GitHub Bug Bounty Experience provides an overview of the author's experience participating in GitHub's bug bounty program. The summary includes 3 key points:
1) The author is an information security engineer who participated in GitHub's bug bounty program to find vulnerabilities for monetary rewards, as well as for fun and the challenge.
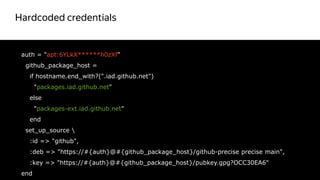
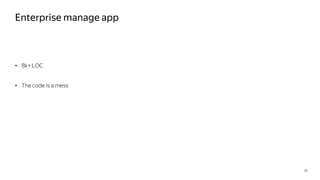
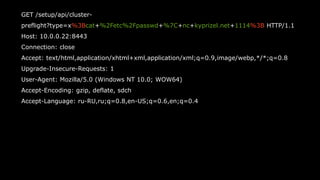
2) Through analyzing GitHub Enterprise's virtual machine images and Ruby applications, the author discovered several security issues like hardcoded credentials, lack of input validation, and potential for command injection.
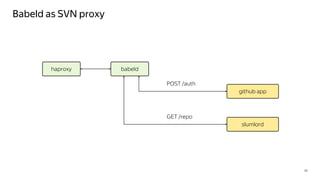
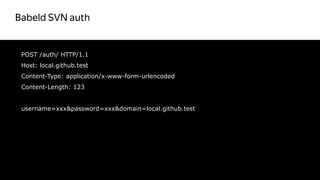
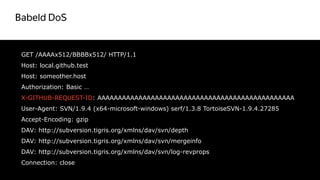
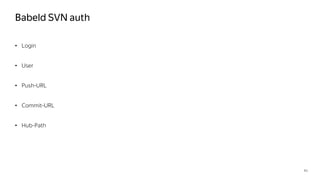
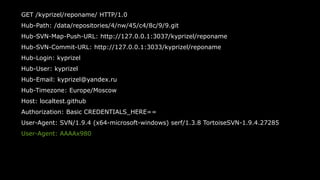
3) By probing the Babeld SVN proxy service, the author found ways to bypass authentication and potentially cause denial of service through excessive requests.













![Blackbox -> Whitebox
17
require "ruby_concealer.so“
_ruby_concealer__
"xx9CrxCCMOx830x18x00xE0x17xC4x96x8Fx96x0Fx85mxCERx92xC5,Frx
17xB3xF81x0F"tx8EbexA1#x1Ex86']2x0F^<x18xBDxF8xDBxF5xF9x01xCF
rxA6xA8xB2x1FfGxC8%1xDEJ0XxC1xF4@xCC}bxAAxDFx06x8Ax92x13axB
8xF1xxD2xCELJxE9@x9CxC7xB1xCDxF6xBEK%
xEFx86x81Ux13v!qbxF3x15xD1xDDfPmxB2xD0xDC'wx01"x16vxACxFFcxB
Dx14xF0xF5xF1"xE6x90'2|xEEx11xF5<xE8xC0xCCexBCxDAUQx99x19x
03x15x81O.xADx16x87xE8pxB4xF8xF4NxABxFBx1Ex0Evx8BNxE5xD9x9Ah
xF6YxA9xA0txC6xDA[!4xE9ox85Mx7FxDESfxC0x9FxD4x04xFBxBBxC6x91S]
xD3x86}{x9BxF8xB5xCBbxD9]axC7x89xEAx97ixD2x92Qx1Ax8CuxC9x91
x83xA3xD7?txA5&xA9"
Красный цвет
не правильный](https://image.slidesharecdn.com/2-170705051113/85/Github-bugbounty-17-320.jpg)




