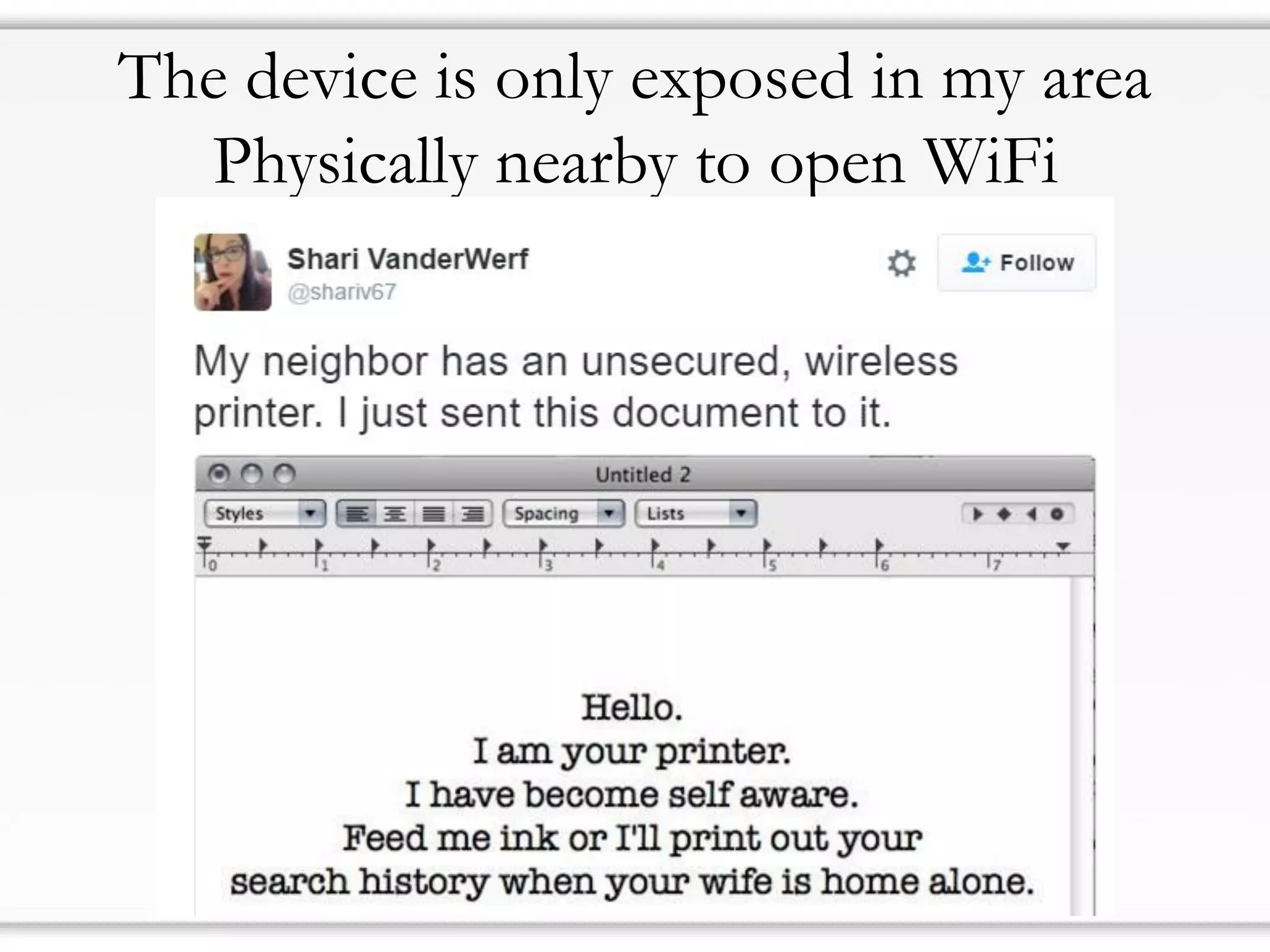
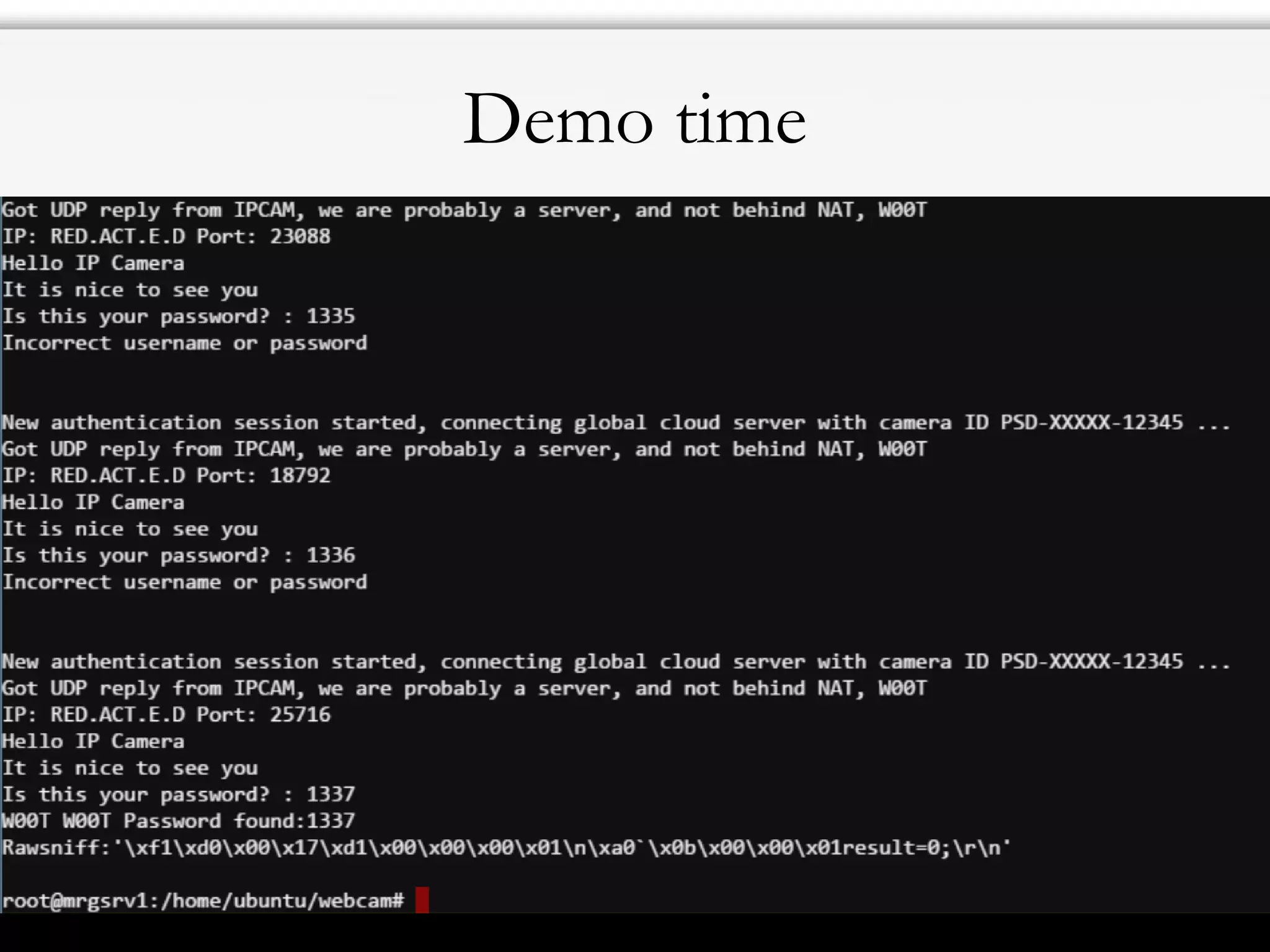
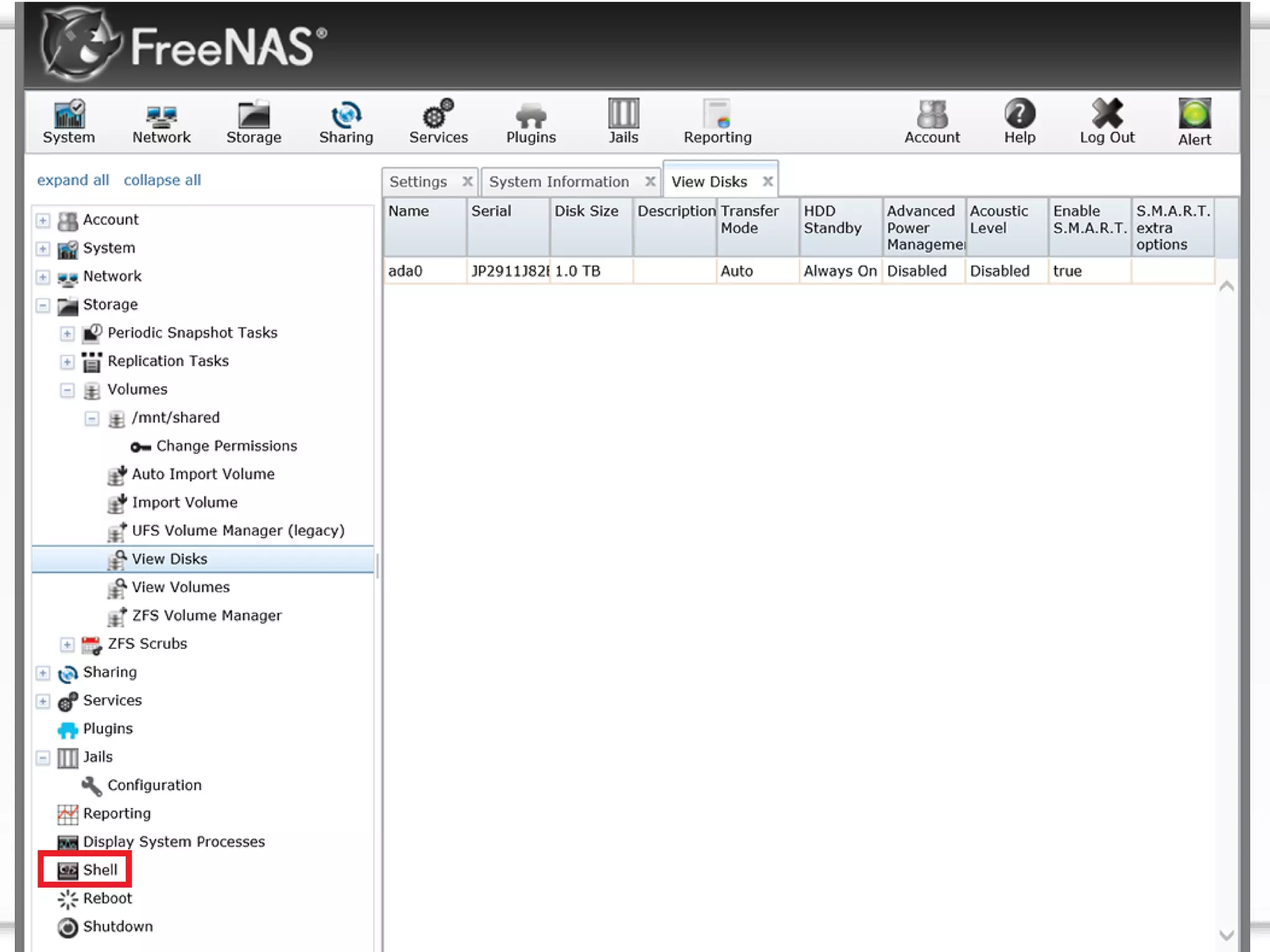
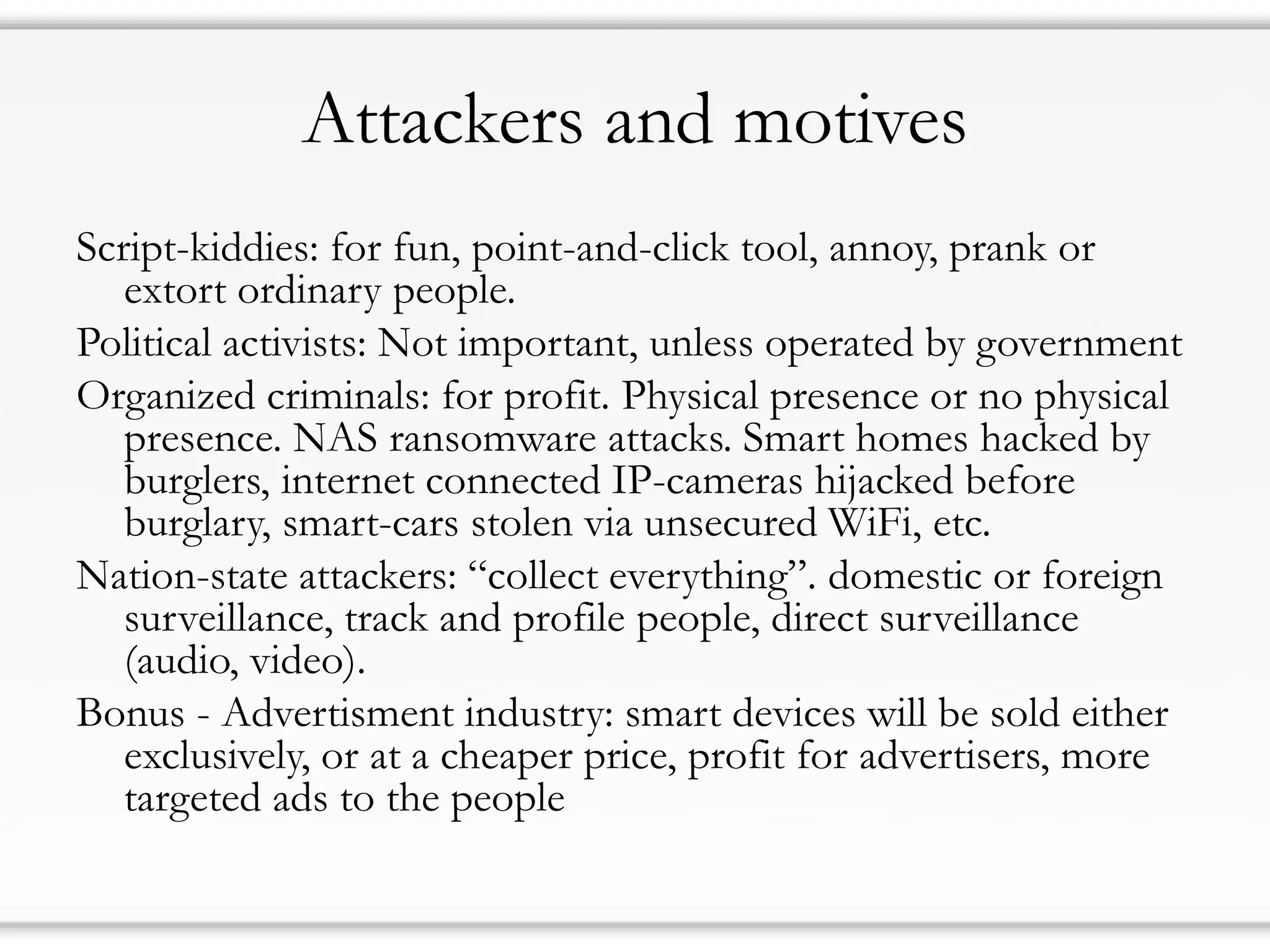
