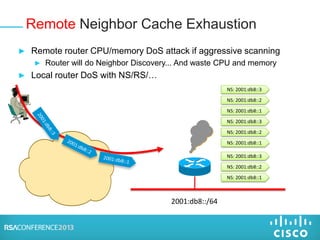
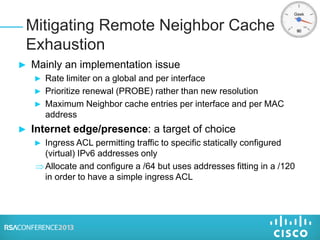
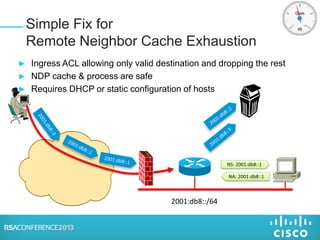
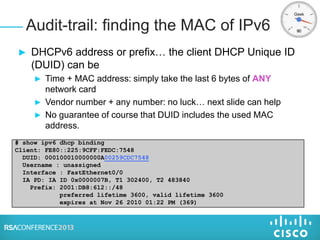
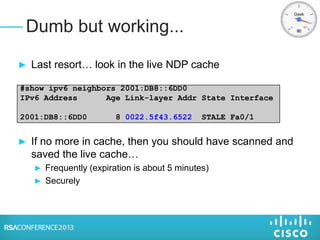
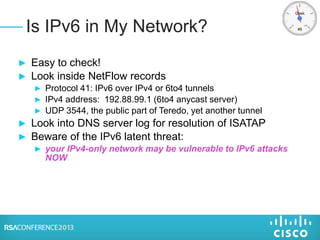
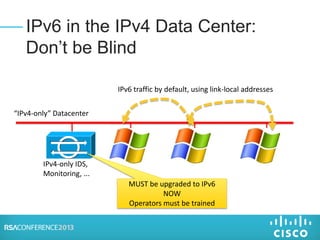
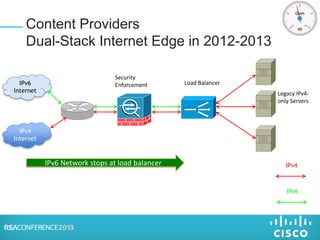
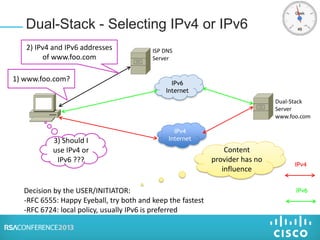
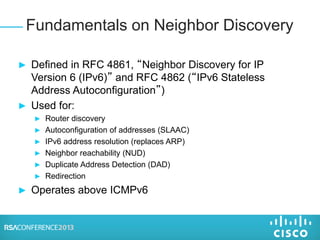
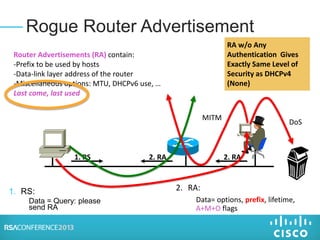
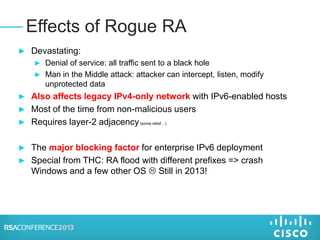
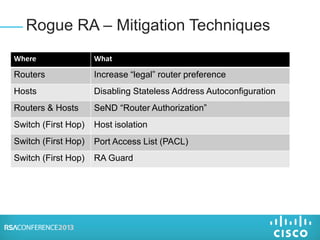
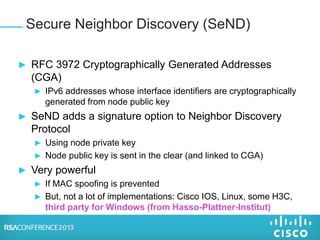
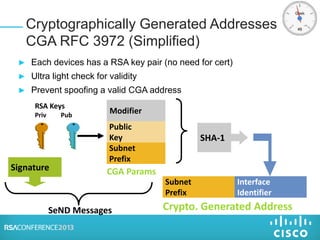
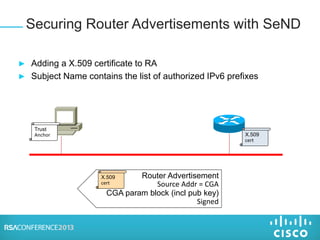
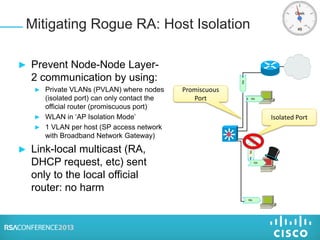
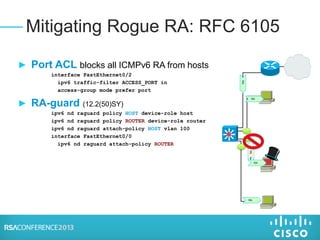
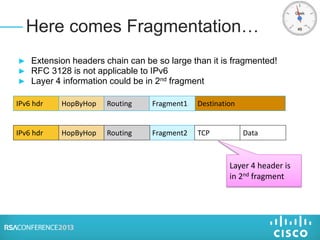
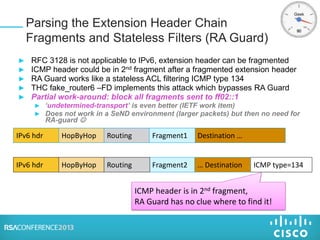
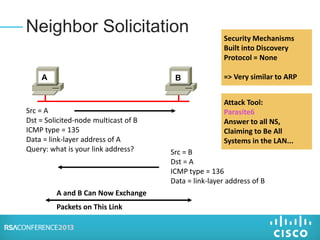
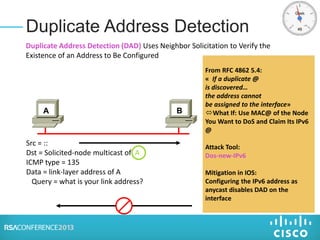
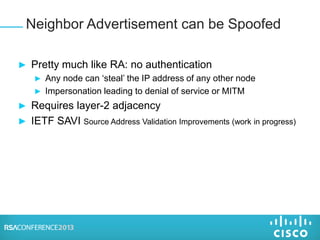
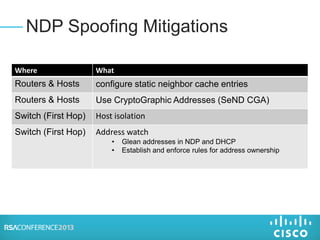
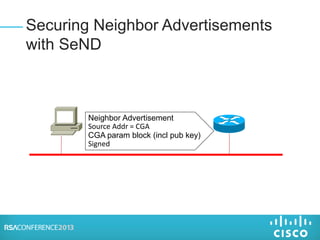
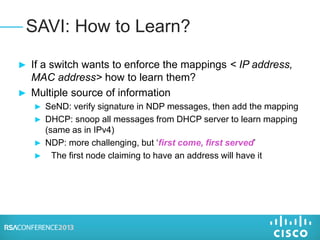
The document discusses security issues with IPv6 and proposed mitigation techniques. It covers topics such as router advertisements, neighbor discovery protocol, and fragmentation. Specifically, it notes that router advertisements and neighbor solicitations are not authenticated by default, allowing for spoofing attacks. The document proposes several mitigation approaches including cryptographically generated addresses, router authorization, port access control lists, and host isolation to secure IPv6 networks.

