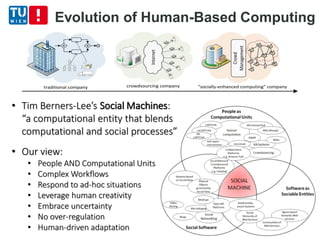
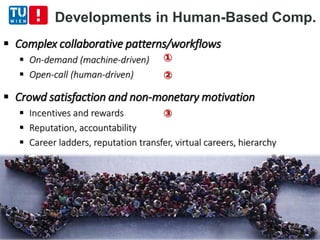
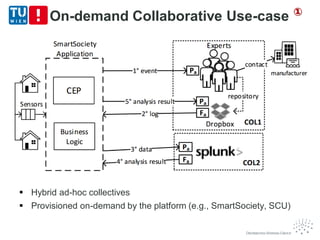
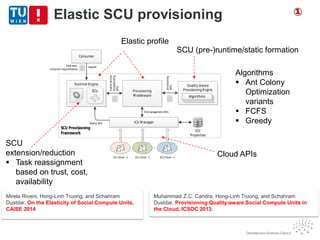
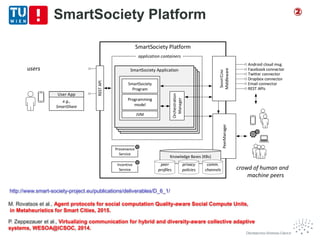
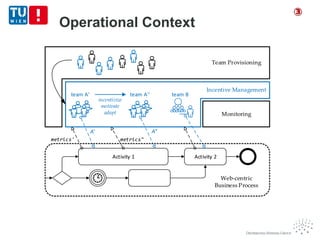
The document discusses the concept of elastic cognitive systems and their implications for various domains such as smart cities, e-health, and human computing. It emphasizes the need for robustness, elasticity in resource utilization, and the integration of human and machine capabilities to handle complex scenarios. Key features include incentive management, programming for elasticity, and the use of social compute units to optimize human-based services within distributed systems.


![Crowd satisfaction and
non-monetary motivation
[2] Kittur, A., et al.: The future of crowd work. Proc. of CSCW ’13, New York, USA.
• How to make virtual labor market competitive
and attractive for skilled workers? [2]
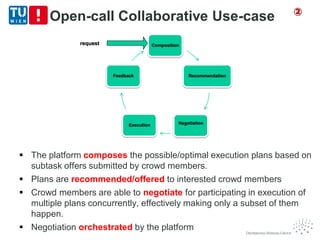
Complex collaborative patterns/workflows
Hierarchy/structure
Worker satisfaction and non-monetary motivation
Reputation, accountability
Career ladders, reputation transfer, virtual careers
Incentive
Management
③](https://image.slidesharecdn.com/elasticcognitivesystems18-6-2015dustdar-150618140933-lva1-app6891/85/Elastic-cognitive-systems-18-6-2015-dustdar-22-320.jpg)
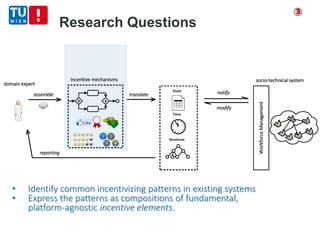
![Modeling Incentives
Examined incentive strategies in over 200 existing
social computing platforms
Examined incentive mechanisms in economics,
management science, sociology, psychology
Identified fundamental incentive mechanisms
in use today and their constituent elements
New mechanisms can be built by composing
and customizing well-known incentive elements
[3] Scekic, O., Truong, H.-L., Dustdar, S.: Incentives and rewarding in social computing.
Communications of the ACM, 56(6), 72 (2013).
③](https://image.slidesharecdn.com/elasticcognitivesystems18-6-2015dustdar-150618140933-lva1-app6891/85/Elastic-cognitive-systems-18-6-2015-dustdar-26-320.jpg)
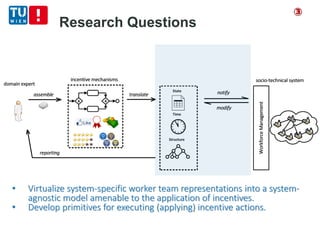
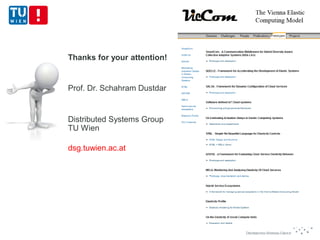
![Abstraction Interlayer
PRINC (PRogrammable INcentives) framework.
Allows modeling of human worker teams
– storing and altering worker metrics
– storing and altering worker structure
– storing behavioral history and scheduling of incentive actions
Event-based communication with underlying socio-technical system
[4] Scekic, O., Truong, H.-L., Dustdar, S.: Modeling
rewards and incentive mechanisms for social BPM.
Proc. BPM’12 (pp. 150–155), Talinn, (2013).
[5] Scekic, O., Truong, H.-L., Dustdar, S.:
Programming incentives in information systems. In
Proc. CAiSE’13 (pp. 688–703), Valencia (2013).