1) IoT security is a major issue as many devices have poor security and will never receive patches. This leaves them vulnerable to attacks over the internet or through home networks.
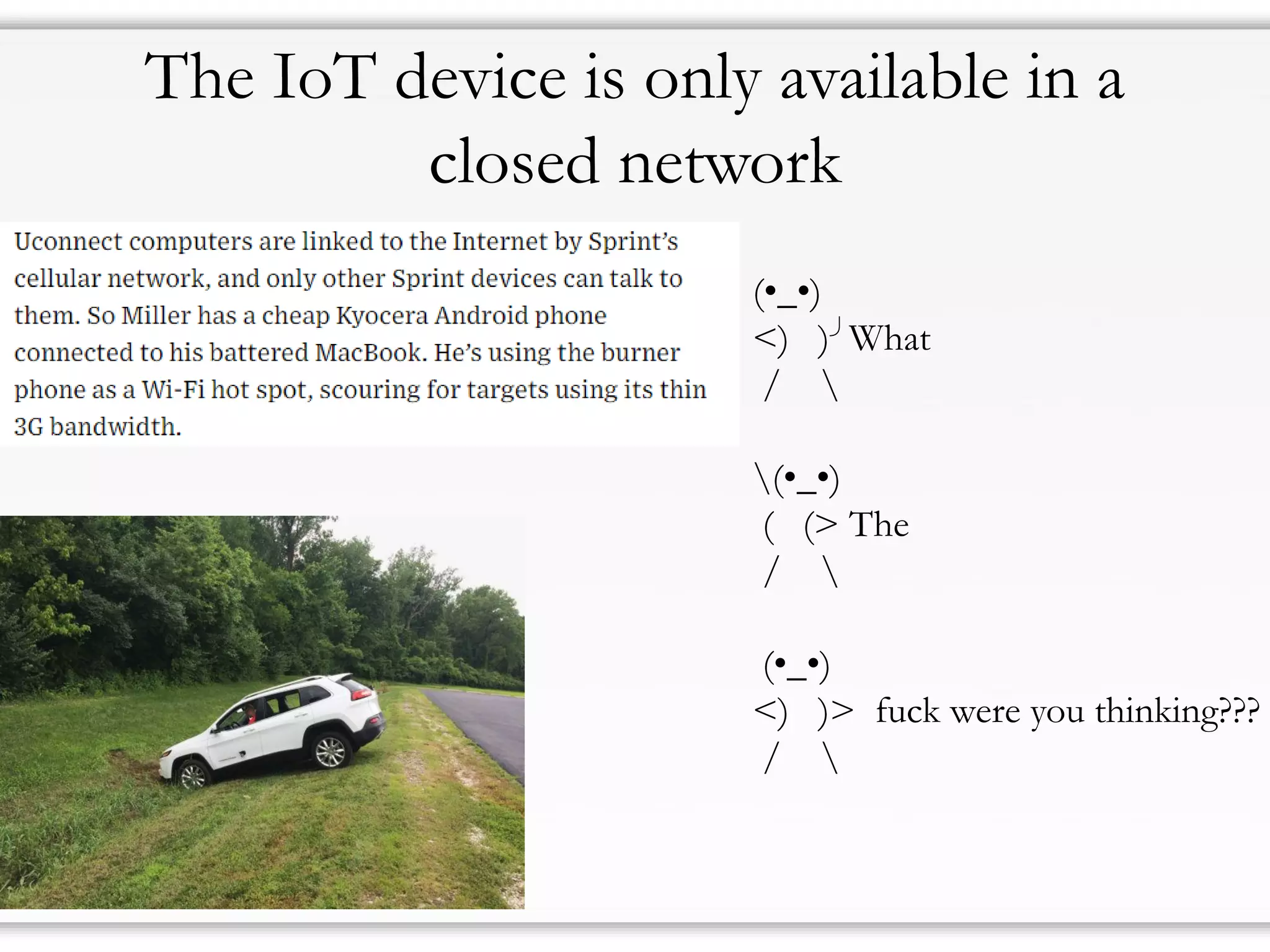
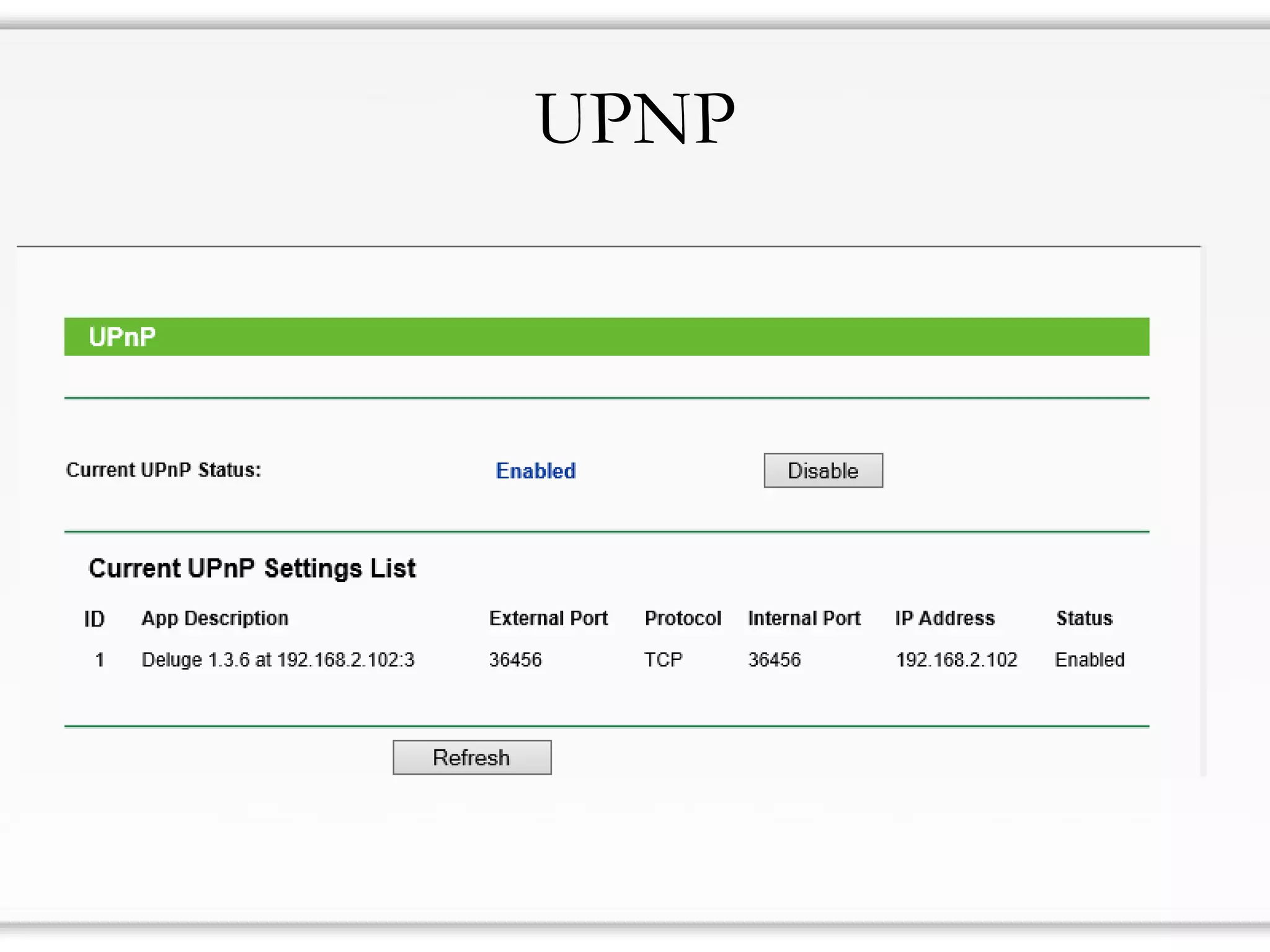
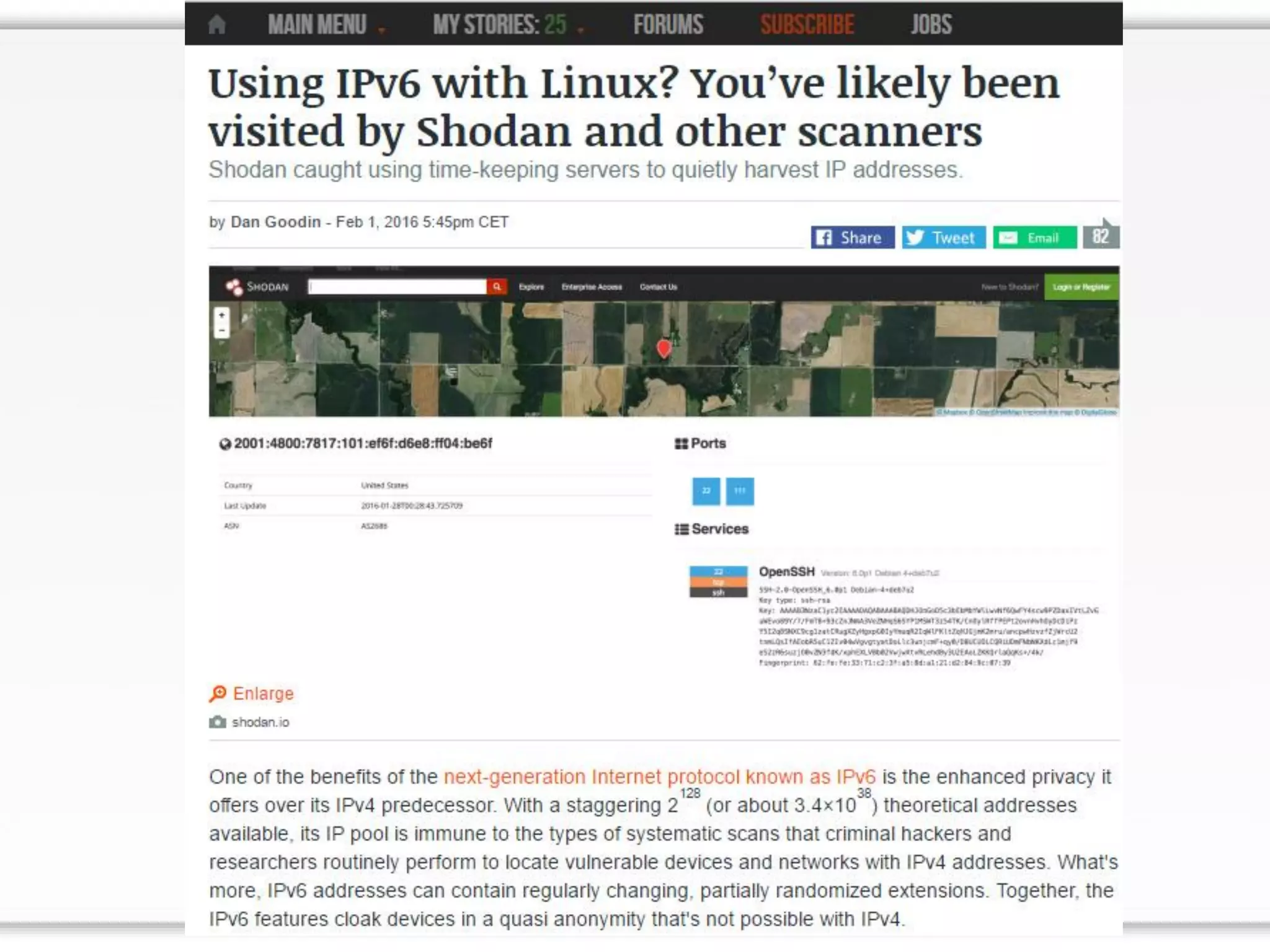
