How to Recover Corrupted Word File
•
0 likes•446 views
If your word file corrupted due to any cause like virus-attack, human error, etc. You can recover with given manual process. so, please visit our official web-sites : http://www.repairdocfile.com
Report
Share
Report
Share
Download to read offline
Recommended
Fix Slow Running PC

The Internet is flooded with questions related to slowed PC performance over a period of time. In this article we'll help you optimize the system and recover lost performance.
Reimaging Your MacBook

How to back up and restore your files to your MacBook for the reimaging process.
Bust the myth upgrade xp to windows 7 final

West Region TechNet Presents: Bust the Myth: Can you upgrade Windows XP to Windows 7.
Windows server 2008 r2 installation

This section describes the steps for installing the Windows Server 2008 R2 on a new Virtual Machine.
02 technicla tearm sttp 2020

This is the educational material for STTP 2020 IT workshop. Students can learn themselves with this published PowerPoint. I hope the student gets more interest and get skill in IT world..
Recommended
Fix Slow Running PC

The Internet is flooded with questions related to slowed PC performance over a period of time. In this article we'll help you optimize the system and recover lost performance.
Reimaging Your MacBook

How to back up and restore your files to your MacBook for the reimaging process.
Bust the myth upgrade xp to windows 7 final

West Region TechNet Presents: Bust the Myth: Can you upgrade Windows XP to Windows 7.
Windows server 2008 r2 installation

This section describes the steps for installing the Windows Server 2008 R2 on a new Virtual Machine.
02 technicla tearm sttp 2020

This is the educational material for STTP 2020 IT workshop. Students can learn themselves with this published PowerPoint. I hope the student gets more interest and get skill in IT world..
Lotus Notes Error 4005 Access to Data Denied - Fix It

Solution to fix the error 4005 access to data denied or cannot create file in IBM Lotus Notes email client during opening mail file or creating new memo. Know more @ http://www.emaildoctor.org/convert/nsf-pst.html
30 Inspirational Entrepreneurial Quotes

Being an entrepreneur is a fabulous experience and a great way to learn new things everyday. This quotes are my fuel for everyday; quotes to inspire and motivate you during those tough patches.
Photo recovery

Here is a guide that helps in fix your deleted, formatted and lost photo, video and song. Visit here : http://digitalmediarecovery.blogspot.com/2013/12/recover-corrupt-photos.html
Repair pst

What to do if you are address the issues in making the regular operations of MS Outlook like send/receive. The above presentation mentioned all steps to resolve the all outlook issue.
Fixed: MS Word the File is Corrupted and Cannot be Opened

Sometimes, some unavoidable problems will appear during using MS Word. Such as the suddenly corrupted or damaged. Why the Word document that has been used normally is suddenly damaged and can’t be opened? Is there any way to solve it? In this article, you can learn about the reasons for Microsoft Word document damage and learn how to solve the problem -- the file is corrupted and cannot be opened.
More Related Content
What's hot
Lotus Notes Error 4005 Access to Data Denied - Fix It

Solution to fix the error 4005 access to data denied or cannot create file in IBM Lotus Notes email client during opening mail file or creating new memo. Know more @ http://www.emaildoctor.org/convert/nsf-pst.html
What's hot (6)
Lotus Notes Error 4005 Access to Data Denied - Fix It

Lotus Notes Error 4005 Access to Data Denied - Fix It
Viewers also liked
30 Inspirational Entrepreneurial Quotes

Being an entrepreneur is a fabulous experience and a great way to learn new things everyday. This quotes are my fuel for everyday; quotes to inspire and motivate you during those tough patches.
Photo recovery

Here is a guide that helps in fix your deleted, formatted and lost photo, video and song. Visit here : http://digitalmediarecovery.blogspot.com/2013/12/recover-corrupt-photos.html
Repair pst

What to do if you are address the issues in making the regular operations of MS Outlook like send/receive. The above presentation mentioned all steps to resolve the all outlook issue.
Viewers also liked (15)
Similar to How to Recover Corrupted Word File
Fixed: MS Word the File is Corrupted and Cannot be Opened

