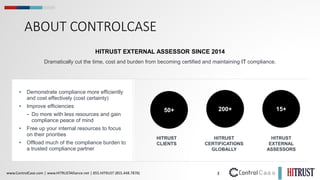
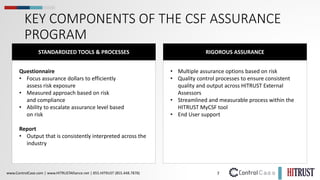
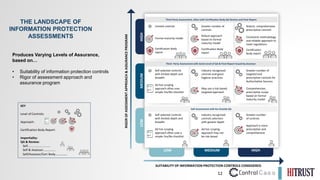
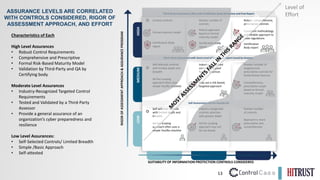
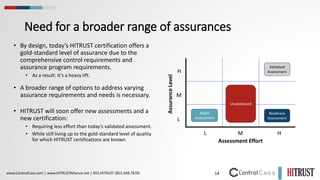
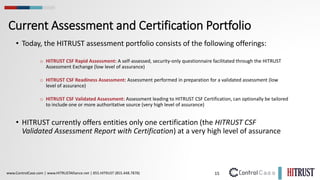
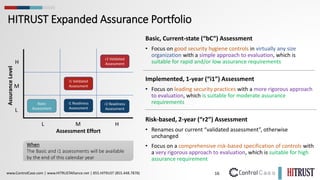
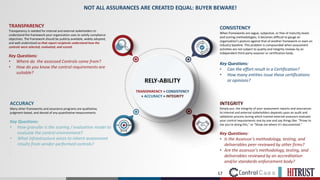
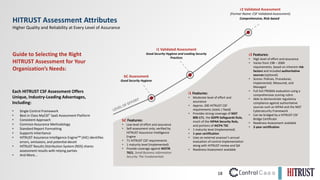
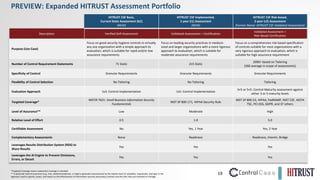
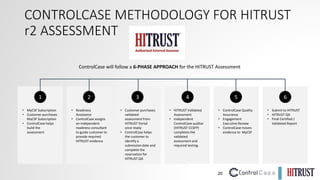
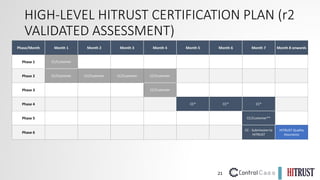
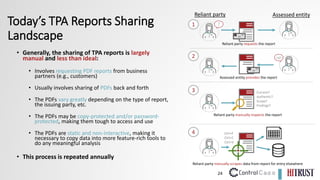
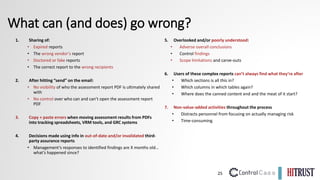
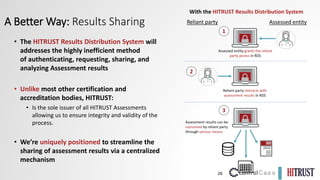
The document outlines the HITRUST framework designed to help organizations safeguard sensitive data while minimizing compliance burden through a certifiable process. It details various assessment and certification options, including the HITRUST CSF and its domains, aimed at establishing trust and efficiency in information security risk management. Additionally, it discusses the collaborative role of ControlCase as an external assessor in facilitating these compliance efforts.