Ghassancv
•Download as DOCX, PDF•
0 likes•81 views
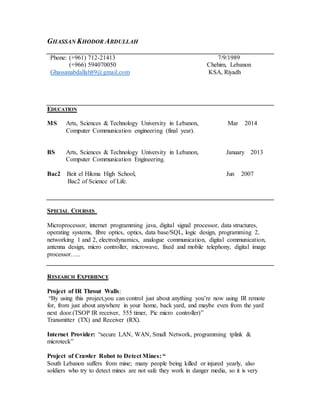
Ghassan Khodor Abdullah is a computer communication engineer with experience in programming, networking, security systems, and fiber optics. He has a Master's degree in Arts, Sciences & Technology and a Bachelor's degree in Computer Communication Engineering. He has worked on projects involving infrared signal transmission, mine detection robots, washing machines, and antenna design. Ghassan also has professional experience in networking and security systems through internships and training. He is currently employed as an IT Officer at the Arabian Construction Company in Riyadh, KSA.
Report
Share
Report
Share
Recommended
Latest Seminar Topics for Engineering,MCA,MSc Students

Latest Seminar Topics on IEEE Topics with free PPT download for ECE, CSE, EEE, Mechanical and Civil Engineering and MCA Students
Modern computer network technologies

Here is detail about latest 10 modern computer network technologies
New world of Wireless

In this presentation,i specially describe the wireless system for new generation.This presentation is made in my 1st yr.
CV_Agung Radistya Putra

I'm hard worker person and have responsibility to my job and must be finishe on time. I have skill in network and system computer. I have done some course such as ICND (CCNA), oracle, red hat, unix/linux.
Recommended
Latest Seminar Topics for Engineering,MCA,MSc Students

Latest Seminar Topics on IEEE Topics with free PPT download for ECE, CSE, EEE, Mechanical and Civil Engineering and MCA Students
Modern computer network technologies

Here is detail about latest 10 modern computer network technologies
New world of Wireless

In this presentation,i specially describe the wireless system for new generation.This presentation is made in my 1st yr.
CV_Agung Radistya Putra

I'm hard worker person and have responsibility to my job and must be finishe on time. I have skill in network and system computer. I have done some course such as ICND (CCNA), oracle, red hat, unix/linux.
Enabling on-device learning at scale

The need for intelligent, personalized experiences powered by AI is ever-growing. Our devices are producing more and more data that could help improve our AI experiences. How do we learn and efficiently process all this data from edge devices while maintaining privacy? On-device learning rather than cloud training can address these challenges. In this presentation, we’ll discuss:
- Why on-device learning is crucial for providing intelligent, personalized experiences without sacrificing privacy
- Our latest research in on-device learning, including few-shot learning, continuous learning, and federated learning
- How we are solving system and feasibility challenges to move from research to commercialization
An IOT Based Low Power Health Monitoring with Active Personal Assistance

Among sensible goals of active and assisted living paradigm is the unobtrusive monitoring of daily living activities. A lot of research has been going on continuous home and personal monitoring applications. There are many solutions were adapted by these technologies to make better remote monitoring applications. The traditional continuous home and personal monitoring systems which are implemented with traditional client server architecture which may fail in factors like low power consumption, un deterministic data delivery time, More sensitive to external connectivity issues temporary failures of servers , adhoc networks using ZigBee and Z wave etc. and also increase the cost of implementation. However, when dealing with the home environment, and especially with older adults, obtrusiveness, usability, and cost concerns are of the utmost relevance for active and assisted Living AAL joint program. With advent of cloud services, the continuous remote monitoring based applications became truly plug and play' approach implementation and also reduce the problems of temporary failures. One of the biggest challenges in this area is to make such application devices work with low power battery based applications . The main drawback comes from the higher power consumption, inherently needed to sustain much higher data rates. In this project, a solution is proposed to improve the low power consumption in Wi Fi sensors by making use of advanced RF based Microprocessor from Texas instruments CC3200 . Bed Occupancy sensor automation has been designed and implemented to test the feasibility of the approach. The TI CC3200 comes with ARM Cortex M4 as a core and inbuilt Wi Fi subsystem. The CC3200 provides different power modes to make the device enter into sleep or hibernate mode. This device will only enter only in work phase when the sensor is active state. During this phase, the processor sample and processes the sensor data and uploads to the cloud using REST API. Thing speak is an IoT cloud service used to present the sensory data as graphs, bar charts, and dashboards on the cloud remaining time it will enter into sleep phase to save the power of the device, so that it will extend the battery life time of the device. B. N. Meenakshi | Mrs. N. V. Durga "An IOT Based Low Power Health Monitoring with Active Personal Assistance" Published in International Journal of Trend in Scientific Research and Development (ijtsrd), ISSN: 2456-6470, Volume-4 | Issue-1 , December 2019, URL: https://www.ijtsrd.com/papers/ijtsrd29603.pdfPaper URL: https://www.ijtsrd.com/engineering/electronics-and-communication-engineering/29603/an-iot-based-low-power-health-monitoring-with-active-personal-assistance/b-n-meenakshi
Intrusion Detection in A Smart Forest-Fire Early Warning Sensory System