![Innocent Windows Upgrade
C:>ping svr-01
Pinging svr-01.example.com [10.121.12.25] with 32 bytes of data:
Reply from 10.121.12.25: bytes=32 time<1ms TTL=128
Reply from 10.121.12.25: bytes=32 time<1ms TTL=128
Reply from 10.121.12.25: bytes=32 time<1ms TTL=128
Reply from 10.121.12.25: bytes=32 time<1ms TTL=128
Windows 2003
C:>ping svr-01
Pinging svr-01 [fe80::c4e2:f21d:d2b3:8463%15] with 32 bytes of data:
Reply from fe80::c4e2:f21d:d2b3:8463%15: time<1ms
Reply from fe80::c4e2:f21d:d2b3:8463%15: time<1ms
Reply from fe80::c4e2:f21d:d2b3:8463%15: time<1ms
Reply from fe80::c4e2:f21d:d2b3:8463%15: time<1ms
Upgraded Host to Windows 2008
ALL recent OS have IPv6 enabled by default and prefer it...
=> Enable IPv6 host security and IPv6 IPS](https://image.slidesharecdn.com/tech-f42-150420135137-conversion-gate01/85/Tech-f42-8-320.jpg)


![Binding table
NS [IP source=A1, LLA=MACH1]
DHCP-
server
REQUEST [XID, SMAC = MACH2]
REPLY[XID, IP=A21, IP=A22]
data [IP source=A3, SMAC=MACH3]
DAD NS [IP source=UNSPEC, target = A3]
NA [IP source=A3, LLA=MACH3]
ADR MAC VLAN IF
A1 MACH1 100 P1
A21 MACH2 100 P2
A22 MACH2 100 P2
A3 MACH3 100 P3
DHCP LEASEQUERY
DHCP LEASEQUERY_REPLY
H1 H2 H3
NDP Spoofing – Mitigation: Binding
Integrity at the First Hop
Then, drop all Neighbor Discovery packets not matching the binding...](https://image.slidesharecdn.com/tech-f42-150420135137-conversion-gate01/85/Tech-f42-34-320.jpg)