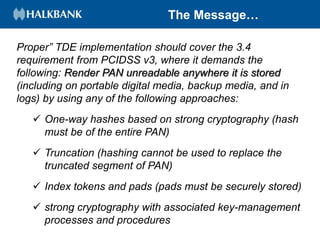
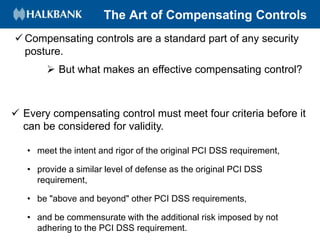
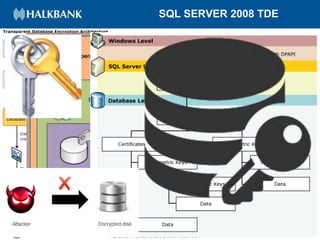
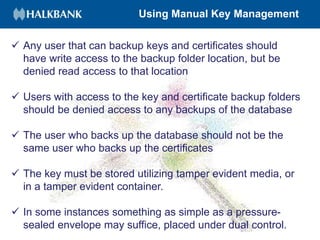
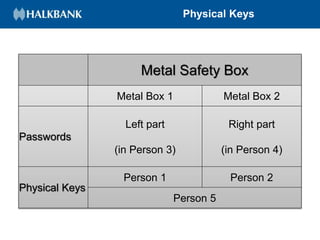
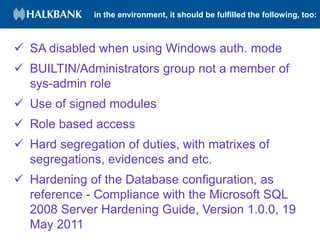
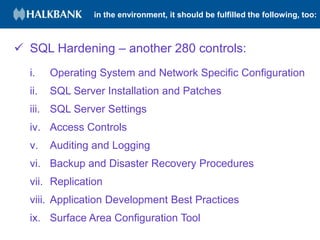
This document discusses implementing Transparent Data Encryption (TDE) and additional compensating controls as an alternative method to encrypting primary account numbers (PANs) in a Microsoft SQL database to comply with PCI DSS version 3 requirement 3.4. TDE provides full data encryption with minimal performance impact. Additional controls like key management and access restrictions are also required. Compensating controls can meet the intent of PCI requirements if they provide similar defense and are above other requirements. TDE benefits include no schema changes and minimal performance impact, but it only encrypts data at rest and does not help secure communication. Proper key backups and access controls must be implemented for TDE.