The document discusses cross-compiling native packages for Android using autotools or cmake. It describes downloading and configuring the Android NDK, which provides cross-compilation tools for ARM, x86, and MIPS architectures. It then gives steps to cross-compile the expat library as an example, including downloading the sources, extracting them, and configuring/building using the autotools system. Key points covered include limitations of the Bionic C library used on Android and associations between Android API levels and supported architectures.



![make install &&
install -v -m755 -d /usr/share/doc/expat-2.1.0 &&
install -v -m644 doc/*.{html,png,css} /usr/share/doc/expat-2.1.0
5. Cross-compilation d'un package à base d'autotools
Pour l'exemple, je vais cross-compiler la librairie expat.
Je vais commencer par la récupérer les sources du package via le bash script suivant :
#!/bin/bash
echo "--> Récupération du package ${PACKAGE_NAME} - v${PACKAGE_VERSION} "
# --- Téléchargement du package --if [ "${PACKAGE_PROTOCOL}" != "" ] && [ "${PACKAGE_URL}" != "" ] && [ "${PACKAGE_NAME}" !
= "" ] && [ "${PACKAGE_VERSION}" != "" ] && [ "${PACKAGE_EXTENSION}" != "" ]; then
echo -n "
--> Téléchargement du package ... "
wget ${PACKAGE_PROTOCOL}://${PACKAGE_URL}/${PACKAGE_NAME}-${PACKAGE_VERSION}.$
{PACKAGE_EXTENSION} > /dev/null 2>&1
if [ -e "${PACKAGE_NAME}-${PACKAGE_VERSION}.${PACKAGE_EXTENSION}" ]; then
echo "OK"
else
echo "NOK ... arrêt !!"
exit
fi
else
echo " --> [ERROR] Package mal référencé ; Téléchargement impossible. "
echo " Exemple de description du package définissant la librairie expat : "
echo "
export PACKAGE_PROTOCOL=http "
echo "
export PACKAGE_URL=downloads.sourceforge.net/expat "
echo "
export PACKAGE_VERSION=2.1.0 "
echo "
export PACKAGE_NAME=expat "
echo "
export PACKAGE_EXTENSION=tar.gz "
echo "
export PACKAGE_CMD_EXTRACTION=tar zxvf "
exit
fi
# --- Extraction du package --if [ "${PACKAGE_CMD_EXTRACTION}" != "" ] && [ "${PACKAGE_NAME}" != "" ] && [ "$
{PACKAGE_VERSION}" != "" ] && [ "${PACKAGE_EXTENSION}" != "" ]; then
echo -n "
--> Extraction du package ... "
${PACKAGE_CMD_EXTRACTION} ${PACKAGE_NAME}-${PACKAGE_VERSION}.${PACKAGE_EXTENSION}
> /dev/null 2>&1
if [ -d "${PACKAGE_NAME}-${PACKAGE_VERSION}" ]; then
echo "OK"
else
echo "NOK ... arrêt !!"
exit
fi
else
echo " --> [ERROR] Impossible de trouver l'outils d'extraction $
{PACKAGE_CMD_EXTRACTION}
"
echo "
ou bien le package ${PACKAGE_NAME}-${PACKAGE_VERSION}.$
{PACKAGE_EXTENSION} "
exit
fi
# --- Déférencement des variables des registres pour nettoyer l'environement --echo -n "
--> Nettoyage de l'environement ... "
LIST_ENV="PACKAGE_PROTOCOL PACKAGE_URL PACKAGE_VERSION PACKAGE_NAME PACKAGE_EXTENSION
PACKAGE_CMD_EXTRACTION"](https://image.slidesharecdn.com/lm-gayetthierry-cross-compilationnativesousandroid-140127132808-phpapp02/85/Cross-compilation-native-sous-android-5-320.jpg)
![for VAR in `echo ${LIST_ENV}`
do
if [ "${VAR}" != "" ]; then
unset ${VAR}
fi
done
if [ "`env | grep PACKAGE`" == "" ]; then
echo "OK"
else
echo "NOK ... arrêt !!"
exit
fi
# Done.
echo "<-- Done."
