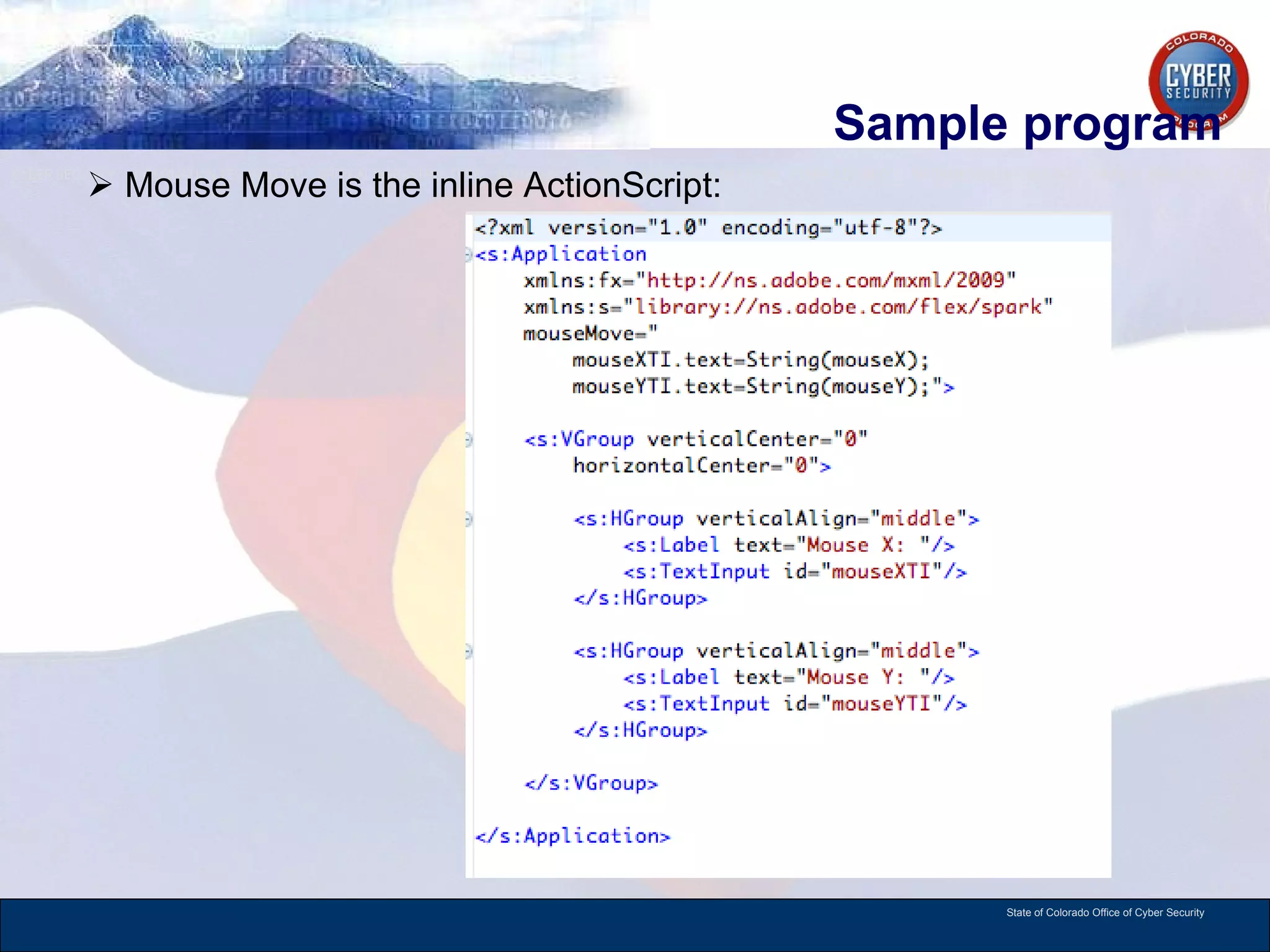
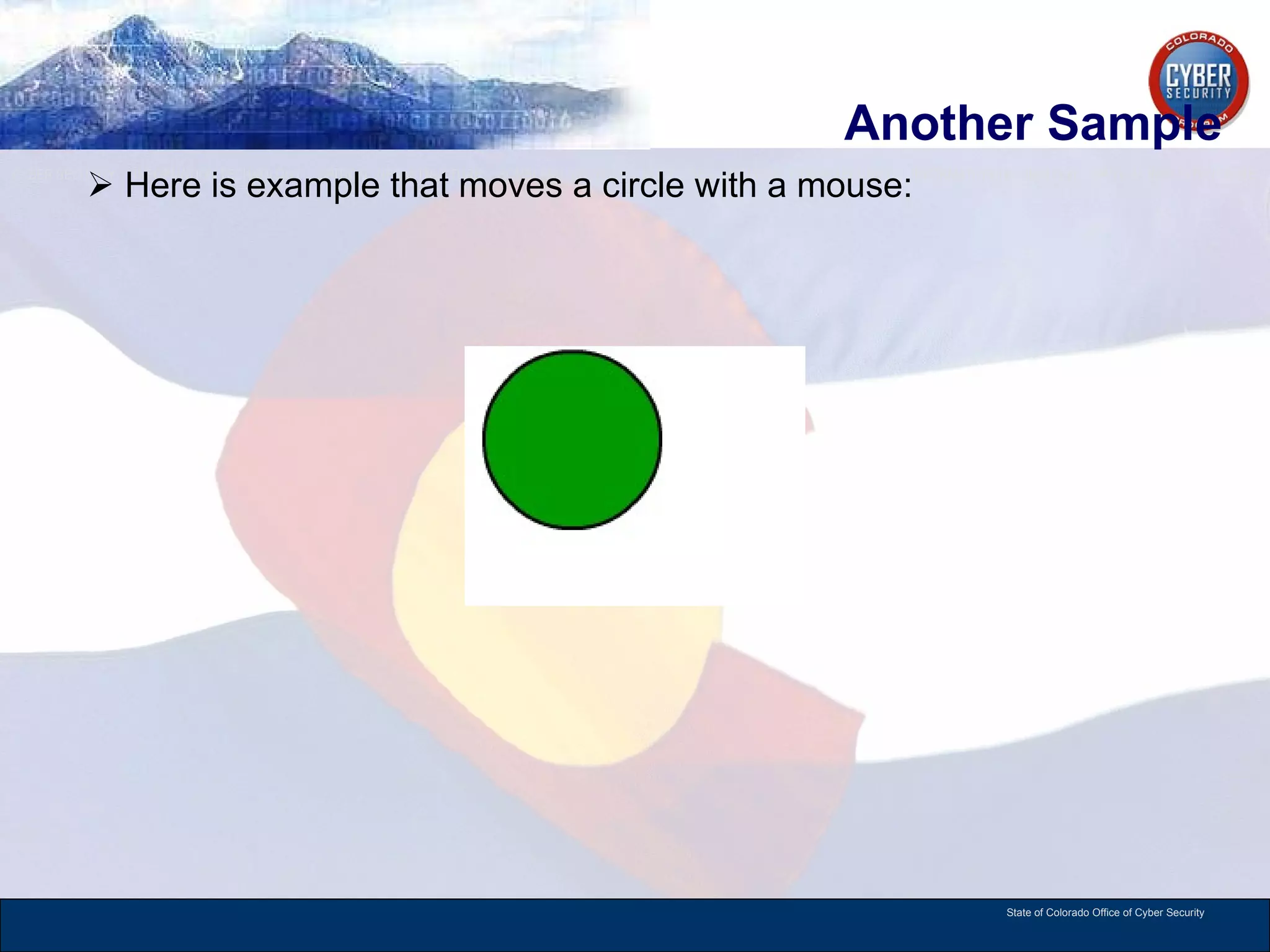
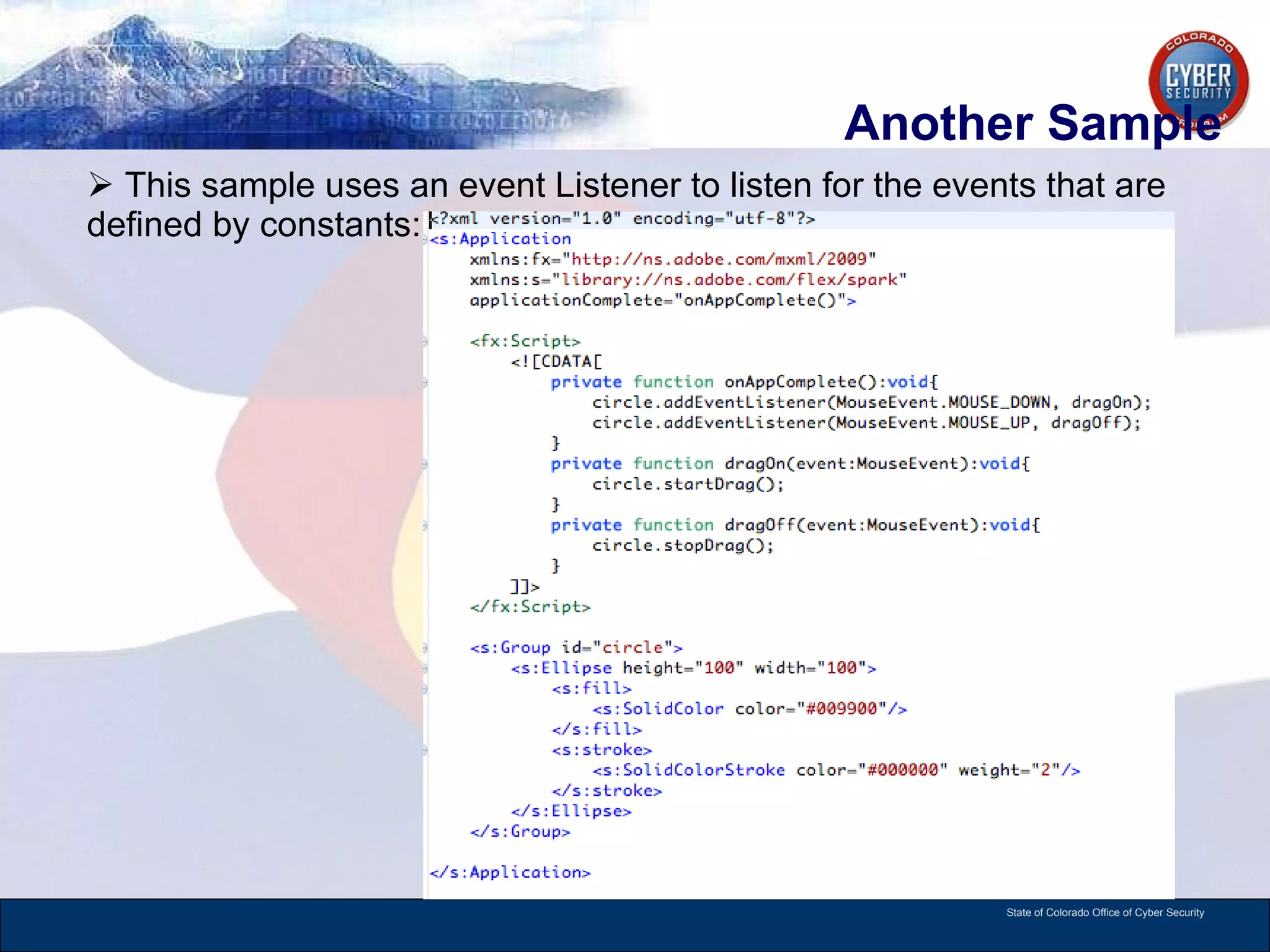
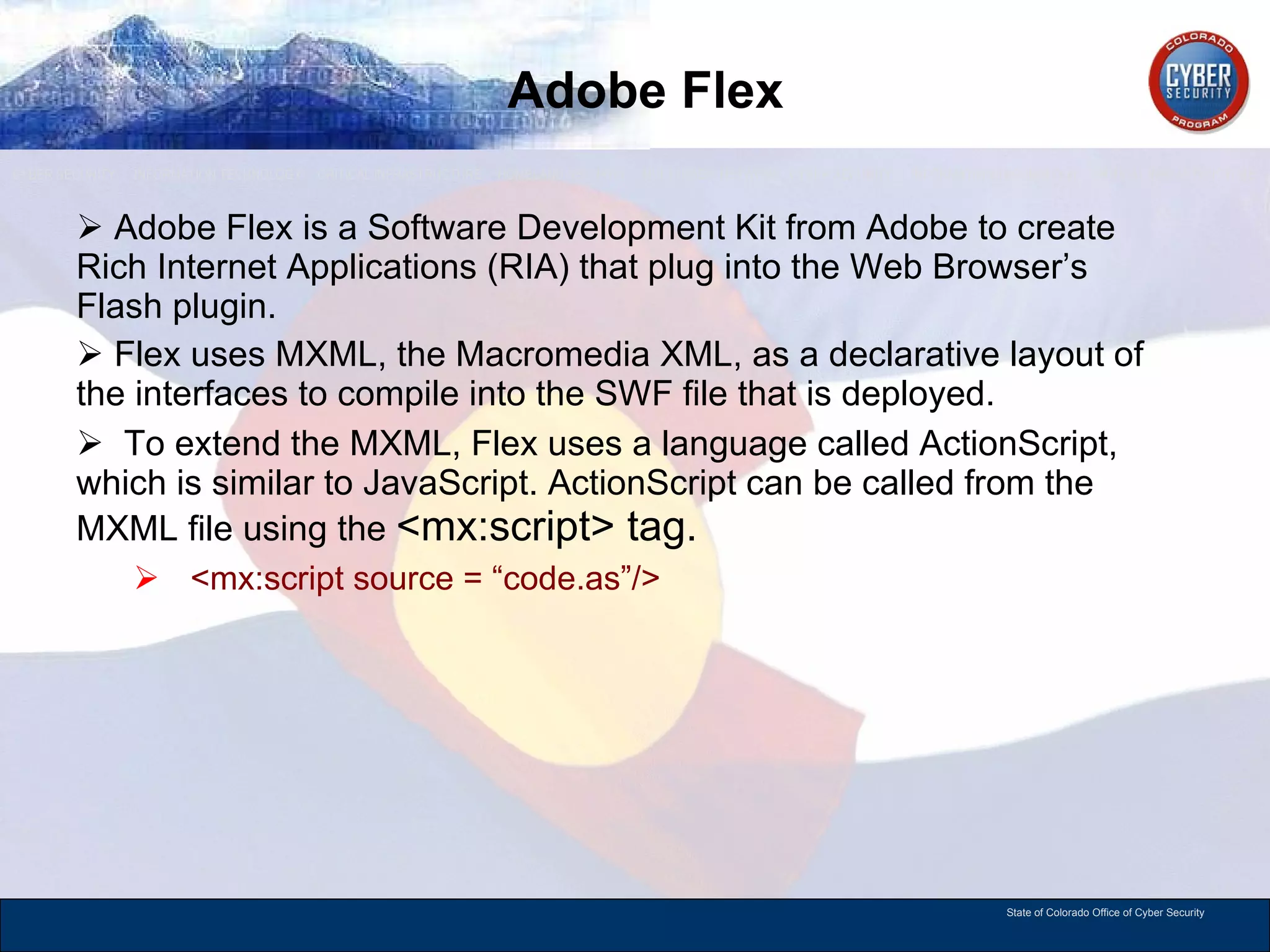
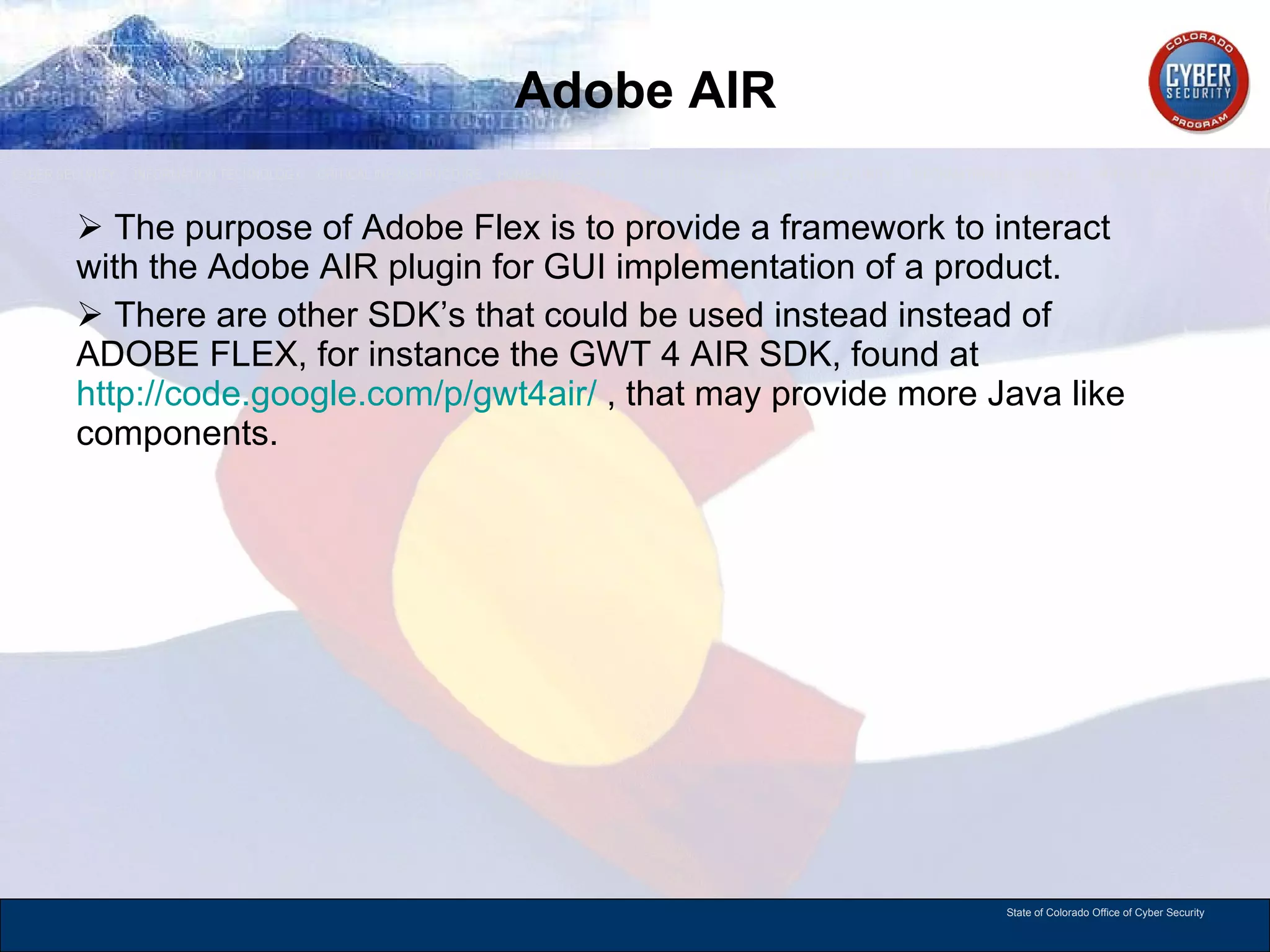