![enterprise-manage/current/lib/manage/api.rb
25
get "/cluster-preflight" do
command = "sudo /usr/bin/env CLUSTER_ROLE=#{params[:type]}
/usr/local/share/enterprise/ghe-preflight-check“
if system(command)
status 200
else
status 400
`#{command}`
end
end
Красный цвет
не правильный](https://image.slidesharecdn.com/2-170705051113/85/Github-bugbounty-25-320.jpg)
![27
get "/cluster-preflight“ do
role = params[:type]
cluster_roles = %w(git web job mysql elasticsearch redis memcache metrics pages
storage)
if cluster_roles.include?(role)
output = IO.popen(["sudo", "/usr/bin/env", "CLUSTER_ROLE=#{role}",
"/usr/local/share/enterprise/ghe-preflight-check"]) { |io| io.read }
if $?.exitstatus == 0
status 200
else
status 400
output
end
else
…](https://image.slidesharecdn.com/2-170705051113/85/Github-bugbounty-27-320.jpg)




![src/util.c
32
assert_mem(line = calloc(strlen(read_buffer) + 1, sizeof(char)));
strncpy(line, read_buffer, strlen(read_buffer));
// See if we need to finish reading the line
while(line[strlen(line) - 1] != 'n') {
rc = fgets(read_buffer, sizeof(read_buffer), f);
if((rc == NULL) && feof(f)) {
// We got everything that we can get, so we'll
// call it a "line"
break;
}
…
Красный цвет
не правильный](https://image.slidesharecdn.com/2-170705051113/85/Github-bugbounty-32-320.jpg)
![src/util.c
33
assert_mem(line = calloc(strlen(read_buffer) + 1, sizeof(char)));
strncpy(line, read_buffer, strlen(read_buffer));
// See if we need to finish reading the line
while(strlen(line) && line[strlen(line) - 1] != 'n') {
rc = fgets(read_buffer, sizeof(read_buffer), f);
if((rc == NULL) && feof(f)) {
// We got everything that we can get, so we'll
// call it a "line"
break;
}
…
Красный цвет
не правильный](https://image.slidesharecdn.com/2-170705051113/85/Github-bugbounty-33-320.jpg)


![39
EFLAGS: 0x10246 (carry PARITY adjust ZERO sign trap INTERRUPT direction overflow)
[-------------------------------------code-------------------------------------]
0x7fbdfb6a923e <_IO_vfprintf_internal+126>: mov QWORD PTR [rbp-0x450],rax
0x7fbdfb6a9245 <_IO_vfprintf_internal+133>: mov rax,QWORD PTR [r15+0x10]
0x7fbdfb6a9249 <_IO_vfprintf_internal+137>: mov QWORD PTR [rbp-0x448],rax
=> 0x7fbdfb6a9250 <_IO_vfprintf_internal+144>: call 0x7fbdfb6ef750 <strchrnul>
0x7fbdfb6a9255 <_IO_vfprintf_internal+149>: and r13d,0x8000
0x7fbdfb6a925c <_IO_vfprintf_internal+156>: mov QWORD PTR [rbp-0x4b8],rax
0x7fbdfb6a9263 <_IO_vfprintf_internal+163>: mov QWORD PTR [rbp-0x4a0],rax
0x7fbdfb6a926a <_IO_vfprintf_internal+170>: je 0x7fbdfb6a92f0
<_IO_vfprintf_internal+304>
Guessed arguments:
arg[0]: 0x44bc45 ("duration_ms=%f fs_sent=%lu fs_recv=%lu client_recv=%lu
client_sent=%lu ")
arg[1]: 0x25 ('%')](https://image.slidesharecdn.com/2-170705051113/85/Github-bugbounty-39-320.jpg)










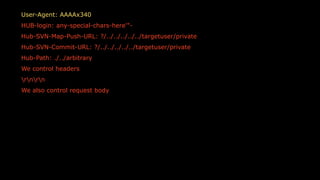
![55
::ffff:127.0.0.1 - kyprizel,special-chars-here'"-
[21/Jan/2017:00:04:44 +0000] - "GET /kyprizel/reponame/
HTTP/1.0" 500 5 0.0027
at=exception class=Rugged::OSError message="Failed to
resolve path
'/data/repositories/4/nw/45/c4/8c/9/9.git,./../arbitary': No such
file or directory“](https://image.slidesharecdn.com/2-170705051113/85/Github-bugbounty-55-320.jpg)