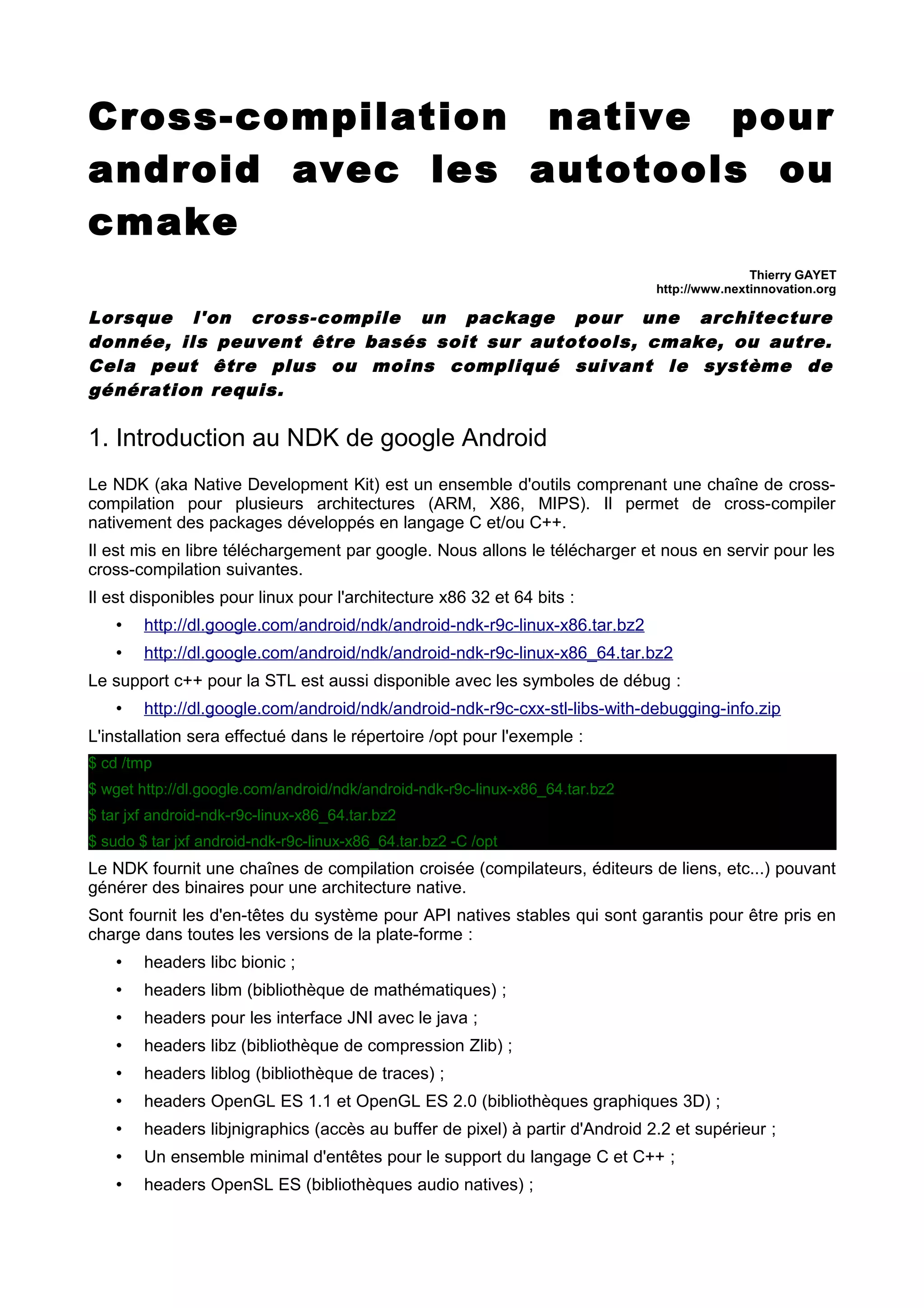
Après définition des informations du package, le téléchargement et l'extraction du package s'effectue de la
façon suivante :
$ PACKAGE_PROTOCOL="http" PACKAGE_URL="downloads.sourceforge.net/expat"
PACKAGE_VERSION="2.1.0" PACKAGE_NAME="expat" PACKAGE_EXTENSION="tar.gz"
PACKAGE_CMD_EXTRACTION="tar zxvf" ./getPackage.sh
--> Récupération du package expat - v2.1.0
--> Téléchargement du package ...
