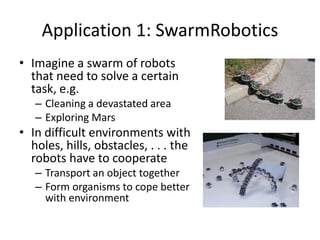
Robots working in swarms need to be self-aware to adapt their behavior based on task performance and collective behavior emerges. Self-aware computing systems could help manage distributed energy production and consumption in smart grids. Data and services could manage themselves in an "ecosystem" through decentralized algorithms. Human cognitive processes like inference could help systems manage internet content by acquiring new content and filtering existing content. Self-aware electric vehicles could communicate to improve reliability, adaptability, and predictability through cooperation. Science clouds use self-aware computing to manage distributed notebooks, servers and virtual machines.