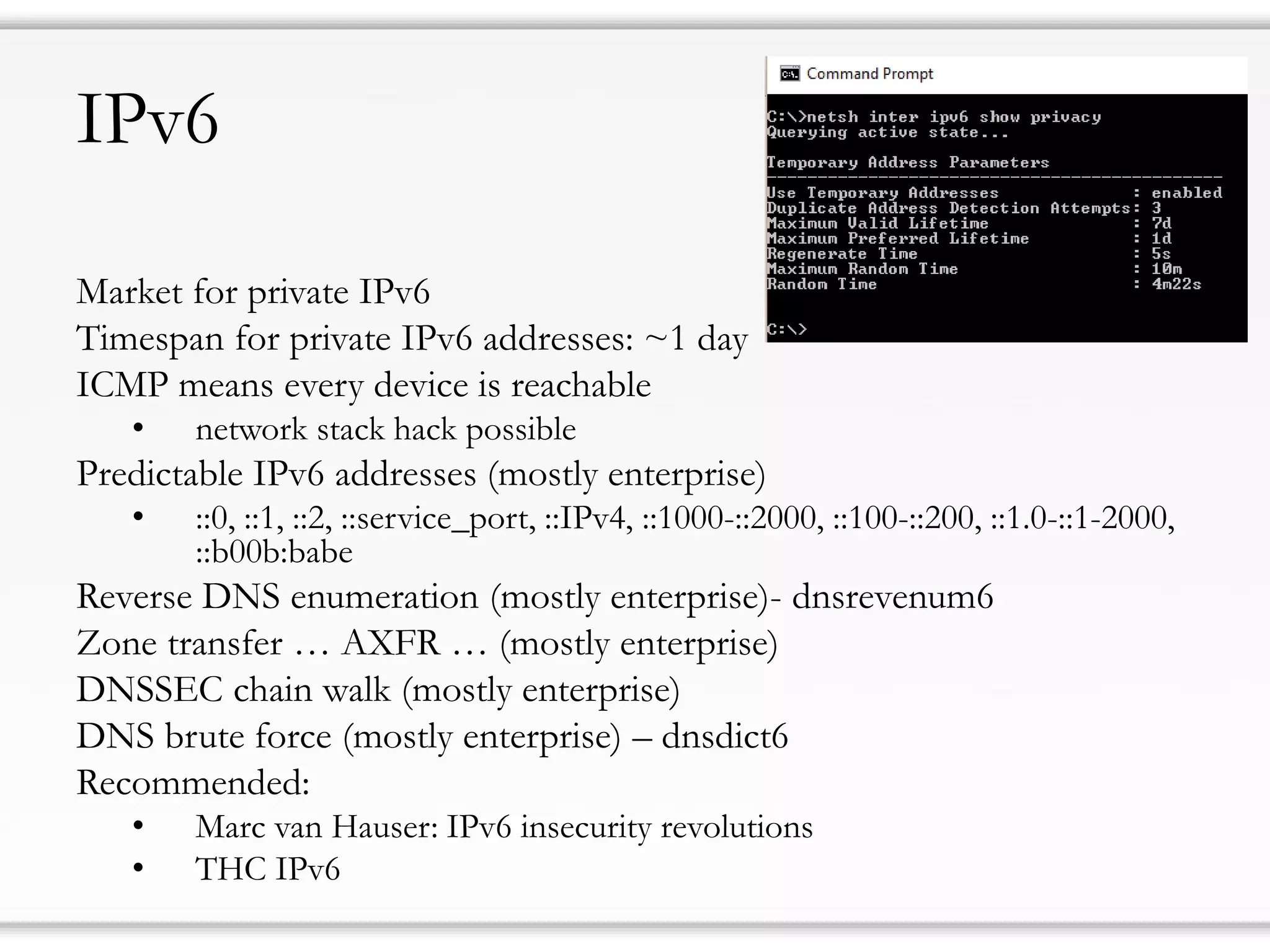
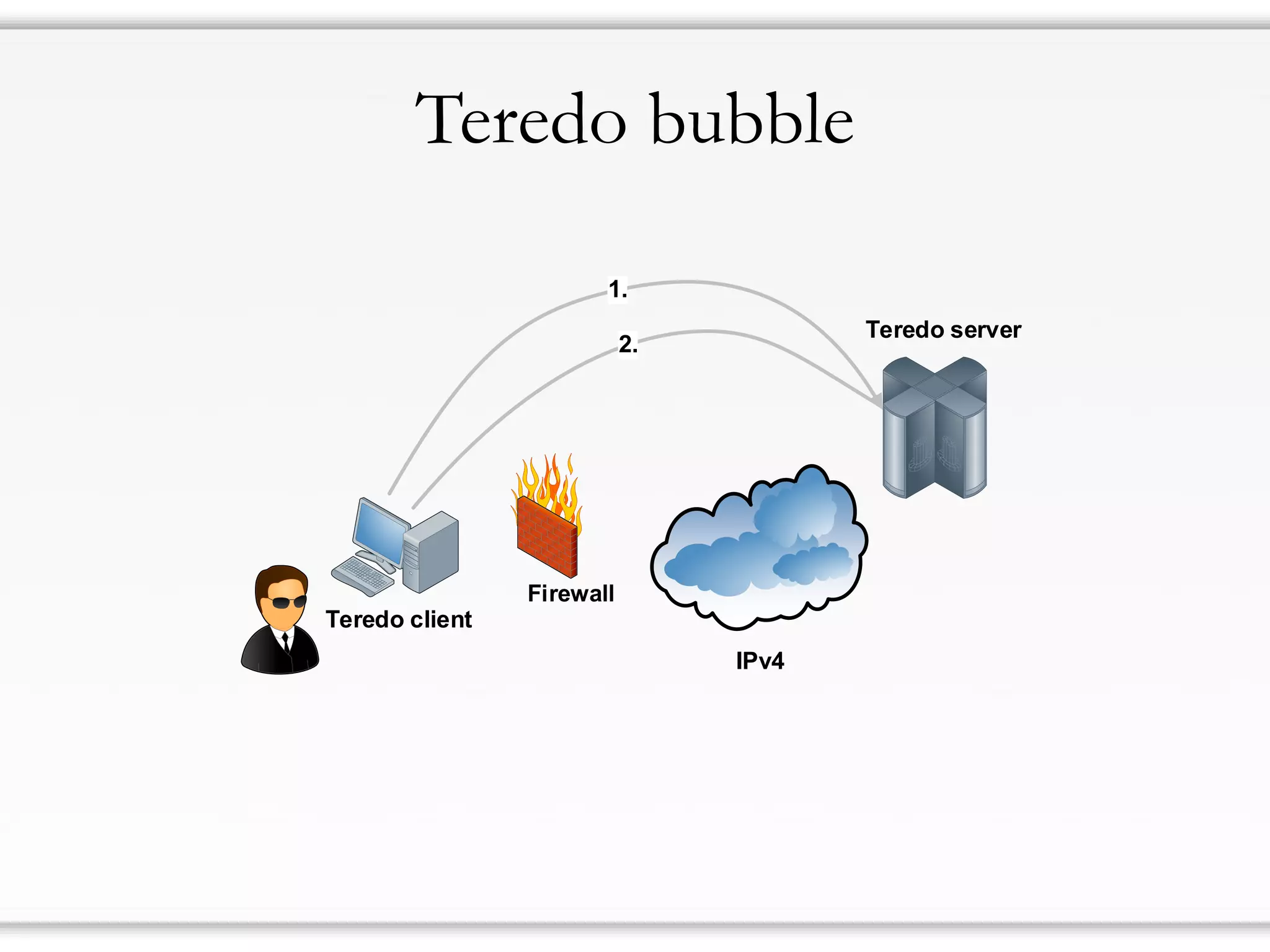
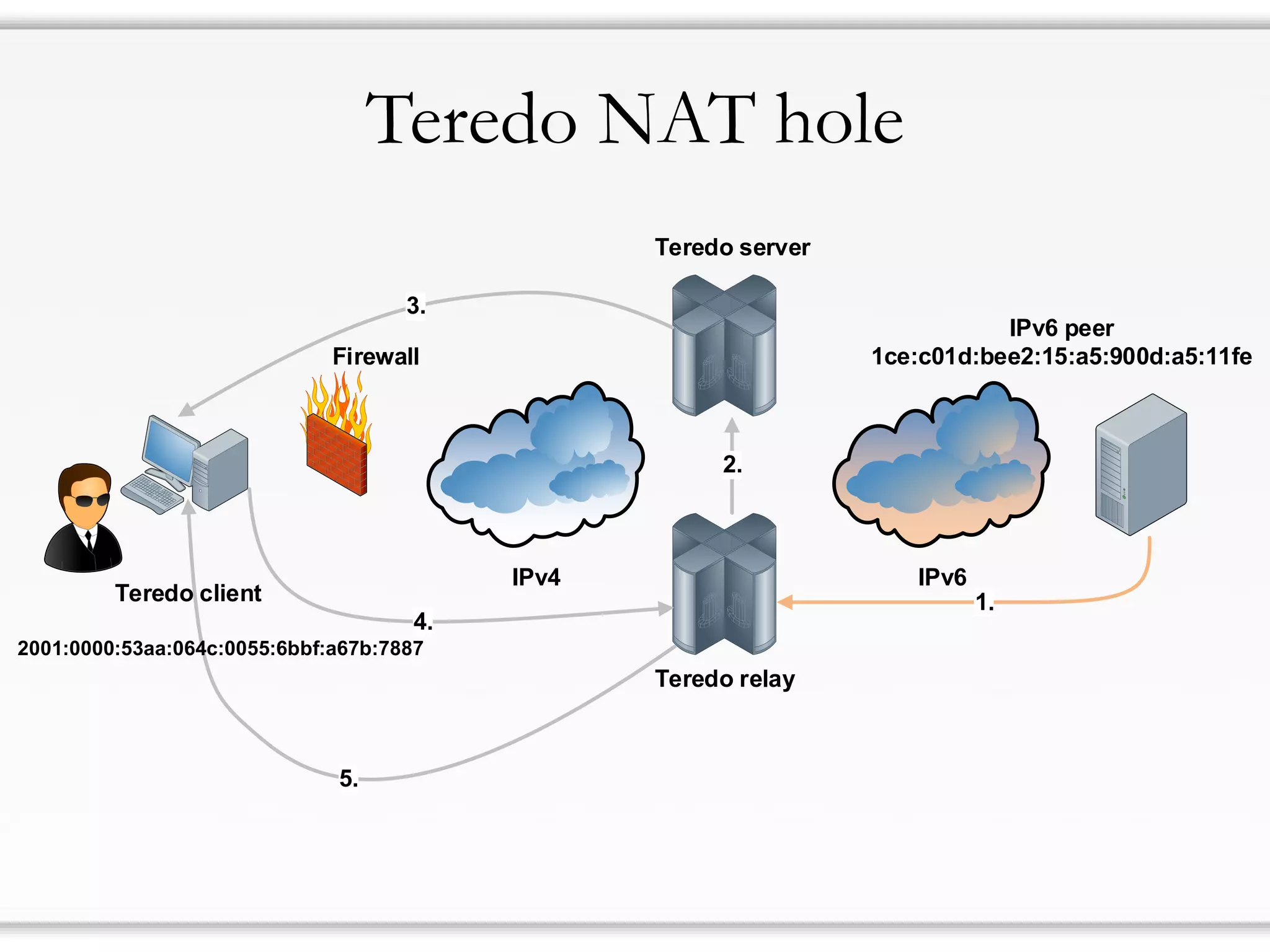
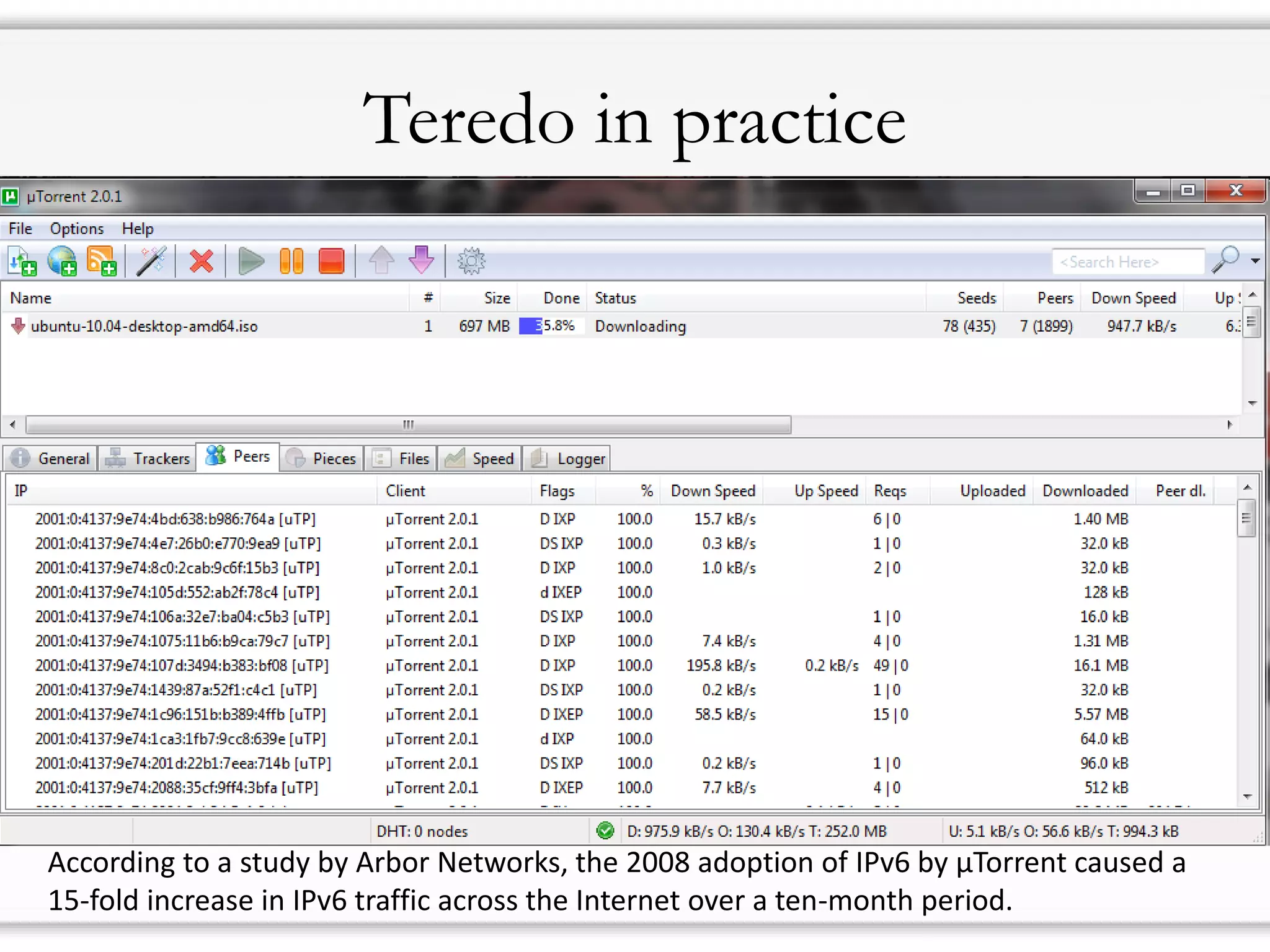
