This document provides a summary of key concepts in computer networks:
1. It defines a computer network and describes the basic components - PCs, interconnections like network cards and cables, switches, and routers.
2. It discusses common network applications like email, web browsers, instant messaging, and collaboration tools.
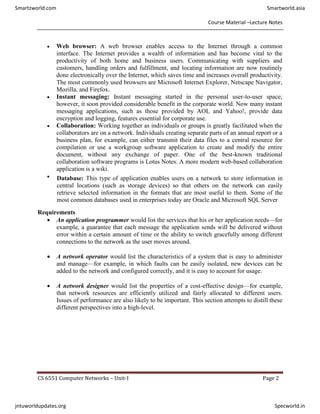
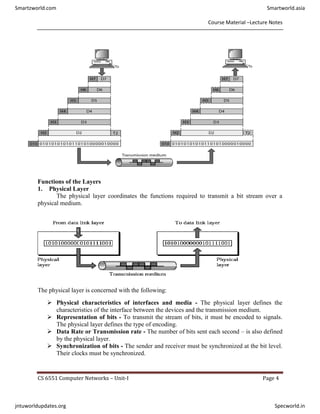
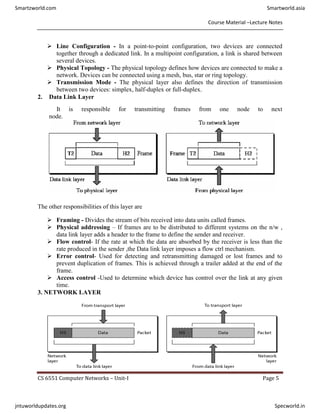
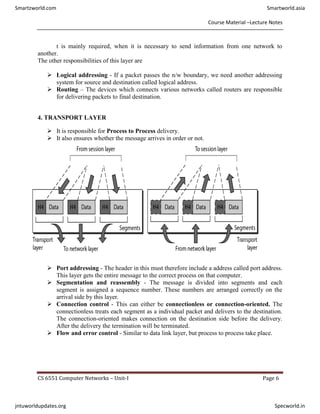
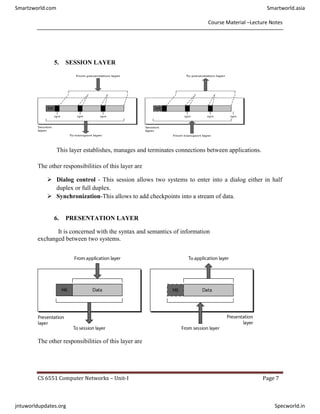
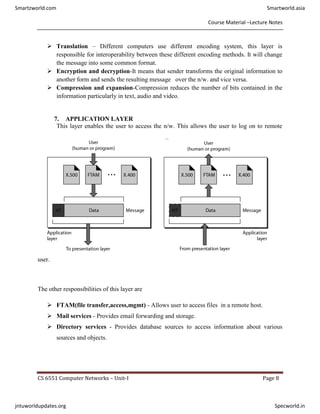
3. It describes the seven-layer OSI model and compares it to the TCP/IP model, explaining the functions of the physical, data link, network, and transport layers.
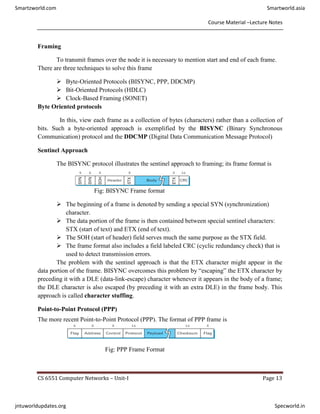
4. It discusses networking software, network performance metrics like bandwidth and latency, and link layer services like acknowledged and unacknowledged connection-oriented services.