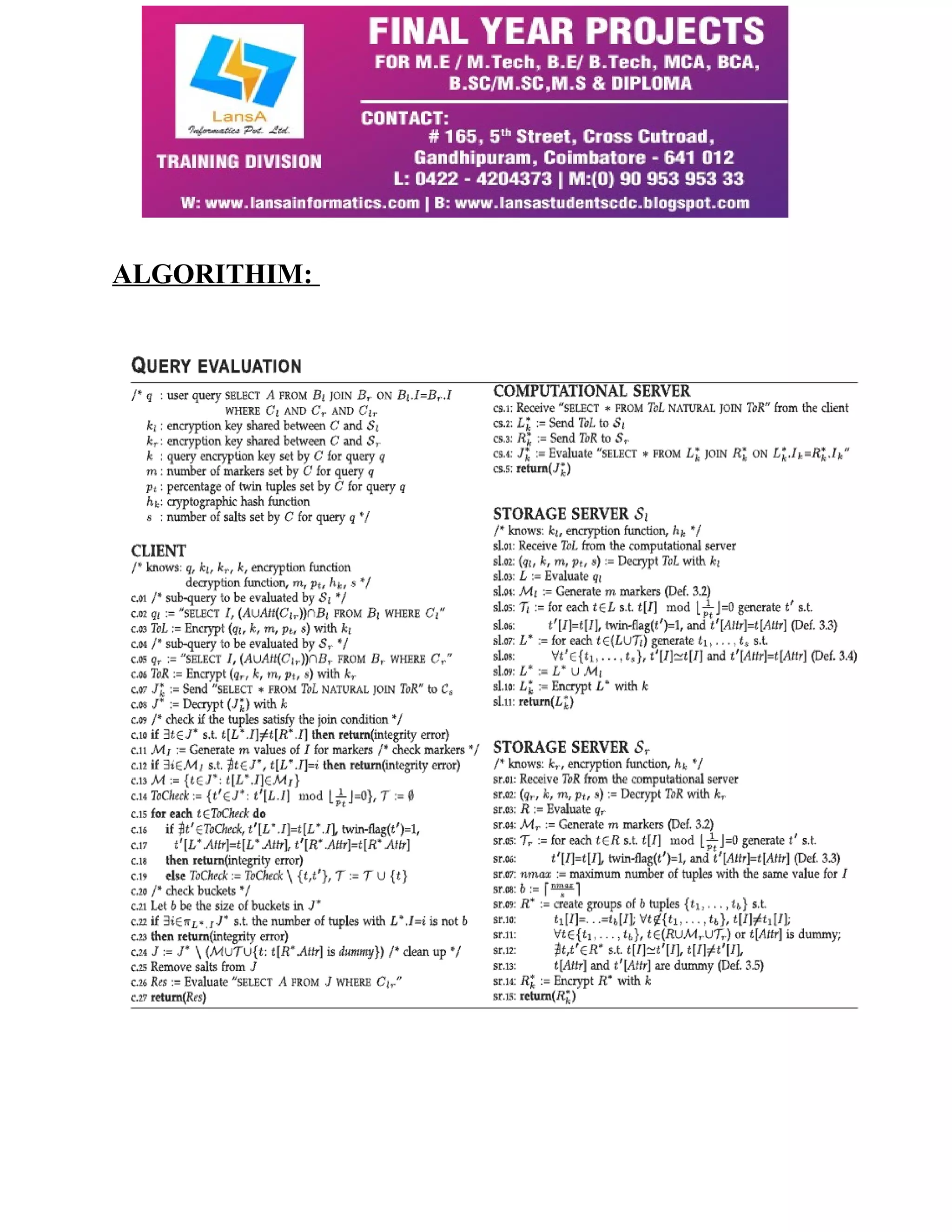
This document discusses a system designed to ensure the integrity of join query results produced by external cloud computational providers and databases, emphasizing transparency and confidentiality. It highlights the evolution of cloud services towards a diverse ecosystem that requires robust integrity guarantees, overcoming limitations of existing systems that mostly focus on data confidentiality. The proposed approach enables users to cost-effectively select cloud services while ensuring security, hence facilitating a flexible market in cloud computing.