EA History
•
4 likes•724 views
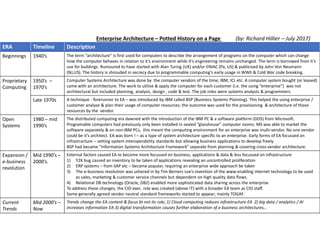
A potted history of Enterprise Architecture from the 1940's through to the present day. All on one page !
Report
Share
Report
Share
Download to read offline
Recommended
Information and Communications Technology

Here,you can add your knowledge about social information on how it is being developed.Hence, I do believe that students are and will be better equipped with knowledge should they use ICT in schools. It is definitely a win-win situation as both teacher and student learn to use ICT.As a whole, I find that use of ICT in schools is the way to go.
With the rapid advances in technology, the prevalence of using ICT in schools is indeed prominent. Not only does it gear the students for the future, it also creates an avenue for students to be more innovative and not learn strictly by the book. Enjoy!
SDN for Enterprise Networks

Nick Lippis
Analyst
Lippis Enterprises, Inc.
ONS2015: http://bit.ly/ons2015sd
ONS Inspire! Webinars: http://bit.ly/oiw-sd
Watch the talk (video) on ONS Content Archives: http://bit.ly/ons-archives-sd
Software Trends: Past, Present and Future

Software Trends: Past, Present and Future
Presentation by Biniam Asnake
BCO 117 IT Software for Business Lecture Reference Notes.docx

BCO 117 IT Software for Business
Lecture Reference Notes
Cloud
computing
Eras in IT infrastructure evolution
Chapter 5. IT Infrastructure and EmergingTechnologies
Management Information Systems (Kenneth P. Laudon, Jane C. Laudon)
An information technology (IT) paradigm, a model for enabling ubiquitous access to shared pools of configurable resources (such as computer networks, servers, storage, applications and services), which
can be rapidly provisioned with minimal management effort, often over the Internet.
· Computing as a service
· Computing on the Internet
· Business line for computing corporations
Hassan, Qusay (2011).
"Demystifying Cloud Computing"(PDF).
The Journal of Defense Software Engineering.
Cloud computing
Cloud computing
Cloud computing
Cloud computing
www.euruni.edu
Cloud computing examples
Software as a Service
Platform as a Service
Insfrastructure as a Service
Cloud computing examples
Cloud computing examples
https://aws.amazon.com/products/?hp=tile&so-exp=below
Cloud computing examples
Cloud computing examples
Cloud computing examples
www.euruni.edu
Cloud computing examples
Cloud computing examples
Cloud computing examples
www.euruni.edu
Cloud computing success
Key concepts
·
Reliability – reliability of the system, measured in Mean Time Between Failures (MTBF)
·
Availability – uptime of the system or application, measured in parts per million (PPM) of downtime
·
Serviceability – easily restoring the system after a failure, measured in Mean Time To Repair (MTTR)
·
Manageability – the ease with which the entire system can be managed, measured in systems per headcount.
·
Scalability - the ability of an information system to be used or produced in a range of capabilities
·
“Updatability”– a key factor linked to performance, integration with other IS and security
https://software.intel.com/en-us/articles/total-cost-of-ownership-factors-to-consider
Top Benefits of Cloud Computing
http://www.mushibhuiyan.com/category/cloud/
Debate
https://www.forbes.com/sites/louiscolumbus/2013/08/13/idg-cloud-computing-survey-security-integration-challenge-growth/#268d6d3755cb
Debate
https://www.forbes.com/sites/louiscolumbus/2013/08/13/idg-cloud-computing-survey-security-integration-challenge-growth/#268d6d3755cbCloud Computing strategy
https://www-01.ibm.com/common/ssi/cgi-bin/ssialias?htmlfid=WUW12350USEN
www.euruni.edu
image24.jpg
image25.jpg
image26.png
image27.png
image31.png
image29.png
image28.png
image3.jpg
image4.png
image5.jpg
image30.png
image4.jpg
image6.jpg
image7.jpg
image8.jpg
image9.jpg
image70.jpg
image80.jpg
image10.png
image11.png
image12.jpg
image1.png
image13.png
image14.jpg
image15.jpg
image13.jpg
image140.jpg
image16.png
image17.png
image15.png
image32.png
image2.png
image18.jpg
image19.png
i.
Introduction of Cloud Computing By Pawan Thakur HOD CS & IT