Incorporating an Intrusion Detection System(IDS) for a wireless sensor network (WSN) is one of the efficient moves to detect early intrusion to protect the integrity of the system. Machine learning Neural networks makes the intrusion detection task in WSN much easier by analyzing the data collected from sensor nodes(temperature, light, sound, and smoke). However, maintaining security and preventing intrusion in such approach remains a challenge. In this paper, we propose a Smart Intrusion Detection System (SIDS) which will be trained and tested using neural network approaches. The SIDS will be evaluated using parameters such as accuracy, timeliness, and trusted neighbor nodes, and the result is obtained for intrusion scenario using neural networks algorithms.
Environmental Monitoring using Wireless Sensor Networks (WSN) based on IOT.

https://irjet.net/archives/V4/i1/IRJET-V4I1246.pdf
Presentación Qualcomm evento Movilidad en la empresa española

Gaby Treiband, Director, Sales and Business Development, Key Accounts en Qualcomm, nos cuenta los cambios que están sucediendo en el paso de la era del PC a la era del móvil.
A SECURITY PROTOCOL FOR WIRELESS SENSOR NETWORKS

As sensor networks edge closer towards wide-spread placement, security issues become a central concern. So far, much research has concentrated on making sensor networks feasible and useful, and has not focused on security.
We present a set of security building blocks optimized for resource constrained environments and wireless communication. SPINS has two secure building blocks: SNEP and TESLA. SNEP provides the following important baseline security primitives: Data confidentiality, two-party data authentication, and data freshness. A particularly hard problem is to provide effective broadcast authentication, which is an important mechanism for sensor networks. TESLA is a new protocol which provides authenticated broadcast for severely resource-constrained surroundings. We realized the above protocols, and show that they are practical straighly on minimal hardware: the performance of the protocol suite easily matches the data rate of our network. Additionally, we prove that the suite can be used for building higher level protocols
Distributed Systems, Mobile Computing and Security

Secure Systems, Mobile Computing and Distributed Systems, Mobile Cloud Gaming, QoE Optimization of Mobile Video Streaming, Mobile crowd sourcing for indoor navigation, Internet of Things, Mobile Edge Computing, Green Big Data, Big Data Platforms for IoT and Health, Automated Parallel Testing and Verification, Information-Centric Networking (ICN)
PhD Projects in Telecommunication Research Help

Specific Categories on Communication Projects
Susceptible Notions in Telecommunication Projects
Vibrant Subjects in Telecommunication Projects
Current technologies being used for data communication

Current technologies being used for data communication
5G
Meanwhile spectrum
Internet of things takes off
Driverless everything
security, privacy and hiding bodies in the cloud
Distributed degrees
Artificial intelligence
New way to communicate
A New Trust Model for 5G Networks

Presentation from Digital Transformation World May 15th 2018 covering:
Understanding the reality of data breaches today
Virtualization security challenges for the CSP 5G network
Key capabilities to create trustworthy 5G virtualized networks
Usage of secure enclaves to create a fabric of trust within the network
How to protect VNFs and enterprise applications, leveraging Intel SGX technology
More Related Content
What's hot
Enabling on-device learning at scale