Sometimes, some unavoidable problems will appear during using MS Word. Such as the suddenly corrupted or damaged. Why the Word document that has been used normally is suddenly damaged and can’t be opened? Is there any way to solve it? In this article, you can learn about the reasons for Microsoft Word document damage and learn how to solve the problem -- the file is corrupted and cannot be opened.
SysInfoTools MS Word Doc Repair

The Doc Repair software of SysInfoTools is an ideal solution for MS Word users. The software helps users repair corrupt word documents (Doc) and recover maximum recoverable data from them. It enables users to recover single as well as multiple Doc files simultaneously. It safely restores data from selected Doc file(s) such as: formatted text, images, tables, graphs, charts, hyperlinks, headers & footers without causing any damage or alteration. It supports previewing of recovered data in two forms: text and image. The software is available with free demo version to examine the performance and features before purchasing the full version.
Entourage recovery

Entourage recovery software follows advanced means for recovering lost, deleted, corrupted, missing RGE database file. Address book, notes, contact and entourage email recovery is all possible in an easy and efficient way for entourage 2004 and 2008 working on Mac OS X system.
SysInfoTools MS Word DOCM Recovery

SysInfoTools MS Word DOCM Recovery software is an advanced solution to fix corrupt .docm files of Microsoft Word. It recovers maximum possible data from corrupt .docm files and enables users to see the preview of recovered data in both text and image form. It supports recovery of multiple .docm files at a time. The software maintains the file structure, formatting and properties while recovering corrupt .docm files.
How to Recover Files

Lost important data from your PC? No worries, SFWare software can be made use of for recovering deleted or lost files from various storage devices instantly
Seven steps to great PC health (Windows)

A simple and easy overview of what you can do to keep your Windows PC running smoothly. Free and easy cleanup and optimization tips with useful links and short intros.
SysInfoTools Archive Recovery

SysInfoTools Archive Recovery Software is an outstanding solution to recover multiple types of compressed archives such as ZIP, RAR, TAR, TAR.GZ and 7Z archive. It is the only software in the market that supports the recovery of five different files. The software supports recovery of both ZIP files, i.e. 32 & 64 bits which are created in Windows as well as Mac OSs. It can successfully recovers a corrupt archive file up to 1 TB (1024 GB) of size. The software supports multiple archive recovery at the same time. The corrupted archives (except 7Z) which are password protected can also be recovered by this software.
Step guide to Outlook mac backup

Too many users have been worried about the process of email backup and recovery. This is why there is a sudden rise in the number of solutions which are available online. If you try to find a tool to backup outlook email folders, you are going to come across hundreds of tools, all of which claim to be the best way to backup outlook emails. Now, are all of these tools safe?
Let’s find out
The truth about online methods to backup outlook email
Since there are too many online and free tools that claim to get this task done for you, you should know how these methods work. Most of these tools are web based solutions where you are asked to upload your email data on to their server and they create a backup archive. It is as risky as it sounds. Such methods cannot ensure the safety and security of your email data. There have been major cases of file modification and data loss with these tools. So tread wisely.
How to Recover Word Document

Yodot File Recovery application helps you recover deleted or lost Word document on Windows system easily and efficiently.
How to Recover Deleted Word Documents on Windows

When accidently deleted a Word document permanently, can it be recovered? Yes, watch this presentation to learn how to recover deleted documents with ease.
Basic Computer Skills.pptx

About
Google Drive
Anti Virus
How to Delete Tempory Files
How to Change the Network Adapter setting
Connecting a Projector and using Extended Desktop
Cleaning and Maintaing your Laptop
Troubleshooting Techniques
1.0 QuickBooks Fundementals : Day 02 Windows :2.1 windows

What all windows information a NHT should have.The basics of windows which are required to be performed and known by a proadvisor to troubleshoot the error.
SysInfoTools OpenOffice Writer Repair