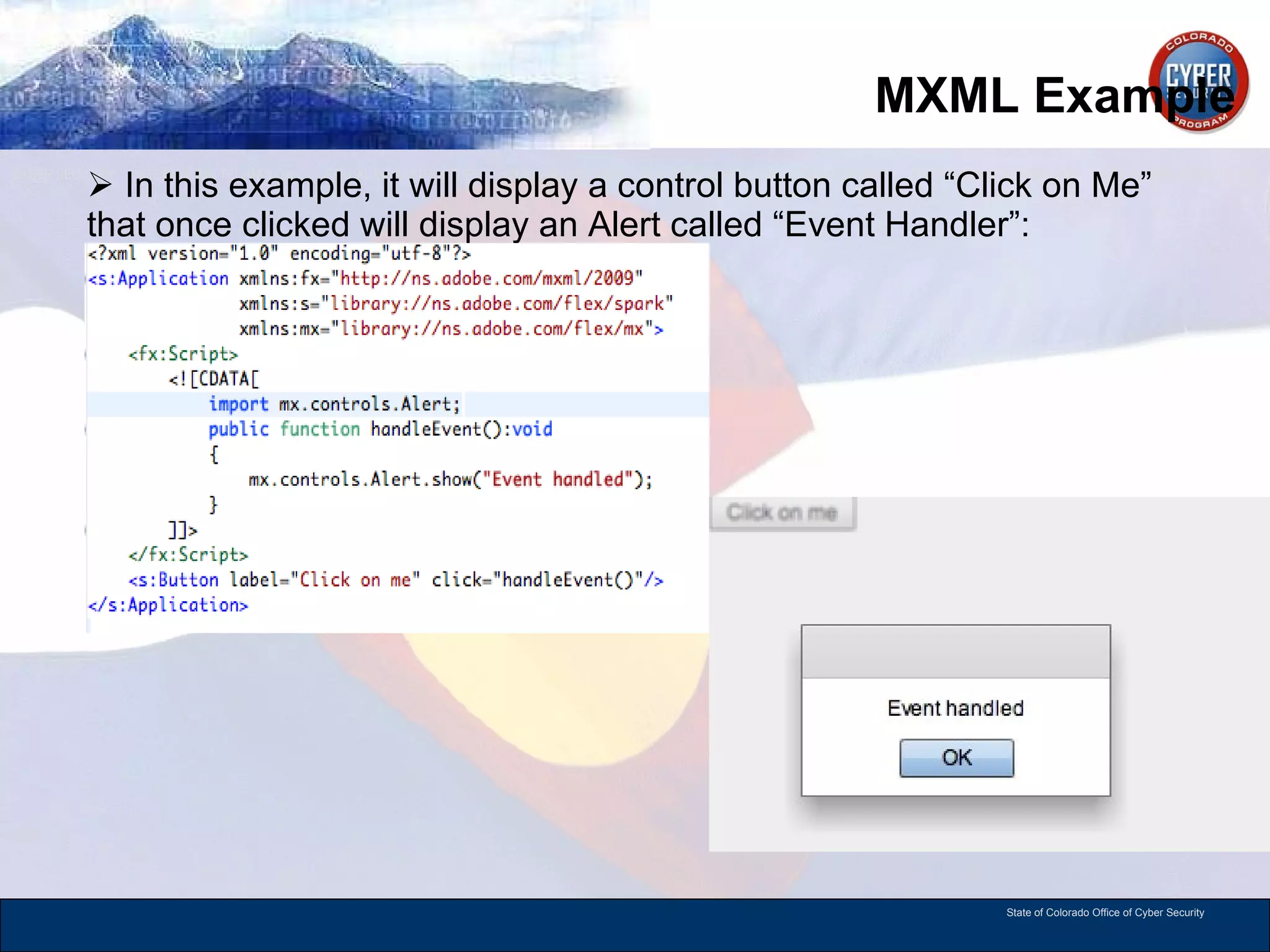
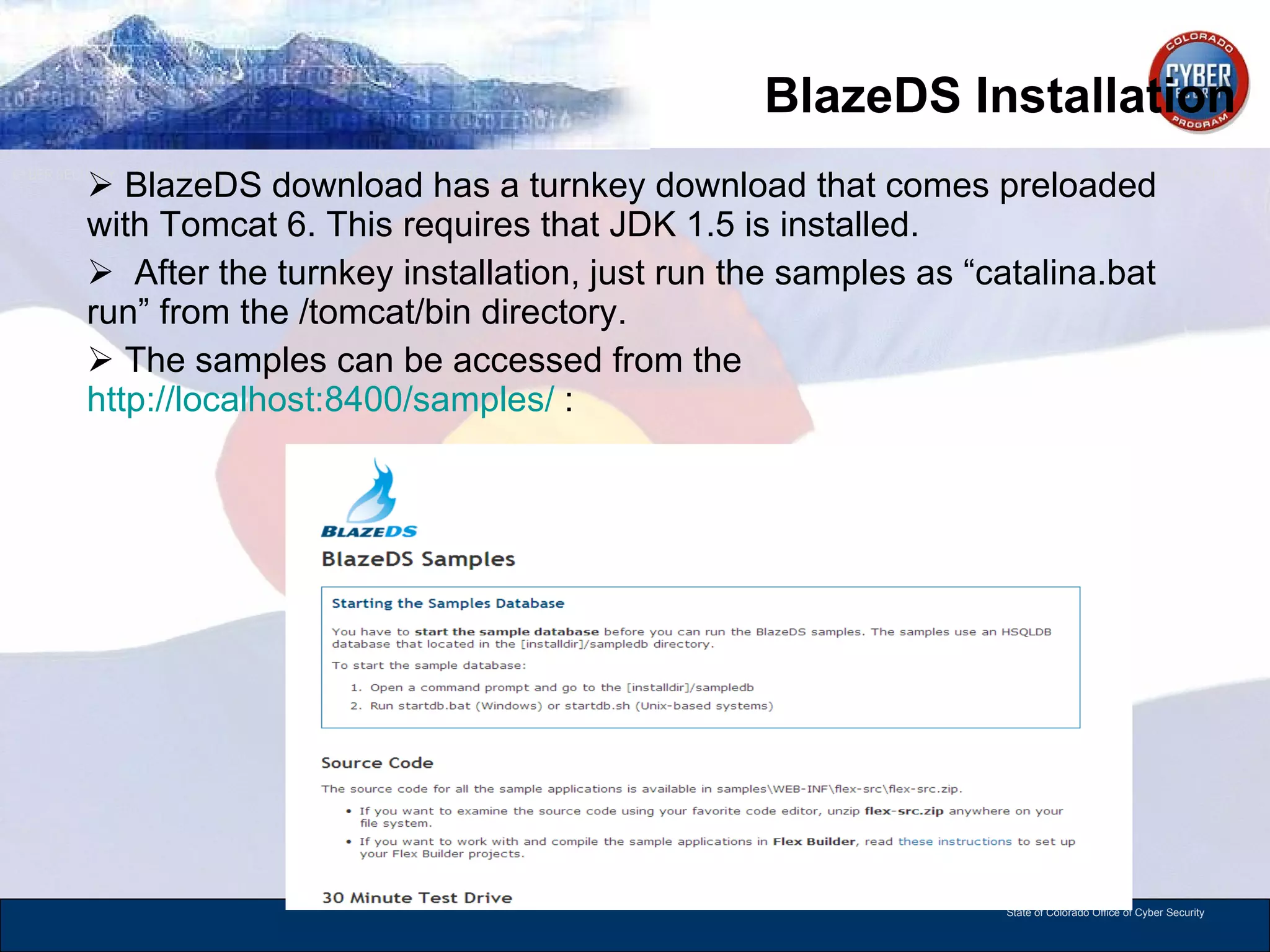
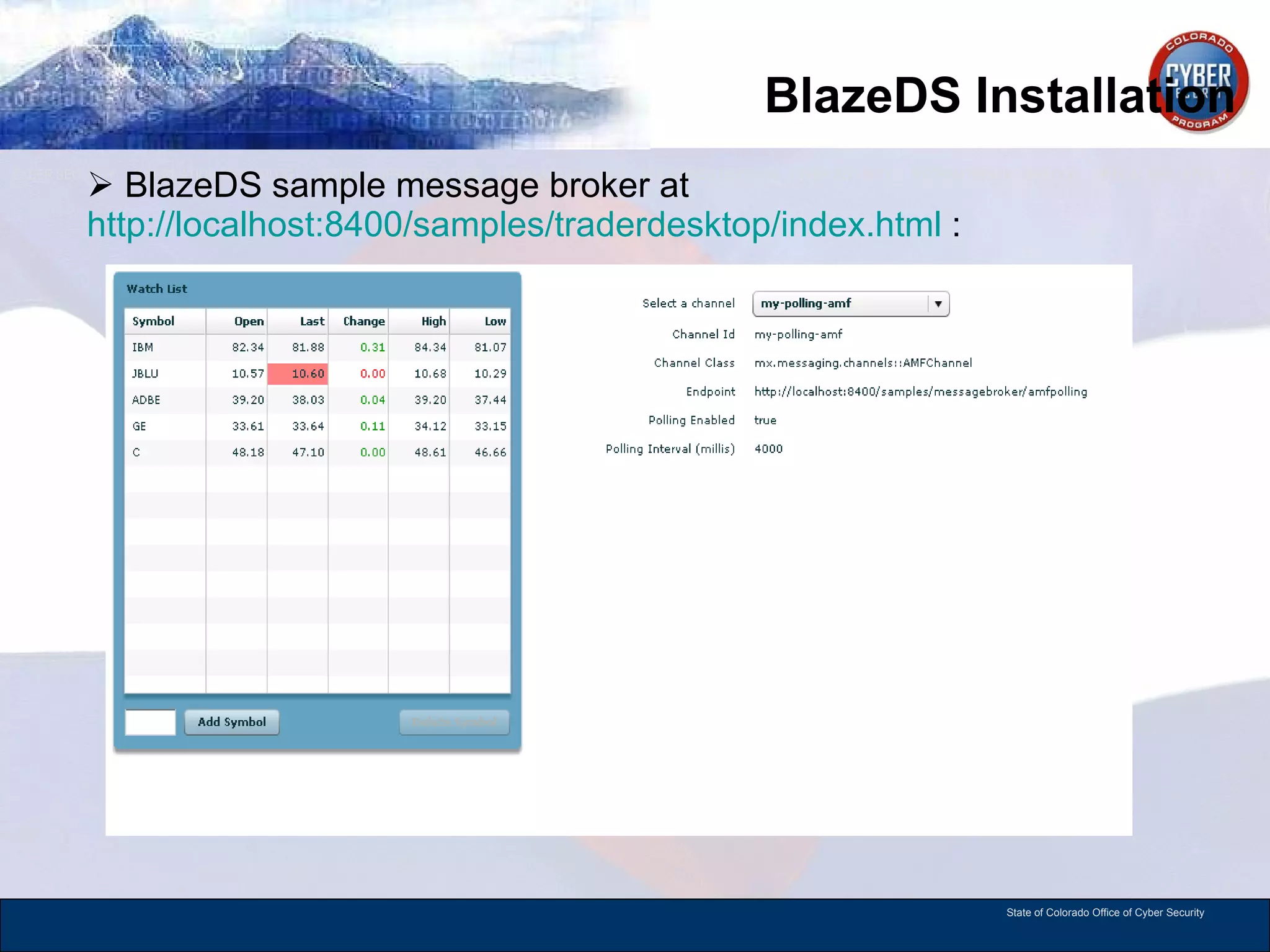
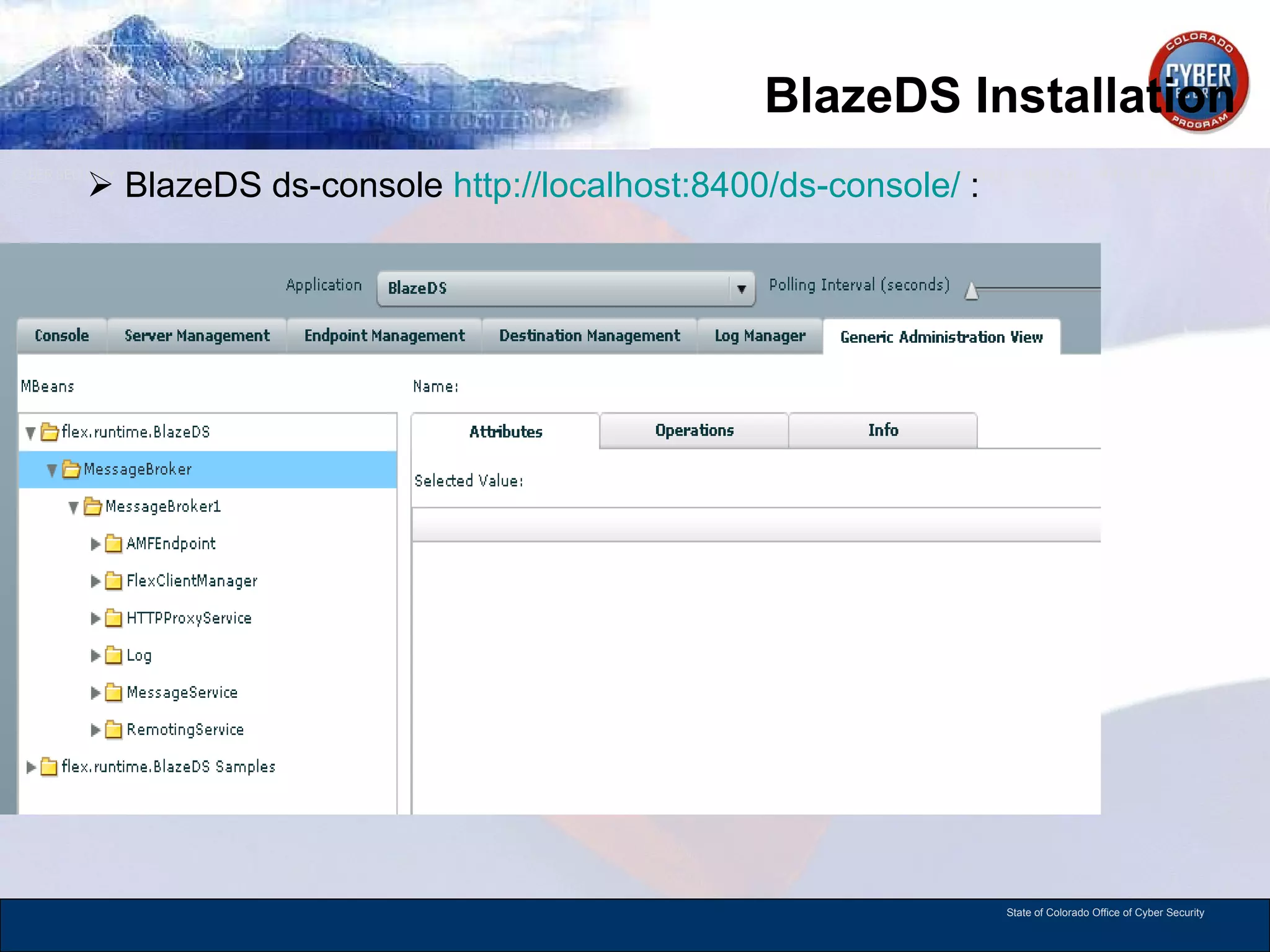
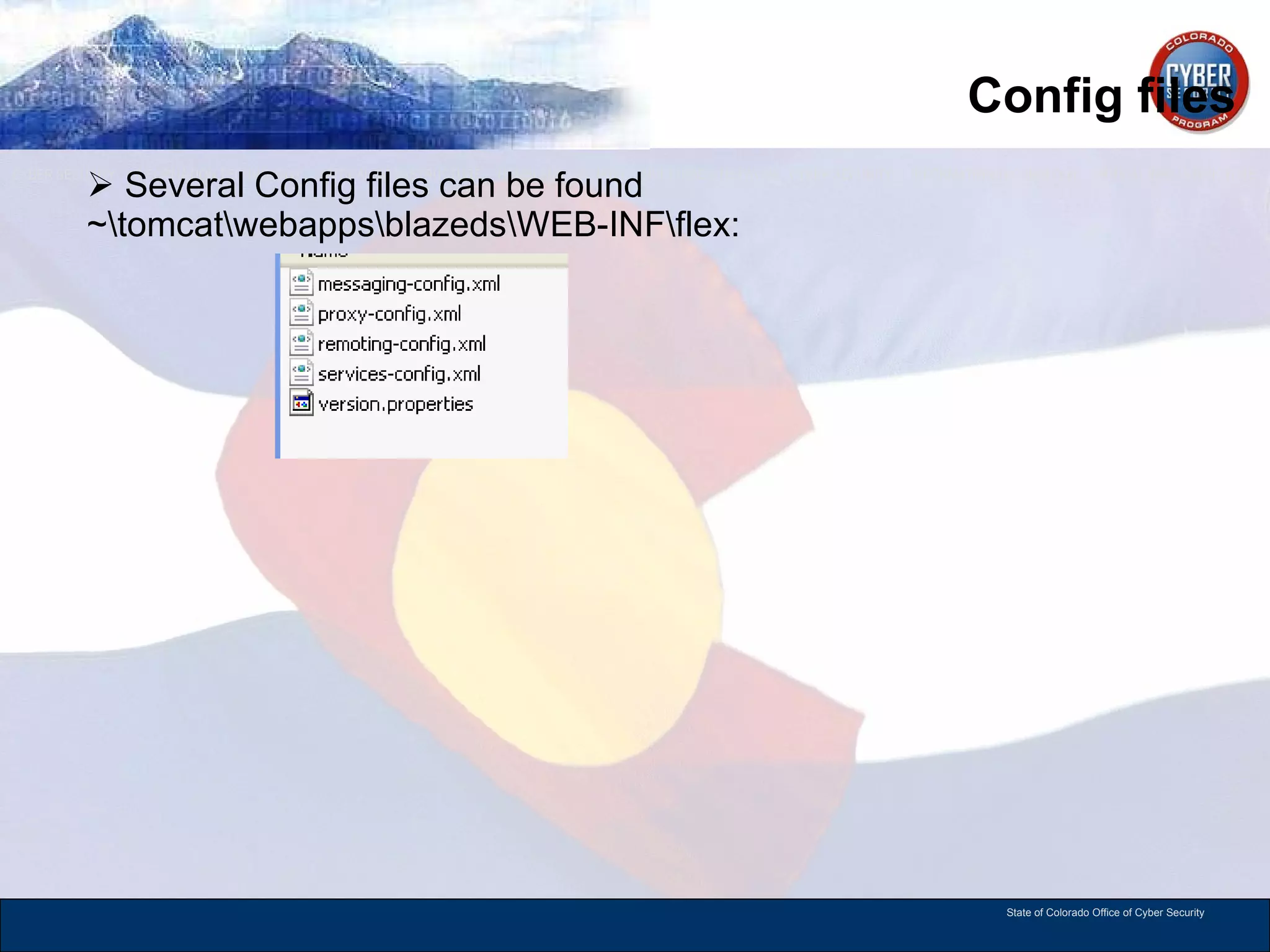