The need for intelligent, personalized experiences powered by AI is ever-growing. Our devices are producing more and more data that could help improve our AI experiences. How do we learn and efficiently process all this data from edge devices while maintaining privacy? On-device learning rather than cloud training can address these challenges. In this presentation, we’ll discuss:
- Why on-device learning is crucial for providing intelligent, personalized experiences without sacrificing privacy
- Our latest research in on-device learning, including few-shot learning, continuous learning, and federated learning
- How we are solving system and feasibility challenges to move from research to commercialization
An IOT Based Low Power Health Monitoring with Active Personal Assistance

Among sensible goals of active and assisted living paradigm is the unobtrusive monitoring of daily living activities. A lot of research has been going on continuous home and personal monitoring applications. There are many solutions were adapted by these technologies to make better remote monitoring applications. The traditional continuous home and personal monitoring systems which are implemented with traditional client server architecture which may fail in factors like low power consumption, un deterministic data delivery time, More sensitive to external connectivity issues temporary failures of servers , adhoc networks using ZigBee and Z wave etc. and also increase the cost of implementation. However, when dealing with the home environment, and especially with older adults, obtrusiveness, usability, and cost concerns are of the utmost relevance for active and assisted Living AAL joint program. With advent of cloud services, the continuous remote monitoring based applications became truly plug and play' approach implementation and also reduce the problems of temporary failures. One of the biggest challenges in this area is to make such application devices work with low power battery based applications . The main drawback comes from the higher power consumption, inherently needed to sustain much higher data rates. In this project, a solution is proposed to improve the low power consumption in Wi Fi sensors by making use of advanced RF based Microprocessor from Texas instruments CC3200 . Bed Occupancy sensor automation has been designed and implemented to test the feasibility of the approach. The TI CC3200 comes with ARM Cortex M4 as a core and inbuilt Wi Fi subsystem. The CC3200 provides different power modes to make the device enter into sleep or hibernate mode. This device will only enter only in work phase when the sensor is active state. During this phase, the processor sample and processes the sensor data and uploads to the cloud using REST API. Thing speak is an IoT cloud service used to present the sensory data as graphs, bar charts, and dashboards on the cloud remaining time it will enter into sleep phase to save the power of the device, so that it will extend the battery life time of the device. B. N. Meenakshi | Mrs. N. V. Durga "An IOT Based Low Power Health Monitoring with Active Personal Assistance" Published in International Journal of Trend in Scientific Research and Development (ijtsrd), ISSN: 2456-6470, Volume-4 | Issue-1 , December 2019, URL: https://www.ijtsrd.com/papers/ijtsrd29603.pdfPaper URL: https://www.ijtsrd.com/engineering/electronics-and-communication-engineering/29603/an-iot-based-low-power-health-monitoring-with-active-personal-assistance/b-n-meenakshi
Intrusion Detection in A Smart Forest-Fire Early Warning Sensory System

Incorporating an Intrusion Detection System(IDS) for a wireless sensor network (WSN) is one of the efficient moves to detect early intrusion to protect the integrity of the system. Machine learning Neural networks makes the intrusion detection task in WSN much easier by analyzing the data collected from sensor nodes(temperature, light, sound, and smoke). However, maintaining security and preventing intrusion in such approach remains a challenge. In this paper, we propose a Smart Intrusion Detection System (SIDS) which will be trained and tested using neural network approaches. The SIDS will be evaluated using parameters such as accuracy, timeliness, and trusted neighbor nodes, and the result is obtained for intrusion scenario using neural networks algorithms.
Environmental Monitoring using Wireless Sensor Networks (WSN) based on IOT.

https://irjet.net/archives/V4/i1/IRJET-V4I1246.pdf
Presentación Qualcomm evento Movilidad en la empresa española

Gaby Treiband, Director, Sales and Business Development, Key Accounts en Qualcomm, nos cuenta los cambios que están sucediendo en el paso de la era del PC a la era del móvil.
A SECURITY PROTOCOL FOR WIRELESS SENSOR NETWORKS