--> Extraction du package ...
--> Nettoyage de l'environement ...
<-- Done.
Une fois effectué, si aucune erreur n'est apparue, voilà ce que l'on doit avoir, à savoir le répertoire contenant
les sources et l'archive :
$ ls -al | grep expat-2.1.0
drwxrwxr-x 13 tgayet tgayet 4096 mars 24 2012 expat-2.1.0
-rw-rw-r-- 1 tgayet tgayet 562616 mars 24 2012 expat-2.1.0.tar.gz
$ cd expat-2.1.0/
$ ls -al
total 980
drwxrwxr-x 13 tgayet tgayet 4096 mars 24 2012 .
drwxrwxr-x 3 tgayet tgayet 4096 janv. 21 13:26 ..
-rw-rw-r-- 1 tgayet tgayet 304569 mars 24 2012 aclocal.m4
drwxrwxr-x 3 tgayet tgayet 4096 mars 24 2012 amiga
drwxrwxr-x 2 tgayet tgayet 4096 mars 24 2012 bcb5
-rw-rw-r-- 1 tgayet tgayet 11379 mars 24 2012 Changes
-rwxrwxr-x 1 tgayet tgayet 3299 mars 5 2012 CMakeLists.txt
-rwxrwxr-x 1 tgayet tgayet 1768 mars 5 2012 CMake.README
-rwxrwxr-x 1 tgayet tgayet 565580 mars 24 2012 configure
-rwxrwxr-x 1 tgayet tgayet 1512 mars 5 2012 ConfigureChecks.cmake
-rw-rw-r-- 1 tgayet tgayet 4652 mars 4 2012 configure.in
drwxrwxr-x 2 tgayet tgayet 4096 mars 24 2012 conftools
-rw-rw-r-- 1 tgayet tgayet 1208 déc. 29 2005 COPYING
drwxrwxr-x 2 tgayet tgayet 4096 mars 24 2012 doc
drwxrwxr-x 2 tgayet tgayet 4096 mars 24 2012 examples
-rwxrwxr-x 1 tgayet tgayet 2735 mars 5 2012 expat_config.h.cmake](https://image.slidesharecdn.com/lm-gayetthierry-cross-compilationnativesousandroid-140127132808-phpapp02/85/Cross-compilation-native-sous-android-6-320.jpg)







![-- Check size of unsigned short - done
-- Using unsigned short
-- Check if the system is big endian - little endian
-- Looking for off_t
-- Looking for off_t - not found
-- Looking for size_t
-- Looking for size_t - not found
-- Configuring done
-- Generating done
-- Build files have been written to: /home/tgayet/Documents/articles_lm/cross-compilation android/expat2.1.0/androidbuild
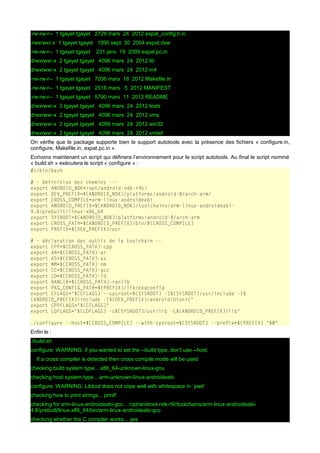
Cette étape permet de préparer le projet de façon à permettre un build :
$ make
Scanning dependencies of target expat
[ 5%] Building C object CMakeFiles/expat.dir/lib/xmlparse.c.o
[ 11%] Building C object CMakeFiles/expat.dir/lib/xmlrole.c.o
[ 17%] Building C object CMakeFiles/expat.dir/lib/xmltok.c.o
[ 23%] Building C object CMakeFiles/expat.dir/lib/xmltok_impl.c.o
[ 29%] Building C object CMakeFiles/expat.dir/lib/xmltok_ns.c.o
Linking C shared library ../libs/armeabi-v7a/libexpat.so
[ 29%] Built target expat
Scanning dependencies of target elements
[ 35%] Building C object CMakeFiles/elements.dir/examples/elements.c.o
Linking C executable ../bin/elements
[ 35%] Built target elements
Scanning dependencies of target outline
[ 41%] Building C object CMakeFiles/outline.dir/examples/outline.c.o
Linking C executable ../bin/outline
[ 41%] Built target outline
Scanning dependencies of target runtests
[ 47%] Building C object CMakeFiles/runtests.dir/tests/runtests.c.o
[ 52%] Building C object CMakeFiles/runtests.dir/tests/chardata.c.o
[ 58%] Building C object CMakeFiles/runtests.dir/tests/minicheck.c.o
Linking C executable ../bin/runtests
[ 58%] Built target runtests
Scanning dependencies of target runtestspp
[ 64%] Building CXX object CMakeFiles/runtestspp.dir/tests/runtestspp.cpp.o
In file included from /home/tgayet/Documents/articles_lm/cross-compilation android/expat2.1.0/tests/runtests.c:19:0,
from /home/tgayet/Documents/articles_lm/cross-compilation android/expat2.1.0/tests/runtestspp.cpp:6:
/home/tgayet/Documents/articles_lm/cross-compilation android/expat-2.1.0/tests/runtests.c: In function 'void
basic_setup()':
(...)
