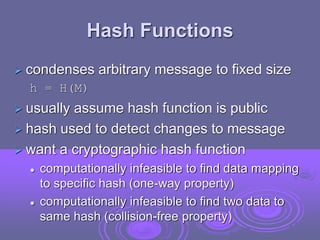
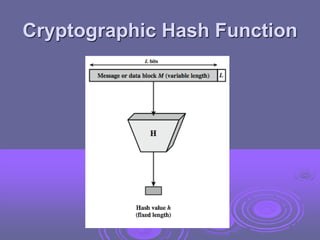
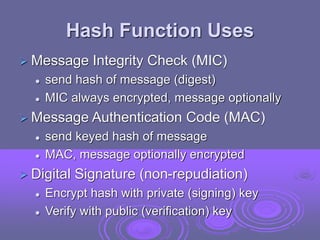
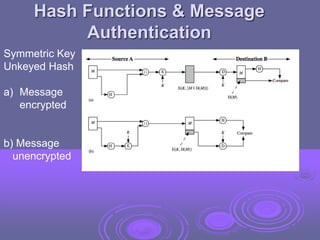
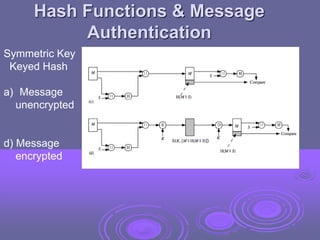
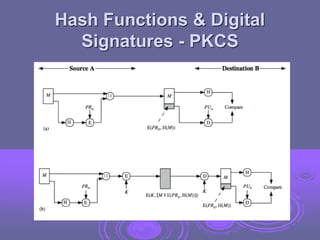
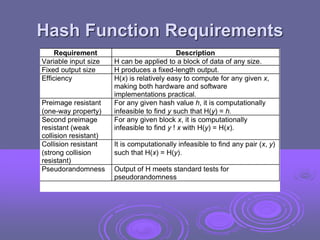
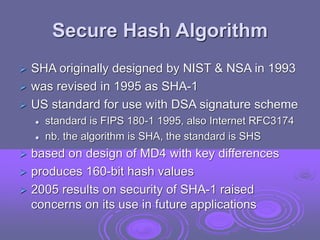
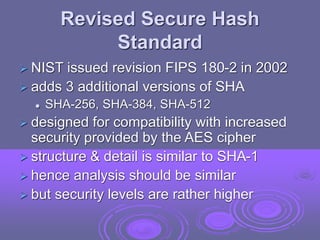
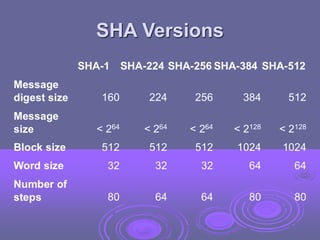
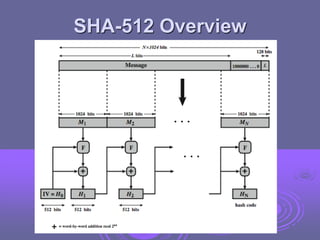
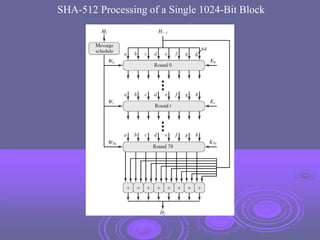
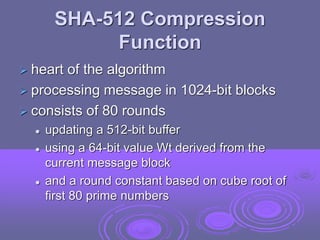
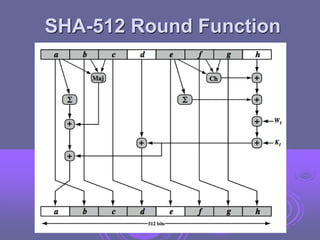
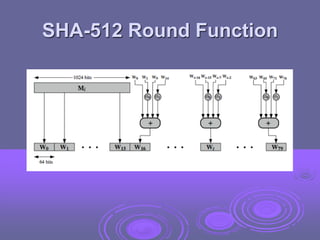
The document discusses cryptographic hash functions, focusing on their properties, uses, and security requirements. It highlights the significance of SHA-1 and its successors, including SHA-256, SHA-384, and SHA-512, emphasizing their role in message integrity, authentication, and digital signatures. Additionally, it outlines issues related to hash functions, such as collision resistance and the importance of secure hash algorithms in modern applications.