OpenOffice Writer Repair software of SysInfoTools is an advanced solution to repair highly corrupt ODT documents of OpenOffice Writer and recover maximum possible data from them. The software successfully resolves all the error messages from corrupt open office documents. It supports recovery of multiple corrupt ODT files simultaneously. The ODT recovery is executed in two recovery modes: standard and advanced mode. It supports all major versions of OpenOffice (from v1.0 to v3.4). The preview of recovered data is shown in two forms: text and image form. And, all the recovered data can be saved in two formats: ODT and HTML.
Care & Feeding Of Your Computer

A short presentation I am giving to local instructors on basic computer maintenance as part of the LTI series.
Low disk space is dangerous for your pc

this slide contains information about why low disk space is dangerous for your pc
Similar to How to Recover Corrupted Word File (20)
Fixed: MS Word the File is Corrupted and Cannot be Opened

Fixed: MS Word the File is Corrupted and Cannot be Opened
Recover shift+delete word file on Windows Computer

Recover shift+delete word file on Windows Computer
How to restore deleted word documents on windows 7

How to restore deleted word documents on windows 7
1.0 QuickBooks Fundementals : Day 02 Windows :2.1 windows

1.0 QuickBooks Fundementals : Day 02 Windows :2.1 windows
Recently uploaded
National Security Agency - NSA mobile device best practices

Threats to mobile devices are more prevalent and increasing in scope and complexity. Users of mobile devices desire to take full advantage of the features
available on those devices, but many of the features provide convenience and capability but sacrifice security. This best practices guide outlines steps the users can take to better protect personal devices and information.
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

Dr. Sean Tan, Head of Data Science, Changi Airport Group
Discover how Changi Airport Group (CAG) leverages graph technologies and generative AI to revolutionize their search capabilities. This session delves into the unique search needs of CAG’s diverse passengers and customers, showcasing how graph data structures enhance the accuracy and relevance of AI-generated search results, mitigating the risk of “hallucinations” and improving the overall customer journey.
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

As the digital landscape continually evolves, operating systems play a critical role in shaping user experiences and productivity. The launch of Nitrux Linux 3.5.0 marks a significant milestone, offering a robust alternative to traditional systems such as Windows 11. This article delves into the essence of Nitrux Linux 3.5.0, exploring its unique features, advantages, and how it stands as a compelling choice for both casual users and tech enthusiasts.
zkStudyClub - Reef: Fast Succinct Non-Interactive Zero-Knowledge Regex Proofs

This paper presents Reef, a system for generating publicly verifiable succinct non-interactive zero-knowledge proofs that a committed document matches or does not match a regular expression. We describe applications such as proving the strength of passwords, the provenance of email despite redactions, the validity of oblivious DNS queries, and the existence of mutations in DNA. Reef supports the Perl Compatible Regular Expression syntax, including wildcards, alternation, ranges, capture groups, Kleene star, negations, and lookarounds. Reef introduces a new type of automata, Skipping Alternating Finite Automata (SAFA), that skips irrelevant parts of a document when producing proofs without undermining soundness, and instantiates SAFA with a lookup argument. Our experimental evaluation confirms that Reef can generate proofs for documents with 32M characters; the proofs are small and cheap to verify (under a second).
Paper: https://eprint.iacr.org/2023/1886
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

