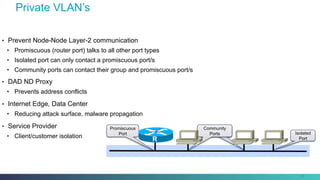
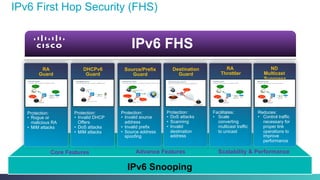
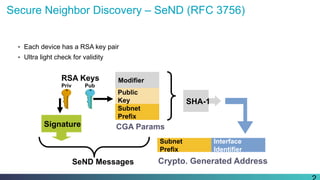
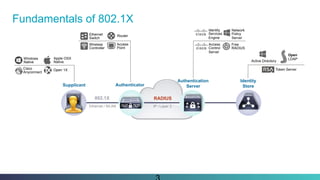
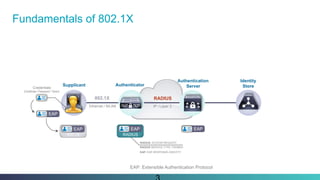
IPv6 access security provides three main methods for securing first hop connections: IPv6 first hop security, secure neighbor discovery, and 802.1x authentication. These methods help protect against spoofing, man-in-the-middle attacks, and denial of service attacks on IPv6 networks.



![RADIUS802.1X
IP / Layer 3
Supplicant Authenticator
Authentication
Server
Identity
Store
Fundamentals of 802.1X
EAP: EAP-SUCCESS
RADIUS: ACCESS-ACCEPT
[+Authorization Attributes ]
802.1X
RADIUS
EAP
Port-Authorized
802.1X
EAP
Port-Unauthorized
(If authentication fails)
EAP: Extensible Authentication Protocol](https://image.slidesharecdn.com/fedv6tf-fhs-151103154950-lva1-app6891/85/Fedv6tf-fhs-33-320.jpg)