^](https://image.slidesharecdn.com/lm-gayetthierry-cross-compilationnativesousandroid-140127132808-phpapp02/85/Cross-compilation-native-sous-android-15-320.jpg)
![[ 70%] Building C object CMakeFiles/runtestspp.dir/tests/chardata.c.o
[ 76%] Building C object CMakeFiles/runtestspp.dir/tests/minicheck.c.o
Linking CXX executable ../bin/runtestspp
[ 76%] Built target runtestspp
Scanning dependencies of target xmlwf
[ 82%] Building C object CMakeFiles/xmlwf.dir/xmlwf/xmlwf.c.o
[ 88%] Building C object CMakeFiles/xmlwf.dir/xmlwf/xmlfile.c.o
[ 94%] Building C object CMakeFiles/xmlwf.dir/xmlwf/codepage.c.o
[100%] Building C object CMakeFiles/xmlwf.dir/xmlwf/readfilemap.c.o
Linking C executable ../bin/xmlwf
[100%] Built target xmlwf
Une version moins silentieuse peut être demandé :
$ make VERBOSE=1
L'installation est aussi simple :
$ sudo make install
[ 29%] Built target expat
[ 35%] Built target elements
[ 41%] Built target outline
[ 58%] Built target runtests
[ 76%] Built target runtestspp
[100%] Built target xmlwf
Install the project...
-- Install configuration: ""
-- Up-to-date: /opt/android-ndk-r9c/toolchains/arm-linux-androideabi-4.8/prebuilt/linuxx86_64/user/lib/libexpat.so
-- Up-to-date: /opt/android-ndk-r9c/toolchains/arm-linux-androideabi-4.8/prebuilt/linuxx86_64/user/include/expat.h
-- Up-to-date: /opt/android-ndk-r9c/toolchains/arm-linux-androideabi-4.8/prebuilt/linuxx86_64/user/include/expat_external.h
-- Up-to-date: /opt/android-ndk-r9c/toolchains/arm-linux-androideabi-4.8/prebuilt/linuxx86_64/user/lib/pkgconfig/expat.pc
-- Up-to-date: /opt/android-ndk-r9c/toolchains/arm-linux-androideabi-4.8/prebuilt/linux-x86_64/user/bin/xmlwf
-- Up-to-date: /opt/android-ndk-r9c/toolchains/arm-linux-androideabi-4.8/prebuilt/linuxx86_64/user/share/man/man1/xmlwf.1
7. Conclusion
Avec ces deux recettes, il nous sera possible de cross-compiler nombre packages via la toolchain
android sur le même modèle.
8. Liens
•
•
•
•
•
http://www.linuxfromscratch.org/blfs/view/svn/general/expat.html
http://developer.android.com/tools/sdk/ndk/index.html
https://github.com/android/platform_bionic
http://elinux.org/Android_Notes#C_Library_.28bionic.29_info
http://developer.android.com/index.html](https://image.slidesharecdn.com/lm-gayetthierry-cross-compilationnativesousandroid-140127132808-phpapp02/85/Cross-compilation-native-sous-android-16-320.jpg)