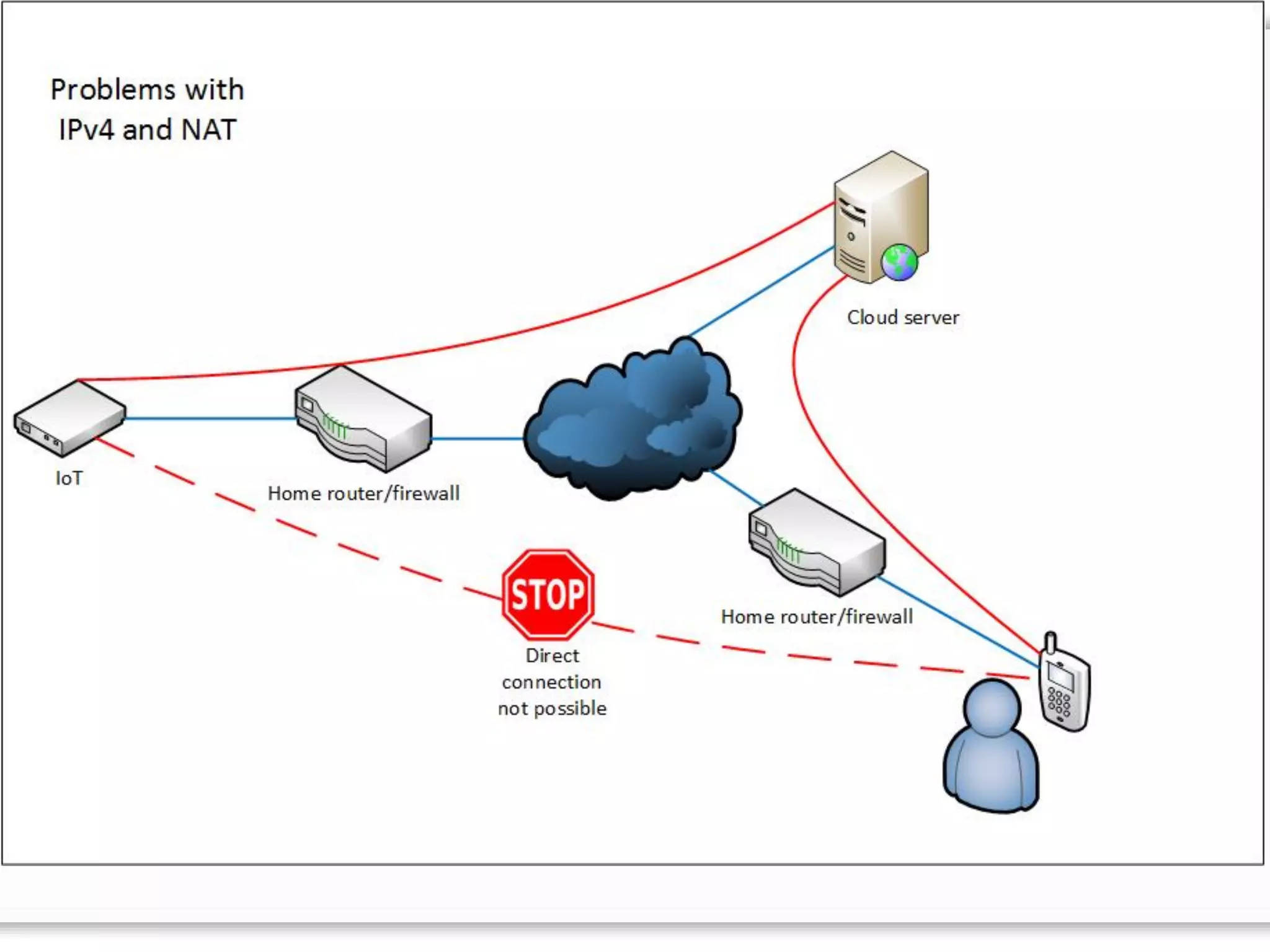
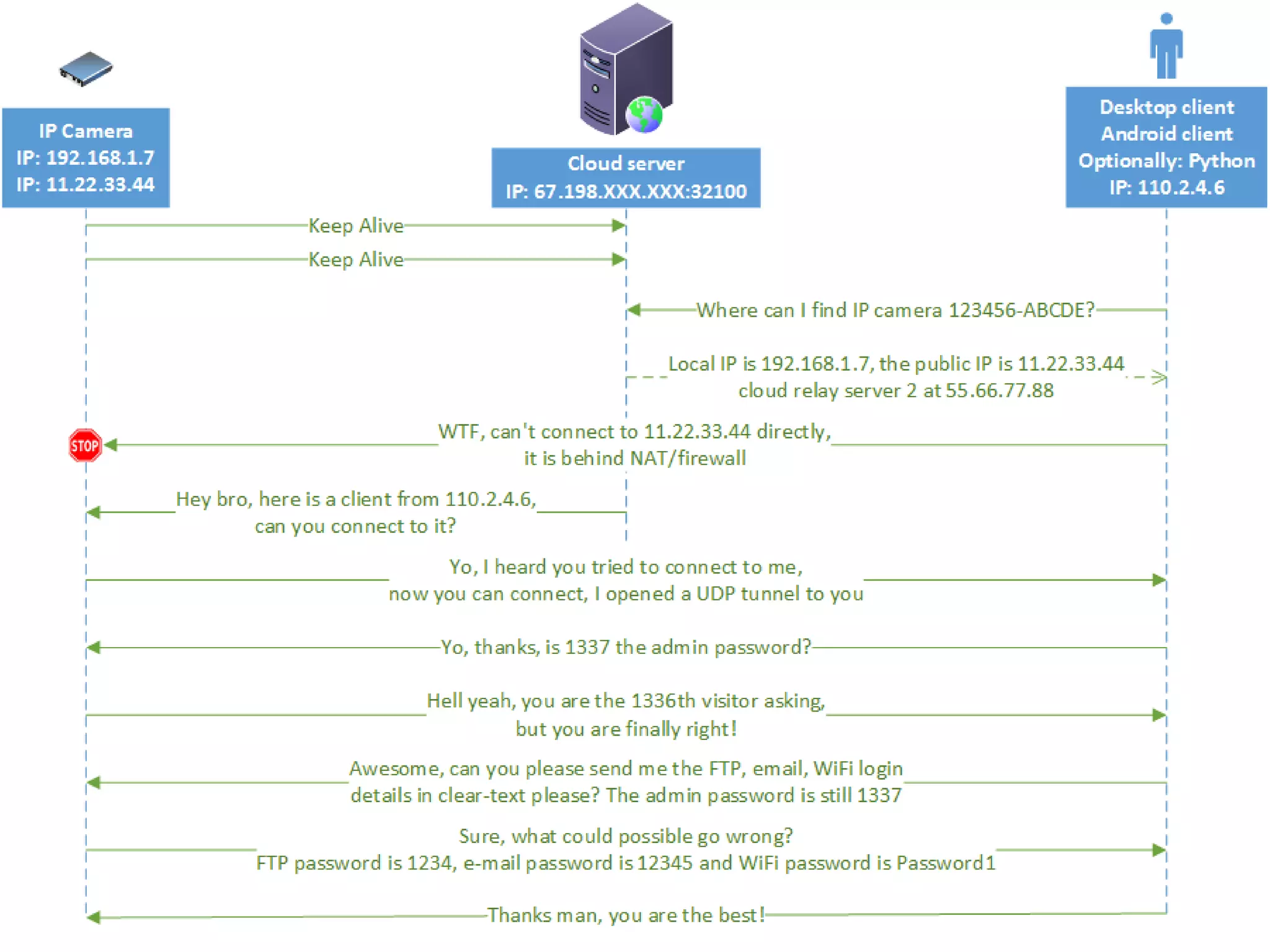
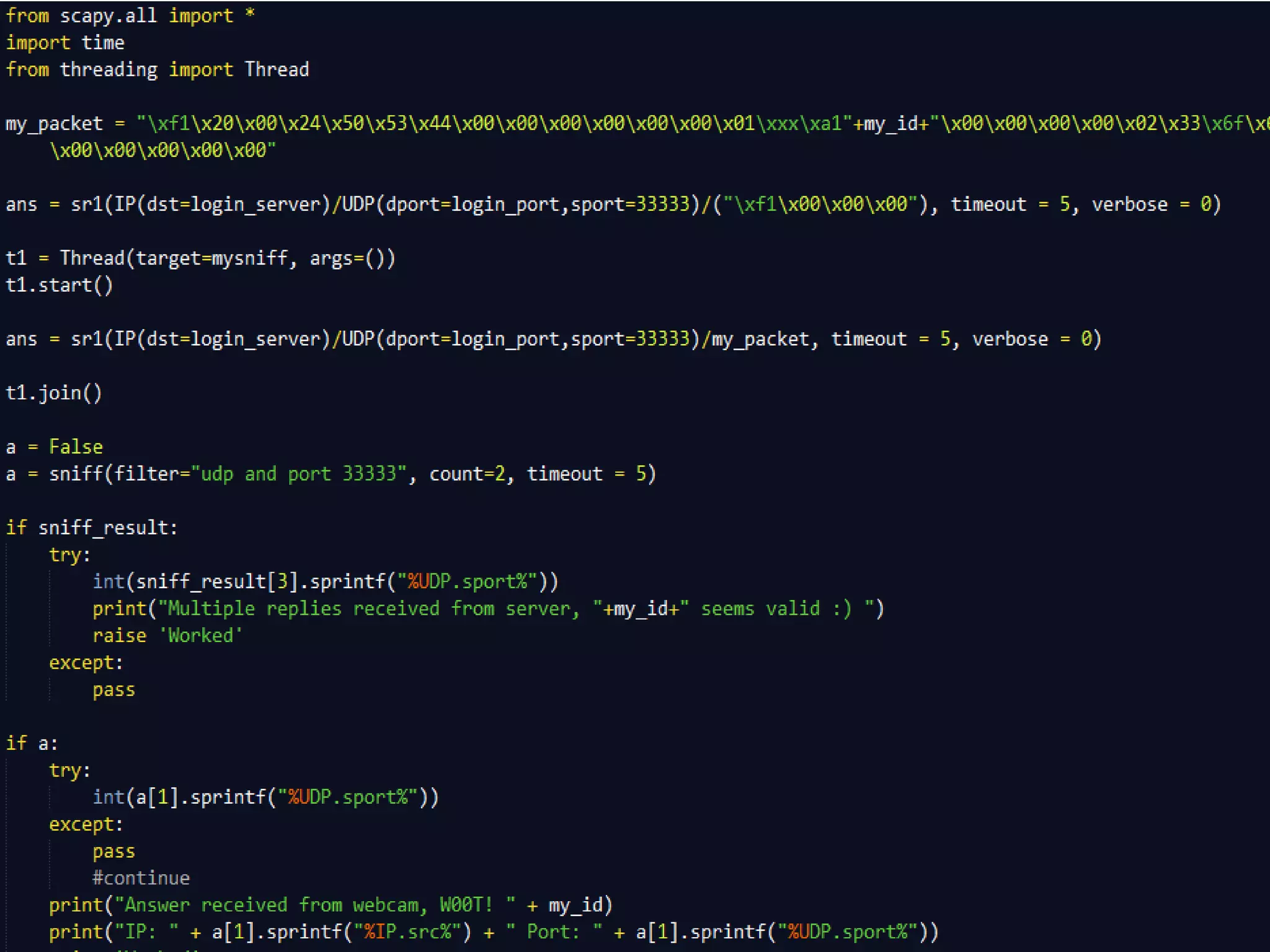
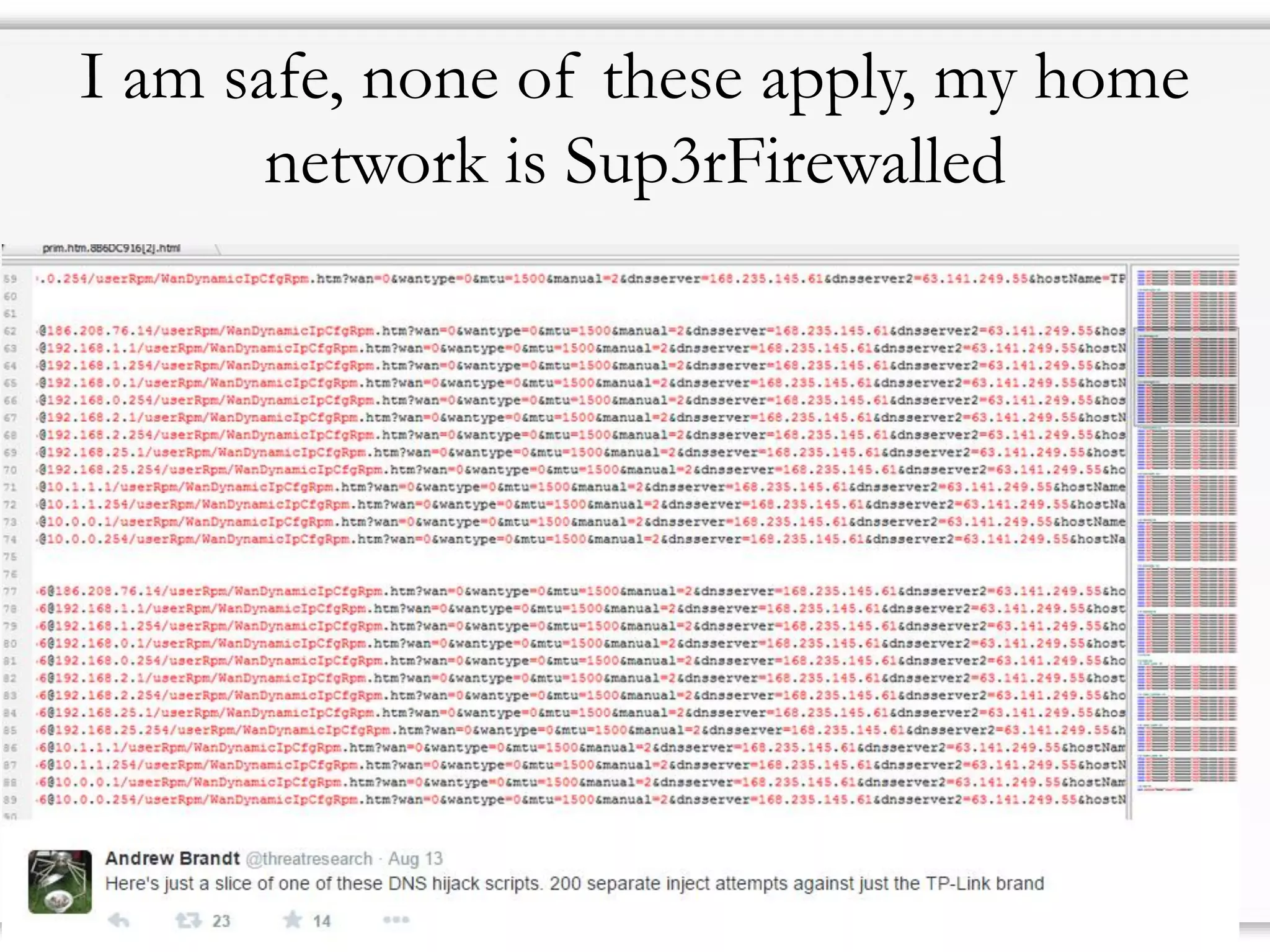
