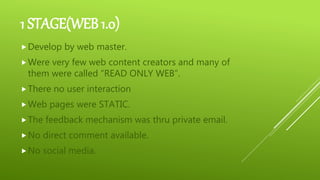
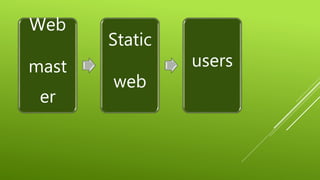
The document discusses information and communication technology (ICT) and its evolution from Web 1.0 to Web 3.0. ICT is defined as any electronic device or application used for communication, and includes radio, television and computers. The World Wide Web started as mostly static, "read-only" Web 1.0 sites created by webmasters. Web 2.0 introduced more interactivity through user-generated content and social media. Web 3.0 aims to be more semantic and machine-readable. Examples of social media discussed include Facebook, Twitter, Instagram and Snapchat. The document also covers dangers online like spam, spoofing, phishing and computer viruses, as well as ways to protect computers using firewalls and antivirus