Over the past decade cloud computing has interrupted nearly every part of IT. Sales, marketing, finance and support all of these applications are being reengineered to take advantage of cloud's instant access no download and pay as we go attributes. The term cloud computing is sometimes used to refer to a new paradigm some even speak of a new technology.
Recommended
Information and Communications Technology

Here,you can add your knowledge about social information on how it is being developed.Hence, I do believe that students are and will be better equipped with knowledge should they use ICT in schools. It is definitely a win-win situation as both teacher and student learn to use ICT.As a whole, I find that use of ICT in schools is the way to go.
With the rapid advances in technology, the prevalence of using ICT in schools is indeed prominent. Not only does it gear the students for the future, it also creates an avenue for students to be more innovative and not learn strictly by the book. Enjoy!
SDN for Enterprise Networks

Nick Lippis
Analyst
Lippis Enterprises, Inc.
ONS2015: http://bit.ly/ons2015sd
ONS Inspire! Webinars: http://bit.ly/oiw-sd
Watch the talk (video) on ONS Content Archives: http://bit.ly/ons-archives-sd
Software Trends: Past, Present and Future

Software Trends: Past, Present and Future
Presentation by Biniam Asnake
BCO 117 IT Software for Business Lecture Reference Notes.docx

BCO 117 IT Software for Business
Lecture Reference Notes
Cloud
computing
Eras in IT infrastructure evolution
Chapter 5. IT Infrastructure and EmergingTechnologies
Management Information Systems (Kenneth P. Laudon, Jane C. Laudon)
An information technology (IT) paradigm, a model for enabling ubiquitous access to shared pools of configurable resources (such as computer networks, servers, storage, applications and services), which
can be rapidly provisioned with minimal management effort, often over the Internet.
· Computing as a service
· Computing on the Internet
· Business line for computing corporations
Hassan, Qusay (2011).
"Demystifying Cloud Computing"(PDF).
The Journal of Defense Software Engineering.
Cloud computing
Cloud computing
Cloud computing
Cloud computing
www.euruni.edu
Cloud computing examples
Software as a Service
Platform as a Service
Insfrastructure as a Service
Cloud computing examples
Cloud computing examples
https://aws.amazon.com/products/?hp=tile&so-exp=below
Cloud computing examples
Cloud computing examples
Cloud computing examples
www.euruni.edu
Cloud computing examples
Cloud computing examples
Cloud computing examples
www.euruni.edu
Cloud computing success
Key concepts
·
Reliability – reliability of the system, measured in Mean Time Between Failures (MTBF)
·
Availability – uptime of the system or application, measured in parts per million (PPM) of downtime
·
Serviceability – easily restoring the system after a failure, measured in Mean Time To Repair (MTTR)
·
Manageability – the ease with which the entire system can be managed, measured in systems per headcount.
·
Scalability - the ability of an information system to be used or produced in a range of capabilities
·
“Updatability”– a key factor linked to performance, integration with other IS and security
https://software.intel.com/en-us/articles/total-cost-of-ownership-factors-to-consider
Top Benefits of Cloud Computing
http://www.mushibhuiyan.com/category/cloud/
Debate
https://www.forbes.com/sites/louiscolumbus/2013/08/13/idg-cloud-computing-survey-security-integration-challenge-growth/#268d6d3755cb
Debate
https://www.forbes.com/sites/louiscolumbus/2013/08/13/idg-cloud-computing-survey-security-integration-challenge-growth/#268d6d3755cbCloud Computing strategy
https://www-01.ibm.com/common/ssi/cgi-bin/ssialias?htmlfid=WUW12350USEN
www.euruni.edu
image24.jpg
image25.jpg
image26.png
image27.png
image31.png
image29.png
image28.png
image3.jpg
image4.png
image5.jpg
image30.png
image4.jpg
image6.jpg
image7.jpg
image8.jpg
image9.jpg
image70.jpg
image80.jpg
image10.png
image11.png
image12.jpg
image1.png
image13.png
image14.jpg
image15.jpg
image13.jpg
image140.jpg
image16.png
image17.png
image15.png
image32.png
image2.png
image18.jpg
image19.png
i.
Introduction of Cloud Computing By Pawan Thakur HOD CS & IT

Over the past decade cloud computing has interrupted nearly every part of IT. Sales, marketing, finance and support all of these applications are being reengineered to take advantage of cloud's instant access no download and pay as we go attributes. The term cloud computing is sometimes used to refer to a new paradigm some even speak of a new technology.
Fundamentals of Computer Design including performance measurements & quantita...