This document provides an overview of Rich Internet Applications (RIA) and the Adobe Flex software development kit. It discusses how Flex uses MXML and ActionScript to create RIA applications that interact with the Flash plugin. It also covers related technologies like Adobe AIR, BlazeDS, and LifeCycle Data Services that allow Flex applications to communicate with backend services. Examples of MXML code and Flex application architecture are provided.
![MXML Hello World Example <?xml version="1.0" encoding="utf-8"?> <mx:Application xmlns:mx="http://www.adobe.com/2006/mxml" layout="absolute" backgroundGradientColors="[#000011, #333333]"> <mx:Label text="Hello World!" verticalCenter="0" horizontalCenter="0" fontSize="48" letterSpacing="1"> <mx:filters> <mx:GlowFilter color="#ffffdd"/> </mx:filters> </mx:Label> </mx:Application>](https://image.slidesharecdn.com/flex4rev001-13064342581348-phpapp02-110526132619-phpapp02/75/Adobe-Flex4-5-2048.jpg)


![RemoteClass The Data Transfer Object uses the [RemoteClass] metadata tag. This is part of Flex Remoting. This is part of AMF Binding from Java to ActionScript through BlazeDS. Example ActionScript: Example Java:](https://image.slidesharecdn.com/flex4rev001-13064342581348-phpapp02-110526132619-phpapp02/75/Adobe-Flex4-21-2048.jpg)