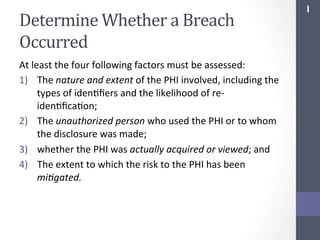
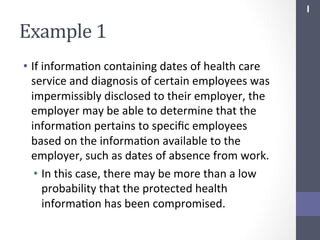
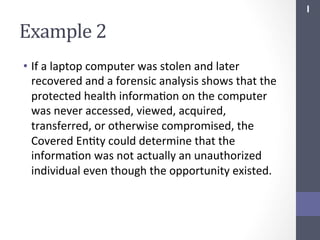
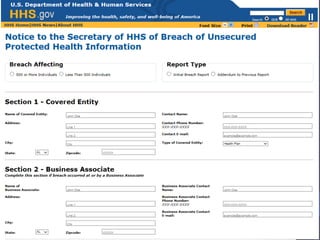
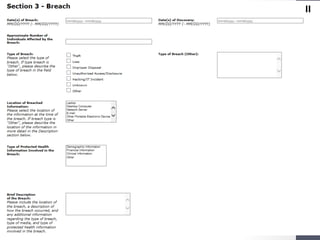
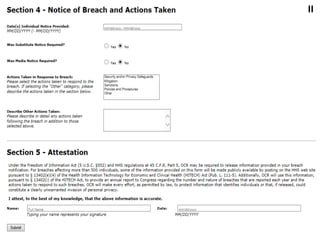
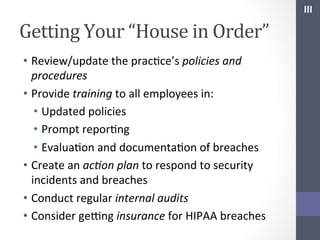
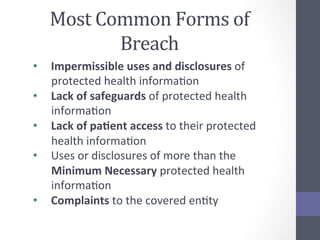
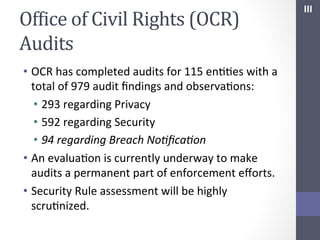
The document provides guidance on handling HIPAA breaches, outlining obligations such as breach notification to affected individuals, the media, and the Secretary of Health and Human Services. It highlights the importance of conducting a risk assessment to determine whether a breach has occurred and discusses training and policies that organizations should implement to ensure compliance. The document emphasizes the necessity of credit monitoring services and cyber insurance to mitigate risks associated with breaches.