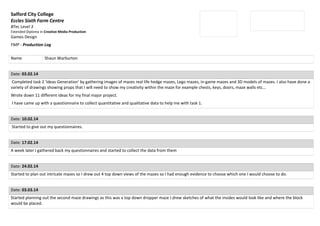
This document contains a production log for a student named Shaun Warburton documenting the progress of his games design final major project creating mazes in Creative Media Production. It outlines tasks completed from February to March including gathering research materials, developing maze ideas and designs, modeling mazes in a 3D program, and facing issues scanning work and accessing project files at the end. The student worked on traditional and dropper mazes, gathered questionnaire feedback, and plans to extend the project deadline to fully complete the work.