Neha Bajwa, Vice President of Product Marketing, Neo4j
Join us as we explore breakthrough innovations enabled by interconnected data and AI. Discover firsthand how organizations use relationships in data to uncover contextual insights and solve our most pressing challenges – from optimizing supply chains, detecting fraud, and improving customer experiences to accelerating drug discoveries.
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Join Maher Hanafi, VP of Engineering at Betterworks, in this new session where he'll share a practical framework to transform Gen AI prototypes into impactful products! He'll delve into the complexities of data collection and management, model selection and optimization, and ensuring security, scalability, and responsible use.
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Effective Application Security in Software Delivery lifecycle using Deployment Firewall and DBOM
The modern software delivery process (or the CI/CD process) includes many tools, distributed teams, open-source code, and cloud platforms. Constant focus on speed to release software to market, along with the traditional slow and manual security checks has caused gaps in continuous security as an important piece in the software supply chain. Today organizations feel more susceptible to external and internal cyber threats due to the vast attack surface in their applications supply chain and the lack of end-to-end governance and risk management.
The software team must secure its software delivery process to avoid vulnerability and security breaches. This needs to be achieved with existing tool chains and without extensive rework of the delivery processes. This talk will present strategies and techniques for providing visibility into the true risk of the existing vulnerabilities, preventing the introduction of security issues in the software, resolving vulnerabilities in production environments quickly, and capturing the deployment bill of materials (DBOM).
Speakers:
Bob Boule
Robert Boule is a technology enthusiast with PASSION for technology and making things work along with a knack for helping others understand how things work. He comes with around 20 years of solution engineering experience in application security, software continuous delivery, and SaaS platforms. He is known for his dynamic presentations in CI/CD and application security integrated in software delivery lifecycle.
Gopinath Rebala
Gopinath Rebala is the CTO of OpsMx, where he has overall responsibility for the machine learning and data processing architectures for Secure Software Delivery. Gopi also has a strong connection with our customers, leading design and architecture for strategic implementations. Gopi is a frequent speaker and well-known leader in continuous delivery and integrating security into software delivery.
Microsoft - Power Platform_G.Aspiotis.pdf

Revolutionizing Application Development
with AI-powered low-code, presentation by George Aspiotis, Sr. Partner Development Manager, Microsoft
A tale of scale & speed: How the US Navy is enabling software delivery from l...

Rapid and secure feature delivery is a goal across every application team and every branch of the DoD. The Navy’s DevSecOps platform, Party Barge, has achieved:
- Reduction in onboarding time from 5 weeks to 1 day
- Improved developer experience and productivity through actionable findings and reduction of false positives
- Maintenance of superior security standards and inherent policy enforcement with Authorization to Operate (ATO)
Development teams can ship efficiently and ensure applications are cyber ready for Navy Authorizing Officials (AOs). In this webinar, Sigma Defense and Anchore will give attendees a look behind the scenes and demo secure pipeline automation and security artifacts that speed up application ATO and time to production.
We will cover:
- How to remove silos in DevSecOps
- How to build efficient development pipeline roles and component templates
- How to deliver security artifacts that matter for ATO’s (SBOMs, vulnerability reports, and policy evidence)
- How to streamline operations with automated policy checks on container images
Climate Impact of Software Testing at Nordic Testing Days

My slides at Nordic Testing Days 6.6.2024
Climate impact / sustainability of software testing discussed on the talk. ICT and testing must carry their part of global responsibility to help with the climat warming. We can minimize the carbon footprint but we can also have a carbon handprint, a positive impact on the climate. Quality characteristics can be added with sustainability, and then measured continuously. Test environments can be used less, and in smaller scale and on demand. Test techniques can be used in optimizing or minimizing number of tests. Test automation can be used to speed up testing.
Removing Uninteresting Bytes in Software Fuzzing

Imagine a world where software fuzzing, the process of mutating bytes in test seeds to uncover hidden and erroneous program behaviors, becomes faster and more effective. A lot depends on the initial seeds, which can significantly dictate the trajectory of a fuzzing campaign, particularly in terms of how long it takes to uncover interesting behaviour in your code. We introduce DIAR, a technique designed to speedup fuzzing campaigns by pinpointing and eliminating those uninteresting bytes in the seeds. Picture this: instead of wasting valuable resources on meaningless mutations in large, bloated seeds, DIAR removes the unnecessary bytes, streamlining the entire process.
In this work, we equipped AFL, a popular fuzzer, with DIAR and examined two critical Linux libraries -- Libxml's xmllint, a tool for parsing xml documents, and Binutil's readelf, an essential debugging and security analysis command-line tool used to display detailed information about ELF (Executable and Linkable Format). Our preliminary results show that AFL+DIAR does not only discover new paths more quickly but also achieves higher coverage overall. This work thus showcases how starting with lean and optimized seeds can lead to faster, more comprehensive fuzzing campaigns -- and DIAR helps you find such seeds.
- These are slides of the talk given at IEEE International Conference on Software Testing Verification and Validation Workshop, ICSTW 2022.
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
Video Streaming: Then, Now, and in the Future