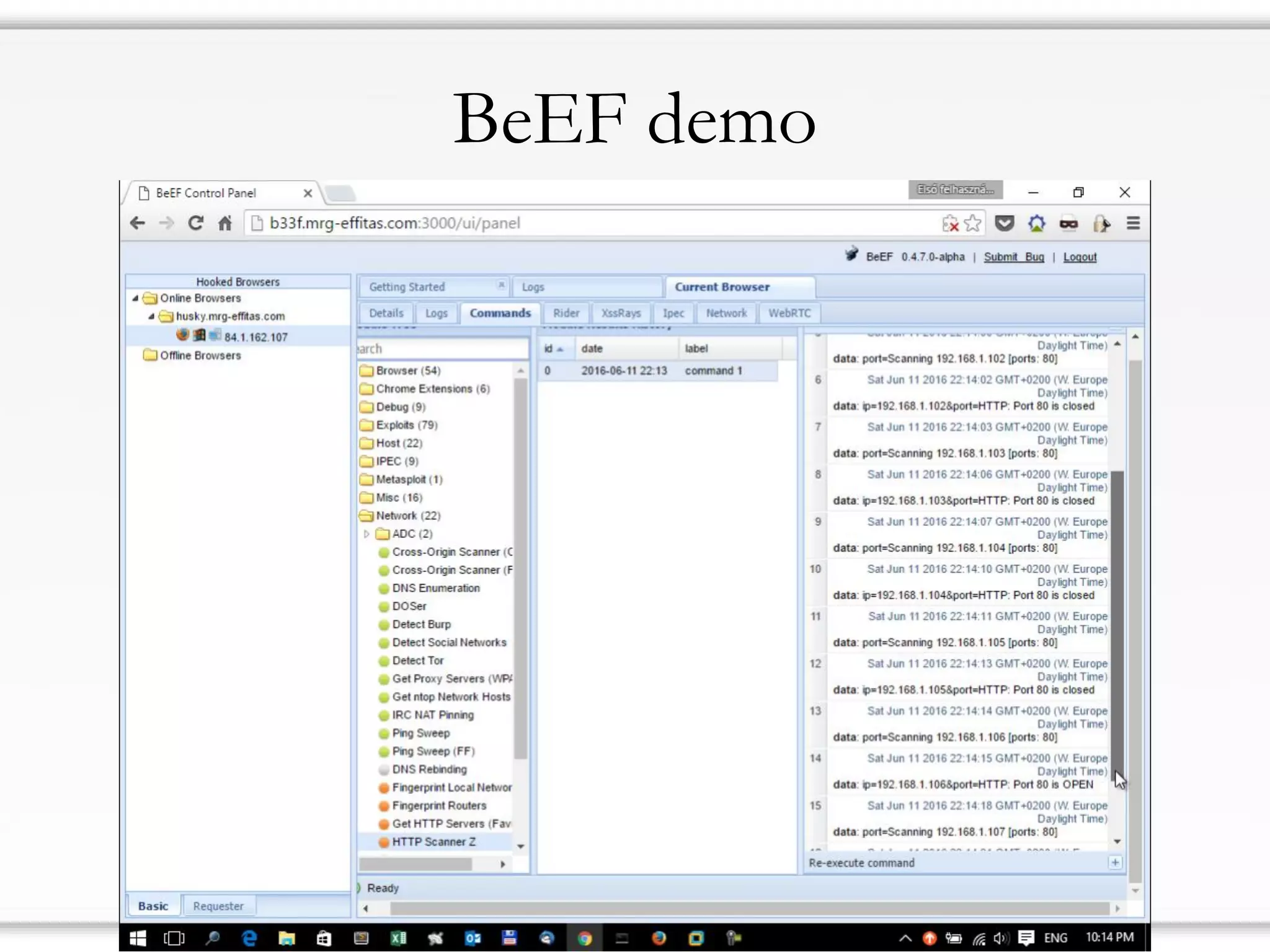
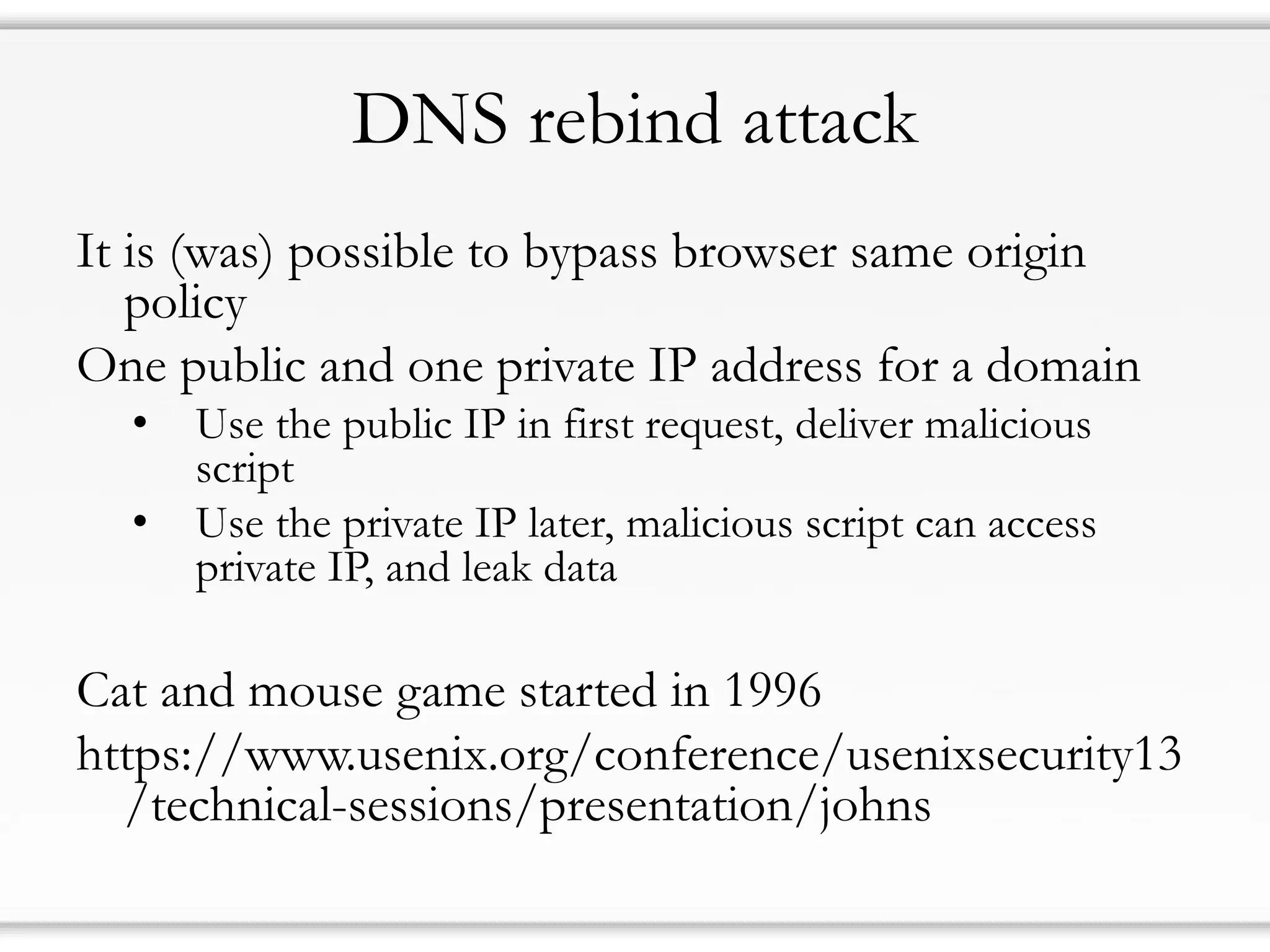
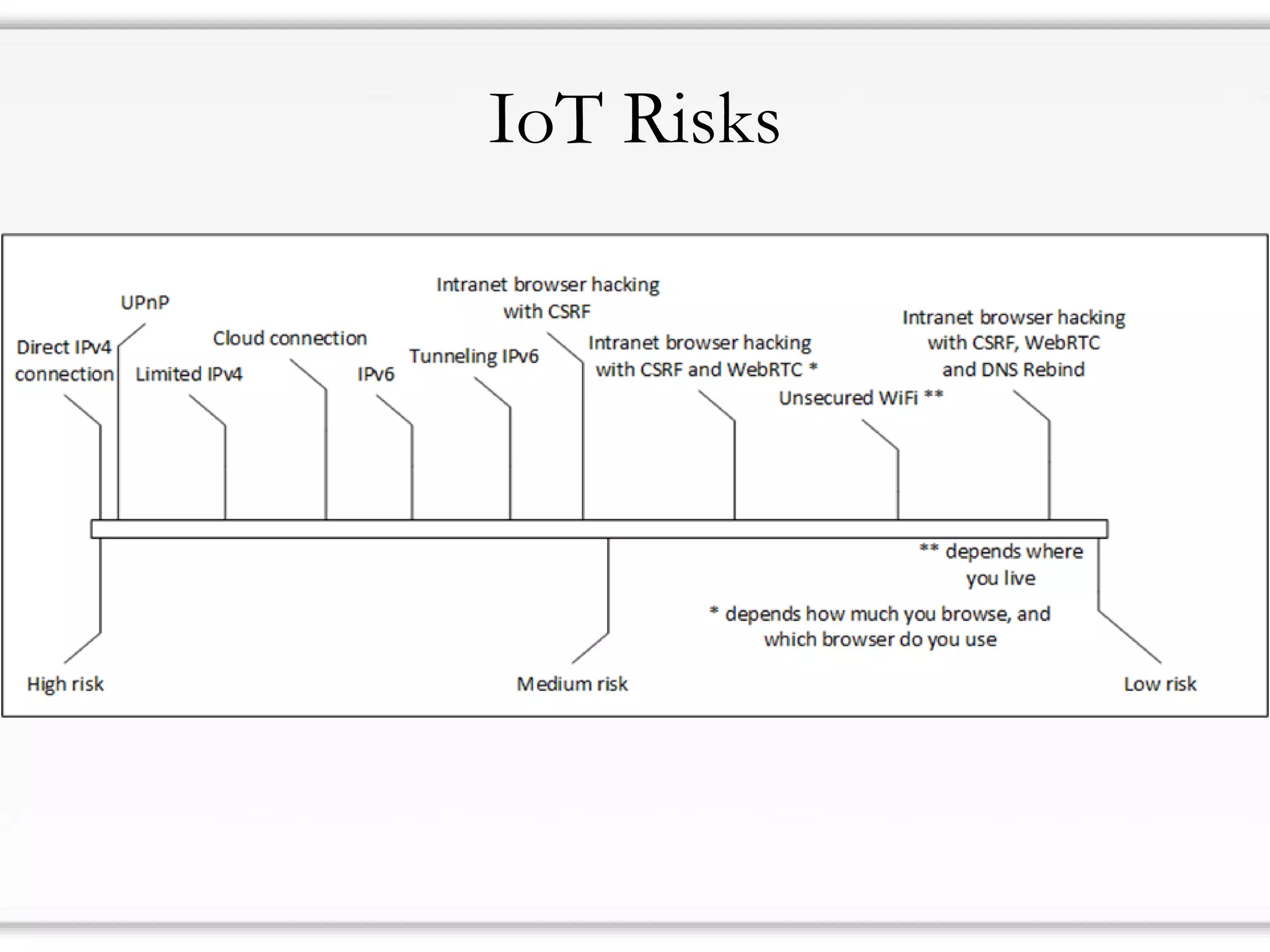
2) There are many risks even for devices that are behind routers or firewalls due to issues like UPnP, IPv6, cloud connections, and protocol tunneling that can bypass network protections.