③](https://image.slidesharecdn.com/elasticcognitivesystems18-6-2015dustdar-150618140933-lva1-app6891/85/Elastic-cognitive-systems-18-6-2015-dustdar-28-320.jpg)
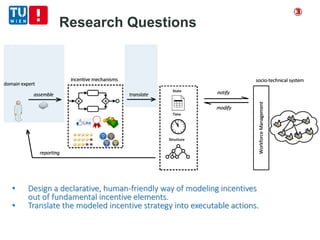
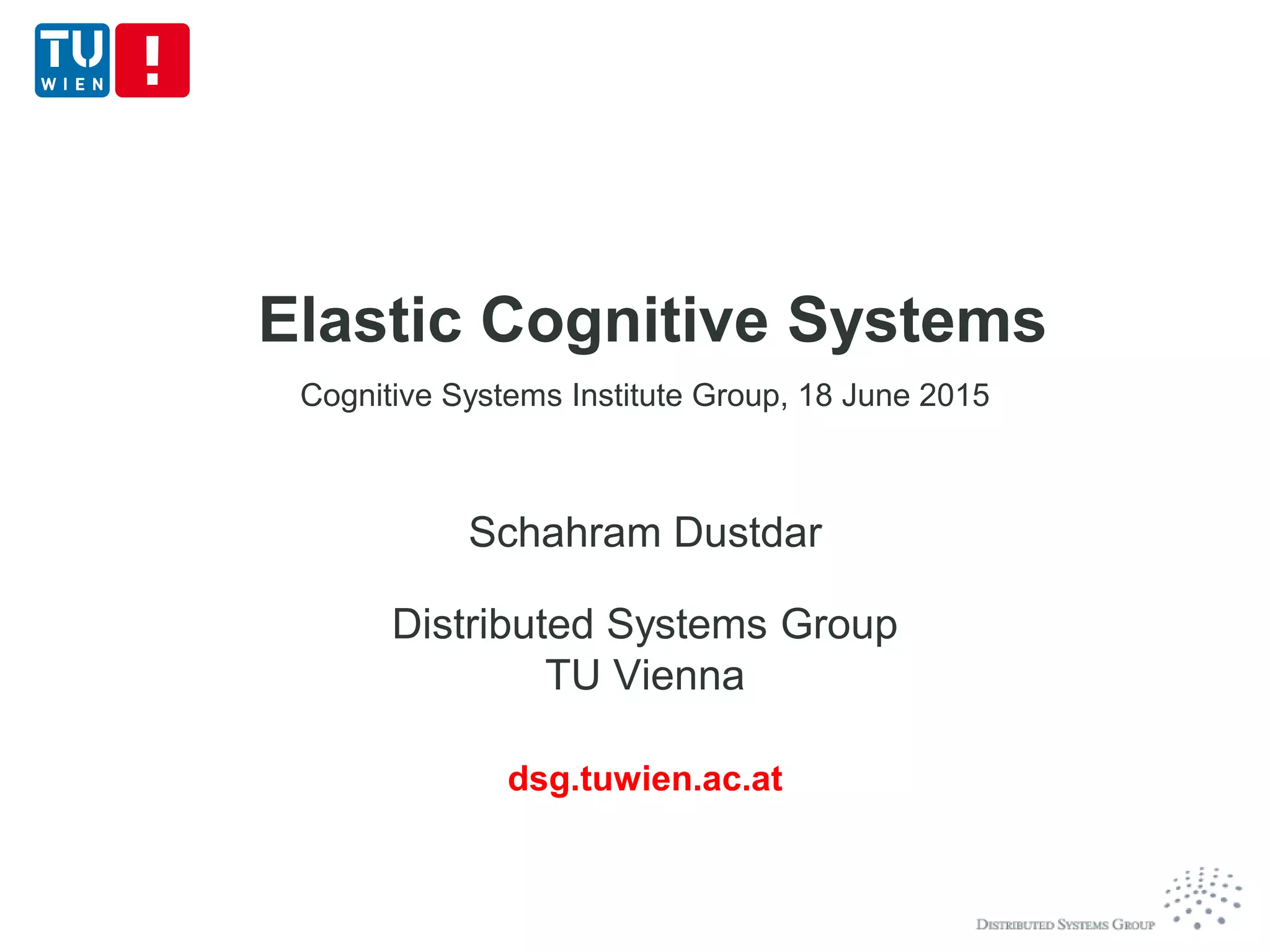
![A Domain-Specific Language for
Incentives
[6] Scekic, O., Truong, H.-L., Dustdar, S.:
Managing Incentives in Social Computing Systems with PRINGL. WISE’14 (pp. 415—424), Thessaloniki, Greece
PRINGL – PRogrammable INcentive Graphical Language
Visuo-textual language
– Graphical elements for modeling and
composing incentive elements
– Traditional code snippets for additional
business logic
System-independent
Human-friendly syntax
Elements can be stored, shared, reused
Translated to code executable on abstraction interlayer
③](https://image.slidesharecdn.com/elasticcognitivesystems18-6-2015dustdar-150618140933-lva1-app6891/85/Elastic-cognitive-systems-18-6-2015-dustdar-30-320.jpg)