In his public lecture, Christian Timmerer provides insights into the fascinating history of video streaming, starting from its humble beginnings before YouTube to the groundbreaking technologies that now dominate platforms like Netflix and ORF ON. Timmerer also presents provocative contributions of his own that have significantly influenced the industry. He concludes by looking at future challenges and invites the audience to join in a discussion.
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

Do you want to learn how to model and simulate an electrical network from scratch in under an hour?
Then welcome to this PowSyBl workshop, hosted by Rte, the French Transmission System Operator (TSO)!
During the webinar, you will discover the PowSyBl ecosystem as well as handle and study an electrical network through an interactive Python notebook.
PowSyBl is an open source project hosted by LF Energy, which offers a comprehensive set of features for electrical grid modelling and simulation. Among other advanced features, PowSyBl provides:
- A fully editable and extendable library for grid component modelling;
- Visualization tools to display your network;
- Grid simulation tools, such as power flows, security analyses (with or without remedial actions) and sensitivity analyses;
The framework is mostly written in Java, with a Python binding so that Python developers can access PowSyBl functionalities as well.
What you will learn during the webinar:
- For beginners: discover PowSyBl's functionalities through a quick general presentation and the notebook, without needing any expert coding skills;
- For advanced developers: master the skills to efficiently apply PowSyBl functionalities to your real-world scenarios.
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
By Design, not by Accident - Agile Venture Bolzano 2024

As presented at the Agile Venture Bolzano, 4.06.2024
Recently uploaded (20)
National Security Agency - NSA mobile device best practices

National Security Agency - NSA mobile device best practices
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!
zkStudyClub - Reef: Fast Succinct Non-Interactive Zero-Knowledge Regex Proofs

zkStudyClub - Reef: Fast Succinct Non-Interactive Zero-Knowledge Regex Proofs
GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024

GraphSummit Singapore | The Art of the Possible with Graph - Q2 2024
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Generative AI Deep Dive: Advancing from Proof of Concept to Production
Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...

Alt. GDG Cloud Southlake #33: Boule & Rebala: Effective AppSec in SDLC using ...
A tale of scale & speed: How the US Navy is enabling software delivery from l...

A tale of scale & speed: How the US Navy is enabling software delivery from l...
Climate Impact of Software Testing at Nordic Testing Days

Climate Impact of Software Testing at Nordic Testing Days
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...

LF Energy Webinar: Electrical Grid Modelling and Simulation Through PowSyBl -...
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
By Design, not by Accident - Agile Venture Bolzano 2024