As sensor networks edge closer towards wide-spread placement, security issues become a central concern. So far, much research has concentrated on making sensor networks feasible and useful, and has not focused on security.
We present a set of security building blocks optimized for resource constrained environments and wireless communication. SPINS has two secure building blocks: SNEP and TESLA. SNEP provides the following important baseline security primitives: Data confidentiality, two-party data authentication, and data freshness. A particularly hard problem is to provide effective broadcast authentication, which is an important mechanism for sensor networks. TESLA is a new protocol which provides authenticated broadcast for severely resource-constrained surroundings. We realized the above protocols, and show that they are practical straighly on minimal hardware: the performance of the protocol suite easily matches the data rate of our network. Additionally, we prove that the suite can be used for building higher level protocols
Distributed Systems, Mobile Computing and Security

Secure Systems, Mobile Computing and Distributed Systems, Mobile Cloud Gaming, QoE Optimization of Mobile Video Streaming, Mobile crowd sourcing for indoor navigation, Internet of Things, Mobile Edge Computing, Green Big Data, Big Data Platforms for IoT and Health, Automated Parallel Testing and Verification, Information-Centric Networking (ICN)
PhD Projects in Telecommunication Research Help

Specific Categories on Communication Projects
Susceptible Notions in Telecommunication Projects
Vibrant Subjects in Telecommunication Projects
Current technologies being used for data communication

Current technologies being used for data communication
5G
Meanwhile spectrum
Internet of things takes off
Driverless everything
security, privacy and hiding bodies in the cloud
Distributed degrees
Artificial intelligence
New way to communicate
A New Trust Model for 5G Networks

Presentation from Digital Transformation World May 15th 2018 covering:
Understanding the reality of data breaches today
Virtualization security challenges for the CSP 5G network
Key capabilities to create trustworthy 5G virtualized networks
Usage of secure enclaves to create a fabric of trust within the network
How to protect VNFs and enterprise applications, leveraging Intel SGX technology
What's hot (20)
An IOT Based Low Power Health Monitoring with Active Personal Assistance

An IOT Based Low Power Health Monitoring with Active Personal Assistance
Intrusion Detection in A Smart Forest-Fire Early Warning Sensory System

Intrusion Detection in A Smart Forest-Fire Early Warning Sensory System
Environmental Monitoring using Wireless Sensor Networks (WSN) based on IOT.

Environmental Monitoring using Wireless Sensor Networks (WSN) based on IOT.
Presentación Qualcomm evento Movilidad en la empresa española

Presentación Qualcomm evento Movilidad en la empresa española
Implementation of embedded real time monitoring temperature and humidity system

Implementation of embedded real time monitoring temperature and humidity system
Distributed Systems, Mobile Computing and Security

Distributed Systems, Mobile Computing and Security
Current technologies being used for data communication

Current technologies being used for data communication
Similar to Ghassancv
5G 2

This is the second part of my 5G project which consists of the architecture structure of 5G. What all it consists of, what all technologies it uses, what all layers it contain etc.
We are looking at the future of technology that has the structure of Nanocore, beneficial for future applications.
Statistical Dissemination Control in Large Machine-to-Machine Communication N...

Ki-Tech Solutions IEEE PROJECTS DEVELOPMENTS WE OFFER IEEE PROJECTS MCA FINAL YEAR STUDENT PROJECTS, ENGINEERING PROJECTS AND TRAINING, PHP PROJECTS, JAVA AND J2EE PROJECTS, ASP.NET PROJECTS, NS2 PROJECTS, MATLAB PROJECTS AND IPT TRAINING IN RAJAPALAYAM, VIRUDHUNAGAR DISTRICTS, AND TAMILNADU. Mail to: kitechsolutions.in@gmail.com
Senior Telecommunications Engineer / Operation Manger

Seeking a challenging position in a reputable multinational company where my studies, skills and experience could be invested as well as Develop and increase my experience in this field.
Toward Transparent Coexistence for Multihop Secondary Cognitive Radio Networks

Ki-Tech Solutions IEEE PROJECTS DEVELOPMENTS WE OFFER IEEE PROJECTS MCA FINAL YEAR STUDENT PROJECTS, ENGINEERING PROJECTS AND TRAINING, PHP PROJECTS, JAVA AND J2EE PROJECTS, ASP.NET PROJECTS, NS2 PROJECTS, MATLAB PROJECTS AND IPT TRAINING IN RAJAPALAYAM, VIRUDHUNAGAR DISTRICTS, AND TAMILNADU. Mail to: kitechsolutions.in@gmail.com
Similar to Ghassancv (20)
Statistical Dissemination Control in Large Machine-to-Machine Communication N...

