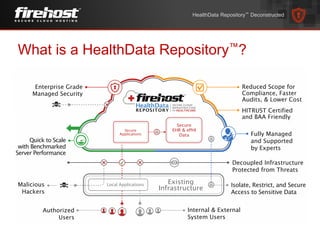
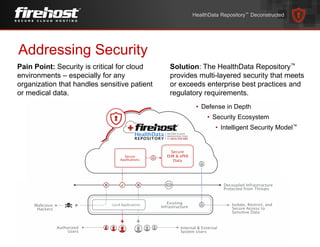
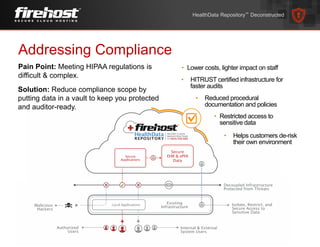
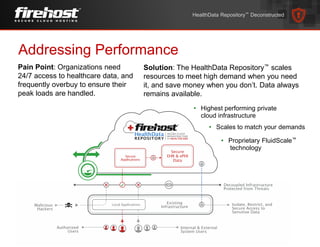
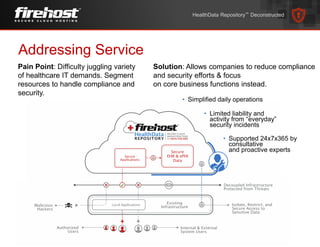
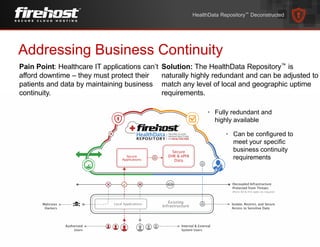
Kurt Hagerman gave a presentation on the HealthData RepositoryTM and how it addresses key challenges for healthcare organizations. It provides security through multi-layered defenses that meet regulatory requirements. It simplifies compliance through a HITRUST certified infrastructure. It ensures constant high performance and scalability of resources through proprietary technology. It also offers 24/7 support and business continuity through fully redundant infrastructure that can be configured to meet any uptime needs.