By Design, not by Accident - Agile Venture Bolzano 2024
How to Recover Corrupted Word File
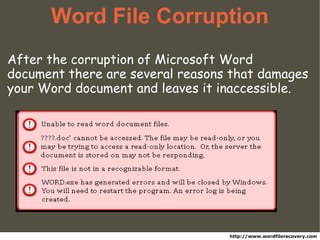
- 1. Word File Corruption After the corruption of Microsoft Word document there are several reasons that damages your Word document and leaves it inaccessible. http://www.wordfilerecovery.com
- 2. Reason of File Corruption * Files and folders are relocated or missing * Open file error (such as invalid file format) * Files are renamed with ASCII characters * File permissions and attributes are modified * Computer frequently freeze and hang without showing any reasons These are Few Common Symptoms of File Corruption:
- 3. Some Common Error • MS Word document displays an error and does not permit to open the file.
- 4. Some Common Error • You can open your Word document, but displays errors or malfunctions.
- 5. Methods to Repair MS Word File 1. Open and Repair 2. Save file in another format 3. Open the file using OpenOffice 4. Third Party Tool
- 6. ` Open and Repair Microsoft Word provides an integrated Open And Repair tool, which can use to force Word to attempt a recovery. Try to Open And Repair integrated tool, use following steps: • Open Word application > Select File > Open > Choose the corrupted file (but don’t open it yet). • Thereafter, Click on “Open” drop-down arrow button • Change the option to “Open and Repair”, then click on it.
- 7. Save File in Another Format • Enter the file name and click on the Save to save the document. • After completing the previous steps, try to opening the document in Word format • Go to File Menu > Save As • In the Save as type drop-down menu choose another file format like RTF, XML, Web Pages, etc.
- 8. Open File In OpenOffice You can install openoffice application on your PC • Open Writer • Files > Open corrupt files • Start Recovery Process
- 9. Third Party Tool It is the only software of its kind that recovers all the elements in the file and the important details. Get the best solution in quality, reliability and speed in the last few years.
- 10. Kernel Recovery for Word
- 11. Why to rely on Kernel Recovery for Word? * Kernel Recovery for Word tool to recover all data from corrupted document. It recovers instantly texts, images, fonts, tables, styles, page and paragraph formats, tables of contents, links and graphs. * The recovery is practically instantaneous using Kernel Recovery for Word. * Kernel Recovery for Word is the easiest software to use for recovering Word documents, so does not require technical skills. Our software will guide you through the recovery process until you have your restored document open in front of you. * Non-Western characters - Kernel Recovery for Word performs a correct recovery of non-Western characters. It recovers the Unicode in every case and in every part of the file.
- 12. ` Why Kernel Recovery for Word is a Best Solution? * Confidentiality - The entire recovery process is performed safely in your PCs. * Free trial Version - Before you purchase the program you can evaluate without any cost. * 30 Days Money-back guarantee * Qualified Support - At any point of time (before or after) purchase of product, better qualified staff is available to provide customer support. * Virus-free and spy-ware free.
- 13. ` How to Recover Your Damage Files? We have put a lot of effort into creating an automated system that allows you to recover your data in only few clicks. 1. Install: Download and install the free demo of the program you need. 2. Recover: Select and recover your file. 3. Check: Check the recovery results in the program viewer. 4. Purchase: Click on the button to get the activation code. It will take you to the purchase page of our website. You will immediately receive an activation code by email. 5. Save: Insert your activation code in the program and finish the recovery. Save the recovered file at the desired and safe location in your computer.
- 14. ` Process to Recover Lost Word Document 1. Install & Run Kernel Recovery for Word Software on PC
- 15. ` Process to Recover Lost Word Document 1. Select the Repair... item in the Add File(s) menu.
- 16. ` Process to Recover Lost Word Document 1. Select the document corrupted and press "Repair" button. 2. Wait until the file processing is completed.
- 17. ` Process to Recover Lost Word Document 1. Save the recovered file, by assigning it a new name. By default, Recovery for Word adds “Recovered” to the file name, i.e. “Corrupted document.DOC” will be saved as “Recovered Corrupted document.RTF”.
- 18. ` How to uninstall this software? There are two options to un-install the Kernel for Word software : 1. From Windows Start menu o Start > All Programs > Kernel for Word > Uninstall Kernel for Word o Warnning message > Click "Yes" button and then Click on "OK" button. Finally the software successfully gets uninstalled from PC.
- 19. ` How to Uninstall the Software? 1. From Control Panel o Start > Control Panel > Appears Control Panel window o Double-click the Add or Remove Programs > Show list of the programs installed on your PC o Select Kernel for Word > click Remove button o Click “Yes” button after warning message appear> Click “Ok” button and the software will successfully get uninstalled from PC.
- 20. ` How to Download Word Recovery Tool Download Free trial Version http://www.repairdocfile.com/download-free.html
- 21. ` Awards
- 22. ` Contact
- 23. ` Tips to Protect your MS Word documents How can you protect * Use and maintain anti-virus software * Use caution with email attachments * Be wary of downloadable files on websites * Keep software up to date * Check email and your web browser security at fix periodical intervals
- 24. ` Thanks