Fundamentals of Computer Design including performance measurements & quantitative principles
A seminar report on Raspberry Pi

Seminar report on Raspberry Pi, submitted in SEMINAR subject of GTU Gujarat Technological University by Nipun Parikh from Bhagwan Mahavir College of Engineering & Technology
Computer Software Ultimate History and Benefits

Computer software is a couple of directions, data, or programs applied to use pcs and perform specific tasks. It is the alternative to equipment, which explains the bodily aspects of a computer. Actually, Computer software is just a universal term applied to reference purposes, texts, and programs that run using a device
For more details Please visit our Website
https://csubmit.com/
A todo esto ¿Qué es una arquitectura?

Serie de semiarios DCC8090. Charla: "A todo esto, ¿Qué es una arquitectura?". Autor: Juan Carlos Barroux. 2008.
L01 Enterprise Application Architecture

In this first lecture we look at the state of the industry and specifically the post-pc era that follows the digital decade. The PC is not the center anymore and we as architects need to create solution that are long lasting and usable on any device.
Creating software systems is hard. Fortunately, as system architects we have many methods to build upon and in this lecture we will explore those building blocks. We also look at the evolution of software architectures and the importance of service oriented architecture
L01 Introduction to Enterprise Software

Í þessum fyrsta fyrirlestri fjöllum við um Enterprise forrit, hvað einkennir þau og hvaða áskoranir við stöndum frammi fyrir. Byrjum á því að skoða forritunarlausnir í samhengi við þróun undanfarinna ára. Menn tala um að nú séu "post PC" tímabil þar sem einkatölvan eins og við þekkjum hana er bara eitt af mörgum tækjum sem við notum. Forritun okkar geta verið snjallsíma öpp eða PC forrit og gögnin okkar eru í tölvuskýjunum.
Við skilgreinum hvað er átt við með Enterprise forritun og tökum fjölmörg dæmi. Skilgreinum B2B, B2C og tegundir af lausnum. Þá lítum við á þróun enterprise lausna frá Client-Server til gagnavera sem hýsa microservice lausnir. Slæmu fréttirnar eru að það er mjög erfitt að smíða svona lausnir, en góðu fréttirnar eru að við höfum fjölmörg tæki og tól til að hjálpa okkur.
Past & Future Of The Cloud Nott Tues Nov 09

Insights into the cloud, the technologies behind it and what the future holds
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
More Related Content
Similar to EA History
Fundamentals of Computer Design including performance measurements & quantita...

Fundamentals of Computer Design including performance measurements & quantitative principles
A seminar report on Raspberry Pi

Seminar report on Raspberry Pi, submitted in SEMINAR subject of GTU Gujarat Technological University by Nipun Parikh from Bhagwan Mahavir College of Engineering & Technology
Computer Software Ultimate History and Benefits

Computer software is a couple of directions, data, or programs applied to use pcs and perform specific tasks. It is the alternative to equipment, which explains the bodily aspects of a computer. Actually, Computer software is just a universal term applied to reference purposes, texts, and programs that run using a device
For more details Please visit our Website
https://csubmit.com/
A todo esto ¿Qué es una arquitectura?

Serie de semiarios DCC8090. Charla: "A todo esto, ¿Qué es una arquitectura?". Autor: Juan Carlos Barroux. 2008.
L01 Enterprise Application Architecture

In this first lecture we look at the state of the industry and specifically the post-pc era that follows the digital decade. The PC is not the center anymore and we as architects need to create solution that are long lasting and usable on any device.
Creating software systems is hard. Fortunately, as system architects we have many methods to build upon and in this lecture we will explore those building blocks. We also look at the evolution of software architectures and the importance of service oriented architecture
L01 Introduction to Enterprise Software