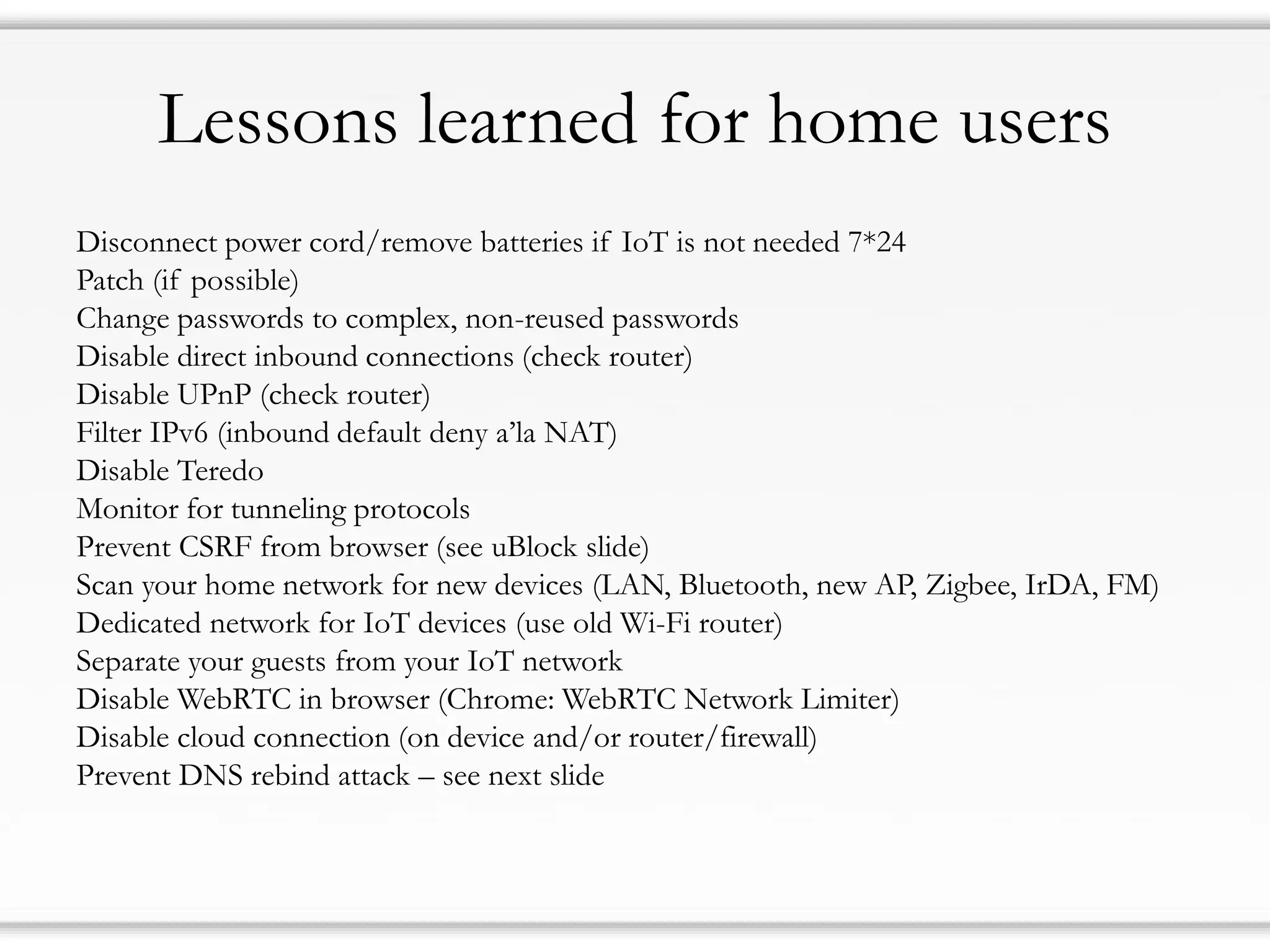
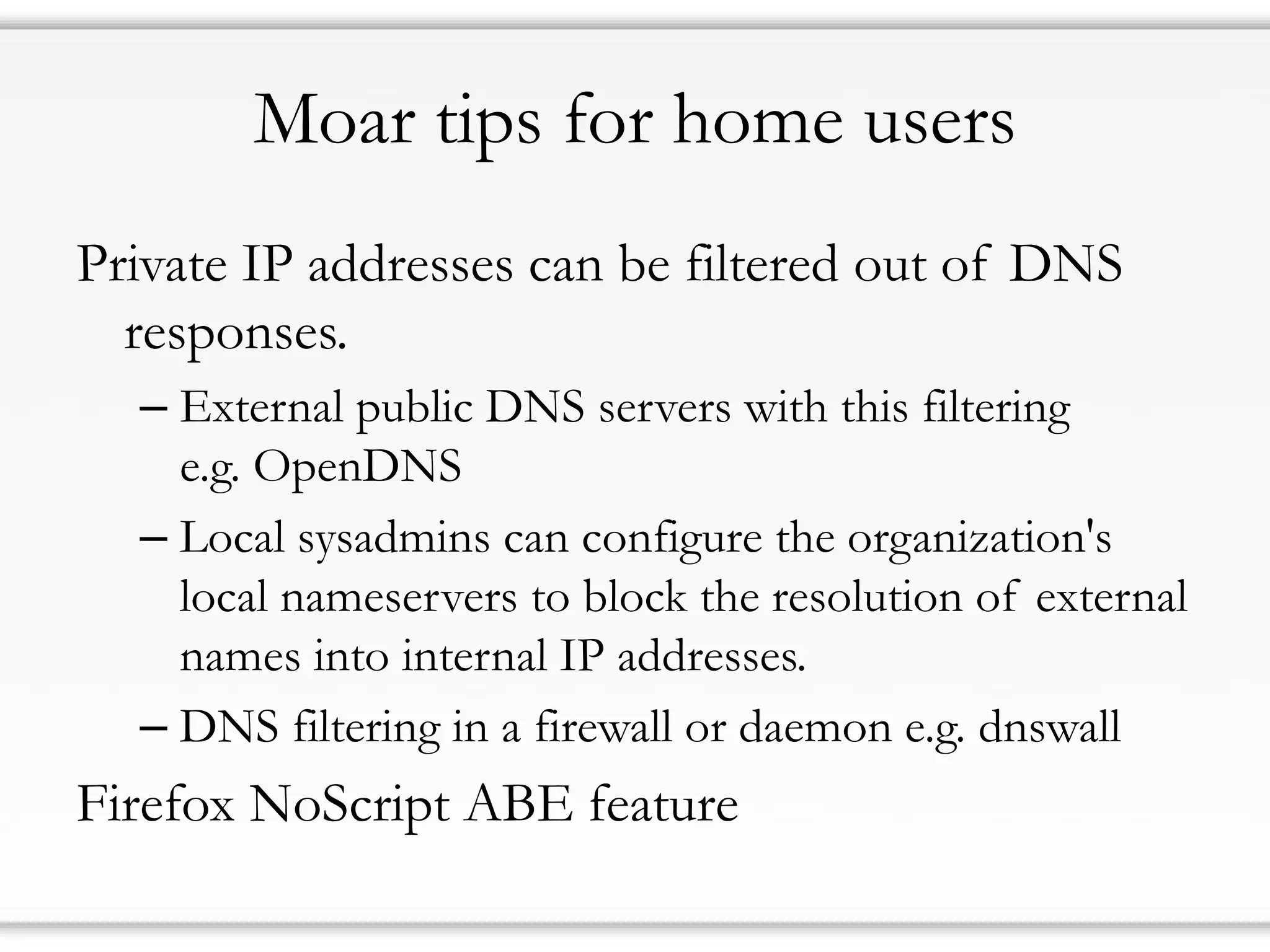
3) Home users should take steps like disconnecting devices when not in use, changing passwords, filtering incoming connections, and monitoring their network to improve their security, but there are no complete solutions given flaws in IoT design and updates.