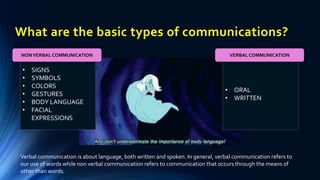
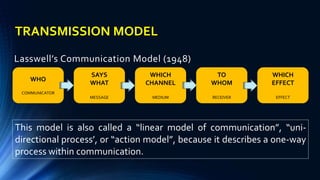
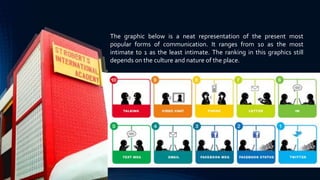
The document discusses empowerment technologies. It defines empowerment as giving power to promote self-actualization or enhance knowledge on a topic. Technology refers to using the internet, which is the major source of information. Empowerment technologies are important to teach millenials the proper use of information and communication technologies (ICT) and internet etiquette, rather than using them for cyberbullying or peer pressure. The document provides lessons on ICT, including definitions of information, communication, and technology, as well as examples of verbal and nonverbal communication methods. It analyzes communication models and how communication has changed with internet technology and social media.