Statistical Dissemination Control in Large Machine-to-Machine Communication N...
Senior Telecommunications Engineer / Operation Manger

Senior Telecommunications Engineer / Operation Manger
Toward Transparent Coexistence for Multihop Secondary Cognitive Radio Networks

Toward Transparent Coexistence for Multihop Secondary Cognitive Radio Networks
IT networks, collaboration and security engineer egy-

IT networks, collaboration and security engineer egy-
Ghassancv
- 1. GHASSAN KHODOR ABDULLAH Phone: (+961) 712-21413 (+966) 594070050 Ghassanabdallah89@gmail.com 7/9/1989 Chehim, Lebanon KSA, Riyadh EDUCATION MS Arts, Sciences & Technology University in Lebanon, Mar 2014 Computer Communication engineering (final year). BS Arts, Sciences & Technology University in Lebanon, January 2013 Computer Communication Engineering. Bac2 Beit el Hikma High School, Jun 2007 Bac2 of Science of Life. SPECIAL COURSES Microprocessor, internet programming java, digital signal processor, data structures, operating systems, fibre optics, optics, data base/SQL, logic design, programming 2, networking 1 and 2, electrodynamics, analogue communication, digital communication, antenna design, micro controller, microwave, fixed and mobile telephony, digital image processor….. RESEARCH EXPERIENCE Project of IR Throut Walls: “By using this project,you can control just about anything you’re now using IR remote for, from just about anywhere in your home, back yard, and maybe even from the yard next door.(TSOP IR receiver, 555 timer, Pic micro controller)” Transmitter (TX) and Receiver (RX). Internet Provider: “secure LAN, WAN, Small Network, programming tplink & microteck” Project of Crawler Robot to Detect Mines: “ South Lebanon suffers from mine; many people being killed or injured yearly, also soldiers who try to detect mines are not safe they work in danger media, so it is very
- 2. important to use our knowledge to help our country. So from our major we tried to help by building a crawler robot that can move at any type of land, this robot is controlled wireless, this robot is guided by a metal detection sensor that detect mines and send data to the controller, this robot is able to be developed in future.” Micro-Controller Project: Wash Machine “The main action in this machine will start. Antenna-Design Project: Patch 2.4 GHz “Design and implementing antenna and studied the E and H - plane, this antenna is used to the internet connection and connect the users to the central”. Designand Architecture for small company: For example if we have 30 users in different department and design an diagram show the different part and how to secure and allows print server and mail server ,DHCP,Firewall,exchange,…… PROFESSIONAL TRAINING/EXPERIENCE Stage in Ogero Company with map phones and router, types of cable (cross, Sata ….) Cisco router, fixed Telephones Training at Khatib & Alami Company With Fiber Optics Broadband Network DWDM (Dense Wavelength Division Multiplexing) Connecting all centrals in Lebanon about fiber optics and testing if we have losses…the losses not have more than 0.75 dB Training at IT for computer and security system Security system, camera security, it & Hardware maintenance Stage at Prevision Networks Internet server provider: Mikrotik and microwave antenna…configuration and testing links…security Wi- Fi…. ARABIAN CONSTRACTION COMPANY SAUDI/RIYADH BRANCH(Current Job) IT Officer
- 3. LANGUAGES English: Intermediate Listener, Novice Speaker, Advanced Reading and Writing. French: Advanced levels in Listening, Speaking, Reading, and Writing. Arabic: Native Language. COMPUTER/WORK SKILLS Programming: Internet programming Java, Data structures, C++, Data Base/SQL, HTML, PCB, Matlab, SAP. Work Skills: - Good work in team. - Speed learning about work. - Studiously at work and loves evolution not only in the field of work. - Trustworthy, honest, faithful. REFERENCES Mr. Youssef Charkawi CCE AUL Mr. Ahmad Abdallah Internet Provider Ferrari Networks Phone: 961-708 25362 Eng. Ali Nassar Prevision Networks Phone: 70088803