Í þessum fyrsta fyrirlestri fjöllum við um Enterprise forrit, hvað einkennir þau og hvaða áskoranir við stöndum frammi fyrir. Byrjum á því að skoða forritunarlausnir í samhengi við þróun undanfarinna ára. Menn tala um að nú séu "post PC" tímabil þar sem einkatölvan eins og við þekkjum hana er bara eitt af mörgum tækjum sem við notum. Forritun okkar geta verið snjallsíma öpp eða PC forrit og gögnin okkar eru í tölvuskýjunum.
Við skilgreinum hvað er átt við með Enterprise forritun og tökum fjölmörg dæmi. Skilgreinum B2B, B2C og tegundir af lausnum. Þá lítum við á þróun enterprise lausna frá Client-Server til gagnavera sem hýsa microservice lausnir. Slæmu fréttirnar eru að það er mjög erfitt að smíða svona lausnir, en góðu fréttirnar eru að við höfum fjölmörg tæki og tól til að hjálpa okkur.
Past & Future Of The Cloud Nott Tues Nov 09

Insights into the cloud, the technologies behind it and what the future holds
Similar to EA History (20)
Fundamentals of Computer Design including performance measurements & quantita...

Fundamentals of Computer Design including performance measurements & quantita...
Recently uploaded
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar
Bits & Pixels using AI for Good.........

A whirlwind tour of tech & AI for socio-environmental impact.
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designer, Beats by Dr Dre
Elevating Tactical DDD Patterns Through Object Calisthenics

After immersing yourself in the blue book and its red counterpart, attending DDD-focused conferences, and applying tactical patterns, you're left with a crucial question: How do I ensure my design is effective? Tactical patterns within Domain-Driven Design (DDD) serve as guiding principles for creating clear and manageable domain models. However, achieving success with these patterns requires additional guidance. Interestingly, we've observed that a set of constraints initially designed for training purposes remarkably aligns with effective pattern implementation, offering a more ‘mechanical’ approach. Let's explore together how Object Calisthenics can elevate the design of your tactical DDD patterns, offering concrete help for those venturing into DDD for the first time!
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP of Product, Amplitude
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
Knowledge engineering: from people to machines and back

Keynote at the 21st European Semantic Web Conference
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Sidekick Solutions uses Bonterra Impact Management (fka Social Solutions Apricot) and automation solutions to integrate data for business workflows.
We believe integration and automation are essential to user experience and the promise of efficient work through technology. Automation is the critical ingredient to realizing that full vision. We develop integration products and services for Bonterra Case Management software to support the deployment of automations for a variety of use cases.
This video focuses on the notifications, alerts, and approval requests using Slack for Bonterra Impact Management. The solutions covered in this webinar can also be deployed for Microsoft Teams.
Interested in deploying notification automations for Bonterra Impact Management? Contact us at sales@sidekicksolutionsllc.com to discuss next steps.
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Presented by Suzanne Phillips and Alex Marcotte
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

Reflecting on new architectures for knowledge based systems in light of generative ai
Securing your Kubernetes cluster_ a step-by-step guide to success !

Today, after several years of existence, an extremely active community and an ultra-dynamic ecosystem, Kubernetes has established itself as the de facto standard in container orchestration. Thanks to a wide range of managed services, it has never been so easy to set up a ready-to-use Kubernetes cluster.
However, this ease of use means that the subject of security in Kubernetes is often left for later, or even neglected. This exposes companies to significant risks.
In this talk, I'll show you step-by-step how to secure your Kubernetes cluster for greater peace of mind and reliability.
When stars align: studies in data quality, knowledge graphs, and machine lear...

Keynote at DQMLKG workshop at the 21st European Semantic Web Conference 2024
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scalable Platform by VP of Product, The New York Times
Accelerate your Kubernetes clusters with Varnish Caching

A presentation about the usage and availability of Varnish on Kubernetes. This talk explores the capabilities of Varnish caching and shows how to use the Varnish Helm chart to deploy it to Kubernetes.
This presentation was delivered at K8SUG Singapore. See https://feryn.eu/presentations/accelerate-your-kubernetes-clusters-with-varnish-caching-k8sug-singapore-28-2024 for more details.
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head of Product, Amazon Games
Recently uploaded (20)
FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf

FIDO Alliance Osaka Seminar: The WebAuthn API and Discoverable Credentials.pdf
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
Designing Great Products: The Power of Design and Leadership by Chief Designe...

Designing Great Products: The Power of Design and Leadership by Chief Designe...
Elevating Tactical DDD Patterns Through Object Calisthenics

Elevating Tactical DDD Patterns Through Object Calisthenics
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...

From Daily Decisions to Bottom Line: Connecting Product Work to Revenue by VP...
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Knowledge engineering: from people to machines and back

Knowledge engineering: from people to machines and back
Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...

Slack (or Teams) Automation for Bonterra Impact Management (fka Social Soluti...
Assuring Contact Center Experiences for Your Customers With ThousandEyes

Assuring Contact Center Experiences for Your Customers With ThousandEyes
To Graph or Not to Graph Knowledge Graph Architectures and LLMs

To Graph or Not to Graph Knowledge Graph Architectures and LLMs
Securing your Kubernetes cluster_ a step-by-step guide to success !

Securing your Kubernetes cluster_ a step-by-step guide to success !
When stars align: studies in data quality, knowledge graphs, and machine lear...

When stars align: studies in data quality, knowledge graphs, and machine lear...
From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...

From Siloed Products to Connected Ecosystem: Building a Sustainable and Scala...
Accelerate your Kubernetes clusters with Varnish Caching

Accelerate your Kubernetes clusters with Varnish Caching
Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...

Unsubscribed: Combat Subscription Fatigue With a Membership Mentality by Head...
EA History
- 1. ERA Timeline Description Beginnings 1940’s The term “architecture” is first used for computers to describe the arrangement of programs on the computer which can change how the computer behaves in relation to it’s environment while it’s engineering remains unchanged. The term is borrowed from it’s use for buildings. Rumoured to have started with Alan Turing (UK) and/or ENIAC (Pa, US) & publicised by John Von Neumann (NJ,US). The history is shrouded in secrecy due to programmable computing’s early usage in WWII & Cold War code breaking. Proprietary Computing 1950’s – 1970’s Computer Systems Architecture was done by the computer vendors of the time; IBM, ICL etc. A computer system bought (or leased) came with an architecture. The work to utilise & apply the computer for each customer (i.e. the using “enterprise”) was not architectural but included planning, analysis, design , code & test. The job roles were systems analysts & programmers. Late 1970s A technique - forerunner to EA – was introduced by IBM called BSP (Business Systems Planning). This helped the using enterprise / customer analyse & plan their usage of computer resources; the outcome was used for the provisioning & architecture of those resources by the vendor. Open Systems 1980 – mid 1990’s The distributed computing era dawned with the introduction of the IBM PC & a software platform (DOS) from Microsoft. Programable computers had previously only been installed in sealed “glasshouse” computer rooms. MS was able to market the software separately & on non-IBM PCs; this meant the computing environment for an enterprise was multi-vendor. No one vendor could be it’s architect. EA was born ! – as a type of system architecture specific to an enterprise. Early forms of EA focussed on infrastructure – setting system interoperability standards but allowing business applications to develop freely. BSP had became ”Information Systems Architecture Framework” separate from planning & covering cross-vendor architecture. Expansion / e-business revolution Mid 1990’s – 2000’s. External factors caused EA to become more focussed on business, applications & data & less focussed on infrastructure 1) Y2K bug caused an inventory to be taken of applications revealing an uncontrolled proliferation 2) ERP systems – from SAP etc – became popular, requiring an enterprise wide approach be taken 3) The e-business revolution was ushered in by Tim Berners Lee’s invention of the www enabling internet technology to be used as sales, marketing & customer service channels but dependent on high quality data flows. 4) Relational DB technology (Oracle, DB2) enabled more sophisticated data sharing across the enterprise To address these changes, the CIO exec. role was created (above IT) with a broader EA team as CIO staff. Some generally agreed vendor neutral standard frameworks started to appear; mainly TOGAF. Current Trends Mid 2000’s – Now Trends change the EA content & focus bt not its role; 1) Cloud computing reduces infrastructure EA 2) big data / analytics / AI increases information EA 3) digital transformation causes further elaboration of e-business architectures… Enterprise Architecture – Potted History on a Page (by: Richard Hillier – July 2017)